Time limit: 0
Quiz-summary
0 of 76 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
Information
DevNet Associate (200-901) Certification Practice Test Online
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 76 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- Answered
- Review
-
Question 1 of 76
1. Question
1 pointsA user is developing an application to remotely manage a network device through the API. The features of the API should support the client-server model, JSON or XML data format, and stateless operation. What is an API architecture style that the developer could use?Correct
Incorrect
Hint
RPC, SOAP, and REST are the three most popular types of API architectural styles. They all support the client-server model. RPC and REST can use XML or JSON. SOAP uses XML. REST requires that the communication between the client and the server remains stateless. -
Question 2 of 76
2. Question
1 pointsA user sends a request to add a loopback interface on a Cisco router through the REST API. Which response status code will the user expect to receive that indicates the request is fulfilled?Correct
Incorrect
Hint
With REST APIs, the response code 201 is with the status message of “Created”. It indicates that the request was fulfilled, and the requested resource was created. -
Question 3 of 76
3. Question
1 pointsRefer to the exhibit. Match the items needed in the Python script. (Not all options are used.)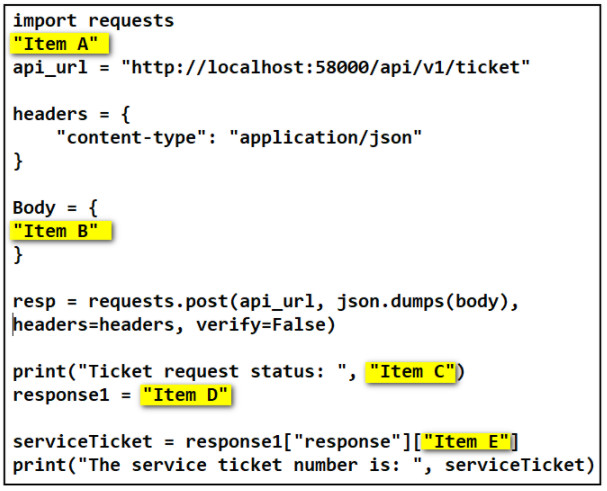 Correct
Correct
Incorrect
-
Question 4 of 76
4. Question
1 pointsRefer to the exhibit. A student is learning Python in the interpret mode. The student enters Python statements and after a while, an error message returns. What is a possible cause for the error?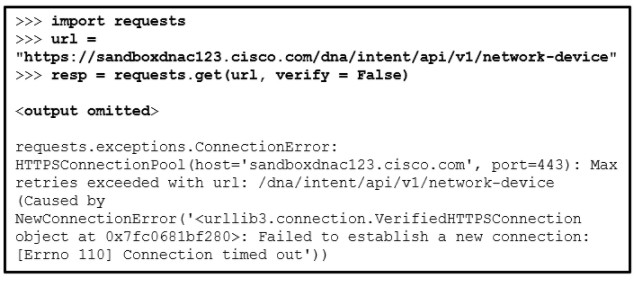 Correct
Correct
Incorrect
Hint
The error message indicates that the connection to the host cannot be established. The causes could be an internet connection issue, or the domain name of the host cannot be resolved by DNS servers because it is wrong. -
Question 5 of 76
5. Question
1 pointsRefer to the exhibit. A developer is constructing a Python script to check the link with a host at http://www.somehost.com/. Which function is performed by the script?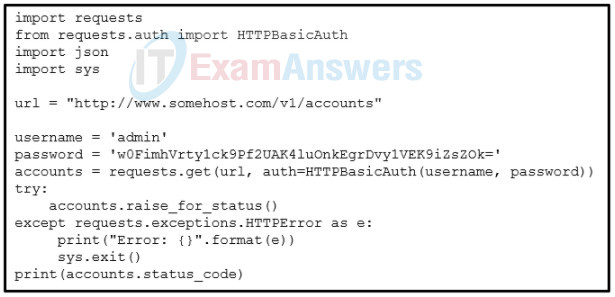 Correct
Correct
Incorrect
Hint
Common types of REST API authentication mechanisms include Basic, Bearer, and API Key. Basic authentication uses the standard Basic HTTP authentication scheme by specifying credentials such as username/password pairs. The username is in plain text and the password is encoded using Base64. -
Question 6 of 76
6. Question
1 pointsWhich situation illustrates the use of a webhook application?Correct
Incorrect
Hint
A webhook is an HTTP callback, or an HTTP POST, to a specified URL that notifies a registered application when an activity or event has occurred in one of the resources on the platform. Webhooks enable applications to get real-time data. With webhooks, applications are more efficient because they no longer need to have a polling mechanism. -
Question 7 of 76
7. Question
1 pointsRefer to the exhibit. A student is learning Python in the interpret mode. The student enters Python statements and an error message returns. What causes the error?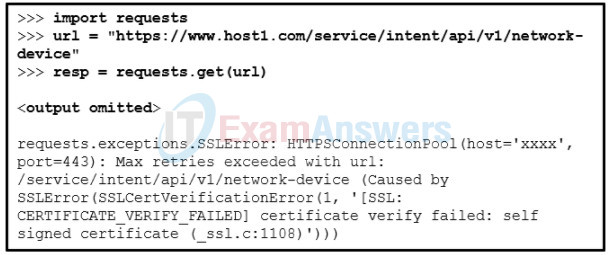 Correct
Correct
Incorrect
Hint
When the scheme of the REST API call URL is HTTPS, the connection will perform an SSL handshake between the client and the server with a Certificate Authority (CA). This handshake needs to be successful before the REST API request is even sent to the API server. The SSL handshake could fail if the certificate is invalid or it is self-signed. A user can specify if the SSL verification should be avoided by specifying “verify = False” as a parameter to the Python requests module, requests.get() method. The default is “verify = True”. -
