1.1.1.6 Lab – Shodan Search (Instructor Version)
Objectives
- Part 1: Obtain Access to Shodan’s Free Features
- Part 2: Investigate Connected IoT Devices
Background / Scenario
Warning: Do not attempt to login to any device you find on the Shodan search engine. Doing so violates your ethical hacking agreement.
In this lab, you will use the Shodan search engine to gain an understanding of why security should be the focus of any IoT implementation.
Shodan has servers located around the world that continually crawl the Internet looking for connected devices. It can find specific devices and device types. This data can then be searched. Some of the more popular searches include terms such as “webcam”, “default passwords”, “routers”, “video games,” and more.
Shodan is a favorite tool used by researchers, security professionals, large enterprises, and computer emergency response teams (CERTs).
- Researchers can use Shodan to data mine information about what devices are connected, where they are connected, and what services are exposed.
- Security professionals can use Shodan as part of a penetration testing plan to discover devices that need to be hardened to prevent potential attacks.
- Large enterprises employ security professionals who should be aware of tools like Shodan for determining the current risk profile of the enterprise’s connected devices.
- CERTs can use Shodan to quickly generate reports about an emerging attack on connected devices.
Shodan is also a tool used by nefarious individuals and groups commonly referred to as threat actors. Shodan can accelerate a threat actor’s reconnaissance of Internet connected devices. Like all the tools in this course, you must use it responsibly according to your organization’s ethical hacking policies.
Instructor Note: Shodan is a powerful website where students can easily get into trouble. For example students can tind detault login information and use it to access the configuration webpage for a device. This violates ethical hacking agreements.
Required Resources
- Device with Internet access.
- SANS Penetration Testing article, “Getting the Most Out of Shodan Searches”
Part 1: Obtain Access to Shodan’s Free Features
In this part of the lab, you will navigate to the Shodan search engine and sign up for an account.
a. Open a web browser and navigate to the Shodan website at https://www.shodan.io/.
b. Create an account in one of two ways:
- If you click Create a Free Account, you will be directed to a page where you can fill in a form to create an account on Shodan.
- If you click Login or Register, you will be directed to a page where you can sign in with one of several other accounts that you may have, including Google or Facebook.
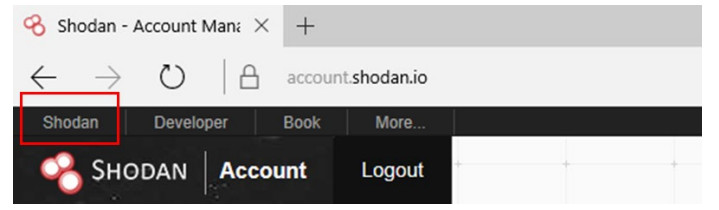
c. After successfully logging in, you will see your account page, as shown below. Click the Shodan link to return to the homepage.
Part 2: Investigate Connected IoT Devices
In this part, you will gain familiarity with using Shodan’s features to search for Internet-connected devices.
Step 1: Use the basic features of the Shodan search engine.
From the main page, you can type keywords in the search field to get a list of results.
a. Type cisco as the keyword and press Enter. How many results did you get for your search?
At the time of testing this lab, this search returned over 6 million results.
Note: Not every device that is found by Shodan is insecure. Shodan simply finds devices that are accessible from the Internet according to a set of search criteria.
b. Look at other information on the left side of the web page. Your search result is broken down into various categories. Each entry in a category is a clickable link that will refine your search.
How many results, if any, are there for the Windows XP operating system? At the time of testing this lab, this search returned 0 results for Windows XP OS. Reference link: https://www.shodan.io/search/facet?query=cisco&facet=os
c. Although Microsoft stopped supporting Windows XP in April 2014, it continues to release patches for it because there are so many end devices still using the operating system. Use an Internet search to discover the well-known 2017 cyberattack that targeted older Windows operating systems.
What was the attack called, what did it target, and what did it do?
WannaCry or WannaCrypt ransomware targeted unpatched, older versions of Windows and encrypted the users’ data and demanded ransom payments in Bitcoin
From your research, you should have noted that this attack targeted unpatched systems. Prior to the attack, Microsoft had released patches that addressed the vulnerabilities. The systems that were affected by the attack were ones that had not downloaded and applied the patches. Unpatched software is a primary attack vector for threat actors. Any connected device is vulnerable to this type of attack. In the IoT landscape, patching devices becomes even more important as tools such as Shodan can quickly reveal your device’s information, including potential vulnerabilities, to the world.
Note: Not all devices discovered by Shodan are vulnerable. Shodan results consist of Internet-connected devices and information about those devices. This information may or may not reveal potential vulnerabilities.
d. On the right side, the main section of your search shows the devices that match your search. Find an entry that looks interesting to you and fill in the information below.
