Check answers here:
Modules 5 – 7: Monitoring and Managing Devices Group Exam Answers Full
Quiz-summary
0 of 27 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
Information
Network Security (Version1.0) Modules 5 – 7: Monitoring and Managing Devices Group Test Online
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 27 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- Answered
- Review
-
Question 1 of 27
1. Question
1 pointsWhich privilege level is predefined for the privileged EXEC mode?Correct
Incorrect
Hint
Privileged EXEC mode (privilege level 15) is reserved for the enable mode privileges (all enable-level commands). Users can change configurations and view configuration files. -
Question 2 of 27
2. Question
1 pointsWhat is a requirement to use the Secure Copy Protocol feature?Correct
Incorrect
Hint
The Secure Copy Protocol feature relies on SSH and requires that AAA authentication and authorization be configured so that the router can determine whether the user has the correct privilege level. For local authentication, at least one user with privilege level 15 has to be configured. Transfers can originate from any SCP client whether that client is another router, switch, or workstation. The ip scp server enable command has to be issued to enable the SCP server side functionality. -
Question 3 of 27
3. Question
1 pointsWhich three items are prompted for a user response during interactive AutoSecure setup? (Choose three.)Correct
Incorrect
Hint
During AutoSecure setup, the following steps occur:- The auto secure command is entered.
- The wizard gathers information about the outside interfaces.
- AutoSecure secures the management place by disabling unnecessary services.
- AutoSecure prompts for a security banner.
- AutoSecure prompts for passwords and enables password and login features.
- Interfaces are secured.
- The forwarding plane is secured.
-
Question 4 of 27
4. Question
1 pointsWhich syslog message type is accessible only to an administrator and only via the Cisco CLI?Correct
Incorrect
Hint
Syslog messages can be sent to the logging buffer, the console line, the terminal line, or to a syslog server. However, debug-level messages are only forwarded to the internal buffer and only accessible through the Cisco CLI. -
Question 5 of 27
5. Question
1 pointsRefer to the exhibit. What two statements describe the NTP status of the router? (Choose two.)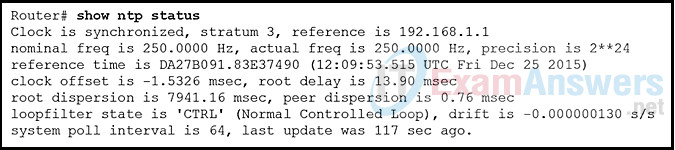 Correct
Correct
Incorrect
Hint
The show ntp status command displays information about how NTP is operating on the device. The output shows that the router clock is synchronized with the NTP server with the address of 192.168.1.1. NTP is hierarchical. The router is a stratum 3 device, therefore it’s time source is a stratum 2 device. Authoritative time sources in the NTP system are located at stratum 0. -
Question 6 of 27
6. Question
1 pointsAn administrator needs to create a user account with custom access to most privileged EXEC commands. Which privilege command is used to create this custom account?Correct
Incorrect
Hint
In Cisco IOS software, there are 16 privilege levels:- Level 0 : Predefined for user-level access privileges.
- Level 1 : The default level for login with the router prompt Router>.
- Levels 2 -14 : May be customized for user-level privileges. Commands from lower levels may be moved up to another higher level, or commands from higher levels may be moved down to a lower level.
- Level 15 : Reserved for the enable mode privileges (enable command). To configure a privilege level with specific commands for a customized user level, use the privilege exec level level [ command ], where level could be between 2 to 14.
