1. A wireless DHCP client cannot connect to the Internet through a Linksys integrated router. When you type ipconfig on the host, no IP address, subnet mask, or default gateway shows. What are two of the first things you will check? (Choose two.)
- SSID
- the cable between client and integrated router
- the firewall configuration on the integrated router
- if the correct default gateway is configured on the client
- if the wireless client is configured for DHCP
- if the correct default gateway is configured on the integrated router
2. When acting as a DHCP server, an integrated router can provide what three types of information to a client? (Choose three.)
- physical address
- MAC address
- static IP address
- dynamic IP address
- DNS server address
- default gateway
3. Where do ISPs get the public addresses that they assign to end users?
- ISPs create the addresses themselves.
- ISPs obtain address blocks from registry organizations.
- ISPs are assigned addresses through the RFC.
- ISPs obtain their addresses automatically.
4. What are two advantages of purchasing a custom-built computer? (Choose two.)
- user can specify higher performance components
- usually a lower cost
- no waiting period for assembly
- supports higher-end graphics and gaming applications
- fewer components to replace
5. What is a service pack?
- an access policy
- an agreement between a company and a vendor
- a piece of code created to fix one specific problem
- a collection of patches and updates released by a vendor
- a small piece of software designed specifically for security issues
6. Refer to the graphic. What feature can be installed on the Linksys integrated router to convert private IP addresses to Internet-routable addresses?
- authentication
- DHCP
- NAT
- encryption
- firewall
- WEP
7. Which attribute must be the same for wireless devices on one network to be able to communicate with devices on a different network?
- DNS server
- MAC address
- operating system
- wireless equipment vendor
- default gateway
8. What is an ISP?
- It is an organization that allows individuals and businesses to connect to the Internet.
- It is a standards body that develops cabling and wiring standards for networking.
- It is a protocol that establishes how computers within a local network communicate.
- It is a networking device that combines the functionality of several different networking devices in one.
9. Which two statements correctly describe Media Access Control (MAC) addresses? (Choose two.)
- MAC addresses are used to identify a specific NIC.
- MAC addresses are physical addresses.
- MAC addresses contain a network number and unique host identification.
- MAC addresses are always assigned to network devices by a network administrator.
- MAC addresses can be dynamically assigned.
10. What are two ways that a user can interact with an operating system shell? (Choose two.)
- CLI
- OS
- NIC
- GUI
- kernel
11. Select the connection that would require a straight-through cable.
- a switch to a hub
- a switch to a switch
- a router to a router
- a router to a switch
12. Choose the option that shows the correct sequence of steps in the encapsulation of TCP/IP data that is passed from a source to a destination host?
A. converts data to bits for transmission
B. packages the data for end to end transport
C. adds the data-link header and trailer
D. adds the network IP address to the header of the frame
- A,B,C,D
- A,C,D,B
- B,D,C,A
- B,C,D,A
- D,C,B,A
13. How does a crossover cable make it possible for two “like devices” (for example, two switches) to communicate?
- The transmit pins are disconnected and only the receive pins are used.
- The transmit pins on one device are connected to the receive pins on the other device.
- The transmit pins on one device are connected to the transmit pins on the other device.
- The receive pins on one device are connected to the receive pins on the other device.
14. What is specified by the network number in an IP address?
- the physical identity of the computer on the network
- the node of the subnetwork which is being addressed
- the network to which the host belongs
- the broadcast identity of subnetwork
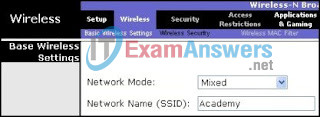
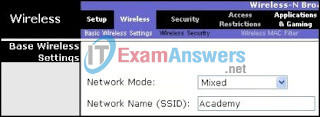
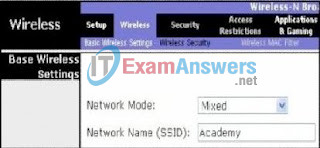
15. Refer to the graphic. What is the purpose of assigning a Network Name of Academy?
- It allows access to the AP configuration GUI by name rather than address.
- It identifies the wireless LAN.
- It translates IP addresses into easy-to-remember domain names.
- It encrypts data between the wireless client and the access point.
- It translates an internal address or group of addresses into an outside, public address.
16. Which of the following statements best describes DNS?
- DNS servers are used to map an IP address to a physical address.
- DNS servers are used to translate from private addresses to public addresses.
- DNS servers are used to map a name to an IP address.
- DNS servers are used to configure logical address information for host computers.
17. Which of the following are the address ranges of the private IP addresses? (Choose three.)
- 10.0.0.0 to 10.255.255.255
- 172.16.0.0 to 172.31.255.255
- 192.168.0.0 to 192.168.255.255
- 27.16.0.0 to 127.31.255.255
- 200.100.50.0 to 200.100.25.255
- 150.150.0.0 to 150.150.255.255
18. Which protocol is used to transfer files among network devices and perform file-management functions?
- HTML
- DNS
- FTP
- HTTP
19. Select three statements that correctly describe how DHCP services may be provided. (Choose three.)
- An integrated router can act as both DHCP server and DHCP client.
- A home PC using a static IP address obtained that address from a DHCP server.
- Most home network integrated routers receive an IP configuration directly from their ISP.
- A variety of devices can act as DHCP servers, as long as they run DHCP service software.
- An integrated router provides IP configurations for most ISPs.
- A home PC is required by standards to obtain an IP address and default gateway from a DHCP server (usually the ISP).
20. Refer to the graphic. Based on the information that is shown, what statement is true?
- This configuration would be commonly found in an ad hoc wireless network.
- All wireless devices that are connected to this access point must have an assigned SSID of Academy.
- In addition to accepting wireless client requests, this access point must connect to the wired network.
- Any wireless client that is attached to this access point would have the same IP address and SSID.
21. What is the purpose of a router?
- to maintain a table of individual host addresses
- to select the best path to reach remote networks
- to forward broadcasts to all interfaces so that all hosts receive them
- to physically connect multiple hosts that belong to the same network
22. Identify two causes of physical layer network problems. (Choose two.)
- logical addressing issues
- cables plugged into wrong ports
- incorrect MAC address assigned
- packets received out of sequence
- improperly terminated cables
- incorrect subnet mask on an interface
23. What are the two possible values for a digital bit? (Choose two.)
- 0
- #
- 1
- A
- F
- 9
24. An administrator is troubleshooting a network problem that involves the inability of users to reach Internet sites. During troubleshooting, the administrator is able to successfully ping web sites by their IP address, but pings to domain names are unsuccessful. Which service is most likely at fault?