Question 8 of 76
8. Question
1 pointsMatch the principles in the uniform interface constraint of the REST to the description. (Not all options are used.)Correct
Incorrect
-
Question 9 of 76
9. Question
1 pointsRefer to the exhibit. Which portion of the RESTful request specifies the API that is being requested.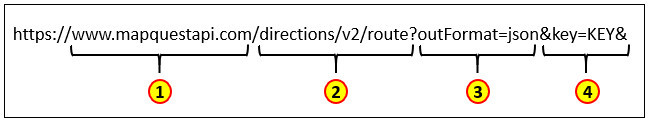 Correct
Correct
Incorrect
-
Question 10 of 76
10. Question
1 pointsA user is testing an application by sending requests to gather information from a network device through a REST API. The user reviews the API responses and notices an HTTP header string of “Cache-Control: max-age=3600, public”. Which two statements describe the HTTP directive? (Choose two.)Correct
Incorrect
Hint
The HTTP header string is a cache control directive that indicates that (1) the response content can be saved by any cache and (2) the cached content will expire in 3600 seconds unless it gets refreshed before it expires. -
Question 11 of 76
11. Question
1 pointsRefer to the exhibit. Which parameter is needed in the Python code (in place of the question mark) to test for an invalid URI condition?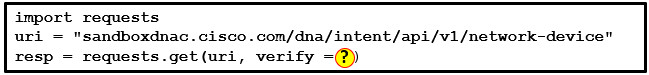 Correct
Correct
Incorrect
Hint
The script will test for an invalid URI condition if the verify parameter is set to False. -
Question 12 of 76
12. Question
1 pointsRefer to the exhibit. A student is learning the REST API call to a local host. Match the items needed in the curl command. (Not all options are used.) Correct
Correct
Incorrect
-
Question 13 of 76
13. Question
1 pointsA network engineer has been asked to automate some of the network management and configuration management. The engineer is going to use NETCONF. Why should the engineer consider also using YANG as part of this project?Correct
Incorrect
Hint
Yet Another Next Generation (YANG) is a standards-based data modeling language. NETCONF is a standards-based protocol designed to retrieve the information of network devices and to manage devices. Extensible Markup Language (XML) is an encoding protocol that provides the transport for NETCONF to communicate with devices using the YANG formatted configuration or operational data. An application that runs on a centralized management platform or laptop/desktop can use NETCONF to send requests to a network device for information or to make configuration changes. -
Question 14 of 76
14. Question
1 pointsMatch the Cisco NSO component to the description.Correct
Incorrect
Hint
- Service Manager: maintains device dependencies and provideds a service self start for triggering diagnostic tests
- Device Manager: deploys configuration changes to multiple devices through the use of distributed transactions
- Configuration Database: provides an internal API for locating network element configurations and automatic support for upgrade and downgrade of configuration data
-
Question 15 of 76
15. Question
1 pointsRefer to the exhibit. A user is working on Ansible on the local NMS to manage remote network devices. The user issues the ansible webservers -m ping command to test the communication. However, an error message returns. What are two possible causes for the error? (Choose two.)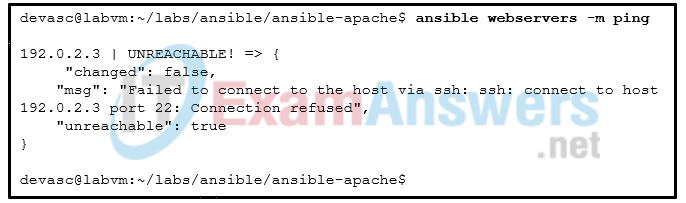 Correct
Correct
Incorrect
Hint
