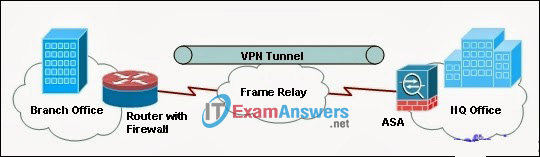
Refer to the exhibit. A VPN tunnel has been established between the HQ Office and the Branch Office over the public Internet. Which three mechanisms are required by the devices on each end of the VPN tunnel to protect the data from being intercepted and modified? (Choose three.)
- The devices must use a dedicated Layer 2 connection.
- The devices must have the VPN client software installed.
- The two parties must inspect the traffic against the same ACLs.
- The two parties must establish a secret key used by encryption and hash algorithms.
- The two parties must agree on the encryption algorithm to be used over the VPN tunnel.
- The devices must be authenticated before the communication path is considered secure.
Exam with this question: CCNA Exploration 4: EWAN Chapter 6 Exam
Please login or Register to submit your answer