- DHCP
- DNS
- FTP
- NAT
25. TCP/IP data transmission between the source and destination host is de-encapsulated in four steps:
A. The TCP header is removed.
B. Bits are decoded and the destination MAC address is recognized.
C. The IP header is removed and the contents are passed to the next layer.
D. The Ethernet header and trailer are removed.
What is the correct sequence of these steps?
- A, B, C, D
- A, C, B, D
- B, C, D, A
- B, D, C, A
- C, A, B, D
26. What are two examples of peripheral input devices? (Choose two.)
- external modem
- barcode reader
- printer
- digital camera
- plotter
27. What are three examples of logical configuration information used when planning a network implementation? (Choose three.)
- physical device location
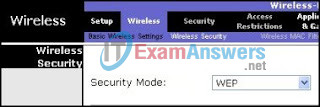
- location of power outlets
- size of broadcast domains
- naming scheme
- length of cable runs
- IP addressing scheme
28. Refer to the exhibit. What is the effect of setting the security mode to WEP on the Linksys integrated router?
- It identifies the wireless LAN.
- It allows the access point to inform clients of its presence.
- It translates IP addresses into easy-to-remember domain names.
- It translates an internal address or group of addresses into an outside, public address.
- It encrypts data between the wireless client and the access point.
- It ensures that only authorized users are allowed access to the WLAN.
29. What is the name for the contract between a customer and an ISP that specifies requirements for uptime and service response time?
- DSL
- IAB
- NAP
- SLA
30. What information within a data packet does a router use, by default, to make forwarding decisions?
- the destination host name
- the destination service requested
- the destination MAC address
- the destination IP address
31. When are leased lines typically used?
- when low bandwidth is required
- as a less expensive option to cable and DSL modem service
- for home and small business connectivity
- when a dedicated digital data line is necessary
32. Which wireless protocol is used for encryption?
- EAP
- PSK
- WEP
- Open
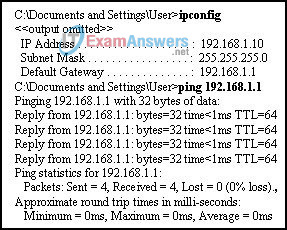
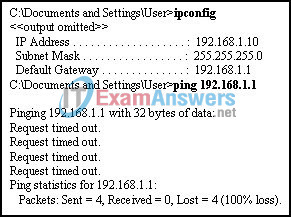
33. Refer to the graphic. Assume that the command output is from a wireless DHCP client that is connected to a Linksys integrated router. What can be deduced from the output?
- The DHCP configuration on the router needs to be checked.
- The wireless NIC driver or the NIC itself needs to be reinstalled.
- The wireless connection is good.
- The WEP key or SSID needs to be checked.
34. The area covered by a single AP is known as what?
- ad-hoc network
- basic service set
- independent basic service set
- extended service set
- distribution system
35. What layer is the first point of entry for a host into the network?
- core layer
- access layer
- network layer
- distribution layer
36. Which installation option should be chosen when the current operating system is too damaged to work properly?
- upgrade
- virtualization
- multi-boot
- clean install
37. What two commands can be used to form a new binding if client information does not agree with the DHCP client table? (Choose two.)
- ipconfig /flushdns
- ipconfig /renew
- ipconfig
- ipconfig /release
- ipconfig /all
38. Which part of the electromagnetic spectrum is commonly used to exchange data between a PDA and a computer?
- FM
- radar
- infrared
- ultraviolet
39. Which of the following are transport layer protocols of the TCP/IP model? (Choose two.)
- FTP
- UDP
- SMTP
- TFTP
- TCP
40. For the second time in a week, workstations on a LAN are not able to log into the server. The technician fixed the problem the first time, but cannot remember the steps taken to solve it. What aspect of the troubleshooting process has the technician neglected?
- identifying the problem
- using structured techniques to solve a problem
- asking end-users questions
- documenting the troubleshooting process
41. What action will a router take when it receives a frame with a broadcast MAC address?
- It will not forward the frame to another network.
- It forwards the frame back to the sending host with its IP address as a response.
- It forwards the frame out of all interfaces except the interface where the frame was received. **
- It forwards the frame back out the receiving interface to insure all hosts on the local network receive it.
42. A network host is accessing a web server. What two protocols are most likely being used as the TCP/IP model application layer protocol and the internetwork layer protocol? (Choose two.)
- IP
- FTP
- TCP
- DHCP
- HTTP
43. Which statement is true concerning stateful packet inspection?
- Access is permitted only if the type of application that is attempting to reach the internal host is allowed.
- Access is permitted only if it is a legitimate response to a request from an internal host.
- Access is permitted based on IP addresses of the source and destination devices.
- Access is permitted based on the MAC addresses of the source and destination devices.
44. What is the default subnet mask for a class B address?
- 255.0.0.0
- 255.255.0.0
- 255.255.255.0
- 255.255.255.255
45. Refer to the graphic. Based on the configuration information that is shown, which three types of 802.11 networks are allowed access to the WLAN? (Choose three.)
- 802.11a
- 802.11b
- 802.11e
- 802.11g
- 802.11n
- 802.11x
46. Within a local network, which two items must be unique on a computer for it to successfully connect to the network? (Choose two.)
- IP address
- subnet mask
- operating system version
- computer name
- default gateway address
47. What measurement is commonly used to describe communication speed when transferring data?
- bps
- cps
- Hz
- MB
48. When considering the purchase of a new operating system, what is meant by “Total Cost of Ownership?”
- applications and support costs
- hardware and support costs
- hardware and software costs
- hardware, software, and support costs
- hardware, operating system, and applications costs
49. A computer joins the network and announces itself to all hosts on the LAN. What type of message does the computer send out?
- broadcast
- simulcast
- multicast
- unicast
50. Which three statements are true about local and network applications? (Choose three.)
- A local application is loaded in a local computer and can be accessed by a remote computer on the network.
- An example of a local application is e-mail.
- An example of a network application is instant messaging.
- A network application is loaded in a local computer and accessed from a remote computer.
- A local application is loaded in a local computer and accessed only by the local computer.
- A network application is loaded in a local computer and accessed only by the local computer.
51. What type of computer would most likely use a docking station?
- laptop
- server
- desktop
- mainframe
- workstation
52. Bottom-up troubleshooting begins at which layer of the OSI model?
- data link layer
- transport layer
- application layer
- network layer
- physical layer
53. Which two statements are true about local applications? (Choose two.)
- They run on the network.
- An example of a local application is e-mail.
- They run on the computer where they are installed.
- They are accessed from a remote computer.
- They are stored on the local hard disk.