Ansible uses an inventory file called hosts that contains device information used by Ansible playbooks. The hosts file begins with an alias for the remote. After the alias, the hosts file specifies three variables that will be used by the Ansible playbook to access the device. These are the SSH credentials Ansible needs to securely access the remote host. The error message indicates that the SSH server on the destination host cannot be reached. The possible issue is either the SSH server is not running or the IP address configured in the hosts file is wrong. -
Question 16 of 76
16. Question
1 pointsThe development team in the IT department has decided to implement CI/CD. What are three characteristics of this strategy? (Choose three.)Correct
Incorrect
Hint
Continuous Integration/Continuous Deployment (CI/CD) is a philosophy for software development that includes automation as part of the process. Continuous integration attempts to eliminate the problem of conflicts that occur when new or updated code is applied to the main application. Even though there is a potential of a bad build being deployed to the users, companies can limit that impact by using a deployment strategy such as a rolling upgrade, canary pipeline, or blue-green deployment. -
Question 17 of 76
17. Question
1 pointsWhat are two features of the formal code review? (Choose two.)Correct
Incorrect
Hint
In a formal code review, developers have a series of meetings to review the whole codebase and go over the code line by line, discussing each one in detail. The formal code review process promotes discussion among all of the reviewers. -
Question 18 of 76
18. Question
1 pointsWhat are two benefits of model-driven programmability in infrastructure automation? (Choose two.)Correct
Incorrect
Hint
In summary, model-driven programmability does the following:- Provides configuration language that is human-readable
- Is model-based, structured, and computer-friendly
- Includes support for multiple model types, including native, OpenConfig, and IETF
- Uses a specification that is decoupled from transport, protocol end encoding
- Uses model-driven APIs for abstraction and simplification
- Leverages open-source and enjoys wide support
-
Question 19 of 76
19. Question
1 pointsMatch the component of Chef to the description.Correct
Incorrect
-
Question 20 of 76
20. Question
1 pointsA credit union has been growing very rapidly in the past 3 years and the IT department has been struggling to keep up. The department has always been criticized for the time it takes to program and implement change requests. The new CIO has decided to implement CI/CD. What are three benefits of this strategy? (Choose three.)Correct
Incorrect
Hint
Continuous Integration/Continuous Deployment (CI/CD) is a philosophy for software development that includes automation as part of the process and integrates with Agile development strategies. Application development occurs in small chunks and allows users to receive incremental changes, making it easier for adaptation to new software and reducing disruption. -
Question 21 of 76
21. Question
1 pointsRefer to the exhibit. A user is working on Ansible on the local NMS to manage remote network devices. Which file is the user creating?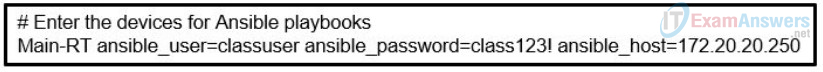 Correct
Correct
Incorrect
Hint
Ansible uses an inventory file called hosts that contains device information used by Ansible playbooks. The hosts file begins with an alias for the remote. After the alias, the hosts file specifies three variables that will be used by the Ansible playbook to access the device. These are the SSH credentials Ansible needs to securely access the remote host. -
Question 22 of 76
22. Question
1 pointsWhat two components form the Python-based network device test and validation solution of pyATS?Correct
Incorrect
Hint
PyATS uses Python for low-level code, but relies on Genie, a higher-level library system, in order to interact with network devices and perform testing. -
