Check answers here:
Network Security v1.0 Final Exam Answers
Quiz-summary
0 of 152 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
- 143
- 144
- 145
- 146
- 147
- 148
- 149
- 150
- 151
- 152
Information
Network Security (Version1.0) – Final Test Online Full
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 152 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
- 143
- 144
- 145
- 146
- 147
- 148
- 149
- 150
- 151
- 152
- Answered
- Review
-
Question 1 of 152
1. Question
1 pointsWhich statement describes a difference between the Cisco ASA IOS CLI feature and the router IOS CLI feature?Correct
Incorrect
Hint
The ASA CLI is a proprietary OS which has a similar look and feel to the Cisco router IOS. Although it shares some common features with the router IOS, it has its unique features. For example, an ASA CLI command can be executed regardless of the current configuration mode prompt. The IOS do command is not required or recognized. Both the ASA CLI and the router CLI use the # symbol to indicate the EXEC mode. Both CLIs use the Tab key to complete a partially typed command. Different from the router IOS, the ASA provides a help command that provides a brief command description and syntax for certain commands. -
Question 2 of 152
2. Question
1 pointsRefer to the exhibit. A network administrator is configuring AAA implementation on an ASA device. What does the option link3 indicate?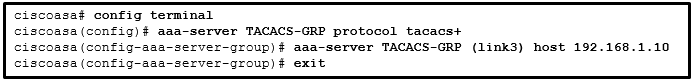 Correct
Correct
Incorrect
-
Question 3 of 152
3. Question
1 pointsWhat provides both secure segmentation and threat defense in a Secure Data Center solution?Correct
Incorrect
-
Question 4 of 152
4. Question
1 pointsWhat are the three core components of the Cisco Secure Data Center solution? (Choose three.)Correct
Incorrect
Hint
Secure segmentation is used when managing and organizing data in a data center. Threat defense includes a firewall and intrusion prevention system (IPS). Data center visibility is designed to simplify operations and compliance reporting by providing consistent security policy enforcement. -
Question 5 of 152
5. Question
1 pointsWhat are three characteristics of ASA transparent mode? (Choose three.)Correct
What are three characteristics of ASA transparent mode? (Choose three.)
Incorrect
-
Question 6 of 152
6. Question
1 pointsWhat is needed to allow specific traffic that is sourced on the outside network of an ASA firewall to reach an internal network?Correct
Incorrect
Hint
In order to explicitly permit traffic from an interface with a lower security level to an interface with a higher security level, an ACL must be configured. By default, traffic will only flow from a higher security level to a lower. -
Question 7 of 152
7. Question
1 pointsWhat will be the result of failed login attempts if the following command is entered into a router?login block-for 150 attempts 4 within 90
Correct
Incorrect
Hint
The components of the login block-for 150 attempts 4 within 90 command are as follows: The expression block-for 150 is the time in seconds that logins will be blocked. The expression attempts 4 is the number of failed attempts that will trigger the blocking of login requests. The expression within 90 is the time in seconds in which the 4 failed attempts must occur. -
Question 8 of 152
8. Question
1 pointsWhich two tasks are associated with router hardening? (Choose two.)Correct
Incorrect
-
Question 9 of 152
9. Question
1 pointsWhich threat protection capability is provided by Cisco ESA?Correct
Incorrect
Hint
Email is a top attack vector for security breaches. Cisco ESA includes many threat protection capabilities for email such as spam protection, forged email detection, and Cisco advanced phishing protection. -
Question 10 of 152
10. Question
1 pointsWhich three types of traffic are allowed when the authentication port-control auto command has been issued and the client has not yet been authenticated? (Choose three.)Correct
Incorrect
Hint
Until the workstation is authenticated, 802.1X access control enables only Extensible Authentication Protocol over LAN (EAPOL), Cisco Discovery Protocol (CDP), and Spanning Tree Protocol (STP) traffic through the port to which the workstation is connected. After authentication succeeds, normal traffic can pass through the port. -