54. Refer to the exhibit. What default gateway address will be assigned to PC1 if access to remote resources is needed?
- 192.168.1.101
- 192.168.1.253
- A default gateway is not necessary.
- 192.31.7.3
55. How do ISPs obtain public IP addresses?
- They obtain the addresses from the Internet registry.
- They obtain the addresses from the RFC.
- They create the addresses themselves.
- They obtain the addresses from the home PCs.
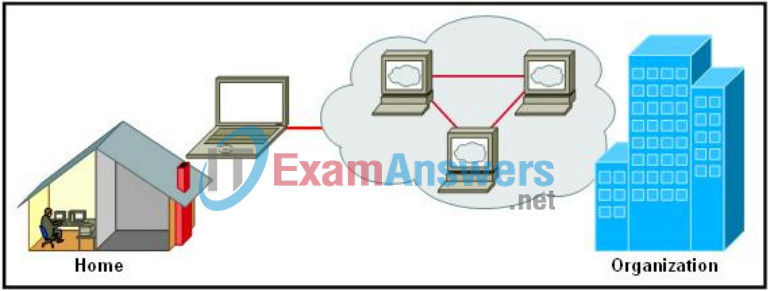
56. Refer to the exhibit. The security policy of an organization allows employees to connect to the office intranet from their homes. Which type of security policy is this?
- acceptable use
- incident handling
- network maintenance
- remote access
57. Which wireless component allows wireless clients to gain access to a wired network?
- PDA
- STA
- access point
- wireless bridge
58. Which network design layer provides a connection point for end user devices to the network?
- access
- core
- distribution
- network
59. Which two transport layer protocols are used to transfer messages between hosts? (Choose two.)
- SMTP
- TCP
- DHCP
- FTP
- UDP
60. What is an accurate description of network devices in the distribution layer?
- They are designed to interconnect individual hosts.
- They are designed to interconnect multiple companies.
- They are designed to interconnect local network segments.
- They are designed to switch data packets as fast as possible.
61. When terminating UTP cabling, why is it important to untwist only a small amount of each wire pair?
- ensures wires are in correct order
- makes it easier to fit wires into connector
- minimizes crosstalk
- makes installation faster
62. A host sent a message that all other hosts on the local network received and processed. What type of domain are all these hosts a part of?
- collision domain
- broadcast domain
- local domain
- multicast domain
63. Your school network blocks all websites related to online gaming. What type of security policy is being applied?
- identification and authentication
- remote access
- acceptable use
- incident handling
64. A company has a web server that must be accessible to both external and internal clients. Which security policy best practice should be followed to maximize security of the server?
- Place the web server in a DMZ.
- Keep the web server on the external network.
- Configure a firewall device to serve as the web server.
- Locate the web server in the server farm of the internal network.
65. Refer to the graphic. Assume that the exhibited output is from a host that is connected to a Linksys integrated router. What is one of the first things you should check?
- IP address on the host
- IP address on the router
- subnet mask on the host
- default gateway on the host
- link status LED on the front of the router
66. What are two examples of storage peripheral devices? (Choose two.)
- printer
- external DVD
- barcode reader
- flash drive
- headphones
67. Which value represents the host portion of IP address 128.107.10.11 with a subnet mask of 255.255.0.0?
- .10
- .10.11
- 128.107
- .107.10.11
- 128.107.10
68. A home user is looking for an ISP connection that provides high speed digital transmission over regular phone lines. What ISP connection type should be used?
- satellite
- cell modem
- DSL
- dial-up
- cable modem
69. What is the purpose of pop-up blocker software?
- It detects and removes spyware.
- It detects and removes viruses.
- It prevents the display of advertisement windows.
- It removes unwanted e-mail.
70. Refer to the exhibit. PC1 is unable to access the web server at 209.165.200.226/27. Based on the provided output, what is the most likely cause of the problem?
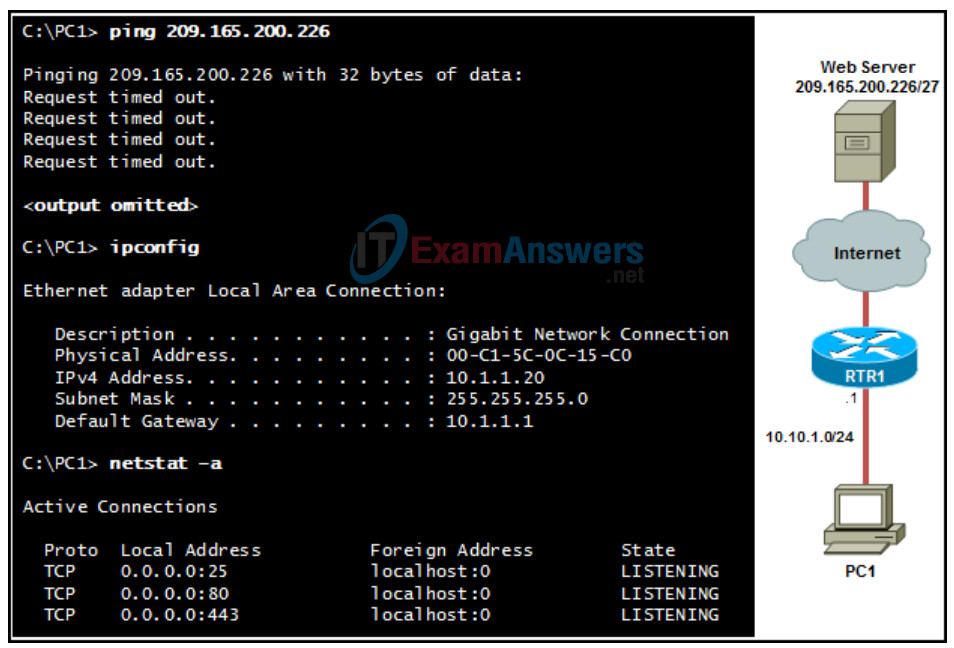
- PC1 is not plugged in to RTR1.
- Port 80 is already in use on PC1.
- No DNS server is configured on PC1.
- PC1 is configured with an incorrect IP address and default gateway.
71. Which term is associated with logical addressing?
- IP addresses
- port addresses
- physical addresses
- Media Access Control addresses
72. Which Windows PC command line utility can be used to discover the path that a packet takes to reach a destination?
- ping
- netstat
- tracert
- nslookup
- ipconfig
73. Which statement accurately describes what network devices do in the distribution layer of the three layer design model?
- They interconnect individual hosts.
- They interconnect the company network to the ISP.
- They interconnect multiple companies.
- They interconnect local network segments.