Question 23 of 76
23. Question
1 pointsWhat is immutable infrastructure in DevOps?Correct
Incorrect
-
Question 24 of 76
24. Question
1 pointsMatch the OWASP threat to the description.Correct
Incorrect
-
Question 25 of 76
25. Question
1 pointsWhich security device is used to make requests from multiple computers look like they all come from the same client?Correct
Incorrect
Hint
The job of a forward proxy is to make requests from multiple computers look like they all come from the same client. This is the opposite of a reverse proxy, which makes sure responses look like they all come from the same server. -
Question 26 of 76
26. Question
1 pointsWhich term is used to describe an automated process of testing and deploying code?Correct
Incorrect
Hint
The CI/CD (Continuous Integration and Continuous Delivery) pipeline is a software deployment philosophy that provides for a process of automated testing and deployment. -
Question 27 of 76
27. Question
1 pointsWhat is a benefit of using a bare metal deployment solution?Correct
Incorrect
-
Question 28 of 76
28. Question
1 pointsRefer to the exhibit. Which network service is being tested?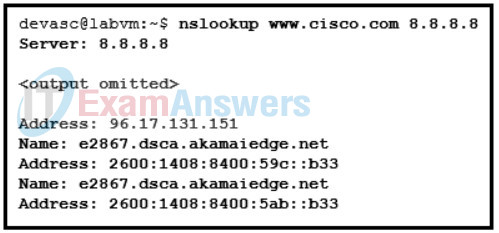 Correct
Correct
Incorrect
Hint
The nslookup command is available on nearly all operating systems. It is used for querying the Domain Name System (DNS) in order to obtain domain name to IP address mapping. -
Question 29 of 76
29. Question
1 pointsWhat are two benefits of using bare metal software deployment for a large enterprise deploying virtualized servers? (Choose two.)Correct
Incorrect
Hint
Bare metal deployment installs software directly on host hardware and provides applications with direct access to host hardware resources. This is more efficient and increases performance. -
Question 30 of 76
30. Question
1 pointsMatch the CI/CD software development philosophy with a description.Correct
Incorrect
-
Question 31 of 76
31. Question
1 pointsAn engineer is implementing an edge computing solution where a number of sensors are streaming a large amount data. Where should the computing capability be placed?Correct
Incorrect
Hint
The term edge computing refers to the practice of placing computing resources as close the actual sources of data as possible. -
Question 32 of 76
32. Question
1 pointsWhat type of attack is being attempted if code similar to this is entered in the login field on a web site? SELECT REPLACE (User_Name, ‘administrator’, ‘hacker’) Userlist FROM Credentials;Correct
Incorrect
Hint
This item is based on information contained in the presentation. A DoS (denial of service) attack prevents users from accessing network resources. A brute force attack attempts to guess the password of an account. A zero day attack is the first occurrence of a previously unknown virus or other malware. -
Question 33 of 76
33. Question
1 pointsA student is learning network automation using the DevNet site. Which DevNet resource allows users to search and share their programming skills and experiences?Correct
Incorrect
Hint
DevNet provides ways for community members to share with each other. These are called Exchanges. In the Code Exchange site, users can submit a repository that they have found useful for any technology area. Users can search for any keyword in the repository and get a list of results. -
Question 34 of 76
34. Question
1 pointsMatch the Meraki APIs for integration to the description. (Not all options are used.)Correct
Incorrect
Hint
The Meraki enterprise cloud-managed networking infrastructure service has five different APIs for integration:- Dashboard API: This a RESTful service for device provisioning, management, and monitoring.
