Refer to the exhibit and the following configuration. The named ACL SURFING should enable only the hosts on the 192.168.10.0 network web and secure web access. The hosts on 192.168.11.0 should not be permitted any access. The BROWSING ACL should permit return access only to traffic that originated from the 192.168.10.0 network. However, the ACLs do not accomplish this. Which changes would correct this problem?
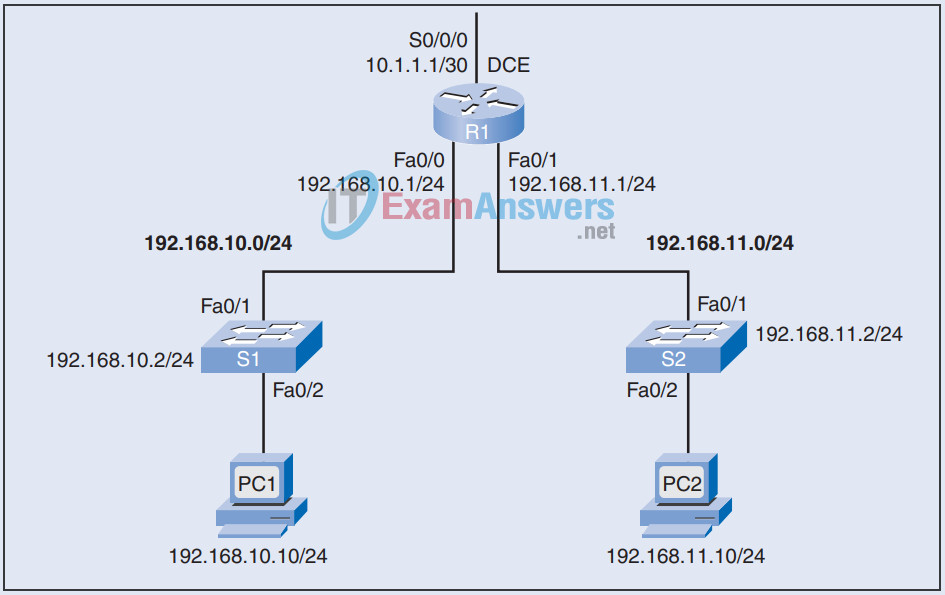
R1(config)# access-list extended SURFING R1(config-ext-nacl)# permit tcp 192.168.10.0 0.0.0.255 any eq 23 R1(config-ext-nacl)# permit tcp 192.168.10.0 0.0.0.255 any eq 443 R1(config)# access-list extended BROWSING R1(config-ext-nacl)# permit tcp any 192.168.10.0 0.0.0.255 R1(config-ext-nacl)# exit R1(config)# interface S0/0/0 R1(config-if)# ip access-group SURFING out R1(config-if)# ip access-group BROWSING in
On router R1:
- The first permit statement of the SURFING ACL allows Telnet access (23). It should permit web access (80).
- The BROWSING ACL requires the established keyword at the end.
Correct configuration:
R1(config)# access-list extended SURFING R1(config-ext-nacl)# permit tcp 192.168.10.0 0.0.0.255 any eq 80 R1(config-ext-nacl)# permit tcp 192.168.10.0 0.0.0.255 any eq 443 R1(config)# access-list extended BROWSING R1(config-ext-nacl)# permit tcp any 192.168.10.0 0.0.0.255 established R1(config-ext-nacl)# exit R1(config)# interface S0/0/0 R1(config-if)# ip access-group SURFING out R1(config-if)# ip access-group BROWSING in
Exam with this question: EWAN v4 Chapter 5 Check Your Understanding: Access Control Lists
Please login or Register to submit your answer
