Author: IT Administrator
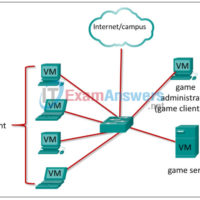
The CyberOps Skills Challenge – Student Guide Reference Topology Note: The topology is provided as an illustration of the logical game architecture. Other topologies can be used as long as the connectivity requirements are met. Purpose This document will support you as you prepare to play the Cyber …
1. Which form of communication is a real-time text-based communication type used between two or more people who use mostly text to communicate with each other? Weblogs Wikis Instant Messaging Podcasting Collaboration Tools 2. Which type of network provides customer’s limited access to corporate data such as inventory, …
Endpoint Security: My Knowledge Check Answers 1. Which Windows version was the first to introduce a 64-bit Windows operating system? Windows NT Windows XP Windows 7 Windows 10 2. Employees in an organization report that the network access is slow. Further investigation reveals that one employee downloaded a …
Cyber Threat Management: My Knowledge Check Answers 1. Match the network security testing tool with the correct function. (Not all options are used.) 2. In which step of the NIST incident response process does the CSIRT perform an analysis to determine which networks, systems, or applications are affected; …
Network Defense – My Knowledge Check Answers 1. In a hierarchical CA topology, where can a subordinate CA obtain a certificate for itself? from the root CA only from the root CA or from self-generation from the root CA or another subordinate CA at the same level from …
Network Support and Security: My Knowledge Check Answers 1. Employees in an organization report that they cannot access the customer database on the main server. Further investigation reveals that the database file is now encrypted. Shortly afterward, the organization receives a threatening email demanding payment for the decryption …
CCNA Discovery v4.0 Exam Answers
Network Addressing and Basic Troubleshooting: My Knowledge Check Answers 1. Why are two strands of fiber used for a single fiber optic connection? The two strands allow the data to travel for longer distances without degrading. They prevent crosstalk from causing interference on the connection. They increase the …
Networking Basics – My Knowledge Check (Answers) 1. Which two application layer protocols manage the exchange of messages between a client with a web browser and a remote web server? (Choose two.) HTTP HTTPS DNS DHCP HTML 2. What is the default SSID Broadcast setting on a wireless …
Networking Essentials (Version 2) – Networking Essentials 2.0 Practice Final Exam Answers 1. Match the type of malware with the definition. 2. An intruder tries a large number of possibilities in rapid succession to guess a password. As a result, other users on the network are locked out. …