- Webhook API: This is a real-time notification system for network alerts, covering events and network health.
- Location Streaming API: This is an HTTP POST method providing Wi-Fi and Bluetooth client location information (GPS, X/Y coordinates) based on Meraki Access Point (AP) map placement and client signal strength.
- External Captive Portal (EXCAP) API: This enables an organization to build out custom engagement models at Wi-Fi access points.
- MV Sense API: This is a combination of REST APIs and real-time MQTT stream supporting oversight of a physical space.
-
Question 35 of 76
35. Question
1 pointsMatch the node type in YANG to the description. (Not all options are used.)Correct
Incorrect
-
Question 36 of 76
36. Question
1 pointsA network administrator is evaluating Cisco UCS Manager products to deploy centralized management for the data center. The data center has about 500 physical servers. Which product should the administrator choose?Correct
Incorrect
Hint
The Cisco UCS Manager products provide scalability by integrating many components of a data center. The different management products directly relate to the number of servers being managed:- Cisco Integrated Management Controller (CIMC) can manage a single physical server.
- Cisco UCS Manager (UCSM) can manage up to 160 physical servers.
- Cisco UCS Central (UCSC) can manage up to 10,000 physical servers.
-
Question 37 of 76
37. Question
1 pointsRefer to the exhibit. Match the Python coding components to the location. (Not all options are used.)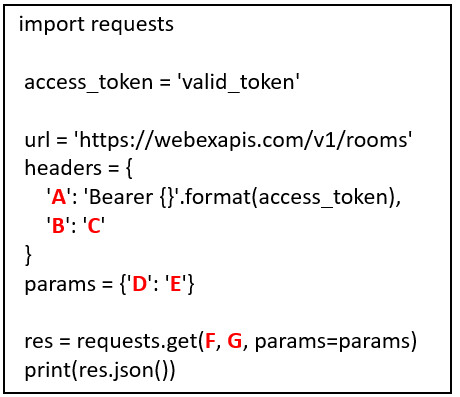 Correct
Correct
Incorrect
-
Question 38 of 76
38. Question
1 pointsMatch Cisco Advanced Malware Protection (AMP) solution components and product integration options to the description. (Not all options are used.)Correct
Incorrect
-
Question 39 of 76
39. Question
1 pointsWhich two statements describe the characteristics of the model-driven programmability implemented on Cisco IOS XE? (Choose two.)Correct
Incorrect
Hint
Cisco IOS XE is the next-generation programmable platform. Both NETCONF and RESTCONF are supported. Their connections should be authenticated using AAA credentials. RESTCONF runs over HTTPS which is enabled by the command ip http secure-server . The CLI command to enable RESTCONF is simply restconf . NETCONF uses SSH as a transport. NETCONF supports both running and candidate data stores, whereas RESTCONF supports only a running datastore. -
Question 40 of 76
40. Question
1 pointsWhich REST API supported by Cisco Unified Communications Manager is designed to enable end users to update and configure personal settings.?Correct
Incorrect
Hint
User Data Services (UDS) is a REST-based API that provides a mechanism for inserting, retrieving, updating, and removing data from the Unified Communication configuration database. The UDS API is designed to enable end users to update and configure personal settings. -
Question 41 of 76
41. Question
1 pointsMatch the principle to the software development method. (Not all options are used.)Correct
Incorrect
-
Question 42 of 76
42. Question
1 pointsMatch the method of organizing code with the description.Correct
Incorrect
-
Question 43 of 76
43. Question
1 pointsWhat is the outcome of performing a Git merge between two branches?Correct
Incorrect
Hint
When a Git merge is performed, the source branch is untouched and only the target branch is modified. -
Question 44 of 76
44. Question
1 pointsWhat is a philosophy associated with the test-driven development process?Correct
Incorrect
Hint
With the Test-Driven Development process, testing code is written before application code. The application code is then created with the single purpose of being able to barely pass the testing code. -
Question 45 of 76
45. Question
