Check answers here:
Modules 8 – 10: ACLs and Firewalls Group Exam Answers Full
Quiz-summary
0 of 35 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
Information
Network Security (Version1.0) Modules 8 – 10: ACLs and Firewalls Group Test Online
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 35 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- Answered
- Review
-
Question 1 of 35
1. Question
1 pointsWhen creating an ACL, which keyword should be used to document and interpret the purpose of the ACL statement on a Cisco device?Correct
Incorrect
Hint
In order to document the purpose of an ACL and identify its function more easily, the remark keyword is used when building the ACL. The established keyword is used to allow connections that were initially sourced from the current device. The eq operator is used to specify a port number for denying or permitting traffic. The description keyword is used when configuring and documenting interfaces. -
Question 2 of 35
2. Question
1 pointsWhich two pieces of information are required when creating a standard access control list? (Choose two.)Correct
Incorrect
Hint
Standard ACLs can be numbered 1 to 99 and 1300 to 1999. Standard IP ACLs filter only on the source IP address. -
Question 3 of 35
3. Question
1 pointsWhat two steps provide the quickest way to completely remove an ACL from a router? (Choose two.)Correct
Incorrect
Hint
To completely remove an ACL from a router requires two steps. Removing the actual ACL with the no access-list command and removing the association of the ACL from the appropriate interface. -
Question 4 of 35
4. Question
1 pointsWhich two types of addresses should be denied inbound on a router interface that attaches to the Internet? (Choose two.)Correct
Incorrect
Hint
The following addresses should not be permitted inbound from the Internet in order to mitigate IP spoofing and DoS attacks:- All zero address
- Broadcast addresses
- Local host addresses that start with 127
- Reserved private addresses
- IP multicast addresses
-
Question 5 of 35
5. Question
1 pointsIn the creation of an IPv6 ACL, what is the purpose of the implicit final command entries, permit icmp any any nd-na and permit icmp any any nd-ns ?Correct
Incorrect
Hint
IPv6 address to MAC address resolution is performed through the exchange of ICMPv6 neighbor discovery packets comprised of neighbor solicitation and neighbor advertisement packets. Unless these packets are permitted on a router interface, the interface will not be able to perform MAC address resolution. -
Question 6 of 35
6. Question
1 pointsWhat two statements describe characteristics of IPv6 access control lists? (Choose two.)Correct
Incorrect
Hint
IPv6 access lists have distinct characteristics that are different than IPv4 access lists:- They use prefix lengths instead of wildcard masks to match network bits.
- They permit two ICMPv6 message types: neighbor solicitations and neighbor advertisements by default.
- They are only created as named access lists.
- They use the command ipv6 taffic-filter when applied to an interface.
-
Question 7 of 35
7. Question
1 pointsRefer to the exhibit. A network administrator created an IPv6 ACL to block the Telnet traffic from the 2001:DB8:CAFE:10::/64 network to the 2001:DB8:CAFE:30::/64 network. What is a command the administrator could use to allow only a single host 2001:DB8:CAFE:10::A/64 to telnet to the 2001:DB8:CAFE:30::/64 network?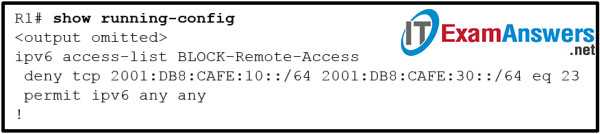 Correct
Correct
Incorrect
Hint
When an IPv6 ACE is created and is to be processed before an existing ACE is processed, the next command entered must use the sequence argument with a number lower than the existing ACE. This allows an entry to be placed before an existing entry, as the default sequence numbers are commonly numbered by increments of 10. Thus, using a sequence number of 5 on an ACE will place it in front of a prior existing entry with a sequence number of 10. -
Question 8 of 35
8. Question
1 pointsWhen implementing components into an enterprise network, what is the purpose of a firewall?Correct
Incorrect
Hint
A firewall is a system that enforces an access control policy and prevents the exposure of sensitive hosts, resources, and applications to untrusted users. -
Question 9 of 35
9. Question
1 pointsWhat are two possible limitations of using a firewall in a network? (Choose two.)Correct
Incorrect
Hint
Firewalls have some limitations:- A misconfigured firewall can have serious consequences for the network, such as becoming a single point of failure.
