IT Essentials (Version 7.00) – IT Essentials 7.0 Chapter 10 exam Answers
IT Essentials v7.0:
1. What are two types of computer user interface? (Choose two.)
- CLI
- PnP
- GUI
- OpenGL
- API
2. What are two default account types provided by Windows 10? (Choose two.)
- Guest
- Users
- Administrator
- Standard User
- DefaultAccount
3. Which term best describes the process of breaking a program into smaller parts that can be loaded as needed by the operating system?
- multithreading
- multiprocessing
- multiuser
- multitasking
4. What is the default file system used during a fresh installation of Windows 7?
- NTFS
- HPFS
- FAT16
- FAT32
5. A user installs a new sound card driver in a computer that is working properly. After the installation of the drivers for the new sound card, the computer fails to boot. Which quick fix can the user implement to return to the previous working state?
- Boot to Emergency Recovery State.
- Boot to Last Known Good Configuration.
- Boot to Recovery Console.
- Boot to Start Windows Normally.
6. What is a possible situation when it might be necessary to boot Windows 7 from a USB device, a CD, or a DVD?
- to disable background services
- to delete registry keys
- to partition the hard drive
- to repair the system
7. What feature of an operating system allows it to support two or more CPUs?
- multiprocessing
- multitasking
- multiuser support
- multithreading
8. What term is used to describe a logical drive that can be formatted to store data?
- volume
- track
- sector
- cluster
- partition
9. Which key, when pressed during the boot process, will allow the user to choose to start Windows in safe mode?
- F8
- F1
- Esc
- Windows
10. Which file system is used to access files over a network?
- NFS
- NTFS
- FAT
- CDFS
11. Which statement is a feature of the Windows 8 operating system?
- It supports a touch screen interface.
- It uses the Aero user interface.
- It can be directly upgraded from Windows XP.
- It is a 128-bit operating system.
12. Which component of a CPU architecture allows the CPU immediate access to data?
- registers
- cache
- RAM
- CMOS
13. When would the PXE option be used when repairing a PC?
- The display cannot be seen clearly.
- There is no response from the mouse or keyboard.
- The computer needs a replacement operating system.
- A newly installed application caused the system to perform erratically.
14. Which statement accurately describes the GUID partition table?
- It is 512 bytes long and contains the boot loader.
- It cannot be used in a multiboot environment.
- It is commonly used in computers with UEFI firmware.
- It is not supported by Windows 10 Home edition.
15. Which statement describes dynamic disks in a PC that is running Windows 10 Pro?
- They have the ability to create volumes that span across more than one disk.
- Free space can only be added from the same disk to extend the volume.
- A partition created on a dynamic disk can be shrunk without deleting the partition first.
- More space can be added to a partition by extending it into adjacent, unallocated space, as long as it is contiguous.
16. A technician wishes to deploy Windows 10 Pro upgrade to a group of employee PCs on the network and ensure that the user state migrates successfully. Which tool would the technician use to do this?
- User State Migration
- Windows Easy Transfer
- PCmover Express
- Windows 10 Update Assistant
17. Which operating system does not support Windows Easy Transfer to transfer information from one computer to another?
- Windows 8
- Windows 10
- Windows Vista
- Windows 7
18. Which command line utility was developed by Microsoft to allow users to transfer files and settings to a new edition of Windows OS during an upgrade to Windows 10?
- PCmover Express
- Windows Easy Transfer
- User State Migration Tool
- Windows Upgrade Assistant
19. Which operation in Windows 10 is limited to users with Administrator privileges only?
- Run applications.
- Modify user settings.
- Change system settings.
- Install software programs.
20. Which program file is loaded by the boot manager in a Windows boot process?
- winload.exe
- sysprep.exe
- ntoskrnl.exe
- winlogon.exe
21. At the end of the boot process of Windows 10, the login program file winlogon.exe loads. Which program loads winlogon.exe?
- hal.dll
- winload.exe
- ntoskrnl.exe
- sysprep.exe
22. Which tab would be used to set the priority for a process in Windows 10 Task Manager?
- Details
- Performance
- Startup
- Services
23. Which statement describes a primary partition?
- It is a physical section of a hard disk. It can contain an operating system to boot the system and cannot be subdivided.
- It is a section of an extended partition on an MBR. It can be used to separate information for administrative purposes.