1 pointsWhat are two benefits of using a distributed version control system compared to other version control systems? (Choose two.)Correct
Incorrect
Hint
The distributed version control system is a peer-to-peer model that clones the full repository to client systems and allows every individual to work on any file, even at the same time. -
Question 46 of 76
46. Question
1 pointsMatch the symbols in a .diff file to the appropriate meaning.Correct
Incorrect
-
Question 47 of 76
47. Question
1 pointsMatch each stage of the Git distributed version control system with the decription.Correct
Incorrect
-
Question 48 of 76
48. Question
1 pointsWhich two components of XML code are contained within the XML prologue? (Choose two.)Correct
Incorrect
Hint
The XML prologue is placed as the first line in an XML file and contains the tag name xml and attributes that provide the version and the character encoding. -
Question 49 of 76
49. Question
1 pointsWhat process would need to be taken to extract information from XML and convert it into a form that Python could access conveniently?Correct
Incorrect
Hint
Parsing is the process of analyzing a message, separating it into component parts, and understanding the purpose of it in context. -
Question 50 of 76
50. Question
1 pointsWhat is the purpose of the subnet mask in conjunction with an IP address?Correct
Incorrect
Hint
With the IPv4 address, a subnet mask is also necessary. A subnet mask is a special type of IPv4 address that coupled with the IP address determines the subnet of which the device is a member. -
Question 51 of 76
51. Question
1 pointsA network app developer has configured an app to use a particular DNS server in order to test the application against a test database. The developer suspects a DNS issue. Which command could be used to verify a particular domain name?Correct
Incorrect
Hint
The nslookup command is used to obtain an IP address for a specific domain name by querying a DNS server. The desired domain name follows the command and optionally the IP address of a particular DNS server. -
Question 52 of 76
52. Question
1 pointsA developer is using Cisco AnyConnect to connect through a VPN to the DevNet Sandbox. Which AnyConnect preference would cause the connection to fail?Correct
Incorrect
Hint
If the connection fails when using Cisco AnyConnect to connect to the DevNet Sandbox, check login credentials for any typing errors, the VPN URL of the DevNet Sandbox, and clear the Block Untrusted Connections option in the AnyConnect preferences. -
Question 53 of 76
53. Question
1 pointsRefer to the exhibit. A company uses three servers to support a new network app. The network administrator is looking to include a load balancer as part of the network design to improve the performance of the application response. Where should the load balancer be installed?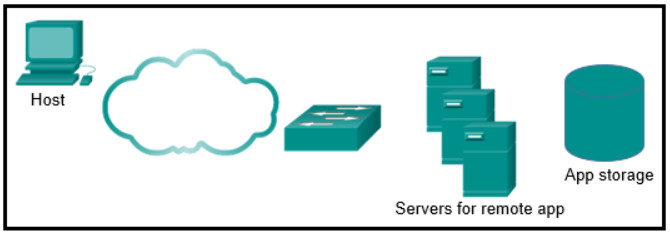 Correct
Correct
Incorrect
Hint
Because server load balancing distributes server requests across multiple servers, the load balancer should be attached to the same switch that the servers are on. -
Question 54 of 76
54. Question
1 pointsWhat are two reasons a VLAN would be used on a Layer 2 switch? (Choose two.)Correct
Incorrect
Hint
A virtual local-area network (VLAN) is a separate Layer 2 network that has its own broadcast domain. A Layer 3 device such as a router or multilayer switch is required to communicate between VLANs. -
Question 55 of 76
55. Question
1 pointsMatch the default port number to the network protocol. (Not all options are used.)Correct
Incorrect
-
Question 56 of 76
56. Question
1 pointsWhat are two symptoms that DNS is an issue when developing and testing network scripts? (Choose two.)Correct
Incorrect
Hint