74. Which two causes of networking problems are related to the physical layer? (Choose two.)
- disconnected cables
- improper operation of cooling fans
- incorrect MAC address
- incorrect default gateway
- incorrect subnet mask
75. What two pieces of information should a help desk technician document while troubleshooting connectivity issues with an end user? (Choose two.)
- if the user can ping the default gateway address
- if the word processing software is installed correctly
- the CPU clock speed of the computer
- the number of network jacks that are in the room
- whether the PC uses dynamic or static IP addressing
76. After attaching four PCs to the switch ports, configuring the SSID and setting authentication properties for a small office network, a technician successfully tests the connectivity of all PCs that are connected to the switch and WLAN. A firewall is then configured on the device prior to connecting it to the Internet. What type of network device includes all of the described features?
- switch
- ISR router
- firewall appliance
- standalone wireless access point
77. What is the default subnet mask for an IP address of 64.100.19.14?
- 255.255.255.0
- 255.255.255.255
- 255.0.0.0
- 255.255.0.0
78. What will be one result of using a wireless infrastructure when designing the communications infrastructure for a new building?
- Wireless devices will be easy to add or relocate.
- Infrastructure installation will be difficult and expensive.
- There will be less interference from outside electronic sources.
- Data transmitted over wireless networks will be more secure than when transmitted over wired networks.
79. Which type of computer has an integrated mouse?
- mainframe
- server
- pocket PC
- desktop
- laptop
80. What does the term “attenuation” mean in data communication?
- loss of signal strength as distance increases
- time for a signal to reach its destination
- leakage of signals from one cable pair to another
- strengthening of a signal by a networking device
81. Which Windows command is used to display the configured IP address, subnet mask, and default gateway?
- netstat
- nslookup
- ipconfig
- tracert
82. What must be identical on all devices in a WLAN for successful wireless communication between the devices?
- SSID
- antenna type
- network mode
- wireless NIC driver
83. For devices that do not autosense, which connection requires a crossover cable?
- PC to switch port
- PC port to PC port
- hub port to router port
- PC to hub port
84. Refer to the exhibit. A user on Host1 requests a web page from the web server. Which diagram is accurate for the encapsulation of the traffic that is sent from the user to the web server?
ONBEKEND> Waarschijnlijk D
85. Which two components are configured via software in order for a PC to participate in a network environment? (Choose two.)
- MAC address
- IP address
- kernel
- shell
- subnet mask
86. What destination IP address is used in a unicast packet?
- a group of hosts
- all hosts on the network
- a specific host
- the network broadcast address
87. What describes the external IP address that is obtained by a router through a cable or DSL modem?
- a public address that is obtained from ICANN
- a private address that is manually configured by the administrator
- a public address that is obtained through DHCP from the ISP
- a private address that converts to a public address on the internal LAN
88. Which picture shows a USB port on a PC?
*deze moet je toch echt weten..
89. A network engineer wants to represent confidential data in binary format. What are the two possible values that the engineer can use? (Choose two.)
- 0
- 1
- 2
- A
- F
90. Refer to the exhibit. A user on host A sends an e-mail to the user on host B. Which type of message does host A send?
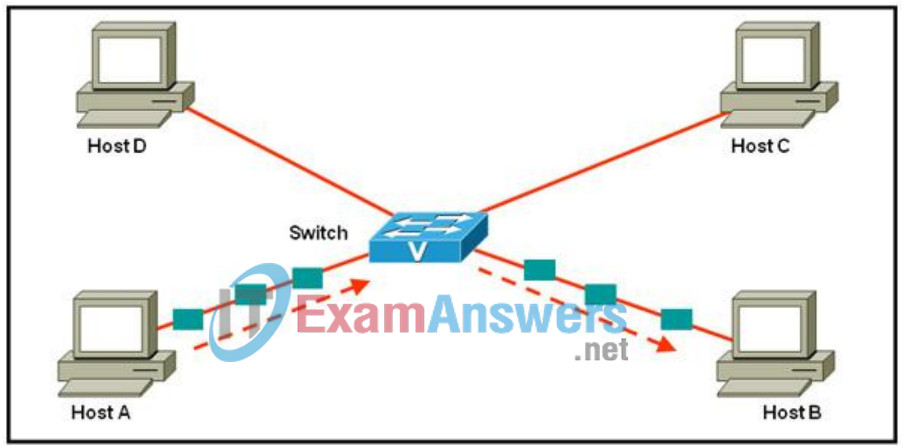
- broadcast
- multicast
- simulcast
- unicast
91. All hosts within a domain receive the same frame that originates from one of the devices. The domain is also bounded by routers. What type of domain is this?
- broadcast
- collision
- local
- multicast
92. Which three statements describe an IP address? (Choose three.)
- An IP address is known as a logical address.
- An IP address uses a 30-bit addressing scheme.
- An IP address is found in the Layer 2 header during transmission.
- The network portion of an IP address is burned into a network interface card.
- An IP address is unique within the same local network.
- The network portion of an IP address will be the same for all hosts that are connected to the same local network.
93. What is a function of the distribution layer in the hierarchical design model?
- to provide latency free switching
- to organize end devices in small manageable groups
- to provide connectivity using the high-speed backbone
- to provide connectivity between smaller local networks
94. For the TCP/IP model for internetwork communication, which statement describes the process for the transition of data from the internet layer to the network access layer?
- An IP packet is encapsulated in a frame.
- A TCP segment is placed in an IP packet.
- HTML data is encapsulated in a TCP segment.
- A frame is placed on the network media as encoded bits.
95. In IP telephony, what is the purpose of a gateway to the PSTN?
- to connect IP voice clients to Internet phone service
- to create a peer-to-peer connection between two IP voice clients
- to map unique names of IP voice endpoints to a client list on a voice server
- to allow IP voice clients to communicate with regular analog telephones.
96. TCP/IP data transmission between the source and destination host is encapsulated in four steps:
A. adds the data-link header and trailer;
B. converts data to bits for transmission;
C. adds the network IP address to the header of the packet;
D. segments the data for end-to-end transport.
What is the correct sequence of these steps?
- A, B, C, D
- A, D, B, C
- B, D, A, C
- D, C, A, B
- D, C, B, A
97. A home user was successfully browsing the Internet earlier in the day but is now unable to connect. A ping command from a wireless laptop to a wired PC in the LAN is successful, but the nslookup command fails to resolve a website address. The user decides to analyze the LEDs on the Linksys router to verify connectivity. Which LED should be of main concern in this situation?
- WLAN LED
- power LED
- Internet LED
- 1-4 Ethernet LEDs
98. Which portion of the packet does a router use to forward the packet to the destination?
- source IP address
- user data
- destination IP address
- control information
- destination MAC address
99. Refer to the exhibit. H1 can ping H2, H3, and the Fa0/0 interface of router R1. H2 and H3 but not H1 can ping H4 and H5. What is a possible cause for the H1 failure?
