Check answers here:
Modules 18 – 19: VPNs Group Exam Answers Full
Quiz-summary
0 of 22 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
Information
Network Security (Version1.0) Modules 18 – 19: VPNs Group Test Online
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 22 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- Answered
- Review
-
Question 1 of 22
1. Question
1 pointsWhich two statements describe the IPsec protocol framework? (Choose two.)Correct
Incorrect
Hint
The two primary protocols used with IPsec are AH and ESP. AH is protocol number 51 and provides data authentication and integrity for IP packets that are exchanged between the peers. ESP, which is protocol number 50, performs packet encryption. -
Question 2 of 22
2. Question
1 pointsWhat technology is used to negotiate security associations and calculate shared keys for an IPsec VPN tunnel?Correct
Incorrect
Hint
The Internet Key Exchange (IKE) protocol is a key management protocol standard used when creating an IPsec VPN tunnel. IKE negotiates security associations (SAs) and calculates shared keys. -
Question 3 of 22
3. Question
1 pointsWhat are the two modes used in IKE Phase 1? (Choose two.)Correct
Incorrect
Hint
The two modes for IKE Phase 1 are main and aggressive. Main mode takes more time because the identity of the IKE peers are hidden from eavesdroppers. -
Question 4 of 22
4. Question
1 pointsWhat takes place during IKE Phase 2 when establishing an IPsec VPN?Correct
Incorrect
Hint
During IKE Phase 2, IPsec peers exchange the IPsec security associations (SAs) that each peer is willing to use to establish the IPsec tunnel. -
Question 5 of 22
5. Question
1 pointsA site-to-site IPsec VPN is to be configured. Place the configuration steps in order.Correct
Incorrect
-
Question 6 of 22
6. Question
1 pointsRefer to the exhibit. A VPN tunnel is configured on the WAN between R1 and R2. On which R1 interface(s) would a crypto map be applied in order to create a VPN between R1 and R2?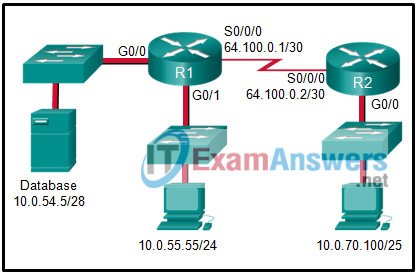 Correct
Correct
Incorrect
Hint
The crypto map command is used to finish creating the IPsec security policy by doing the following binding the interesting traffic ACL and transform set to the crypto map specifying the IP address of the remote VPN site configuring the Diffie-Hellman group configuring the IPsec tunnel lifetime The crypto map is bound to the S0/0/0 R1 interface. -
Question 7 of 22
7. Question
1 pointsRouter R1 has configured ISAKMP policies numbered 1, 5, 9, and 203. Router R2 only has default policies. How will R1 attempt to negotiate the IKE Phase 1 ISAKMP tunnel with R2?Correct
Incorrect
Hint
Peers will attempt to negotiate using the policy with the lowest number (highest priority). Peers do not require matching priority numbers. R1 will attempt to use the most secure default policy (policy #1). If R2 has a matching policy, then R1 and R2 can successfully negotiate the IKE Phase 1 ISAKMP tunnel. If there is no agreement to use the most secure default policy, R1 will attempt to use the next most secure policy. -
Question 8 of 22
8. Question
1 pointsWhen the CLI is used to configure an ISR for a site-to-site VPN connection, what is the purpose of the crypto map command in interface configuration mode?Correct
Incorrect
Hint
The crypto map command, along with the name of the policy, is used to bind the interface to the ISAKMP policy created previously. A transform set is configured using the crypto ipsec transform-set command. Interesting traffic between peers forces IKE Phase 1 negotiations to begin. Peers negotiate the ISAKMP SA policy in step 2 of IPsec negotiations. -