Name resolution issues often manifest as lost network connectivity and authentication failures between a network app and a remote server. Common problems include defining the correct DNS server, a missing or incorrect DNS entry, an incorrect hostname, or a configuration issue on the DNS server being used. -
Question 57 of 76
57. Question
1 pointsWhat are two functions of MAC addresses in a LAN? (Choose two.)Correct
Incorrect
Hint
All Ethernet network devices have a unique Media Access Control (MAC) address that is burned into the network interface card (NIC). The MAC address is used to direct data from a particular device to a specific network destination. -
Question 58 of 76
58. Question
1 pointsWhich two port numbers are commonly used for Telnet? (Choose two.)Correct
Incorrect
Hint
Telnet commonly uses 23 or 992 whereas the secure protocol SSH uses port 22. DNS uses port 53. HTTP uses port 80 and HTTPS uses 443. NETCONF uses port 830. RESTCONF can use ports 8008, 8080, or 8888. -
Question 59 of 76
59. Question
1 pointsWhat are three characteristics of containers on a host server? (Choose three.)Correct
Incorrect
Hint
A container is an isolated environment where containerized applications run. It contains the application and all dependencies needed for the application to run. The containers on a physical server all share the same OS, are isolated from each other, and leverage the kernel of the host operating system to allow for quick starts. -
Question 60 of 76
60. Question
1 pointsWhat are two characteristics of containers that are running on the same host server? (Choose two.)Correct
Incorrect
-
Question 61 of 76
61. Question
1 pointsWhat is a benefit to an organization of implementing edge computing?Correct
Incorrect
Hint
The term edge computing refers to the practice of placing computing resources as close to the actual sources of data as possible. Deploying computer resources at the edge, can help to avoid high levels of data transfer across the network for performance or security purposes. -
Question 62 of 76
62. Question
1 pointsWhat is Bash?Correct
Incorrect
Hint
Bash is the name of the default script engine that lets you do things from the command line. It is the default shell for most Linux distributions. -
Question 63 of 76
63. Question
1 pointsIn which situation would a router be used?Correct
Incorrect
-
Question 64 of 76
64. Question
1 pointsWhich two statements accurately describe an advantage or a disadvantage when deploying NAT for IPv4 in a network? (Choose two.)Correct
Incorrect
Hint
Network Address Translation (NAT) is a technology that is implemented within IPv4 networks. One application of NAT is to use private IP addresses inside a network and use NAT to share a few public IP addresses for many internal hosts. In this way it provides a solution to slow down the IPv4 address depletion. However, since NAT hides the actual IP addresses that are used by end devices, it may cause problems for some applications that require end-to-end connectivity. -
Question 65 of 76
65. Question
1 pointsA user makes some REST API calls to a server and the responses from the server include third-party executable code. The user notices that the responses do not work. Which network device may prevent the third-party code from execution?Correct
Incorrect
-
Question 66 of 76
66. Question
1 pointsWhat is one function of a Layer 2 switch?Correct
Incorrect
Hint
A switch builds a MAC address table of MAC addresses and associated port numbers by examining the source MAC address found in inbound frames. To forward a frame onward, the switch examines the destination MAC address, looks in the MAC address for a port number associated with that destination MAC address, and sends it to the specific port. If the destination MAC address is not in the table, the switch forwards the frame out all ports except the inbound port that originated the frame. -
Question 67 of 76
67. Question