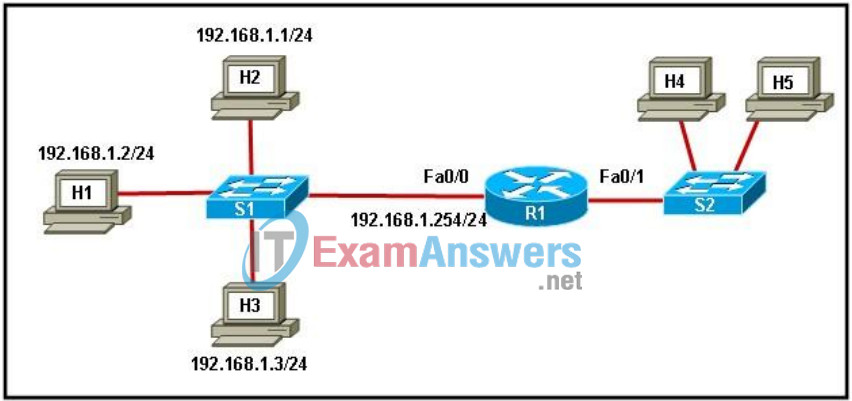
- Router R1 has no route to the destination network.
- Switch S1 does not have an IP address configured.
- The link between router R1 and switch S2 has failed.
- Host H1 does not have a default gateway configured.
100. A network administrator has been notified that users have experienced problems gaining access to network resources. What utility could be used to directly query a name server for information on a destination domain?
- ping
- tracert
- netstat
- ipconfig
- nslookup
101. Under what circumstance would it be appropriate to use private IP addresses?
- for communication between two ISPs
- for a network that is directly connected to the Internet
- for addresses that are used exclusively within an organization.
- for a host with more than one direct connection to the Internet
102. After issuing the ipconfig/all command on a host that has DHCP enabled, a network administrator notes that the output contains faulty IP configuration information. What is the first step the administrator should take to resolve this issue?
- Replace the NIC in the host.
- Change the IP address of the DHCP server.
- Use static addressing to assign the correct IP address.
- Use the release and renew options supported by the ipconfig command.
103. Which three address ranges can be used to depict private IP addresses? (Choose three.)
- 10.0.0.0 to 10.0.0.255
- 127.16.0.0 to 127.16.255.255
- 150.150.0.0 to 150.150.255.255
- 172.16.1.0 to 172.16.1.255
- 192.168.22.0 to 192.168.22.255
- 200.100.50.0 to 200.100.50.255
104. For an IP address, what component decides the number of bits that is used to represent the host ID?
- default-gateway
- host number
- network number
- subnet mask
105. What is the purpose of creating a DMZ during network firewall implementation?
- to create a server security zone accessible only to internal clients
- to create a dirty zone that allows all inbound and outbound traffic
- to allow for a publicly accessible zone without compromising the internal network
- to specify a higher security level than normally required for the internal production network
106. Refer to the exhibit. An educational institution needs to connect PC systems that use private IP addressing to the Internet. They have multiple systems that need to access the Internet, but were only able to purchase one public IP address. What should be activated on the Linksys integrated router to achieve this goal?

- authentication
- DHCP
- encryption
- firewall
- NAT
- WEP
107. Which adapter card would be required for a PC to exchange information with other PCs on a LAN?
- NIC
- video card
- sound card
- internal modem
108. Some new features are available for the OS that is currently running on a user’s PC. What method should be chosen so that the user can install these new feature sets?
- clean install
- multi-boot
- upgrade
- virtualization
109. What is true about a wireless access point that is equipped with an omnidirectional antenna?
- concentrates signal in one direction
- typically used in bridging applications
- radiates the signal equally in all directions
- provides the greatest transmission distance of all antenna types that are used by APs
110. Which device is often configured to act as both a DHCP client and a DHCP server?
- home PC
- ISP modem
- wireless-enabled laptop
- integrated services router
111. A local PC has the correct configuration that is required to access the network. A ping command that is sourced at the PC does not receive a response from a remote device. Which operating system command might be used to determine where the connection failed?
- netstat
- tracert
- ipconfig
- nslookup
112. What type of cable would be required to connect a Linksys router to a wired PC?
- crossover cable
- rollover cable
- serial cable
- straight-through cable
113. What data communication technology uses low-power radio waves to transmit data?
- copper cable
- fiber optic cable
- wireless
- radio
114. How does a straight-through cable connect two unlike devices?
- It connects the receive pins on the first device to the receive pins on the second device.
- It connects the transmit pins on the first device to the receive pins on the second device.
- It disconnects the transmit pins and uses only the receive pins.
- It uses the same pins for transmitting and receiving.
115. When terminating a UTP cable, why is it important to push the wires all the way into the end of the connector?
- to allow the cable to endure more stretching or twisting
- to ensure good electrical contact
- to ensure that the wires are in correct order
- to minimize crosstalk
116. A college network administrator is planning a wireless LAN to provide service in the student lounge and outdoor patio. The requirements include a range of at least 80 meters and a speed of 30 Mb/s. Which wireless LAN standard meets these requirements?
- 802.11
- 802.11a
- 802.11b
- 802.11g
117. Which two causes of networking problems are related to the physical layer? (Choose two.)
- damaged cables and connectors
- incorrect addressing
- incorrect subnet mask
- overheated components
- incorrect default gateway
118. Because of an increasing number of users, bandwidth per user on a WLAN has decreased to a point where users are complaining about poor performance. What can be done to improve the user experience?
- Increase the AP radio signal strength.
- Place the AP in a more central location.
- Deploy an external omni-directional antenna.
- Reduce the number of devices using each channel.
119. A network technician suspects that malware on a user PC is opening multiple TCP connections to a specific foreign host address. Which Windows command line utility can be used to confirm the multiple TCP connections?
- ping
- netstat
- tracert
- ipconfig
- nslookup
120. A network administrator wishes to deploy a small network without using static IP addresses on employee workstations. However, all employees need Internet access. Which two of these services must be configured to meet network requirements? (Choose two.)
- FTP
- DHCP
- HTTPS
- NAT
- HTTP
121. What are two characteristics of a MAC address? (Choose two.)
- It indicates the physical location of the host within the network.
- It is dynamically assigned by a DHCP server.
- It is displayed in HEX characters.
- It is a physical address.
- It is cable-based.
