Refer to the exhibit. A network security analyst is examining captured data using Wireshark. The captured frames indicate that a host is downloading malware from a server. Which source port is used by the host to request the download?
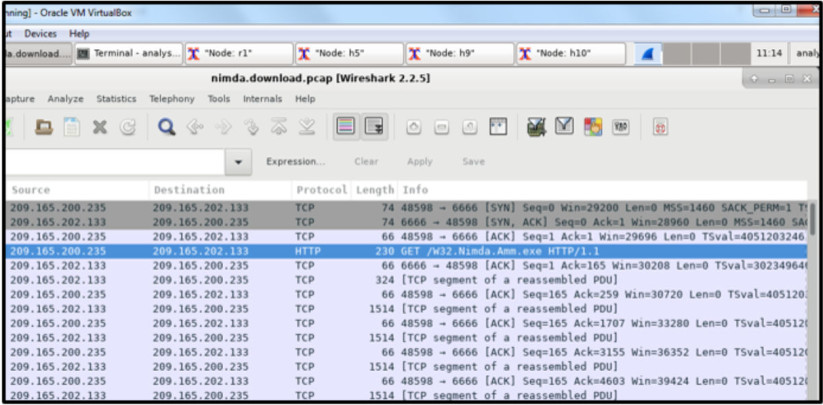
- 66
- 1514
- 6666
- 48598
Explanation: During the TCP three-way handshake process, the output shows that the host uses source port 48598 to initiate the connection and request the download.
Exam with this question: CCNA Cyber Ops Chapter 12 Exam Answers
Exam with this question: Modules 5 - 10: Network Fundamentals Group Exam
Please login or Register to submit your answer