- It is a type of disk with the ability to create volumes that span across more than one disk even if the unallocated space is noncontiguous.
- It is often used to organize data storage by subdividing it into as many as 23 logical sections.
24. Which statement describes formatting?
- It is a process to create a file system in a partition or volume for file storage.
- It is often used to organize data storage by subdividing it into as many as 23 logical sections.
- It is a section of an extended partition on an MBR. It can be used to separate information for administrative purposes.
- It is used to boot an operating system by default.
25. Which statement describes the active partition?
- It is used to boot an operating system by default.
- It is a section of an extended partition on an MBR. It can be used to separate information for administrative purposes.
- It is a type of disk with the ability to create volumes that span across more than one disk even if the unallocated space is noncontiguous.
- It is often used to organize data storage by subdividing it into as many as 23 logical sections.
26. Which statement describes formatting?
- It is a process to create a file system in a partition or volume for file storage.
- It is often used to organize data storage by subdividing it into as many as 23 logical sections.
- It is a section of an extended partition on an MBR. It can be used to separate information for administrative purposes.
- It is a section of the disk, that is inaccessible to the user, containing an image that can be used to restore the computer to its original configuration.
27. Which statement describes the active partition?
- It is used to boot an operating system by default.
- It is a section of the disk, that is inaccessible to the user, containing an image that can be used to restore the computer to its original configuration.
- It is a process to create a file system in a partition or volume for file storage.
- It is a type of disk with the ability to create volumes that span across more than one disk even if the unallocated space is noncontiguous.
28. Which statement describes a recovery partition?
- It is a section of the disk, that is inaccessible to the user, containing an image that can be used to restore the computer to its original configuration.
- It is a process to create a file system in a partition or volume for file storage.
- It is a type of disk with the ability to create volumes that span across more than one disk even if the unallocated space is noncontiguous.
- It is a section of an extended partition on an MBR. It can be used to separate information for administrative purposes.
29. Which statement describes an extended partition?
- It is often used to organize data storage by subdividing it into as many as 23 logical sections.
- It is a section of the disk, that is inaccessible to the user, containing an image that can be used to restore the computer to its original configuration.
- It is a process to create a file system in a partition or volume for file storage.
- It is a type of disk with the ability to create volumes that span across more than one disk even if the unallocated space is noncontiguous.
30. Which statement describes the master boot record (MBR)?
- It takes the first 512 bytes on the disk and contains the boot loader, an executable program that allows a user to choose from multiple operating systems.
- It is a section of the disk, that is inaccessible to the user, containing an image that can be used to restore the computer to its original configuration.
- It is a process to create a file system in a partition or volume for file storage.
- It is a type of disk with the ability to create volumes that span across more than one disk even if the unallocated space is noncontiguous.
31. Which statement describes a logical drive?
- It is a section of an extended partition on an MBR. It can be used to separate information for administrative purposes.
- It is a section of the disk, that is inaccessible to the user, containing an image that can be used to restore the computer to its original configuration.
- It is a process to create a file system in a partition or volume for file storage.
- It is a type of disk with the ability to create volumes that span across more than one disk even if the unallocated space is noncontiguous.
32. Which statement describes the master boot record (MBR)?
- It takes the first 512 bytes on the disk and contains the boot loader, an executable program that allows a user to choose from multiple operating systems.
- It is a process to create a file system in a partition or volume for file storage.
- It is a type of disk with the ability to create volumes that span across more than one disk even if the unallocated space is noncontiguous.
- It is a section of an extended partition on an MBR. It can be used to separate information for administrative purposes.
33. A technician has just purchased a new Windows 10 PC and wants to transfer selected files, folders, profiles, and applications from the old Windows PC. What tool or utility would be the best choice for the user?
- PCmover Express
- Upgrade Assistant
- User State Migration Tool
- Windows Task Manager
34. A manager wants to install Windows 10 directly onto a computer and needs help with the setup process. What tool or utility would be the best choice for the user?
- Upgrade Assistant
- User State Migration Tool
- Windows Easy Transfer
- Windows Boot Manager
35. A technician needs to capture the company user accounts, files, operating system settings, and application settings for migration into the new Windows 10 installation. What tool or utility would be the best choice for the user?
- User State Migration Tool
- Upgrade Assistant
- Windows Easy Transfer
- WinLoad
36. A support technician wants to upgrade a system to Windows 10 but is unsure whether the hardware and software on the existing system are compatible. What tool or utility would be the best choice for the user?