1 pointsA user is testing an application by sending requests to gather information from a network device through a REST API. The user expects a very large amount of data to be returned. The user requests that the network device sends the data back with the compression algorithm of gzip. What response header string would indicate that the return data is compressed as requested?Correct
Incorrect
Hint
If a large amount of return data is expected, the client can request that the return data be compressed with a specific compression algorithm. To request a data compression, the request must add the Accept-Encoding field to the API request header. For example, a header string of “Accept-Encoding: gzip” tells the server to compress the return data using the gzip algorithm. If the server fulfills the compression, it will send the response back with the compressed data and add the Content-Encoding field to the response header. The value of the Content-Encoding is the type of compression that was used. -
Question 68 of 76
68. Question
1 pointsWhich type of threat defense is provided by Cisco Umbrella?Correct
Incorrect
Hint
Cisco Umbrella serves as a first line of defense for an organization by blocking requests to malicious internet destinations. -
Question 69 of 76
69. Question
1 pointsHow does Cisco VIRL benefit the testing and development of code and automation?Correct
Incorrect
Hint
Cisco VIRL is used to build network simulations and it can duplicate the same code that runs inside actual Cisco products. The native configuration format is called a.virl file, which is a human-readable YAML file. -
Question 70 of 76
70. Question
1 pointsWhat CI/CD software development philosophy ensures code is always in a deployable state through the implementation of short development sprints.Correct
Incorrect
Hint
Continuous Delivery is the process of developing in sprints that are short enough so that the code is always in a deployable state. With Continuous Integration, small change sets are continuously integrated into the main code branch. Continuous Delivery means that those changes are engineered to be self-contained to the point where at any given time, you could deploy a working application. -
Question 71 of 76
71. Question
1 pointsFor what purpose are IPv4 addresses utilized?Correct
Incorrect
-
Question 72 of 76
72. Question
1 pointsWhat is the purpose of a default gateway?Correct
Incorrect
-
Question 73 of 76
73. Question
1 pointsRefer to the exhibit. A student is learning network automation by using an API. The student constructs a Python file to communicate with a Webex Teams server. Which two statements describe characteristics of the script? (Choose two.)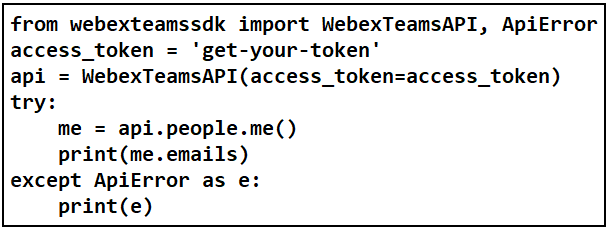 Correct
Correct
Incorrect
-
Question 74 of 76
74. Question
1 pointsMatch the cloud model with a description.Correct
Incorrect
-
Question 75 of 76
75. Question
1 pointsWhich software is used to create, run, and manage containers in a virtual environment?Correct
Incorrect
Hint
Containers provide many of the same benefits as VMs, such as workload isolation and the ability to run multiple workloads on a single machine, but a container shares the operating system of the host machine and uses container-specific binaries and libraries. Docker is a popular container engine. -
Question 76 of 76
76. Question
1 pointsA developer in a company receives feedback that an app is experiencing poor responses from an application on a server. The network engineer is looking for a solution that scales to multiple servers. Which technology should the engineer consider?Correct
Incorrect
Hint
Load balancing distributes server requests across multiple servers. The load balancer selects which server receives the client request and provides connectivity to device redundancy, high availability, and scalability.
