Match the server profile element to the description.
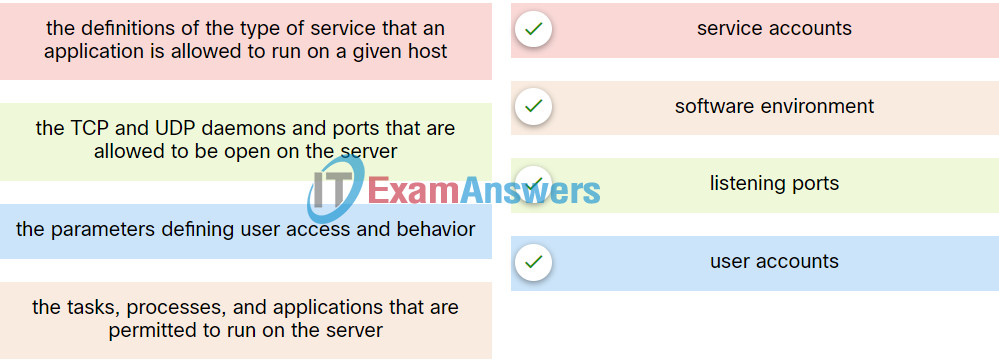
Explanation: Place the options in the following order:
| the parameters defining user access and behavior | user accounts |
| the TCP and UDP daemons and ports that are allowed to be open on the server | listening ports |
| the tasks, processes, and applications that are permitted to run on the server | software environment |
| the definitions of the type of service that an application is allowed to run on a given host | service accounts |
Exam with this question: Cyber Threat Management - 4.4.2 Endpoint Vulnerability Quiz
Please login or Register to submit your answer