- Get Windows 10 app
- Upgrade Assistant
- User State Migration Tool
- Cortana Virtual Assistant
37. An analyst is running Windows 7 on the PC and is planning to migrate to Windows 8.1. The analyst wants help migrating the personal files and settings into the newer version. What tool or utility would be the best choice for the user?
- Windows Easy Transfer
- Upgrade Assistant
- User State Migration Tool
- Application manager
38. A manager wants to install Windows 10 directly onto a computer and needs help with the setup process. What tool or utility would be the best choice for the user?
- Upgrade Assistant
- Windows Easy Transfer
- PCmover Express
- Windows Boot Manager
39. An analyst is running Windows 7 on the PC and is planning to migrate to Windows 8.1. The analyst wants help migrating the personal files and settings into the newer version. What tool or utility would be the best choice for the user?
- Windows Easy Transfer
- User State Migration Tool
- PCmover Express
- Application manager
40. True or False? A 32-bit operating system can address up to a maximum of 4 GB of RAM.
- True
- False
41. A technician needs to capture the company user accounts, files, operating system settings, and application settings for migration into the new Windows 10 installation. What tool or utility would be the best choice for the user?
- User State Migration Tool
- Windows Easy Transfer
- PCmover Express
- WinLoad
42. A support technician wants to upgrade a system to Windows 10 but is unsure whether the hardware and software on the existing system are compatible. What tool or utility would be the best choice for the user?
- Get Windows 10 app
- User State Migration Tool
- Windows Easy Transfer
- Cortana Virtual Assistant
43. True or False? Smartphones require an operating system before they can be operated.
- True
- False
44. True or False? Modern operating systems boot the computer, manage the file system, and support only one user, task, or CPU.
- False
- True
45. True or False? When a hardware device is installed, the operating system needs to use a device driver to access and use that hardware.
- True
- False
46. True or False? When a user is working on a system that uses a network file system, there is no difference between accessing a file stored locally or on another computer on the network.
- True
- False
47. True or False? Windows 10 64-bit version can be installed on as little as 1GB of hard drive space.
- False
- True
48. True or False? DirectX is a collection of APIs related to multimedia tasks for Microsoft Windows.
- True
- False
49. True or False? The registry is a database that only contains information about the device drivers on a computer.
- False
- True
50. True or False? Multitasking describes a computer operating system that is capable of running multiple applications at the same time.
- True
- False
51. True or False? Multithreading describes an operating system that can support two or more CPUs.
- False
- True
IT Essentials v6.0:
1. What are two ways that iOS differs from Android? (Choose two.)
- iOS uses an All Apps button whereas Android uses a Home button.
- iOS has a physical Home button, but Android uses navigation icons.
- In iOS, the icon for an app represents the app itself. Deleting the icon in iOS deletes the app. In Android, the icon on the Home screen is a shortcut to the app.
- In iOS, apps can only appear on screens, whereas in Android, apps can appear on screens and in folders.
- In iOS, folders are created by dragging one app on top of another app, but in Android folders must be created from the home screen menu.
2. What is a good source for safely downloading Android apps?
- iTunes
- Google Play
- freeware sites
- the Apple App Store
3. Refer to the exhibit. What two statements are true about the operating system screen shown? (Choose two.)
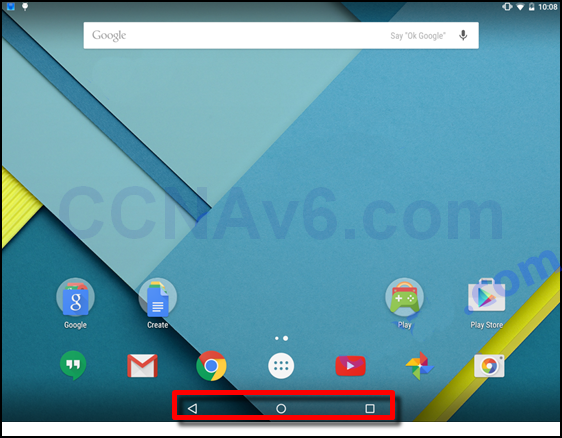
- The area that is highlighted contains navigation icons.
- The area that is highlighted displays background processes and indicators.
- The area that is highlighted contains the system icons.
- This is an Android screen.
- This is an iOS screen.
