Modules 8 – 10: ACLs and Firewalls Group Exam
Network Security (Version 1) – Network Security 1.0 Modules 8-10: ACLs and Firewalls Group Exam Answers
1. When creating an ACL, which keyword should be used to document and interpret the purpose of the ACL statement on a Cisco device?
- remark
- description
- established
- eq
2. Which two pieces of information are required when creating a standard access control list? (Choose two.)
- access list number between 1 and 99
- source address and wildcard mask
- destination address and wildcard mask
- subnet mask and wildcard mask
- access list number between 100 and 199
3. What two steps provide the quickest way to completely remove an ACL from a router? (Choose two.)
- Removal of the ACEs is the only step required.
- Modify the number of the ACL so that it doesn’t match the ACL associated with the interface.
- Copy the ACL into a text editor, add no before each ACE, then copy the ACL back into the router.
- Remove the inbound/outbound reference to the ACL from the interface.
- Use the no access-list command to remove the entire ACL.
- Use the no keyword and the sequence number of every ACE within the named ACL to be removed.
4. Which two types of addresses should be denied inbound on a router interface that attaches to the Internet? (Choose two.)
- private IP addresses
- any IP address that starts with the number 127
- any IP address that starts with the number 1
- NAT translated IP addresses
- public IP addresses
5. In the creation of an IPv6 ACL, what is the purpose of the implicit final command entries, permit icmp any any nd-na and permit icmp any any nd-ns ?
- to allow forwarding of ICMPv6 packets
- to allow automatic address configuration
- to allow IPv6 to MAC address resolution
- to allow forwarding of IPv6 multicast packets
6. What two statements describe characteristics of IPv6 access control lists? (Choose two.)
- They permit ICMPv6 router advertisements by default.
- They can be named or numbered.
- They include two implicit permit statements by default.
- They are applied to an interface with the ip access-group command .
- They use prefix lengths to indicate how much of an address to match.
7. Refer to the exhibit. A network administrator created an IPv6 ACL to block the Telnet traffic from the 2001:DB8:CAFE:10::/64 network to the 2001:DB8:CAFE:30::/64 network. What is a command the administrator could use to allow only a single host 2001:DB8:CAFE:10::A/64 to telnet to the 2001:DB8:CAFE:30::/64 network?
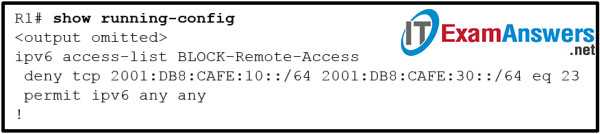
- permit tcp 2001:DB8:CAFE:10::A/64 2001:DB8:CAFE:30::/64 eq 23
- permit tcp 2001:DB8:CAFE:10::A/64 eq 23 2001:DB8:CAFE:30::/64
- permit tcp host 2001:DB8:CAFE:10::A eq 23 2001:DB8:CAFE:30::/64
- permit tcp host 2001:DB8:CAFE:10::A 2001:DB8:CAFE:30::/64 eq 23 sequence 5
8. When implementing components into an enterprise network, what is the purpose of a firewall?
- A firewall is a system that inspects network traffic and makes forwarding decisions based solely on Layer 2 Ethernet MAC addresses.
- A firewall is a system that is designed to secure, monitor, and manage mobile devices, including corporate-owned devices and employee-owned devices.
- A firewall is a system that stores vast quantities of sensitive and business-critical information.
- A firewall is a system that enforces an access control policy between internal corporate networks and external networks.
9. What are two possible limitations of using a firewall in a network? (Choose two.)
- It provides accessibility of applications and sensitive resources to external untrusted users.
- It increases security management complexity by requiring off-loading network access control to the device.
- A misconfigured firewall can create a single point of failure.
- Network performance can slow down.
- It cannot sanitize protocol flows.
10. Which type of firewall makes use of a proxy server to connect to remote servers on behalf of clients?
- stateful firewall
- stateless firewall
- packet filtering firewall
- application gateway firewall
11. How does a firewall handle traffic when it is originating from the public network and traveling to the private network?
- Traffic that is originating from the public network is not inspected when traveling to the private network.
- Traffic that is originating from the public network is usually blocked when traveling to the private network.
- Traffic that is originating from the public network is usually permitted with little or no restrictions when traveling to the private network.