IP address: _______________________________________
Hostname: _______________________________________
ISP: ____________________________________________
Date the entry was added: _____________________________
Country: _________________________________________
e. Your entry will also show some banner information. You may see the beginnings of an SSH banner or an HTTP banner. Click Details for more information about your entry. You should see several open ports. If not, try a different entry. List the information you found below.
City and Country: ____________________________________
Ports open: ________________________________________
Services running: ____________________________________
Key types: _________________________________________
Answers will vary. Encourage students to look for a variety of open ports including 22 (SSH), 25 (SMTP), 80 (HTTP), 123 (NTP), and 443 (HTTPS). They should be able to find one that lists the encryption keys for SSH.
f. Return to the Shodan homepage and click Explore. What are some of the Top Voted results?
At the time of testing this lab, Top Voted results included Webcam, Cams, Netcam, default password, and dreambOx.
One of the Top Voted results for you may have been default password. If so, click default password to see the results. If not, in the search field, type the keywords “default password,” with the quotes, and press Enter. You will see several results that show default passwords embedded in the banners for devices. Hopefully, the owners of these devices have changed the default password. However, this highlights how easy it can be to login to a device if appropriate security measures are not implemented.
Warning: Do not attempt to login to any device you find on the Shodan search engine. Doing so violates your ethical hacking agreement.
g. In the search field, type the keyword “webcam” with the quotes and press Enter. What is your count for Total Results?
At the time of testing this lab, Total Results was over 6,000.
h. In the search field, type the keyword “refrigerator” with the quotes and press Enter. What is your count for Total Results?
At the time of testing this lab, Total Results was 193.
Step 2: Use keywords together with search operators to filter your search.
You may have noticed that you can only get two pages of results with your free account access. However, even with a paid account you would not want to click through the pages that list thousands or millions of results. Instead, you can combine keywords and search operators to filter your results.
Shodan searches for the services running on a device. It then collects banner information for each service. For example, here is the banner information for the SNMP service running on a Cisco device found with the Shodan search:
Cisco Internetwork Operating System Software IOS (tm) 7200 Software (UBR7200-IK9SU2-M), Version 12.3(23)BC10, RELEASE SOFTWARE (fc1) Technical Support: http://www.cisco.com/techsupport Copyright (c) 1986-2011 by cisco Systems, Inc.
A search for just “cisco” most likely reveals one to two million results for you. That information may be helpful to you. However, if you are interested in more specific information, you will want to filter your search using filter names and values from the banner information.
For example, if you are interested in seeing how many Cisco 7200 routers in the United States are running the SNMP service, you would enter the following search phrase.
country:US product:"Cisco 7200 Router" port:161
Note: Shodan searches use the two letter (alpha-2) country code based on the International Standards Organization’s 3166 publication (ISO 3166-1993).
Create your own searches to find the following:
a. Minecraft is a popular video game where players can set up their own servers for others to access online.
Use an Internet search to find the following information.
What is the common port number used by Minecraft servers? 25565
What is the ISO 3166 alpha-2 code for South Africa? ZA
What Shodan search phrase can you use to discover how many Minecraft servers are currently online in South Africa?
Minecraft port:”25565″ country:”ZA”
How many Minecraft servers are currently online in South Africa? At the time of testing this lab, Total Results was 318.
b. Moxa is a supplier of devices that connect industrial equipment to the Internet. How many Moxa devices are running the Telnet service in Brazil?
Search phrase: moxa port:”23″ country:”BR”
Total results:
At the time of testing this lab, Total Results was 5
c. Use an Internet search or review Shodan help pages and tutorials to discover how you can filter your searches based on a range of IP addresses.
d. Mr. Robot is an American drama television series that chronicles the adventures of a cybersecurity engineer. In the series, the protagonist uses the Shodan search engine to research a fictional corporation. Use an Internet search to find the search string that was used to discover E Corp’s web server.
What string was used?
org:”Evil Corp” product:”Apache Tomcat”
Does the string work on the Shodan search engine? Yes
What IP address was returned by the search? 192.251.68.223
What is the URL for the IP address?
compute.evil-corp-usa.com
e. There are many home devices connected and controlled using IoT. Apply the methods previously used to search for “garage door” in the state of Michigan in the United States. What was the search string you used?
country:US state:MI “garage door”
How many results were returned?
16 at the time of this testing
What was the top city listed with the most connected garage doors?
Lansing, with 10 at the time of testing
What are the potential risks of someone having access to this information?
Hackers could take control of the garage door. It could then be opened to allow thefts from the garage or home
f. You can check to see if your IP address has any vulnerabilities by using the Internet of Things Scanner at the following address: https://iotscanner.bullguard.com. Click Check if I am on Shodan to allow the “Internet of Things Scanner” to scan your IP address. This process may take some time to complete.