- This is a Windows Phone screen.
4. A small number has appeared on one of the apps on a user’s iOS home screen. What does this mean?
- It is an alert badge that indicates the number of items requiring attention for that app.
- It indicates the number of instances of the app that are running on the device.
- It indicates how frequently the app has been used within a period of time.
- It indicates the number of items in the app folder.
5. What represents apps in the Windows Phone interface?
- buttons
- icons
- tiles
- widgets
6. What is the name of the Windows Phone 8.1 digital, or virtual, assistant?
- Bing
- Cortana
- Nova Launcher
- Spotlight
7. What is Wi-Fi calling?
- a method used to push apps to smartphones
- a convenient way to securely and digitally make payments with mobile devices
- a government emergency alert service for smartphones
- a way to make mobile phone calls over a wireless data network
- a method for sharing data between two mobile devices
8. What is a benefit of the WEA system?
- It can save lives by sending emergency text messages to mobile phones.
- It can simplify commerce by allowing payments to be made from a mobile phone.
- It is a method of securing a mobile device that has been lost or stolen.
- It allows a user to search for resources that are located near the current location.
9. What are two purposes of the passcode lock feature on mobile devices? (Choose two.)
- to help prevent theft of private information
- to prevent unauthorized use of the device
- to erase all personal data from the device
- to return the device to the default factory state
- to restore and re-synchronize the device
- to remotely lock the device if it is stolen
10. Which two conditions must be met for mobile device security measures such as remote lock and remote wipe to function? (Choose two.)
- The device must be powered on.
- The device must be connected to a network.
- The passcode must be disabled.
- The GPS locator must be enabled.
- Sandboxing must be enabled.
11. Which two location data sources can locator apps use to determine the position of a mobile device? (Choose two.)
- cellular towers
- WiFi hotspots
- the sandbox
- remote lock
- an app source
12. What are two potential user benefits of rooting or jailbreaking a mobile device? (Choose two.)
- The user interface can be extensively customized.
- The operating system can be fine-tuned to improve the speed of the device.
- The root directory of the device is blocked.
- The operation of the carrier cellular network may be affected.
- A custom OS may reduce sandboxing features.
13. Which statement is true about wireless connectivity on an Android mobile device?
- If the network SSID is not being broadcast, the device will not be able to connect to the network.
- When the device roams out of the range of any Wi-Fi networks, it can connect to the cellular data network if this feature is enabled.
- If a Wi-Fi network is secured with a password, the network must be manually configured on the device.
- The Android OS does not support wireless connectivity that uses WPA2 security.
14. In the context of mobile devices, what does the term tethering involve?
- connecting a mobile device to another mobile device or computer to share a network connection
- connecting a mobile device to a hands-free headset
- connecting a mobile device to a 4G cellular network
- connecting a mobile device to a USB port on a computer in order to charge the mobile device
15. Which statement is true about industry standards for cellular networks?
- Cell phones that use a single standard can often only be used in specific geographic areas.
- Cellular standards have made it more difficult and expensive to make calls to people that are on a different network.
- First generation cellular standards are mostly digital standards.
- Third generation cellular standards require a maximum of 1 Gb/s for devices moving slowly, such as when a user has a mobile device and is walking.
16. What will allow someone to use a cell phone for entertainment without connecting to any networks?
- a hotspot
- Bluetooth
- Airplane Mode
- 4G
- WiMax
17. What technology enables a cell phone to be used as a move to trhands-free device?
- Wi-Fi
- Bluetooth
- 4G
- Yosemite
18. A technician is configuring email on a mobile device. The user wants to be able to keep the original email on the server, organize it into folders, and synchronize the folders between the mobile device and the server. Which email protocol should the technician use?
- POP3
- IMAP
- MIME
- SMTP
19. What is the code name used for the OS X 10.10 operating system?
- Ubuntu
- Lollipop
- Aqua
- Yosemite
- Unity
20. What is a purpose of the boot manager program?
- It manages antivirus signature files, encryption keys, and certificates when a device boots.
- It automates the POST and checks the disk for bad sectors during a boot.
- It checks the validity of hardware and software on the device after a factory reset.
- It allows the user to select the OS to use to boot the device.
- It allows the user to determine which apps are automatically opened during the boot process.
21. What is the purpose of signature files used to secure mobile devices and operating systems?
- They contain a record of historical and pending firmware and software updates.