Question 9 of 22
9. Question
1 pointsWhich statement describes the effect of key length in deterring an attacker from hacking through an encryption key?Correct
Incorrect
Hint
While preventing brute-force attacks and other forced decryption concerns, the longer the key length, the harder it is to break. A 64-bit key can take one year to break with a sophisticated computer, while a 128-bit key may take 1019 years to decrypt. Different encryption algorithms will provide varying key lengths for implementation. -
Question 10 of 22
10. Question
1 pointsWhich two statements describe a remote access VPN? (Choose two.)Correct
Incorrect
Hint
Remote access VPNs can be used to support the needs of telecommuters and mobile users by allowing them to connect securely to company networks over the Internet. To connect hosts to the VPN server on the corporate network, the remote access VPN tunnel is dynamically built by client software that runs on the hosts. -
Question 11 of 22
11. Question
1 pointsWhich protocol creates a virtual point-to-point connection to tunnel unencrypted traffic between Cisco routers from a variety of protocols?Correct
Incorrect
Hint
Generic Routing Encapsulation (GRE) is a tunneling protocol developed by Cisco that encapsulates multiprotocol traffic between remote Cisco routers. GRE does not encrypt data. OSPF is a open source routing protocol. IPsec is a suite of protocols that allow for the exchange of information that can be encrypted and verified. Internet Key Exchange (IKE) is a key management standard used with IPsec. -
Question 12 of 22
12. Question
1 pointsHow is “tunneling” accomplished in a VPN?Correct
Incorrect
Hint
Packets in a VPN are encapsulated with the headers from one or more VPN protocols before being sent across the third party network. This is referred to as “tunneling”. These outer headers can be used to route the packets, authenticate the source, and prevent unauthorized users from reading the contents of the packets. -
Question 13 of 22
13. Question
1 pointsWhich two scenarios are examples of remote access VPNs? (Choose two.)Correct
Incorrect
Hint
Remote access VPNs connect individual users to another network via a VPN client that is installed on the user device. Site-to-site VPNs are “always on” connections that use VPN gateways to connect two sites together. Users at each site can access the network on the other site without having to use any special clients or configurations on their individual devices. -
Question 14 of 22
14. Question
1 pointsWhich statement accurately describes a characteristic of IPsec?Correct
Incorrect
Hint
IPsec can secure a path between two network devices. IPsec can provide the following security functions:- Confidentiality – IPsec ensures confidentiality by using encryption.
- Integrity – IPsec ensures that data arrives unchanged at the destination using a hash algorithm, such as MD5 or SHA.
- Authentication – IPsec uses Internet Key Exchange (IKE) to authenticate users and devices that can carry out communication independently. IKE uses several types of authentication, including username and password, one-time password, biometrics, pre-shared keys (PSKs), and digital certificates.
- Secure key exchange- IPsec uses the Diffie-Hellman (DH) algorithm to provide a public key exchange method for two peers to establish a shared secret key.