- Traffic that is originating from the public network is selectively permitted when traveling to the private network.
12. Which two statements describe the two configuration models for Cisco IOS firewalls? (Choose two.)
- ZPF must be enabled in the router configuration before enabling an IOS Classic Firewall.
- The IOS Classic Firewall and ZPF cannot be combined on a single interface.
- IOS Classic Firewalls and ZPF models can be enabled on a router concurrently.
- Both IOS Classic Firewall and ZPF models require ACLs to define traffic filtering policies.
- IOS Classic Firewalls must be enabled in the router configuration before enabling ZPF.
13. Designing a ZPF requires several steps. Which step involves dictating the number of devices between most-secure and least-secure zones and determining redundant devices?
- determine the zones
- design the physical infrastructure
- establish policies between zones
- identify subsets within zones and merge traffic requirements
14. When a Cisco IOS zone-based policy firewall is being configured, which three actions can be applied to a traffic class? (Choose three.)
- pass
- shape
- reroute
- queue
- inspect
- drop
15. When using Cisco IOS zone-based policy firewall, where is the inspection policy applied?
- to a global service policy
- to a zone
- to an interface
- to a zone pair
16. What is the first step in configuring a Cisco IOS zone-based policy firewall via the CLI?
- Define traffic classes.
- Assign router interfaces to zones.
- Define firewall policies.
- Assign policy maps to zone pairs.
- Create zones.
17. What is one benefit of using a stateful firewall instead of a proxy server?
- ability to perform user authentication
- better performance
- ability to perform packet filtering
- prevention of Layer 7 attacks
18. Which statement describes a typical security policy for a DMZ firewall configuration?
- Traffic that originates from the DMZ interface is selectively permitted to the outside interface.
- Return traffic from the inside that is associated with traffic originating from the outside is permitted to traverse from the inside interface to the outside interface.
- Return traffic from the outside that is associated with traffic originating from the inside is permitted to traverse from the outside interface to the DMZ interface.
- Traffic that originates from the inside interface is generally blocked entirely or very selectively permitted to the outside interface.
- Traffic that originates from the outside interface is permitted to traverse the firewall to the inside interface with few or no restrictions.
19. What is one limitation of a stateful firewall?
- weak user authentication
- cannot filter unnecessary traffic
- not as effective with UDP- or ICMP-based traffic
- poor log information
20. Which statement describes Cisco IOS Zone-Based Policy Firewall operation?
- The pass action works in only one direction.
- Router management interfaces must be manually assigned to the self zone.
- A router interface can belong to multiple zones.
- Service policies are applied in interface configuration mode.
21. What is the result in the self zone if a router is the source or destination of traffic?
- No traffic is permitted.
- All traffic is permitted.
- Only traffic that originates in the router is permitted.
- Only traffic that is destined for the router is permitted.
22. What are two characteristics of ACLs? (Choose two.)
- Extended ACLs can filter on destination TCP and UDP ports.
- Standard ACLs can filter on source TCP and UDP ports.
- Extended ACLs can filter on source and destination IP addresses.
- Standard ACLs can filter on source and destination IP addresses.
- Standard ACLs can filter on source and destination TCP and UDP ports.
23. Which three statements describe ACL processing of packets? (Choose three.)
- An implicit deny any rejects any packet that does not match any ACE.
- A packet can either be rejected or forwarded as directed by the ACE that is matched.
- A packet that has been denied by one ACE can be permitted by a subsequent ACE.
- A packet that does not match the conditions of any ACE will be forwarded by default.
- Each statement is checked only until a match is detected or until the end of the ACE list.
- Each packet is compared to the conditions of every ACE in the ACL before a forwarding decision is made.
24. A network administrator configures an ACL with the command R1(config)# access-list 1 permit 172.16.0.0 0.0.15.255 . Which two IP addresses will match this ACL statement? (Choose two.)
- 172.16.0.255
- 172.16.15.36
- 172.16.16.12
- 172.16.31.24
- 172.16.65.21
25. What single access list statement matches all of the following networks?
- 192.168.16.0
- 192.168.17.0
- 192.168.18.0
- 192.168.19.0
- access-list 10 permit 192.168.16.0 0.0.3.255
- access-list 10 permit 192.168.16.0 0.0.0.255
- access-list 10 permit 192.168.16.0 0.0.15.255
- access-list 10 permit 192.168.0.0 0.0.15.255
26. Which two characteristics are shared by both standard and extended ACLs? (Choose two.)
- Both kinds of ACLs can filter based on protocol type.
