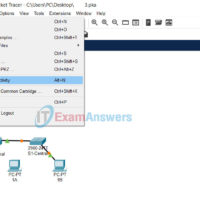
In Packet Tracer, to access the command line interface (CLI) of a Switch or Router, you can use one of the following two ways: The CLI tab Console port The CLI tab This is the simplest way to access the Command Line Interface (CLI) of a Switch/Router. Click …
Use Reset Activity if you want to clear your work, which starts the activity over, or gain more practice. Step 1: Open Activity Packet Tracer .PKA file Step 2: Click File menu > Reset Activity (Alt + N)
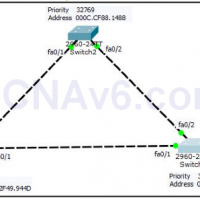
High availability and redundancy is one of the most important factor to enhance the productivity and reputation of an organization. The redundancy can be applied at the various levels such as Server level, Disk-level, and even the network device-level. In this exercise, we will explain the high availability …
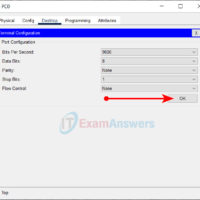
There are many ways to interconnect routers. One of the most popular and traditional way to interconnect routers on a WAN network is using the Serial interfaces. A serial cable has two ends: Data Communication Equipment (DCE) and Data Terminal Equipment (DTE). The DCE end is typically located …
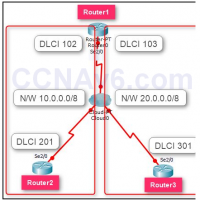
Frame-relay is a WAN technology that supports up to 44.3 Mbps of speed. Nowadays it is not so much popular and heavily replaced by the latest technologies such as ATM. We assume that you know the basics of Frame-relay technology and are familiar with the basic components such …
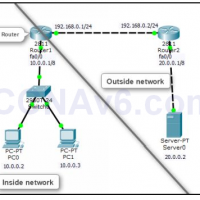
Network Address Translation (NAT) technique translates private IP addresses into public IP addresses. NAT enhances the security of the network by hiding the actual IP information from the external users. The external users see the translated IP addresses rather than actual IP addresses. This is also called masking. …
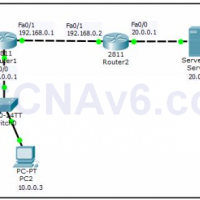
Access Control List (ACL) is a security feature that allows you to filter the network traffic based on configured statements. An ACL can be used to filter either inbound or outbound traffic on an interface. Once you applied an access list on a router, the router examine every …
We know that Spanning-Tree Protocol (STP) help us to prevent to occur switching loop. However, spanning-tree sometime can also create a problem for your network. For example, suppose you have a server that is connected into your switch. You are sure that there are no chances to occur …
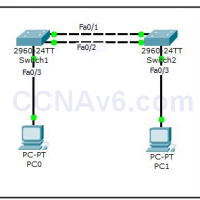
Network loop can create a huge problem in a network. Routing protocols such as RIP and IGRP have their own techniques to stop network loops from occurring at the Network layer of the OSI model. Unfortunately they (routing protocols) cannot be used to stop loops from occurring at …
You can control to access your switch port. For example, you can control who can access a specific interface of a switch or how many devices could be connected to a specific switch interface. There is a feature called Switch Port Security that allow you to do so. …
Etherchannel is a technique that allows you to combine multiple Ethernet switch ports in to a single logical port. Thus help you to combine bandwidth of all port and provide redundancy in case of a single port failure. This technique is also known as NIC Teaming, Link Aggregation, …
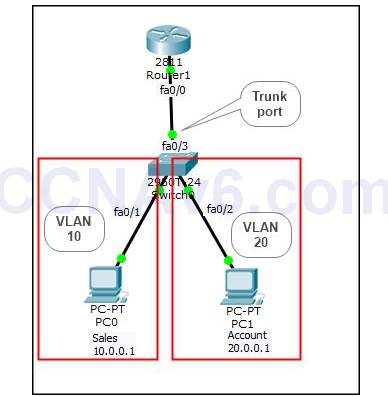
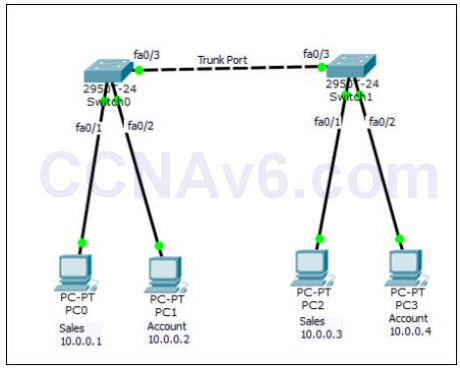
In the previous exercises, we have covered the basics of VLANs and its configuration. As discussed earlier, VLANs are used to separate network traffic, enhance network security, and divide a large network in to several small networks. We know that systems belong to one VLAN cannot communicate to …
Introduction to VLAN VLANs are used to segment a large physical LAN into multiple small virtual LANs for better management and greater security. VLANs provide a number advantages and features. Some of the key features provided by VLANs are: VLANs allow to add, move, and change networks with …
A device can be managed either locally or remotely. There are various protocols, tools, and services (such as Telnet, Secure Shell, and Putty) that are used to manager devices remotely. These tools are also referred as remote administration tools. We will use the following simple topology to configure …