-
Question 15 of 22
15. Question
1 pointsWhich is a requirement of a site-to-site VPN?Correct
Incorrect
Hint
Site-to-site VPNs are static and are used to connect entire networks. Hosts have no knowledge of the VPN and send TCP/IP traffic to VPN gateways. The VPN gateway is responsible for encapsulating the traffic and forwarding it through the VPN tunnel to a peer gateway at the other end which decapsulates the traffic. -
Question 16 of 22
16. Question
1 pointsConsider the following configuration on a Cisco ASA:crypto ipsec transform-set ESP-DES-SHA esp-des esp-sha-hmac
What is the purpose of this command?Correct
Incorrect
Hint
The transform set is negotiated during Phase 2 of the IPsec VPN connection process. The purpose of the transform set is to define what encryption and authentication schemes can be used. The device doing the VPN initiation offers the acceptable transform sets in order of preference, in this case, ESP authentication using DES for encryption or ESP authentication using SHA-HMAC authentication and integrity for the data payload. Remember that ESP provides confidentiality with encryption and integrity with authentication. The ESP-DES-SHA is the name of the transform set. The parameters that follow (esp-des and esp-sha-hmac) are the specific types of encryption or authentication that is supported by the ASA for the VPN tunnel that uses this transform set. -
Question 17 of 22
17. Question
1 pointsWhat is needed to define interesting traffic in the creation of an IPsec tunnel?Correct
Incorrect
Hint
In order to bring up an IPsec tunnel, an access list must be configured with a permit statement that will identify interesting traffic. Once interesting traffic is detected by matching the access list, the tunnel security associations can be negotiated. -
Question 18 of 22
18. Question
1 pointsWhat is a function of the GRE protocol?Correct
Incorrect
Hint
The transform set is the set of encryption and hashing algorithms that will be used to transform the data sent through the IPsec tunnel. GRE supports multiprotocol tunneling. It can encapsulate multiple OSI Layer 3 protocol packet types inside an IP tunnel. Routing protocols that are used across the tunnel enable dynamic exchange of routing information in the virtual network. GRE does not provide encryption. -
Question 19 of 22
19. Question
1 pointsRefer to the exhibit. What HMAC algorithm is being used to provide data integrity?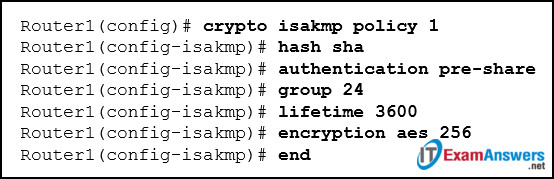 Correct
Correct
Incorrect
Hint
Two popular algorithms that are used to ensure that data is not intercepted and modified (data integrity) are MD5 and SHA. The command Router1(config-isakmp)# hash sha indicates that SHA is being used. AES is an encryption protocol and provides data confidentiality. DH (Diffie-Hellman) is an algorithm that is used for key exchange. RSA is an algorithm used for authentication. -
Question 20 of 22
20. Question
1 pointsTwo corporations have just completed a merger. The network engineer has been asked to connect the two corporate networks without the expense of leased lines. Which solution would be the most cost effective method of providing a proper and secure connection between the two corporate networks?Correct
Incorrect
Hint
The site-to-site VPN is an extension of a classic WAN network that provides a static interconnection of entire networks. Frame Relay would be a better choice than leased lines, but would be more expensive than implementing site-to-site VPNs. The other options refer to remote access VPNs which are better suited for connecting users to the corporate network versus interconnecting two or more networks. -
Question 21 of 22
21. Question
1 pointsRefer to the exhibit. What show command displays whether the securityk9 software is installed on the router and whether the EULA license has been activated?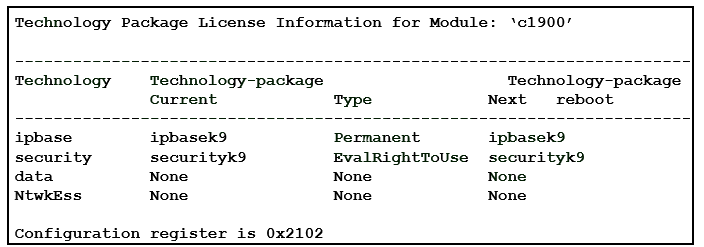 Correct
Correct
Incorrect
Hint
The show version command displays the status of technology packages on the router. Based on the partial output shown, the router software already includes ipbasek9 and securityk9. The EvalRightToUse parameter shows that the license is active thereby giving access to the cryptographic features, IPsec and ISAKMP, required to create an IPsec VPN. -
Question 22 of 22
22. Question
1 pointsWhat type of traffic is supported by IPsec?Correct
Incorrect
Hint
IPsec only supports unicast traffic. If multicast traffic needs to travel through a tunnel, a GRE tunnel will need to be configured between the peers.