- The data from many applications cannot be passed over firewalls securely.
- Users might proactively search for ways around the firewall to receive blocked material, which exposes the network to potential attack.
- Network performance can slow down.
- Unauthorized traffic can be tunneled or hidden as legitimate traffic through the firewall.
-
Question 10 of 35
10. Question
1 pointsWhich type of firewall makes use of a proxy server to connect to remote servers on behalf of clients?Correct
Incorrect
Hint
An application gateway firewall, also called a proxy firewall, filters information at Layers 3, 4, 5, and 7 of the OSI model. It uses a proxy server to connect to remote servers on behalf of clients. Remote servers will see only a connection from the proxy server, not from the individual clients. -
Question 11 of 35
11. Question
1 pointsHow does a firewall handle traffic when it is originating from the public network and traveling to the private network?Correct
Incorrect
Hint
When traffic is originating from the public network it will usually be blocked when traveling to the private network. Traffic that originates from the private network will be selectively allowed to be returned to the public network. -
Question 12 of 35
12. Question
1 pointsWhich two statements describe the two configuration models for Cisco IOS firewalls? (Choose two.)Correct
Incorrect
Hint
There are two configuration models for Cisco IOS Firewalls, IOS Classic Firewalls and zone-based policy firewalls (ZPF). Both configuration models can be enabled concurrently on a router but they cannot be combined on a single interface. One benefit of using ZPF is that ZPF is not dependent on ACLs. -
Question 13 of 35
13. Question
1 pointsDesigning a ZPF requires several steps. Which step involves dictating the number of devices between most-secure and least-secure zones and determining redundant devices?Correct
Incorrect
Hint
Designing ZPFs involves several steps:- Step 1 . Determine the zones – The administrator focuses on the separation of the network into zones. Zones establish the security borders of a network.
- Step 2 . Establish policies between zones – For each pair of “source-destination” zones, define the sessions that clients in the source zones can request from servers in destination zones.
- Step 3 . Design the physical infrastructure – After the zones have been identified, and the traffic requirements between them documented, the administrator must design the physical infrastructure. This includes dictating the number of devices between most-secure and least-secure zones and determining redundant devices.
- Step 4 . Identify subsets within zones and merge traffic requirements – For each firewall device in the design, the administrator must identify zone subsets that are connected to its interfaces and merge the traffic requirements for those zones.
-
Question 14 of 35
14. Question
1 pointsWhen a Cisco IOS zone-based policy firewall is being configured, which three actions can be applied to a traffic class? (Choose three.)Correct
Incorrect
Hint
The inspect CCP action is similar to the classic firewall ip inspect command in that it inspects traffic going through the firewall and allowing return traffic that is part of the same flow to pass through the firewall. The drop action is similar to the deny parameter in an ACL. This action drops whatever traffic fits the defined policy. The pass action is similar to a permit ACL statement–traffic is allowed to pass through because it met the criteria of the defined policy statement. -
Question 15 of 35
15. Question
1 pointsWhen using Cisco IOS zone-based policy firewall, where is the inspection policy applied?Correct
Incorrect
Hint
After configuring the firewall policy, apply the policy to traffic that would flow between a pair of zones. Use the zone-pair security command in global configuration mode. -
Question 16 of 35
16. Question
1 pointsWhat is the first step in configuring a Cisco IOS zone-based policy firewall via the CLI?Correct
Incorrect
Hint
The steps for configuring a Cisco IOS zone-based policy firewall are as follows:- Create zones.
- Define traffic classes.
- Define firewall policies.
- Apply policy maps to zone pairs.
- Assign router interfaces to zones.
-
Question 17 of 35
17. Question
1 pointsWhat is one benefit of using a stateful firewall instead of a proxy server?Correct
Incorrect
Hint
A stateful firewall performs better than a proxy server. A stateful firewall cannot authenticate users or prevent Layer 7 attacks. Both a stateful firewall and a proxy server can filter packets. -
Question 18 of 35
18. Question
1 pointsWhich statement describes a typical security policy for a DMZ firewall configuration?Correct
Incorrect
Hint
With a three interface firewall design that has internal, external, and DMZ connections, typical configurations include the following:- Traffic originating from DMZ destined for the internal network is normally blocked.