122. What type of message is sent to a specific group of hosts?
- static
- unicast
- dynamic
- multicast
- broadcast
123. Refer to the exhibit. How many additional hosts can be added to the local network?
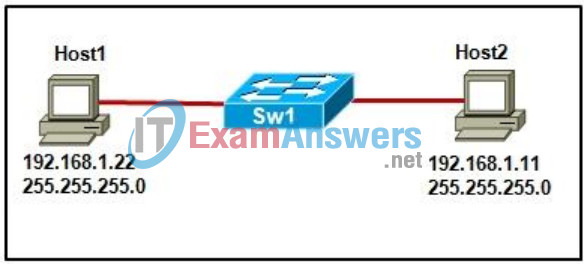
- 124
- 126
- 252
- 254
- 255
- 256
124. What is an advantage of purchasing a custom-built computer?
- It is beneficial for less knowledgeable consumers.
- The waiting period for assembly is negligible.
- The cost is lower compared to a computer that has been preassembled.
- The user can specify high-performance components to meet specific needs.
125. Which type of network supports DHCP and DNS services for network users in a network domain?
- client/server
- peer-to-peer
- hierarchical
- ad hoc
126. A network designer is working with a small company to determine the network type best suited to the needs of the company. Which two characteristics could the designer use to describe a peer-to-peer network to the owner of the company? (Choose two.)
- central administration
- easy to install
- low cost
- scalable
- secure
127. Refer to the exhibit. PC1 sends a data packet to PC4. When the router forwards the data out Fa0/1, what destination MAC address will the router place in the frame?
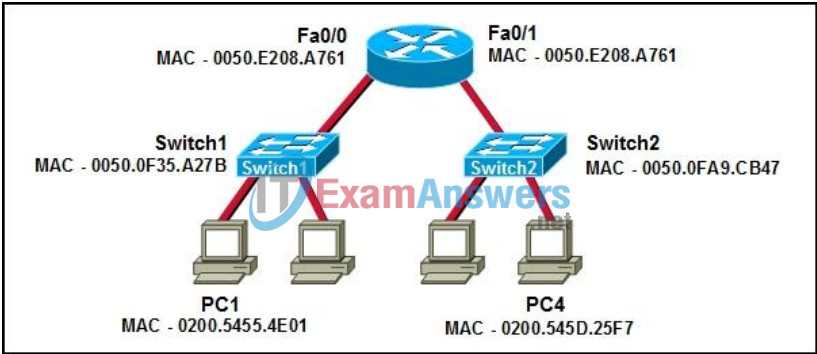
- 0050.0FA9.CB47
- 0050.E208.A761
- 0200.5455.4E01
- 0200.545D.25F7
128. Using both an IP address and name, a network technician successfully pings a remote server. However, all attempts to access a resource on the server fail. What is a possible cause for this failure?
- The server is off line.
- The DNS server is down.
- The requested service is not running.
- A route to the server has not been established.
129. During the process of establishing communications between two hosts, what occurs after a switch finds the destination MAC address in its MAC address table?
- A permanent circuit is established between the source and destination ports.
- The switch builds a temporary connection between the source and destination ports.
- The switch maps the destination MAC address to a destination IP address before forwarding the frame.
- All hosts that are attached to the switch will receive the messages that are passed between the source and destination ports.
130. Which two values represent the network number and default mask for the address 209.165.200.225? (Choose two.)
- 209.0.0.0
- 209.165.0.0
- 209.165.200.0
- 255.0.0.0
- 255.255.0.0
- 255.255.255.0
131. What portion of the destination IP address is used as a packet is routed through the Internet?
- subnet mask
- host portion
- network portion
- default gateway address
132. Which three addresses belong to the category of private IP addresses? (Choose three.)
- 10.0.0.1
- 128.0.0.1
- 150.0.0.1
- 172.16.0.1
- 192.168.31.19
- 172.168.31.1
133. Which statement is true about packet filtering?
- It recognizes and filters specific types of attacks.
- It permits access based on IP address.
- It is performed from a host network device.
- It translates an internal address or group of addresses into a public address that is sent across the network.
134. Which wireless authentication method uses the same key for the AP and the client?
- EAP
- Open
- PSK
- WEP
135. What component of a personal computer is responsible for the processing of all data?
- RAM
- CPU
- firewall
- system bus
- operating system
136. How does a crossover cable connect two routers?
- It connects the pins that are used for receiving on one router to the pins that are used for receiving on the other router.
- It connects the pins that are used for transmitting on one router to the pins that are used for receiving on the other router.
- It disconnects the transmit pins and uses only the receive pins.
- It uses the same pins for transmitting and receiving.
137. What is the purpose of the ipconfig /release command?
- It forces a client to give up its current IP address.
- It forces a client to give up its current MAC address.
- It forces the client to clear all the MAC address to IP address associations it has learned.
- It shows the current IP configuration on the client.
138. Refer to the exhibit. Which statement is true based on the configuration shown?
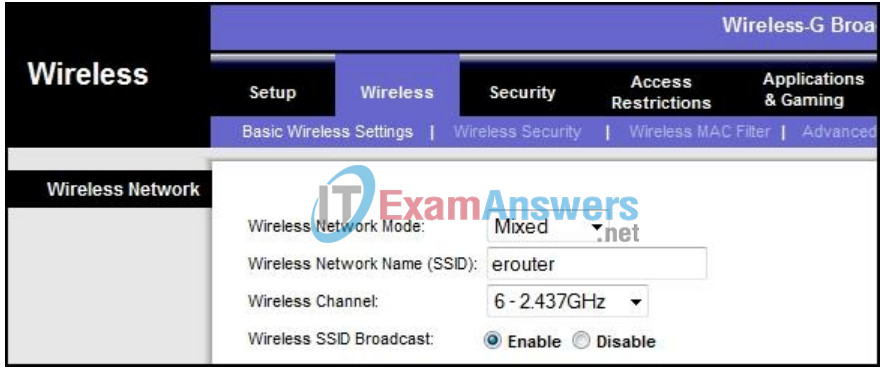
- Multiple modes of encryption are configured on this device.
- Both 802.11b and 802.11g hosts can connect to this device.
- All APs in the WLAN will allow wireless connections via channel 6.
- The network name must be entered on a host computer before the host connects to this network.
139. What is an advantage of selecting an operating system that has a GPL license over one with a commercial license?
- The GPL license-based operating system ensures that everyone can participate in the enhancement of the product.
- The GPL license-based operating system implements a structured development life cycle.
- The GPL license-based operating system prevents modification of the source code.
- The GPL license-based operating system provides structured support.