- They contain a list of all user passwords.
- They contain a log of digital certificates and encryption keys associated with the user.
- They contain sample code from known viruses and malware that is used by security software to identify malicious software.
22. A file called new_resume has the following file permissions: rw-r-x–x What two facts can be determined from these permissions? (Choose two.)
- The user has full access to the file.
- Members of the group have read and execute access to the file.
- Other people have read and execute access to the file.
- Group members are able to modify the file.
- The user is able to read and modify the file.
- Other people have no access to the file.
23. What is the result of doing a factory reset on a mobile device?
- The operating system will be updated with the most recent updates and patches.
- All user data and settings will be deleted.
- The operating system will be deleted and all user data is transferred to the Cloud.
- A complete backup of the device is done and all viruses and malware are removed.
24. What tool can be used on a mobile device to display available cellular networks, location of networks, and signal strength?
- Wi-Fi analyzer
- loopback adapter
- cell tower analyzer
- toner generator and probe
25. An administrator is re-imaging a large number of Mac OS X machines. What built-in tool or command can be used to remotely boot the computers?
- mstsc
- Netboot
- Time Machine
- Finder
26. What tool or command is used in the Mac OS X to navigate the file system?
- File Explorer
- Task Manager
- Finder
- mstsc
27. What command is used to open a text editor in Unix-like systems?
- grep
- ifconfig
- ls
- vi
28. Fill in the blank.
Both Linux and OS X devices have a service called cron* that runs in the background and is responsible for executing scheduled tasks.
Older Version
29. A user receives a phone call from a person who claims to represent IT services and then asks that user for confirmation of username and password for auditing purposes. Which security threat does this phone call represent?
- social engineering
- anonymous keylogging
- spam
- DDoS
30. Which two security precautions will help protect a workplace against social engineering? (Choose two.)
- ensuring that each use of an access card allows access to only one user at the time
- ensuring that all operating system and antivirus software is up to date
- encrypting all sensitive data stored on the servers
- performing daily data backups
- registering and escorting all visitors to the premises
31. What are two typical physical security precautions that a business can take to protect its computers and systems? (Choose two.)
- Perform daily data backups.
- Replace any software firewalls with a hardware firewall.
- Implement biometric authentication.
- Ensure that all operating system and antivirus software is up to date.
- Disable the autorun feature in the operating system.
32. Which physical security technology can hold user authentication information, include software license protection, provide encryption, and provide hardware and software authentication that is specific to the host system?
- biometric authentication
- Trusted Platform Module (TPM)
- card key access
- two-factor security
33. It has been noted that the computers of employees who use removable flash drives are being infected with viruses and other malware. Which two actions can help prevent this problem in the future? (Choose two.)
- Set virus protection software to scan removable media when data is accessed.
- Configure the Windows Firewall to block the ports that are used by viruses.
- Enable the TPM in the CMOS settings.
- Repair, delete, or quarantine the infected files.
- Disable the autorun feature in the operating system.
34. In which situation would a computer technician use the fixmbr command at the command prompt of a Windows XP computer to resolve a security issue?
- when unauthorized users have changed the CMOS settings and the CMOS password must be reset
- when a virus has damaged the master boot record of the system disk
- when a virus has damaged the boot sector of the system disk
- when the folder permissions for user members of a group are incorrect
35. All users working with a particular Windows 7 computer are able to install unauthorized software. In addition to educating the users about correct security behavior, which action should also be performed to solve this issue?
- Set the user folder permissions to Deny.
- Disable the users’ accounts.
- Change the user file permissions to Read Only.
- Enable UAC on the computer.
36. You want to dispose of a 2.5 terabyte hard drive that contains confidential financial information. What is the recommended procedure to achieve this?
- Use data wiping.
- Drill through the HDD.
- Smash the platters with a hammer.
- Immerse the HDD in a weak solution of bicarbonate of soda.
37. What is the most effective way of securing wireless traffic?
- WPA2
- SSID hiding
- WEP
- wireless MAC filtering
38. Which two items are used in asymmetric encryption? (Choose two.)
- a token
- a TPM
- a private key
- a DES key
- a public key
39. Which two characteristics describe a worm? (Choose two.)
- hides in a dormant state until needed by an attacker
- infects computers by attaching to software code
- executes when software is run on a computer
- is self-replicating
- travels to new computers without any intervention or knowledge of the user
40. Which type of security threat uses email that appears to be from a legitimate sender and asks the email recipient to visit a website to enter confidential information?