- Traffic originating from the DMZ destined for external networks is typically permitted based on what services are being used in the DMZ.
- Traffic originating from the internal network destined from the DMZ is normally inspected and allowed to return.
- Traffic originating from external networks (the public network) is typically allowed in the DMZ only for specific services.
-
Question 19 of 35
19. Question
1 pointsWhat is one limitation of a stateful firewall?Correct
Incorrect
Hint
Limitations of stateful firewalls include the following:- Stateful firewalls cannot prevent application layer attacks.
- Protocols such as UDP and ICMP are not stateful and do not generate information needed for a state table.
- An entire range of ports must sometimes be opened in order to support specific applications that open multiple ports.
- Stateful firewalls lack user authentication.
-
Question 20 of 35
20. Question
1 pointsWhich statement describes Cisco IOS Zone-Based Policy Firewall operation?Correct
Incorrect
Hint
The pass action allows traffic only in one direction. Interfaces automatically become members of the self zone. Interfaces are assigned to zones in interface configuration mode, but most configuration takes place in global configuration mode and associated submodes. Interfaces can belong to only one zone at any time. -
Question 21 of 35
21. Question
1 pointsWhat is the result in the self zone if a router is the source or destination of traffic?Correct
Incorrect
Hint
All traffic is permitted in the self zone if the traffic originates from, or is destined for, the router. -
Question 22 of 35
22. Question
1 pointsWhat are two characteristics of ACLs? (Choose two.)Correct
Incorrect
Hint
Standard ACLs can only filter on source addresses. That is why they are normally placed closest to the destination. Extended ACLs can filter on source and destination IP addresses, port numbers, and specific message types within a particular protocol such as echo request within the ICMP protocol. -
Question 23 of 35
23. Question
1 pointsWhich three statements describe ACL processing of packets? (Choose three.)Correct
Incorrect
Hint
When a packet comes into a router that has an ACL configured on the interface, the router compares the condition of each ACE to determine if the defined criteria has been met. If met, the router takes the action defined in the ACE (allows the packet through or discards it). If the defined criteria has not been met, the router proceeds to the next ACE. An implicit deny any statement is at the end of every standard ACL. -
Question 24 of 35
24. Question
1 pointsA network administrator configures an ACL with the command R1(config)# access-list 1 permit 172.16.0.0 0.0.15.255 . Which two IP addresses will match this ACL statement? (Choose two.)Correct
Incorrect
Hint
The wildcard mask indicates that any IP address within the range of 172.16.0.0 to 172.16.15.255 matches. -
Question 25 of 35
25. Question
1 pointsWhat single access list statement matches all of the following networks?- 192.168.16.0
- 192.168.17.0
- 192.168.18.0
- 192.168.19.0
Correct
Incorrect
Hint
The ACL statement access-list 10 permit 192.168.16.0 0.0.3.255 will match all four network prefixes. All four prefixes have the same 22 high order bits. These 22 high order bits are matched by the network prefix and wildcard mask of 192.168.16.0 0.0.3.255. -
Question 26 of 35
26. Question
1 pointsWhich two characteristics are shared by both standard and extended ACLs? (Choose two.)Correct
Incorrect
Hint
Standard ACLs filter traffic based solely on a specified source IP address. Extended ACLs can filter by source or destination, protocol, or port. Both standard and extended ACLs contain an implicit deny as a final statement. Standard and extended ACLs can be identified by either names or numbers. -
Question 27 of 35
27. Question
1 pointsRefer to the exhibit. What is the result of adding the established argument to the end of the ACE?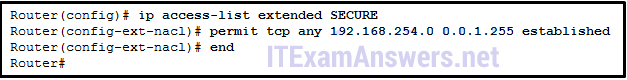 Correct
Correct
Incorrect
Hint
The established argument allows TCP return traffic from established connections to be sent on an outgoing interface to a network. -
Question 28 of 35
28. Question
1 pointsWhich two keywords can be used in an access control list to replace a wildcard mask or address and wildcard mask pair? (Choose two.)Correct
Incorrect
Hint
The host keyword is used when using a specific device IP address in an ACL. For example, the deny host 192.168.5.5 command is the same is the deny 192.168.5.5 0.0.0.0 command. The any keyword is used to allow any mask through that meets the criteria. For example, the permit any command is the same as permit 0.0.0.0 255.255.255.255 command. -