-
Question 7 of 27
7. Question
1 pointsA network administrator is analyzing the features supported by the multiple versions of SNMP. What are two features that are supported by SNMPv3 but not by SNMPv1 or SNMPv2c? (Choose two.)Correct
Incorrect
Hint
SNMPv3 provides message integrity to ensure that a packet was not tampered with and authentication to determine if the message is from a valid source. SNMPv3 also supports message encryption. SNMPv1 and SNMPv2 do not support message encryption, but do support community strings. SNMPv2c supports bulk retrieval operation. All SNMP versions support the SNMP trap mechanism. -
Question 8 of 27
8. Question
1 pointsA network administrator is configuring an AAA server to manage TACACS+ authentication. What are two attributes of TACACS+ authentication? (Choose two.)Correct
Incorrect
Hint
TACACS+ authentication includes the following attributes:- Separates authentication and authorization processes
- Encrypts all communication, not just passwords
- Utilizes TCP port 49
-
Question 9 of 27
9. Question
1 pointsWhat are two characteristics of the RADIUS protocol? (Choose two.)Correct
Incorrect
Hint
RADIUS is an open-standard AAA protocol using UDP port 1645 or 1812 for authentication and UDP port 1646 or 1813 for accounting. It combines authentication and authorization into one process. -
Question 10 of 27
10. Question
1 pointsWhat is the one major difference between local AAA authentication and using the login local command when configuring device access authentication?Correct
Incorrect
Hint
Local AAA authentication works very similar to the login local command, except that it allows you to specify backup authentication methods as well. Both methods require that local usernames and passwords be manually configured on the router. -
Question 11 of 27
11. Question
1 pointsWhich two UDP port numbers may be used for server-based AAA RADIUS authentication? (Choose two.)Correct
Incorrect
Hint
RADIUS authentication and accounting utilize the following UDP port numbers:- UDP port 1645 or 1812 for authentication
- UDP port 1646 or 1813 for accounting
- TACACS+ uses TCP port 49.
-
Question 12 of 27
12. Question
1 pointsWhich command will move the show access-lists command to privilege level 14?Correct
Incorrect
Hint
To configure a privilege level with specific commands, use the privilege exec level level [ command ]. -
Question 13 of 27
13. Question
1 pointsWhich authentication method stores usernames and passwords in the router and is ideal for small networks?Correct
Incorrect
Hint
In a small network with a few network devices, AAA authentication can be implemented with the local database and with usernames and passwords stored on the network devices. Authentication using the TACACS+ or RADIUS protocol will require dedicated ACS servers although this authentication solution scales well in a large network. -
Question 14 of 27
14. Question
1 pointsWhat are three characteristics of superviews in the Cisco role-based CLI access feature? (Choose three.)Correct
Incorrect
Hint
Cisco role-based Superviews have several specific characteristics:- A single CLI view can be shared within multiple superviews.
- Commands cannot be configured for a superview. An administrator must add commands to the CLI view and add that CLI view to the superview.
- Users who are logged into a superview can access all the commands that are configured for any of the CLI views that are part of the superview.
- Each superview has a password that is used to switch between superviews or from a CLI view to a superview.
- Deleting a superview does not delete the associated CLI views. The CLI views remain available to be assigned to another superview.
- Only a root view user can configure a new view and add or remove commands from the existing views.
-
Question 15 of 27
15. Question
1 pointsA student is learning about role-based views and role-based view configurations. The student enters the Router(config)# parser view TECH-view command. What is the purpose of this command?Correct
Incorrect
Hint
The command Router(config)# parser view [ view-name ] is used to create a new CLI view. The command Router(config)# parser view [ view-name ] superview is used to create a new superview view. -
Question 16 of 27
16. Question
1 pointsRefer to the exhibit. A student uses the show parser view all command to see a summary of all views configured on router R1. What is indicated by the symbol * next to JR-ADMIN?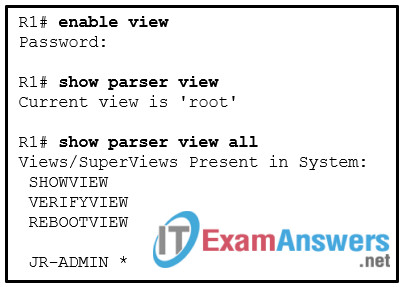 Correct
Correct
Incorrect
Hint
From the root view, a network administrator can see a summary of all role-based views by using the show parser view all command. An asterisk identifies a superview. -
Question 17 of 27
17. Question
1 pointsWhat are two characteristics of the Cisco IOS Resilient Configuration feature? (Choose two.)Correct
Incorrect
Hint
