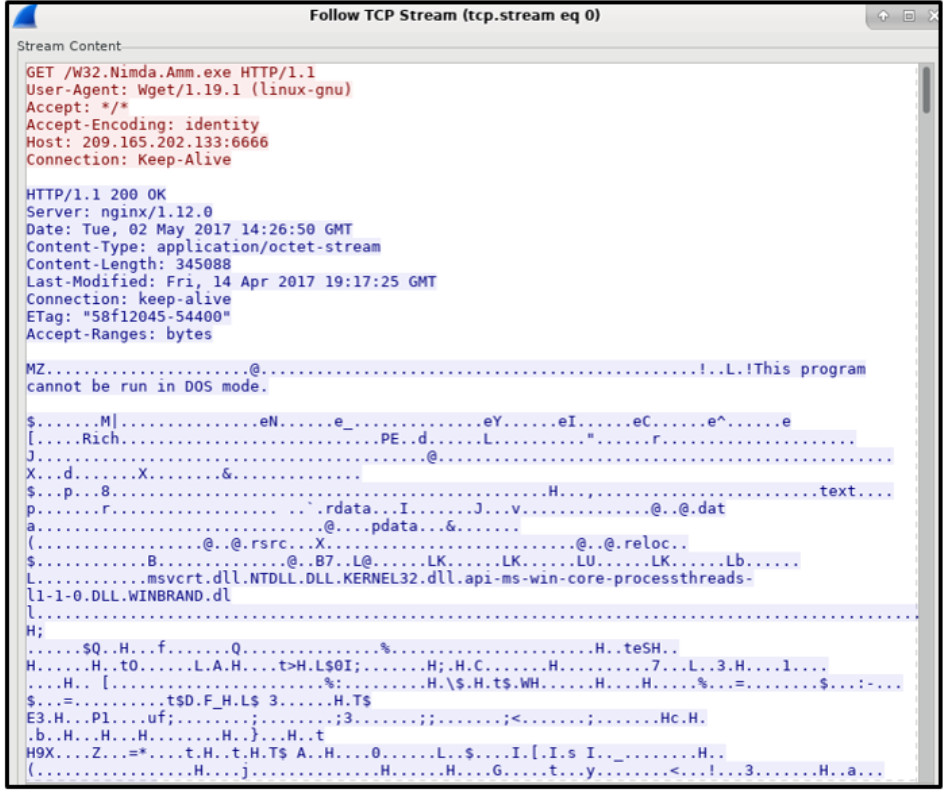
Refer to the exhibit. A network security analyst is using the Follow TCP Stream feature in Wireshark to rebuild the TCP transaction. However, the transaction data seems indecipherable. What is the explanation for this?
- The transaction data is encoded with Base64.
- The transaction data is a binary file.
- The data shown is line noise.
- The transaction data is corrupted.
Explanation: The host is downloading W32.Nimda.Amm.exe, a binary file. Wireshark does not know how to represent it. The displayed symbols are the best guess at making sense of the binary data while decoding it as text.
Exam with this question: CCNA Cyber Ops Chapter 12 Exam Answers
Please login or Register to submit your answer