Question 11 of 152
11. Question
1 pointsWhich statement describes a characteristic of the IKE protocol?Correct
Incorrect
-
Question 12 of 152
12. Question
1 pointsWhich action do IPsec peers take during the IKE Phase 2 exchange?Correct
Incorrect
Hint
The IKE protocol executes in two phases. During Phase 1 the two sides negotiate IKE policy sets, authenticate each other, and set up a secure channel. During the second phase IKE negotiates security associations between the peers. -
Question 13 of 152
13. Question
1 pointsWhat are two hashing algorithms used with IPsec AH to guarantee authenticity? (Choose two.)Correct
Incorrect
Hint
The IPsec framework uses various protocols and algorithms to provide data confidentiality, data integrity, authentication, and secure key exchange. Two popular algorithms used to ensure that data is not intercepted and modified (data integrity and authenticity) are MD5 and SHA. -
Question 14 of 152
14. Question
1 pointsWhich command raises the privilege level of the ping command to 7?Correct
Incorrect
-
Question 15 of 152
15. Question
1 pointsWhat is a characteristic of a role-based CLI view of router configuration?Correct
Incorrect
Hint
A CLI view has no command hierarchy, and therefore, no higher or lower views. Deleting a superview does not delete the associated CLI views. Only a root view user can configure a new view and add or remove commands from the existing views. -
Question 16 of 152
16. Question
1 pointsWhat is a limitation to using OOB management on a large enterprise network?Correct
Incorrect
Hint
OOB management provides a dedicated management network without production traffic. Devices within that network, such as terminal servers, have direct console access for management purposes. Because in-band management runs over the production network, secure tunnels or VPNs may be needed. Failures on the production network may not be communicated to the OOB network administrator because the OOB management network may not be affected -
Question 17 of 152
17. Question
1 pointsRefer to the exhibit. A corporate network is using NTP to synchronize the time across devices. What can be determined from the displayed output?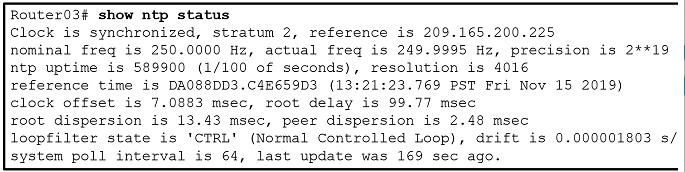 Correct
Correct
Incorrect
-
Question 18 of 152
18. Question
1 pointsWhat are two security measures used to protect endpoints in the borderless network? (Choose two.)Correct
Incorrect
Hint
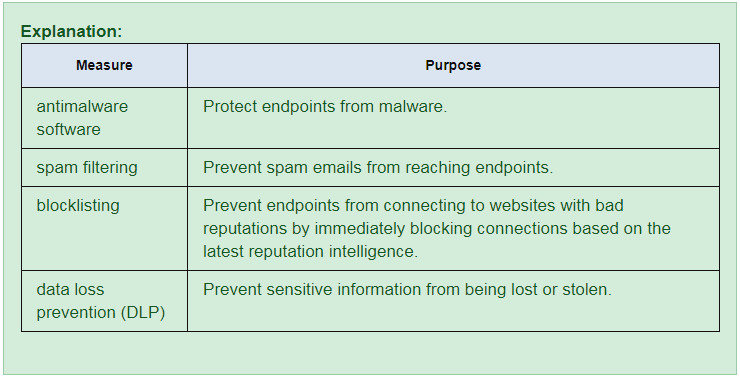
-
Question 19 of 152
19. Question
1 pointsRefer to the exhibit. Which two conclusions can be drawn from the syslog message that was generated by the router? (Choose two.)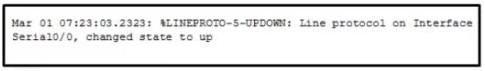 Correct
Correct
Incorrect
Hint
The message is a level 5 notification message as shown in the %LINEPROTO-5 section of the output. Messages reporting the link status are common and do not require replacing the interface or reconfiguring the interface. The date and time displayed at the beginning of the message indicates that service timestamps have been configured on the router. -
Question 20 of 152
20. Question
1 pointsWhich two types of hackers are typically classified as grey hat hackers? (Choose two.)Correct
Incorrect
Hint
Grey hat hackers may do unethical or illegal things, but not for personal gain or to cause damage. Hacktivists use their hacking as a form of political or social protest, and vulnerability brokers hack to uncover weaknesses and report them to vendors. Depending on the perspective one possesses, state-sponsored hackers are either white hat or black hat operators. Script kiddies create hacking scripts to cause damage or disruption. Cyber criminals use hacking to obtain financial gain by illegal means. -
Question 21 of 152
21. Question
1 pointsWhen describing malware, what is a difference between a virus and a worm?Correct
Incorrect
Hint
