Networking Basics Checkpoint Exam: Protocols for Specific Tasks Answers
1. What information is used by TCP to reassemble and reorder received segments?
- acknowledgment numbers
- fragment numbers
- port numbers
- sequence numbers
2. A PC user issues the netstat command without any options. What is displayed as the result of this command?
- a local routing table
- a list of all established active TCP connections
- a network connection and usage report
- a historical list of successful pings that have been sent
3. Which action is performed by a client when establishing communication with a server via the use of UDP at the transport layer?
- The client sends a synchronization segment to begin the session.
- The client sends an ISN to the server to start the 3-way handshake.
- The client sets the window size for the session.
- The client randomly selects a source port number.
4. Refer to the exhibit. A TCP segment was sent by PC1 to the web server via port 80. Because of an unexpected network failure, the data was forwarded by R1 but was not received by R2. Which statement is correct about this scenario?
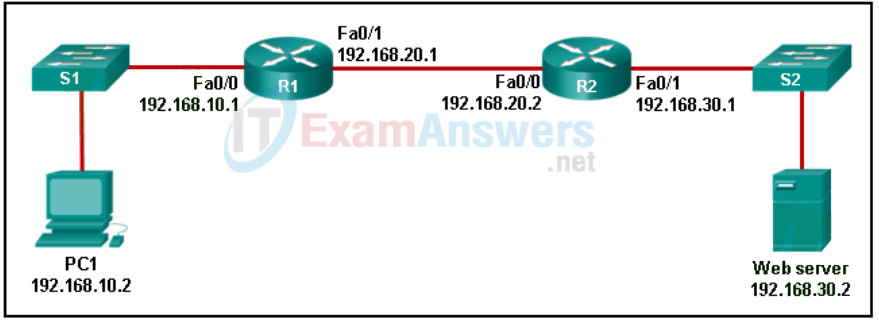
- The web server will not acknowledge this segment. The PC1 timer will expire and PC1 will resend the segment.
- R1 forwarded the data to R2 but R2 did not receive it. R2 will send a request to R1 to resend the segment.
- R1 will request that PC1 resend the segment.
- The timer on R1 will expire and R1 will resend the segment to R2.
5. A destination PC receives an email message with the sequence numbers on packets out of order. Which layer of the TCP/IP model is responsible for reassembling the packets of the message in the correct order?
- application
- network access
- transport
- internet
6. A client device has initiated a secure HTTP request to a web browser. Which well-known port address number is associated with the destination address?
