Match the security policy with the description. (Not all options are used.)
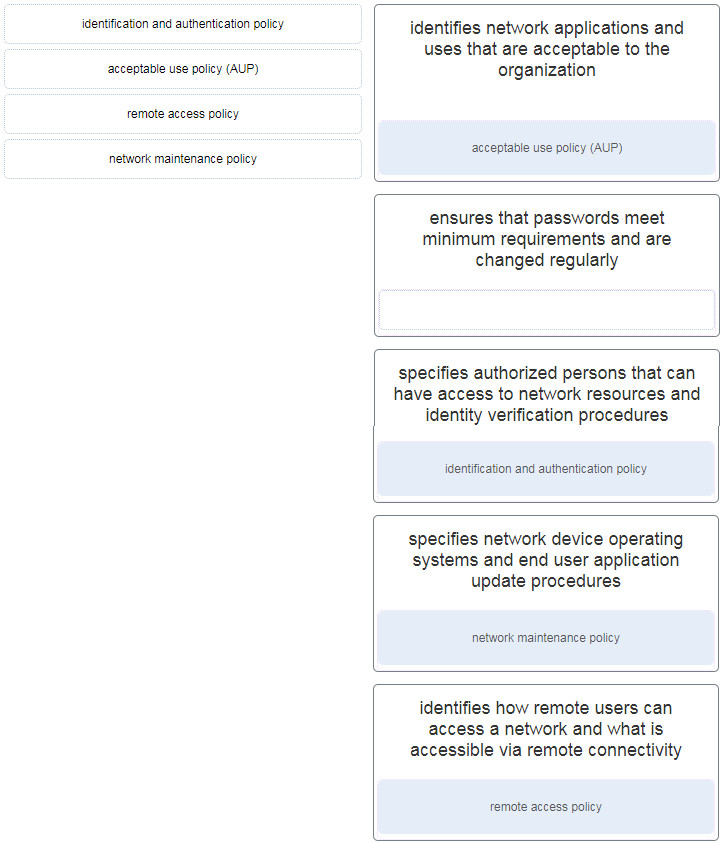
Place the options in the following order:
| identifies network applications and uses that are acceptable to the organization | acceptable use policy (AUP) |
| identifies how remote users can access a network and what is accessible via remote connectivity | remote access policy |
| specifies authorized persons that can have access to network resources and identity verification procedures | identification and authentication policy |
| specifies network device operating systems and end user application update procedures | network maintenance policy |
Exam with this question: CyberOps Associate Course Final Exam Answers
Exam with this question: Network Security 1.0 Practice Final Exam Answers
Exam with this question: Network Defense (NetDef) Course Final Exam Answers
Please login or Register to submit your answer