- worm
- phishing
- adware
- stealth virus
41. Which three questions should be addressed by organizations developing a security policy? (Choose three.)
How should future expansion be done?
- What are the possible threats to the assets of the organization?
- What is to be done in the case of a security breach?
- When do the assets need protecting?
- What assets require protection?
- What insurance coverage is required?
42. What does a malware detection program look for when running a scan?
- a service pack
- patterns in the programming code of the software on a computer
- mirror sites
- patches that prevent a newly discovered virus or worm from making a successful attack
43. Port triggering has been configured on a wireless router. Port 25 has been defined as the trigger port and port 113 as an open port. What effect does this have on network traffic?
- Any traffic that is using port 25 going out of the internal network will also be allowed to transmit out port 113.
- All traffic that is sent into port 25 to the internal network will also be allowed to use port 113.
- All traffic that is sent out port 25 will open port 113 to allow inbound traffic into the internal network through port 113.
- Any traffic that comes into port 25 allows outgoing port 113 to be used.
44. Which two characteristics of network traffic are being monitored if a network technician configures the company firewall to operate as a packet filter? (Choose two.)
- packet size
- physical addresses
- protocols
- packet speed
- ports
45. What is the primary goal of a DoS attack?
- to facilitate access to external networks
- to prevent the target server from being able to handle additional requests
- to scan the data on the target server
- to obtain all addresses in the address book within the server
46. Which question would be an example of an open-ended question that a technician might ask when troubleshooting a security issue?
- Have you scanned your computer recently for viruses?
- What symptoms are you experiencing?
- Did you open any attachments from a suspicious email message?
- Is your security software up to date?
47. Which action would help a technician to determine if a denial of service attack is being caused by malware on a host?
- Install rogue antivirus software on the host.
- Log on to the host as a different user.
- Disable ActiveX and Silverlight on the host.
- Disconnect the host from the network.
48. A technician is troubleshooting a computer security issue. The computer was compromised by an attacker as a result of the user having a weak password. Which action should the technician take as a preventive measure against this type of attack happening in the future?
- Ensure the security policy is being enforced.
- Check the computer for the latest OS patches and updates.
- Scan the computer with protection software.
- Verify the physical security of all offices.
Explanation: As part of the fifth step of the troubleshooting process, technicians should apply preventive measures whenever possible. Most company security policies include a section on password complexity and length requirements. Ensuring that this policy is being enforced can help prevent attackers from being able to compromise systems through password cracking.
49. A user has reported that a computer web browser will not display the correct home page even if the default page is reset. What is the likely cause of this problem?
- A virus has damaged the boot sector of the system disk.
- The computer has been infected with spyware.
- UAC has been disabled on the computer.
- Folder permissions have been changed from Deny to Allow.
50. What is the name given to the programming-code patterns of viruses?
- mirrors
- signatures
- virus definition tables
- grayware

¿Cuál de las siguientes afirmaciones describe el formateo?
RESPUESTA
At the end of the boot process of Windows 10, the login program file winlogon.exe loads. Which program loads winlogon.exe ? this is a new question ……..I need the answer now
Answers in here: https://itexamanswers.net/question/at-the-end-of-the-boot-process-of-windows-10-the-login-program-file-winlogon-exe-loads-which-program-loads-winlogon-exe
New question.
Which statement accurately describes the GUID partition table?
It is not supported by Windows 10 Home edition.
It is 512 bytes long and contains the boot loader.
It cannot be used in a multiboot environment.
It is commonly used in computers with UEFI firmware.
It is commonly used in computers with UEFI firmware.This is the right answer
Thanks you:)
At the end of the boot process of Windows 10, the login program file winlogon.exe loads. Which program loads loads winlogon.exe ?
winload.exe
ntoskrnl.exe
hal.dll
sysprep.exe
ntoskrnl.exe
Yo, New question
Which command line utility was developed by Microsoft to allow users to transfer files and settings to a new edition of Windows OS during an upgrade to Windows 10?
Windows Upgrade Assistant
Windows Easy Transfer
PCmover Express
User State Migration Tool
Navigation Bar
windows easy transfer
user state migration tool navigation bar
user state migration tool navigation bar is answer
Windows Easy Transfer
gosto disso…..