Malware can be classified as follows: Virus (self-replicates by attaching to another program or file) Worm (replicates independently of another program) Trojan horse (masquerades as a legitimate file or program) Rootkit (gains privileged access to a machine while concealing itself) Spyware (collects information from a target system) Adware (delivers advertisements with or without consent) Bot (waits for commands from the hacker) Ransomware (holds a computer system or data captive until payment isreceived) -
Question 22 of 152
22. Question
1 pointsWhich type of packet is unable to be filtered by an outbound ACL?Correct
Incorrect
Hint
Traffic that originates within a router such as pings from a command prompt, remote access from a router to another device, or routing updates are not affected by outbound access lists. The traffic must flow through the router in order for the router to apply the ACEs. -
Question 23 of 152
23. Question
1 pointsConsider the access list command applied outbound on a router serial interface.access-list 100 deny icmp 192.168.10.0 0.0.0.255 any echo reply
What is the effect of applying this access list command?Correct
Incorrect
-
Question 24 of 152
24. Question
1 pointsWhich command is used to activate an IPv6 ACL named ENG_ACL on an interface so that the router filters traffic prior to accessing the routing table?Correct
Incorrect
Hint
For the purpose of applying an access list to a particular interface, the ipv6 traffic-filter IPv6 command is equivalent to the access-group IPv4 command. The direction in which the traffic is examined (in or out) is also required. -
Question 25 of 152
25. Question
1 pointsWhat technology has a function of using trusted third-party protocols to issue credentials that are accepted as an authoritative identity?Correct
Incorrect
Hint
Digital certificates are used to prove the authenticity and integrity of PKI certificates, but a PKI Certificate Authority is a trusted third-party entity that issues PKI certificates. PKI certificates are public information and are used to provide authenticity, confidentiality, integrity, and nonrepudiation services that can scale to large requirements. -
Question 26 of 152
26. Question
1 pointsWhat are two methods to maintain certificate revocation status? (Choose two.)Correct
Incorrect
Hint
A digital certificate might need to be revoked if its key is compromised or it is no longer needed. The certificate revocation list (CRL) and Online Certificate Status Protocol (OCSP), are two common methods to check a certificate revocation status. -
Question 27 of 152
27. Question
1 pointsWhich protocol is an IETF standard that defines the PKI digital certificate format?Correct
Incorrect
Hint
To address the interoperability of different PKI vendors, IETF published the Internet X.509 Public Key Infrastructure Certificate Policy and Certification Practices Framework (RFC 2527). The standard defines the format of a digital certificate. -
Question 28 of 152
28. Question
1 pointsA network administrator is configuring DAI on a switch. Which command should be used on the uplink interface that connects to a router?Correct
Incorrect
Hint
In general, a router serves as the default gateway for the LAN or VLAN on the switch. Therefore, the uplink interface that connects to a router should be a trusted port for forwarding ARP requests. -
Question 29 of 152
29. Question
1 pointsWhat is the best way to prevent a VLAN hopping attack?Correct
Incorrect
Hint
VLAN hopping attacks rely on the attacker being able to create a trunk link with a switch. Disabling DTP and configuring user-facing ports as static access ports can help prevent these types of attacks. Disabling the Spanning Tree Protocol (STP) will not eliminate VLAN hopping attacks. -
Question 30 of 152
30. Question
1 pointsWhat would be the primary reason an attacker would launch a MAC address overflow attack?Correct
Incorrect
-
Question 31 of 152
31. Question
1 pointsWhat is the main difference between the implementation of IDS and IPS devices?Correct
Incorrect
Hint