Question 29 of 35
29. Question
1 pointsIf the provided ACEs are in the same ACL, which ACE should be listed first in the ACL according to best practice?Correct
Incorrect
Hint
A best practice for configuring an extended ACL is to ensure that the most specific ACE is placed higher in the ACL. Consider the two permit UDP statements. If both of these were in an ACL, the SNMP ACE is more specific than the UDP statement that permits a range of 10,001 UDP port numbers. The SNMP ACE would be entered before the other UDP ACE. The ACEs from most specific to least specific are as follows:permit udp 172.16.0.0 0.0.255.255 host 172.16.1.5 eq snmptrap deny udp any host 172.16.1.5 eq snmptrap permit tcp 172.16.0.0 0.0.3.255 any established deny tcp any any eq telnet permit udp any any range 10000 20000 permit ip any any
-
Question 30 of 35
30. Question
1 pointsTo facilitate the troubleshooting process, which inbound ICMP message should be permitted on an outside interface?Correct
Incorrect
Hint
By allowing the ICMP echo reply message inbound to the organization, internal users are allowed to ping external addresses (and the reply message allowed to return). -
Question 31 of 35
31. Question
1 pointsA security specialist designs an ACL to deny access to a web server from all sales staff. The sales staff are assigned addressing from the IPv6 subnet 2001:db8:48:2c::/64. The web server is assigned the address 2001:db8:48:1c::50/64. Configuring the WebFilter ACL on the LAN interface for the sales staff will require which three commands? (Choose three.)Correct
Incorrect
Hint
The ACL requires an ACE denying Telnet access from all users in the LAN to the file server at 2001:db8:48:1c::50/64. The IPv6 ACL also has an implicit deny, so a permit statement is required to allow all other traffic. With IPv6, the ipv6 traffic filter command is used to bind the ACL to the interface. -
Question 32 of 35
32. Question
1 pointsWhat are two characteristics of a stateful firewall? (Choose two.)Correct
Incorrect
Hint
Stateful firewalls are the most versatile and the most common firewall technologies in use. Stateful firewalls provide stateful packet filtering by using connection information maintained in a state table. Stateful filtering is a firewall architecture that is classified at the network layer. It also analyzes traffic at OSI Layers 4 and 5. Stateful firewalls cannot prevent application layer attacks because they do not examine the actual contents of an HTTP connection. -
Question 33 of 35
33. Question
1 pointsWhat are two differences between stateful and stateless firewalls? (Choose two.)Correct
Incorrect
Hint
There are many differences between a stateless and stateful firewall. Stateless firewalls: are susceptible to IP spoofing do not reliably filter fragmented packets use complex ACLs, which can be difficult to implement and maintain cannot dynamically filter certain services examine each packet individually rather than in the context of the state of a connection Stateful firewalls: are often used as a primary means of defense by filtering unwanted, unnecessary, or undesirable traffic strengthen packet filtering by providing more stringent control over security improve performance over packet filters or proxy servers defend against spoofing and DoS attacks by determining whether packets belong to an existing connection or are from an unauthorized source provide more log information than a packet filtering firewall -
Question 34 of 35
34. Question
1 pointsWhen implementing a ZPF, what is the default security setting when forwarding traffic between two interfaces in the same zone?Correct
Incorrect
Hint
A zone-based policy firewall uses the concept of zones to specify where firewall rules and policies should be applied. By default, the traffic between interfaces that exist in the same zone is not subject to any policy and passes freely. -
Question 35 of 35
35. Question
1 pointsWhich two rules about interfaces are valid when implementing a Zone-Based Policy Firewall? (Choose two.)Correct
Incorrect
The rules for traffic transiting through the router are as follows:
- If neither interface is a zone member, then the resulting action is to pass the traffic.
- If both interfaces are members of the same zone, then the resulting action is to pass the traffic.
- If one interface is a zone member, but the other is not, then the resulting action is to drop the traffic regardless of whether a zone-pair exists.
- If both interfaces belong to the same zone-pair and a policy exists, then the resulting action is inspect, allow, or drop as defined by the policy.
