Category: CCNA CyberOps
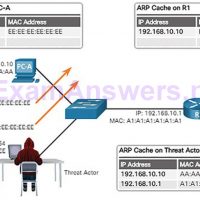
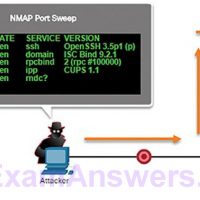
Objectives Upon completion of this chapter, you will be able to answer the following questions: What is the importance of network monitoring? How is network monitoring conducted? How do IP vulnerabilities enable network attacks? How do TCP and UDP vulnerabilities enable network attacks? What are the IP vulnerabilities? …
Objectives Upon completion of this chapter, you will be able to answer the following questions: What is the evolution of network security? What are the various types of attack tools used by threat actors? What is malware? What are some common network attacks? Key Terms This chapter uses …
Objectives Upon completion of this chapter, you will be able to answer the following questions: How do network devices enable network communication? How do wireless devices enable network communication? How are specialized devices used to enhance network security? How do network services enhance network security? How are network …
Objectives Upon completion of this chapter, you will be able to answer the following questions: What is the basic operation of data network communications? How do protocols enable network operations? How does Ethernet support network communication? How does the IPv4 protocol support network communications? How do IP addresses …
Objectives Upon completion of this chapter, you will be able to answer the following questions: Why are Linux skills essential for network security monitoring and investigation? How do you use the Linux shell to manipulate text files? How do client-server networks function? How does a Linux administrator locate …
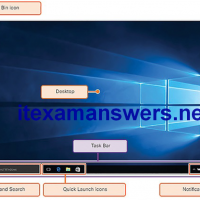
Objectives Upon completion of this chapter, you will be able to answer the following questions: What is the history of the Windows operating system? What is the architecture of Windows and its operation? How do you configure and monitor Windows? How is Windows kept secure? Key Terms This …
Objectives Upon completion of this chapter, you will be able to answer the following questions: What are some features of examples of cybersecurity incidents? What are the motivations of the threat actors behind specific security incidents? What is the potential impact of network security attacks? What is the …
1. Which statement describes an operational characteristic of NetFlow? NetFlow collects metadata about the packet flow, not the flow data itself. 2. What is the purpose of Tor? to allow users to browse the Internet anonymously 3. Threat actors may attack the infrastructure in order to corrupt …
1. If an asymmetric algorithm uses a public key to encrypt data, what is used to decrypt it? a private key 2. Which IETF standard defines the PKI digital certificate format? X.509 3. Which statement describes the use of hashing? Hashing can be used to detect accidental changes, …
1. Which monitoring technology mirrors traffic flowing through a switch to an analysis device connected to another switch port? NetFlow SNMP SIEM SPAN 2. Which network technology uses a passive splitting device that forwards all traffic, including Layer 1 errors, to an analysis device? NetFlow network tap SNMP …