An IPS is deployed in inline mode and will not allow malicious traffic to enter the internal network without first analyzing it. An advantage of this is that it can stop an attack immediately. An IDS is deployed in promiscuous mode. It copies the traffic patterns and analyzes them offline, thus it cannot stop the attack immediately and it relies on another device to take further actions once it detects an attack. Being deployed in inline mode, an IPS can negatively impact the traffic flow. Both IDS and IPS can use signature-based technology to detect malicious packets. An IPS cannot replace other security devices, such as firewalls, because they perform different tasks. -
Question 32 of 152
32. Question
1 pointsWhich attack is defined as an attempt to exploit software vulnerabilities that are unknown or undisclosed by the vendor?Correct
Incorrect
-
Question 33 of 152
33. Question
1 pointsWhat are the three signature levels provided by Snort IPS on the 4000 Series ISR? (Choose three.)Correct
Incorrect
-
Question 34 of 152
34. Question
1 pointsWhat are three attributes of IPS signatures? (Choose three.)Correct
Incorrect
Hint
IPS signatures have three distinctive attributes: type trigger (alarm) action -
Question 35 of 152
35. Question
1 pointsWhich two features are included by both TACACS+ and RADIUS protocols? (Choose two.)Correct
Incorrect
Hint
Both TACACS+ and RADIUS support password encryption (TACACS+ encrypts all communication) and use Layer 4 protocol (TACACS+ uses TCP and RADIUS uses UDP). TACACS+ supports separation of authentication and authorization processes, while RADIUS combines authentication and authorization as one process. RADIUS supports remote access technology, such as 802.1x and SIP; TACACS+ does not. -
Question 36 of 152
36. Question
1 pointsWhat function is provided by the RADIUS protocol?Correct
Incorrect
Hint
When an AAA user is authenticated, RADIUS uses UDP port 1645 or 1812 for authentication and UDP port 1646 or 1813 for accounting. TACACS provides separate authorization and accounting services. When a RADIUS client is authenticated, it is also authorized. TACACS provides secure connectivity using TCP port 49. RADIUS hides passwords during transmission and does not encrypt the complete packet. -
Question 37 of 152
37. Question
1 pointsWhat are three characteristics of the RADIUS protocol? (Choose three.)Correct
Incorrect
Hint
RADIUS is an open-standard AAA protocol using UDP port 1645 or 1812 for authentication and UDP port 1646 or 1813 for accounting. It combines authentication and authorization into one process; thus, a password is encrypted for transmission while the rest of the packet will be sent in plain text. RADIUS offers the expedited service and more comprehensive accounting desired by remote-access providers but provides lower security and less potential for customization than TACACS+. -
Question 38 of 152
38. Question
1 pointsWhich zone-based policy firewall zone is system-defined and applies to traffic destined for the router or originating from the router?Correct
Incorrect
-
Question 39 of 152
39. Question
1 pointsWhat are two benefits of using a ZPF rather than a Classic Firewall? (Choose two.)Correct
Incorrect
Hint
There are several benefits of a ZPF: – It is not dependent on ACLs. – The router security posture is to block unless explicitly allowed. – Policies are easy to read and troubleshoot with C3PL. – One policy affects any given traffic, instead of needing multiple ACLs and inspection actions. -
Question 40 of 152
40. Question
1 pointsHow does a firewall handle traffic when it is originating from the private network and traveling to the DMZ network?Correct
Incorrect
Hint
With a three interface firewall design that has internal, external, and DMZ connections, typical configurations include the following: – Traffic originating from DMZ destined for the internal network is normally blocked. – Traffic originating from the DMZ destined for external networks is typically permitted based on what services are being used in the DMZ. – Traffic originating from the internal network destined from the DMZ is normally inspected and allowed to return. – Traffic originating from external networks (the public network) is typically allowed in the DMZ only for specific services. -
Question 41 of 152
41. Question
1 pointsWhich two protocols generate connection information within a state table and are supported for stateful filtering? (Choose two.)Correct
