Category: CCNA Discovery v4
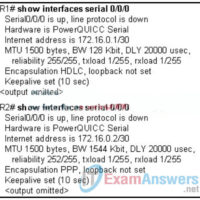
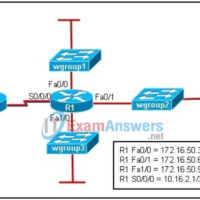
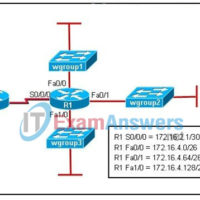
1. Refer to the exhibit. The network administrator enters the command that is shown in the exhibit and then is the show ip route command. The route added by the network administrator is missing from the routing table. What is the reason for this? This static route is …
CCNA Discovery v4.0 Exam Answers
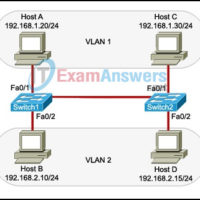
1. What are two advantages of using Layer 3 devices instead of Layer 2 switches at the distribution layer of a hierarchical network? (Choose two.) allows connectivity between different VLANs results in fewer IP subnets to configure and manage provides reliable connectivity to the end user reduces the …
1. A company is developing an Internet store for its website. Which protocol should be used to transfer credit card information from customers to the company web server? FTPS HTTP HTTPS WEP2 TFTP 2. Refer to the exhibit. A new branch office has been added to the corporate …
1. Which two statements describe factors that influence the layout of a proposal? (Choose two.) Proposal layouts are required to use sans serif typefaces. A specific proposal layout is followed when one is specified in the RFP. A designer chooses the layout if a written RFP does not …
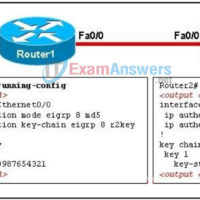
1. Which mechanism is used to create a floating static route? administrative distance cost hop count passive interface 2. IPSec operates at which layer of the OSI model? application network datalink transport 3. Which is true regarding Frame Relay LMI? There are three LMI types standardized by ANSI, …
1. A network engineer has decided to pilot test a portion of a new network design rather than rely on a prototype for proof-of-concept. What are two advantages of pilot testing a design concept?(Choose two.) The test network experiences real-world network traffic. Users within the enterprise are not …
1. A network engineer researched whether there are mechanisms available to help with the transition from an IPv4 addressing structure to IPv6. What three options did the engineer find?(Choose three.) A protocol translation mechanism allows communication between the IPv4 and IPv6 networks. A packet analyzer determines the addressing …
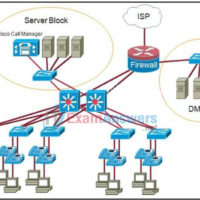
1. Which rule should be followed when implementing the security requirements of a network design? Always use a common security plan for all business needs. As standard practice, lower access restrictions for users if cost is too high. Avoid reducing security in order to add additional network capabilities. …
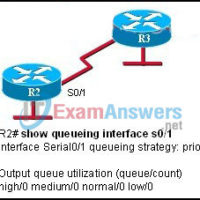
1. In addition to the technical considerations, what other major factor is used to evaluate the success of a network installation? final project costs maintenance costs user satisfaction statistics describing the performance of network devices 2. Which two network applications are most affected by network congestion and delays? …