140. Refer to the exhibit. A ping command that was initiated from the local PC to the file server at IP address 209.165.201.5 succeeded. However, a ping that was initiated from the file server to the local PC was unsuccessful. What could cause the ping command that was initiated from file server to fail?
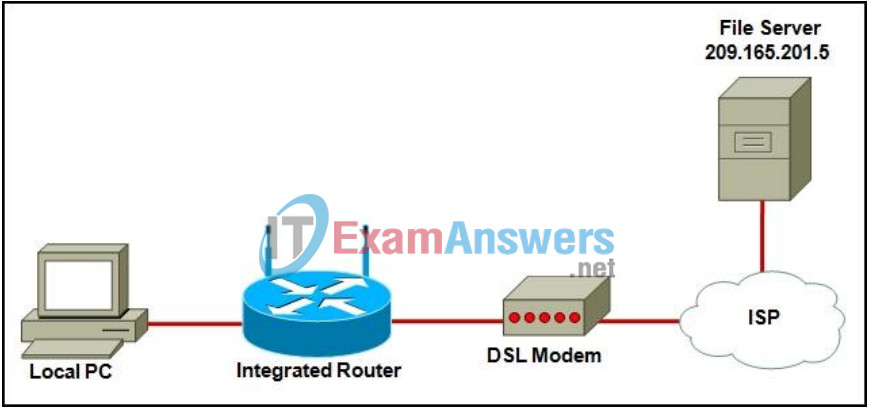
- The file server is down.
- The integrated router has failed.
- NAT has been enabled on the integrated router.
- A security measure is blocking access that initiates from the server.
- The DSL modem failed to provide an IP address for the local PC.
141. A user has reported a failure to connect to the network. Based on similar calls from other users in the same location, the network technician starts troubleshooting by entering the ipconfig command on the user computer. Which troubleshooting technique is the technician using?
- top-down
- bottom-up
- substitution
- divide-and-conquer
142. As an assignment, a computer science student needs to present data in binary format. What are the two possible values that the student can use? (Choose two.)
- 0
- 1
- 2
- A
- F
143. Which two transport layer protocols enable hosts to communicate and transfer data? (Choose two.)
- DHCP
- ICMP
- IP
- TCP
- UDP
144. Which protocol in its default configuration downloads e-mail messages to the client computer and deletes them from the server?
- FTP
- POP3
- SMTP
- IMAP4
145. Which two automatic addressing assignments are supported by DHCP? (Choose two.)
- local server address
- subnet mask
- default gateway address
- physical address of the recipient
- physical address of the sender
146. What is the function of the DNS server?
- It assigns IP addresses to clients.
- It accepts HTTP requests from clients.
- It maps a hostname to a corresponding IP address.
- It manages the domain that clients are assigned to.
147. What destination port number would be used if a client wished to establish a secure connection to a web server?
- 21
- 53
- 80
- 443
148. Refer to the exhibit. If H4 sends a message to H1 and the destination MAC address is in the MAC table for both Switch1 and Switch2, which host devices will receive the message?
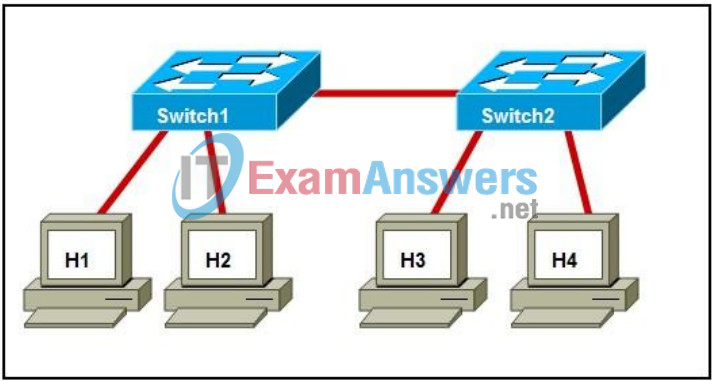
- only H1
- hosts H1 and H4
- all hosts that are connected to Switch1
- all hosts that are connected to Switch1 and Switch2
149. What statement describes the filtering of traffic via the use of Stateful Packet Inspection?
- It recognizes and filters predefined URLs
- It permits access that is based on the application.
- It permits access based on IP or MAC addresses.
- It permits incoming packets that are legitimate responses to requests from internal hosts.
- It translates an internal address or group of addresses into a public address that is sent across the network.
150. Which two statements are true about network applications? (Choose two.)
- Microsoft Word is an example of a network application.
- Network applications are accessible from a remote computer.
- Network applications are installed on a special type of computer that supports only network applications.
- Network applications are installed on a network server.
- Network applications are accessible by one computer at a time.
151. Which network entity would most likely be configured as both a DHCP client and a DHCP server?
- ISP
- desktop PC
- wireless laptop
- PC-based server
- integrated services home router
152. What is one purpose of using logical addresses in an IP network?
- They identify a specific NIC on a host device by assigning a permanent logical address.
- They are used to determine which host device accepts the frame.
- They provide vendor-specific information about the host.
- They are used to determine the network that the host is located on.
- They are used by switches to make forwarding decisions.
153. A network technician is required to provide access to the Internet for a large company. What is needed to accomplish this task?
- ISP
- private IP addresses for each host
- static IP addresses for each host
- DHCP server
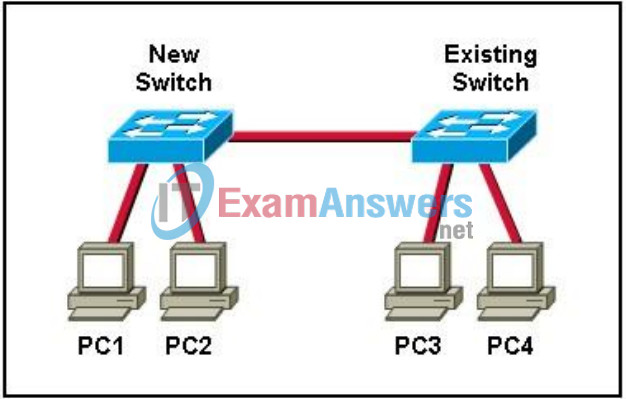
154. Refer to the exhibit. A new switch is connected to an existing switch that has a fully populated MAC table. PC1 requires the destination MAC address of PC3 in order to send a message. Which device or devices will see the ARP sent by PC1?
- only PC3
- PC2 and PC3
- PC3 and PC4
- PC2, PC3 and PC4
155. What is one function of network devices in the distribution layer of a hierarchical network design?
- They control the traffic between independent local networks.
- They control the traffic between individual hosts.
- They control the traffic between multiple companies.
- They switch data packets as fast as possible.