The Cisco IOS Resilient Configuration stores a secure copy of the primary image file and device configuration. These secure files cannot be removed by a user. Its main function is to speed up the recovery time if a device has been compromised and the image file and the device configuration have been deleted. This feature is only available on platforms that support a PCMCIA ATA disk with enough storage space. -
Question 18 of 27
18. Question
1 pointsWhat IOS privilege levels are available to assign for custom user-level privileges?Correct
Incorrect
Hint
There are 16 privilege levels that can be applied to user accounts. Levels 0, 1, and 15 have predefined settings. This leaves levels 2 through 14 available for creating custom levels of access. -
Question 19 of 27
19. Question
1 pointsRefer to the exhibit. What information in the syslog message identifies the facility?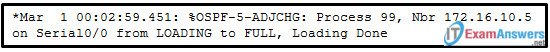 Correct
Correct
Incorrect
Hint
The facility is a service identifier used to categorize and identify the messages being generated by a device using syslog. The facility of OSPF identifies this syslog message as being from the OSPF protocol. Level 5 is the severity level of this message. ADJCHG is the mnemonic to describe the action occurring. Loading Done is part of the description of the event that occurred. -
Question 20 of 27
20. Question
1 pointsWhat is the biggest issue with local implementation of AAA?Correct
Incorrect
Hint
One of the purposes of AAA is to provide secure authentication to network devices. Local implementation does not use RADIUS or TACACS+ servers. It relies on a local database to authenticate all users. This can be a problem in a network that has many devices with hundreds of users or more. -
Question 21 of 27
21. Question
1 pointsWhich task is necessary to encrypt the transfer of data between the ACS server and the AAA-enabled router?Correct
Incorrect
Hint
The key command is used to configure the shared secret key that is used for encryption. The key must be configured the exact same way on the router and on the ACS server. The creation of a VPN tunnel is unnecessary. Neither the configuration of ports nor the use of the single-connection command has any effect on encryption. -
Question 22 of 27
22. Question
1 pointsRefer to the exhibit. Based on the output of the show running-config command, which type of view is SUPPORT?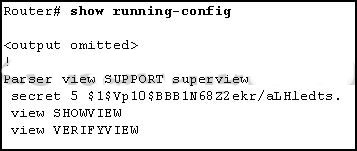 Correct
Correct
Incorrect
Hint
The superview role-based CLI view named SUPPORT has been configured on the router. The SUPPORT suerview consists of two CLI views called SHOWVIEW and VERIFYVIEW. -
Question 23 of 27
23. Question
1 pointsA student is learning role-based CLI access and CLI view configurations. The student opens Packet Tracer and adds a router. Which command should be used first for creating a CLI view named TECH-View?Correct
Incorrect
Hint
Before an administrator can create a view for role-based CLI access, AAA must be enabled using the aaa new-model command. -
Question 24 of 27
24. Question
1 pointsA network engineer is implementing security on all company routers. Which two commands must be issued to force authentication via the password 1A2b3C for all OSPF-enabled interfaces in the backbone area of the company network? (Choose two.)Correct
Incorrect
Hint
The two commands that are necessary to configure authentication via the password 1A2b3C for all OSPF-enabled interfaces in the backbone area (Area 0) of the company network would be ip ospf message-digest-key 1 md5 1A2b3C and area 0 authentication message-digest. The option area 1 authentication message-digest is incorrect because it refers to Area 1, not Area 0. The option enable password 1A2b3C is incorrect because it would set the privileged EXEC mode password instead of the OSPF authentication password. The option username OSPF password 1A2b3C is required to create a username database in a router, which is not required with OSPF authentication. -
Question 25 of 27
25. Question
1 pointsBecause of implemented security controls, a user can only access a server with FTP. Which AAA component accomplishes this?Correct
Incorrect
Hint
One of the components in AAA is authorization. After a user is authenticated through AAA, authorization services determine which resources the user can access and which operations the user is allowed to perform. -
Question 26 of 27
26. Question
1 pointsWhich AAA component can be established using token cards?Correct
Incorrect
Hint
The authentication component of AAA is established using username and password combinations, challenge and response questions, and token cards. The authorization component of AAA determines which resources the user can access and which operations the user is allowed to perform. The accounting and auditing component of AAA keeps track of how network resources are used. -
Question 27 of 27
27. Question
1 pointsWhat is the primary function of the aaa authorization command?Correct
Incorrect
Hint
Authorization is concerned with allowing and disallowing authenticated users access to certain areas and programs on the network as well as specific services. Controlling access to configuration commands greatly simplifies the infrastructure security in large enterprise networks.