- Both can permit or deny specific services by port number.
- Both include an implicit deny as a final statement.
- Both filter packets for a specific destination host IP address.
- Both can be created by using either a descriptive name or number.
27. Refer to the exhibit. What is the result of adding the established argument to the end of the ACE?
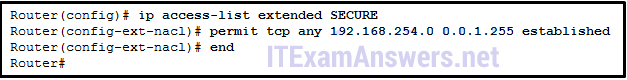
- Any traffic is allowed to reach the 192.168.254.0 255.255.254.0 network.
- Any IP traffic is allowed to reach the 192.168.254.0 255.255.254.0 network as long as it is in response to an originated request.
- 192.168.254.0 /23 traffic is allowed to reach any network.
- Any TCP traffic is allowed to reach the 192.168.254.0 255.255.254.0 network if it is in response to an originated request.
28. Which two keywords can be used in an access control list to replace a wildcard mask or address and wildcard mask pair? (Choose two.)
- most
- host
- all
- any
- some
- gt
29. If the provided ACEs are in the same ACL, which ACE should be listed first in the ACL according to best practice?
- permit ip any any
- permit udp 172.16.0.0 0.0.255.255 host 172.16.1.5 eq snmptrap
- permit tcp 172.16.0.0 0.0.3.255 any established
- permit udp any any range 10000 20000
- deny udp any host 172.16.1.5 eq snmptrap
- deny tcp any any eq telnet
30. To facilitate the troubleshooting process, which inbound ICMP message should be permitted on an outside interface?
- echo request
- echo reply
- time-stamp request
- time-stamp reply
- router advertisement
31. A security specialist designs an ACL to deny access to a web server from all sales staff. The sales staff are assigned addressing from the IPv6 subnet 2001:db8:48:2c::/64. The web server is assigned the address 2001:db8:48:1c::50/64. Configuring the WebFilter ACL on the LAN interface for the sales staff will require which three commands? (Choose three.)
- permit tcp any host 2001:db8:48:1c::50 eq 80
- deny tcp host 2001:db8:48:1c::50 any eq 80
- deny tcp any host 2001:db8:48:1c::50 eq 80
- permit ipv6 any any
- deny ipv6 any any
- ip access-group WebFilter in
- ipv6 traffic-filter WebFilter in
32. What are two characteristics of a stateful firewall? (Choose two.)
- uses static packet filtering techniques
- uses connection information maintained in a state table
- analyzes traffic at Layers 3, 4 and 5 of the OSI model
- uses complex ACLs which can be difficult to configure
- prevents Layer 7 attacks
33. What are two differences between stateful and stateless firewalls? (Choose two.)
- A stateless firewall is able to filter sessions that use dynamic port negotiations while a stateful firewall cannot.
- A stateless firewall will examine each packet individually while a stateful firewall observes the state of a connection.
- A stateless firewall will provide more logging information than a stateful firewall.
- A stateful firewall will prevent spoofing by determining whether packets belong to an existing connection while a stateless firewall follows pre-configured rule sets.
- A stateless firewall provides more stringent control over security than a stateful firewall.
34. When implementing a ZPF, what is the default security setting when forwarding traffic between two interfaces in the same zone?
- Traffic between interfaces in the same zone is selectively forwarded based on Layer 3 information.
- Traffic between interfaces in the same zone is not subject to any policy and passes freely.
- Traffic between interfaces in the same zone is blocked.
- Traffic between interfaces in the same zone is selectively forwarded based on the default policy restrictions.
35. Which two rules about interfaces are valid when implementing a Zone-Based Policy Firewall? (Choose two.)
- If neither interface is a zone member, then the action is to pass traffic.
- If one interface is a zone member, but the other is not, all traffic will be passed.
- If both interfaces belong to the same zone-pair and a policy exists, all traffic will be passed.
- If both interfaces are members of the same zone, all traffic will be passed.
- If one interface is a zone member and a zone-pair exists, all traffic will be passed.

7
Which two statements describe the two configuration models for Cisco IOS firewalls? (Choose two.)