156. What is the default subnet mask for the IP address 128.107.23.10?
- 255.0.0.0
- 255.255.0.0
- 255.255.255.0
- 255.255.255.255
157. What wireless technology has the ability to communicate with many devices at the same time, makes use of the 2.4 GHz band, and is limited to low-speed, short-range communications?
- RF
- ISM
- infrared
- Bluetooth
158. Refer to the exhibit. A PC is requesting a web page from a server on the Internet through a router running NAT. What combination of destination IP address and destination port number will the web server use when replying to this request?
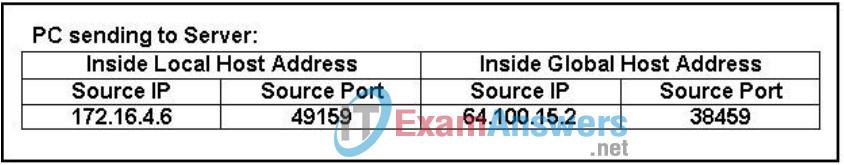
- 64.100.15.2, 38459
- 64.100.15.2, 49159
- 172.16.4.6, 38459
- 172.16.4.6, 49159
159. Refer to the exhibit. Assume that the exhibited output is from a host that is connected to a Linksys integrated router. What is the first thing that should be checked if using a bottom-up troubleshooting approach?
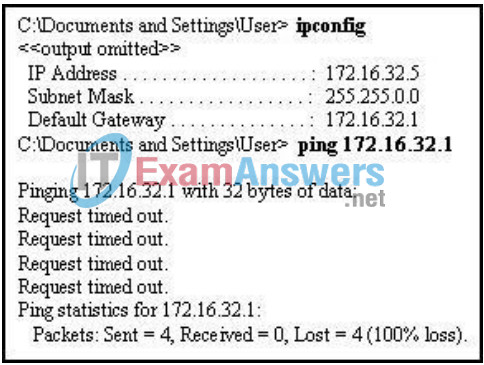
- the default gateway on the host
- the IP address on the host
- the IP address on the router
- the link status LED on the front of the router
- the subnet mask on the host
160. Refer to the exhibit. A small office uses an ISR to provide connectivity for both wired and wireless computers. One day, a sales person who is using a laptop cannot connect to Server1 through the wireless network. A network technician attempts to determine if the problem is on the wireless or the wired network. The technician pings successfully from the wireless laptop to the default gateway IP address on the ISR. What should be the next troubleshooting step?
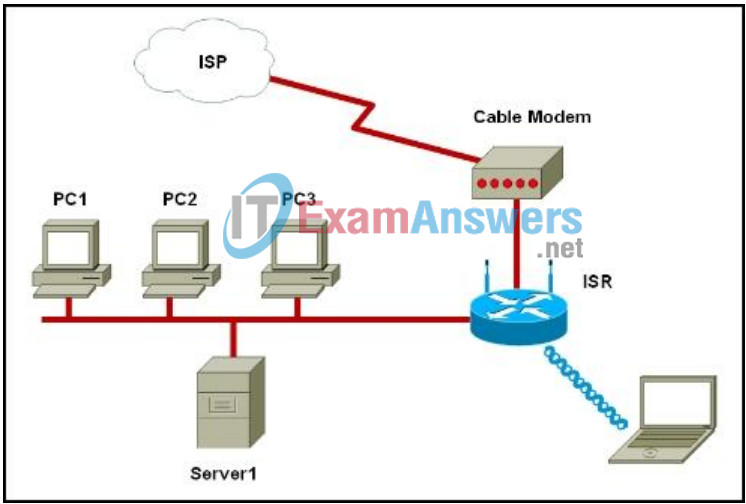
- Ping from the laptop to PC1.
- Ping from Server1 to PC1.
- Ping from Server1 to its gateway IP address.
- Ping from the laptop to the Ethernet port on the cable modem.
161. Which two IP configuration components does the computer use to identify its subnetwork? (Choose two.)
- default gateway
- IP address
- MAC address
- DNS server address
- subnet mask
162. A user in a small office is unable to connect to the Internet. The user examines the physical connections to the ISR, a Linksys WRT300N, and notices a solid green LED on the port that is wired to the computer. What does the LED indicate about the current state of the port?
- The ISR is making adjustments to the port.
- The device is plugged in and traffic is flowing.
- The computer is plugged in but no traffic is flowing.
- The ISR does not detect that the computer is plugged in.
163. Refer to the exhibit. A wireless client is unable to connect to a Linksys WRT300N access point that is using network 192.168.1.0/24its LAN and WLAN clients. What could cause the problem?
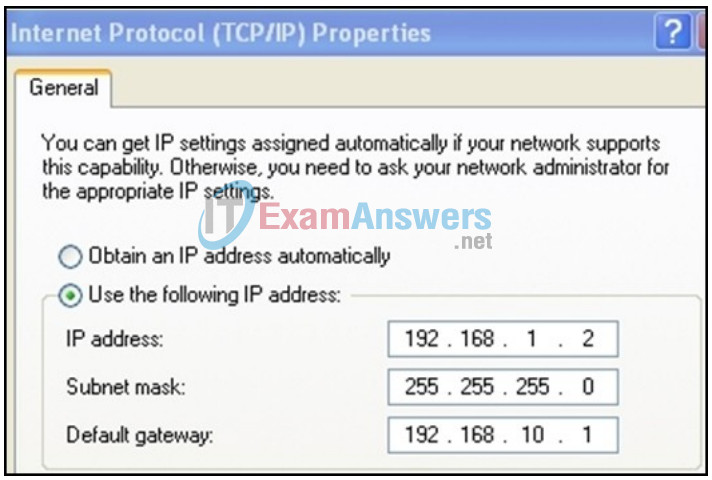
- The IP address is incorrect.
- The subnet mask is incorrect.
- The default gateway is incorrect.
- All addresses are correct, so the SSID must be incorrect.
164. Refer to the exhibit. What is the effect of setting the security mode to WEP on the Linksys integrated router?

- The WEP security mode enables the AP to inform clients of its presence.
- The WEP security mode encrypts network traffic during transmission between the AP and the wireless client.
- The WEP security mode generates a dynamic key each time a client establishes a connection with the AP.
- The WEP security mode identifies the WLAN.
165. A system administrator routinely monitors failed login attempts on a server. If the administrator sees an extremely high number of faattempts by a single user who is trying multiple password combinations, what type of attack is in progress?
- brute force
- phishing
- SYN flood
- virus
- vishing
166. What is the function of a physical topology map?
- records IP addressing of each host
- records hostnames and applications
- organizes groups of hosts by how they use the network
- shows where wiring is installed and the locations of network devices
