Module 7: Infrastructure and Automation Exam Answers
DevNet Associate (Version 1.0) 7.9 Module Exam – DevNet Associate Module 7 Exam Answers
1. What is the most common cause of IT outages?
- a threat actor targeting the enterprise equipment
- an experienced engineer implementing a configuration using automation
- an engineer misconfiguring a device or network with manual changes
- an experienced engineer using an open source product
2. What is an unopinionated component in a software ecosystem?
- a component that does not show an increased preference for specific companion components or architectures unless those components or architectures are necessary
- a component that is classified as open source and does not require the implementation of specific vendor products
- a component that may function in a limited ability in order to compensate for the selection of companion components or architectures
- a component that requires a specific companion component in order to provide full stack implementation
3. In the use of container technologies, what is a function of platform abstraction when considering the deployment of a product in a cloud environment?
- Traditional complementary software components such as a database server and web server would be implemented as a single containerized application.
- Applications require re-engineering in order to implement scalability and consolidation.
- A containerized app can run on a generically-specified host environment.
- Applications are aware of underlying hardware configurations and are customized to provide increased functionality.
4. A student is setting up the DEVASC-LAB VM and CSR1000v VM in VirtualBox that is installed on the local computer. Both VMs are imported to the VirtualBox successfully. The student starts both VMs and tries to verify communications to the CSR1000v VM by opening a web browser on the local computer and enters the URL https://192.168.56.101. After a few seconds, an error message displays that “The connection has timed out”. How can the student verify the IP address assigned by DHCP to the CSR1000v virtual router?
- Issue the ping 192.168.56.101 command on the local computer.
- Issue the show ip interface brief command in the CSR1000v VM.
- Issue the show running-config command in the CSR1000v VM.
- Issue the ifconfig command in the CSR1000v VM.
5. What is the historical correlation between software developers and IT operations?
- Developers had the job of creating applications. Operations had the job of verifying that these applications work for users.
- Operations had the job of brainstorming applications. Developers had the job of testing that these applications work for users and the business.
- Operations had the job of testing applications. Developers had the job of implementing these applications for clients.
- Developers had the job of testing applications. Operations had the job of implementing these applications for clients.
6. How is an error budget calculated in the DevOps/SRE culture?
- An error budget is the difference between the SLO and the SLI.
- An error budget is the difference between the SLO and 100% availability.
- An error budget is the difference between the SLO and the SLA.
- An error budget is the difference between the and 100% availability.
7. In reviewing a formalized agreement between an organization and a customer, what is the purpose of an SLI?
- An SLI is a specific set of steps for slowing releases as errors occur.
- An SLI is an easy to complete, external agreement that is set between the organization and the customer.
- An SLI is a benchmark metric used to determine and describe SLOs.
- An SLI is an agreed-upon number of errors per unit time.
8. What is the default shell commonly used on macOS and Linux?
- Bash
- csh
- tcsh
- Bourne
9. Which type of automation includes scripting that may be dangerous if the starting state is not completely known and controlled?
- stateful
- stateless
- declarative
- procedural
10. What is an imperative procedure?
- An ordered sequence of commands that is used to reach a specific end state.
- A set of commands that require administrator privileges and can only be executed on a local system.
- A set of commands that is piped to a remote host and immediately executed.
- A set of commands that examines a target and only performs the tasks needed to achieve the desired state.
11. Which statement describes the declarative static model?
- A declarative model will examine present circumstances and bring real infrastructure into alignment in order to reach a desired state.
- A declarative model will execute code that is sequentially task-driven instead of focusing on deployment-specific details.
- A declarative model will follow a specific order of sequential steps in order to effect changes on a target system.
- A declarative model will subdivide code into top-down sections and condition-driven handlers.
12. Refer to the exhibit. A user is working on Ansible on the local NMS to manage remote network devices. The user issues the ansible webservers -m ping command to test the communication. However, an error message returns. What are two possible causes for the error? (Choose two.)
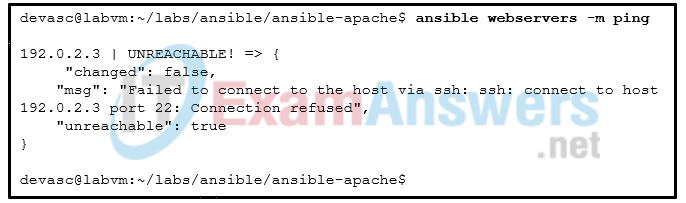
- The SSH credential is wrong.
- The destination host IP address is wrong.
- The switch -m should be -M
- The SSH client is not installed.
- The destination host alias is wrong.
- The SSH service does not start on the host.
13. Which component in the pyATS ecology handles bundling and running jobs?
- EasyPy
- AEtest
- Genie
- Clover
14. An engineer has just created a backup file of a Cisco VIRL network simulation. Which command should be used to compare the most recent .virl file with the previous backup file?
- diff
- pyats
- knife
- source
- list
15. While working in the Ansible code structure, which type of file contains a sequence of tasks, executed in top-down order?
- .virl
- .yml
- .py
- .txt
16. What is a standard command to create a Python virtual environment?
- sudo apt-get install python3-pip
- pip install [options] [package-index-options]…
- python3 -m venv /path/to/new/virtual/environment
- source bin/activate

The correct response
What is the most common cause of IT outages?