- 404
- 110
- 443
- 80
7. What type of applications are best suited for using UDP?
- applications that need reliable delivery
- applications that are sensitive to delay
- applications that are sensitive to packet loss
- applications that require retransmission of lost segments
8. Match the term to a function.
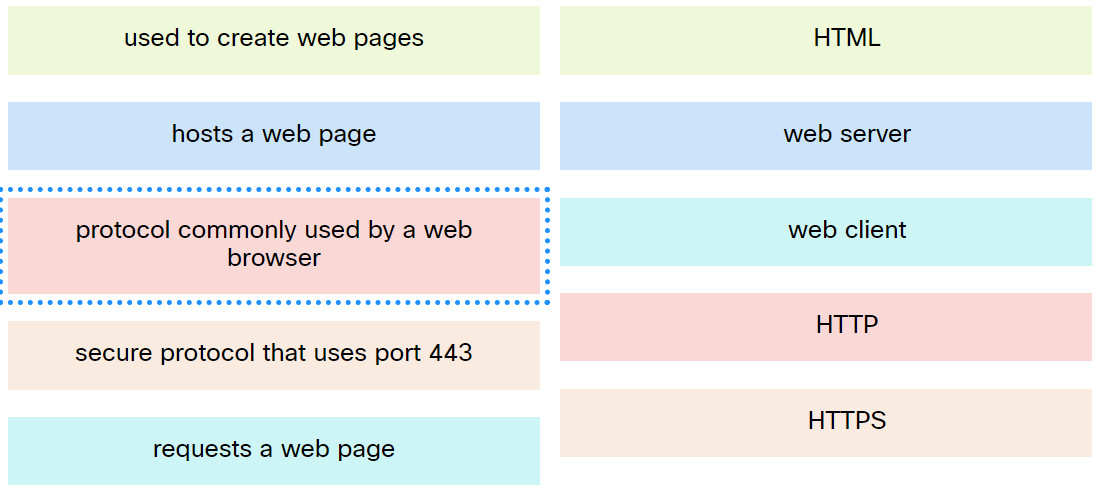
Networking Basics Module 15 – 17 Checkpoint Exam 8
9. Which three pieces of information are identified by a URL? (Choose three.)
- the domain name that is being accessed
- the MAC address of the web server
- the location of the resource
- the protocol that is being used
- the version of the browser
- the IP address of the gateway
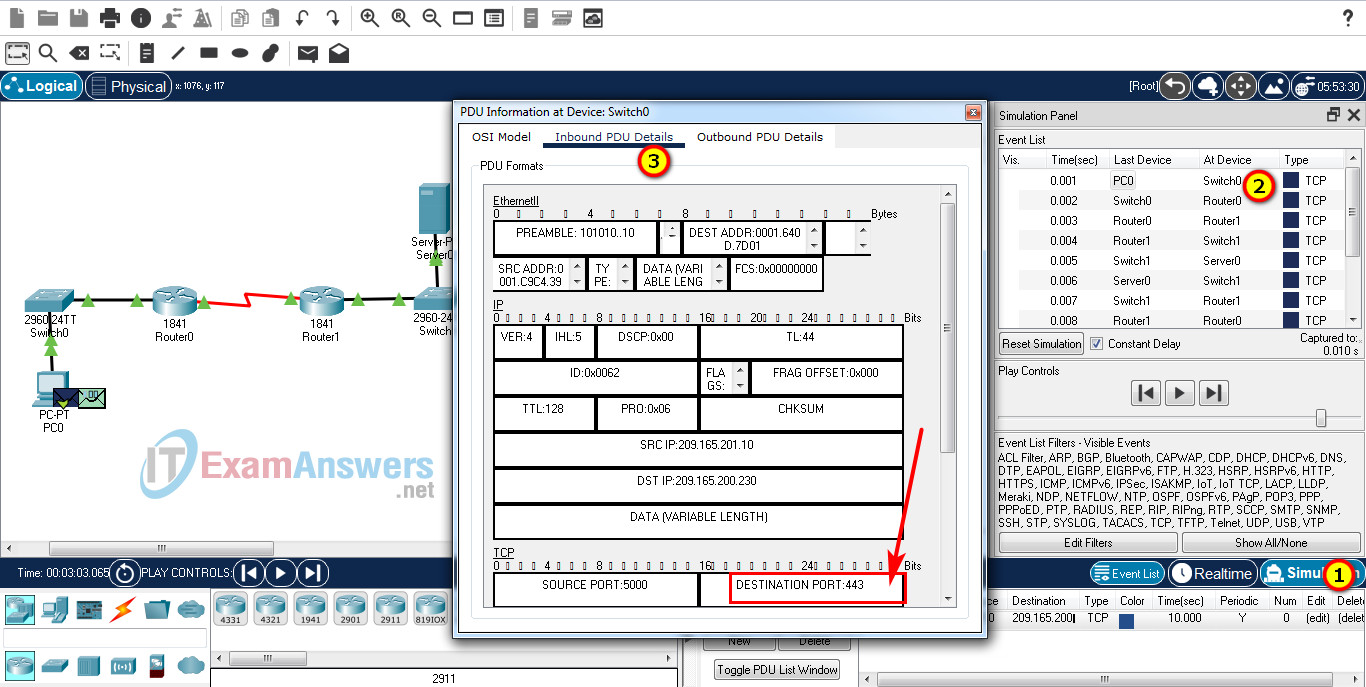
10. Open the PT activity. Perform the tasks in the activity instructions and then answer the question.
What is the application layer service being requested from Server0 by PC0?
- DNS
- FTP
- HTTP
- SMTP
- HTTPS
11. Which number or set of numbers represents a socket?
- 192.168.1.1:80
- 10.1.1.15
- 21
- 01-23-45-67-89-AB
12. A new employee is attempting to configure a cell phone to connect to the email server of the company. Which port number should be selected when using the IMAP4 protocol to access email messages stored on the local server?
- 69
- 25
- 143
- 110
13. Open the PT Activity. Perform the tasks in the activity instructions and then answer the question or complete the task.
Capture traffic in simulation mode. What application layer service is PC-A requesting from the web server?
- TFTP
- SSH
- HTTP
- telnet
- FTP
14. While a network security product is being deployed, a customizable list of allowable protocols is shown. Which three protocols should be allowed to provide for the use of email on a network? (Choose three.)
- Telnet
- TFTP
- POP3
- HTTP
- IMAP4
- SMTP
- DNS
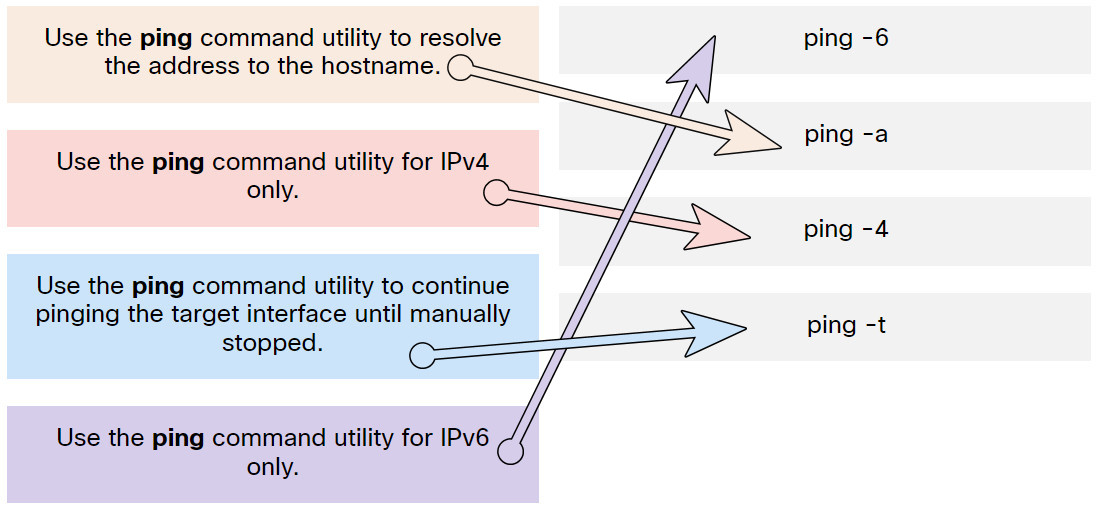
15. Match the command line utility with the description.
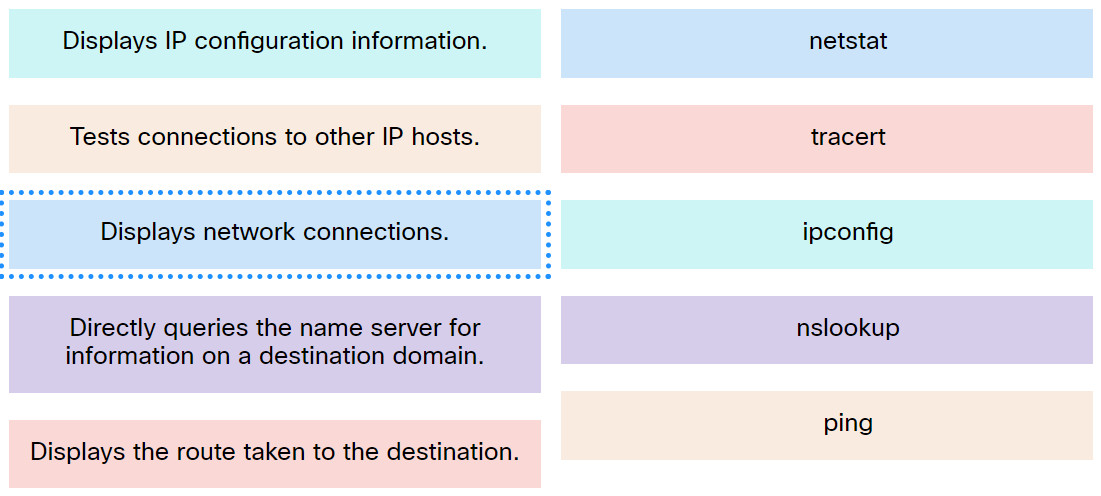
16. Match the command line utility with the function.
17. What is a function of the tracert command that differs from the ping command when they are used on a workstation?
- The tracert command reaches the destination faster.
- The tracert command is used to test the connectivity between two devices.
- The tracert command shows the information of routers in the path.
- The tracert command sends one ICMP message to each hop in the path.
18. A technician is troubleshooting a network where it is suspected that a defective node in the network path is causing packets to be dropped. The technician only has the IP address of the end point device and does not have any details of the intermediate devices. What command can the technician use to identify the faulty node?
- ipconfig /flushdns
- ping
- tracert
- ipconfig /displaydns
19. Which statement describes the use of the ping command?
- The ping command tests end-to-end connectivity between two devices.
- The ping command can be used to determine the exact location of the problem when troubleshooting reachability issues.
- The ping command can be used to test reachability using the physical address of the device.
- The ping command shows current Layer 4 sessions.
20. A computer has been assigned an IP address of 169.254.33.16. What command initiates the process of requesting a new IP address?
- net computer
- nslookup
- tracert
- ipconfig /release