Incorrect
-
Question 42 of 152
42. Question
1 pointsWhich type of firewall is supported by most routers and is the easiest to implement?Correct
Incorrect
Hint
Packet Filtering (Stateless) Firewall uses a simple policy table look-up that filters traffic based on specific criteria and is considered the easiest firewall to implement. -
Question 43 of 152
43. Question
1 pointsWhat network testing tool would an administrator use to assess and validate system configurations against security policies and compliance standards?Correct
Incorrect
Hint
Tripwire – This tool assesses and validates IT configurations against internal policies, compliance standards, and security best practices. -
Question 44 of 152
44. Question
1 pointsWhat type of network security test can detect and report changes made to network systems?Correct
Incorrect
Hint
Integrity checking is used to detect and report changes made to systems. Vulnerability scanning is used to find weaknesses and misconfigurations on network systems. Network scanning is used to discover available resources on the network. -
Question 45 of 152
45. Question
1 pointsWhat network security testing tool has the ability to provide details on the source of suspicious network activity?Correct
Incorrect
-
Question 46 of 152
46. Question
1 pointsHow do modern cryptographers defend against brute-force attacks?Correct
Incorrect
Hint
In a brute-force attack, an attacker tries every possible key with the decryption algorithm knowing that eventually one of them will work. To defend against the brute-force attacks, modern cryptographers have as an objective to have a keyspace (a set of all possible keys) large enough so that it takes too much money and too much time to accomplish a brute-force attack. A security policy requiring passwords to be changed in a predefined interval further defend against the brute-force attacks. The idea is that passwords will have been changed before an attacker exhausts the keyspace. -
Question 47 of 152
47. Question
1 pointsHow does a Caesar cipher work on a message?Correct
Incorrect
-
Question 48 of 152
48. Question
1 pointsWhat is the main factor that ensures the security of encryption of modern algorithms?Correct
Incorrect
Hint
With most modern algorithms, successful decryption requires knowledge of the appropriate cryptographic keys. This means that the security of encryption lies in the secrecy of the keys, not the algorithm. -
Question 49 of 152
49. Question
1 pointsWhat is the next step in the establishment of an IPsec VPN after IKE Phase 1 is complete?Correct
Incorrect
Hint
Establishing an IPsec tunnel involves five steps: detection of interesting traffic defined by an ACL IKE Phase 1 in which peers negotiate ISAKMP SA policy IKE Phase 2 in which peers negotiate IPsec SA policy Creation of the IPsec tunnel Termination of the IPsec tunnel -
Question 50 of 152
50. Question
1 pointsRefer to the exhibit. What algorithm will be used for providing confidentiality?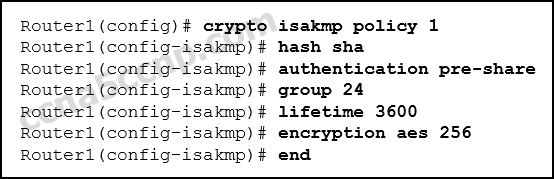 Correct
Correct
Incorrect
Hint
The IPsec framework uses various protocols and algorithms to provide data confidentiality, data integrity, authentication, and secure key exchange. Two popular algorithms that are used to ensure that data is not intercepted and modified (data integrity) are MD5 and SHA. AES is an encryption protocol and provides data confidentiality. DH (Diffie-Hellman) is an algorithm that is used for key exchange. RSA is an algorithm used for authentication. -
Question 51 of 152
51. Question
1 pointsAfter issuing a show run command, an analyst notices the following command:crypto ipsec transform-set MYSET esp-aes 256 esp-md5-hmac
What is the purpose of this command?Correct
Incorrect
-
Question 52 of 152
52. Question
1 pointsWhich algorithm can ensure data integrity?Correct
Incorrect
Hint
Data integrity guarantees that the message was not altered in transit. Integrity is ensured by implementing either of the Secure Hash Algorithms (SHA-2 or SHA-3). The MD5 message digest algorithm is still widely in use. -
Question 53 of 152
53. Question
1 pointsA company implements a security policy that ensures that a file sent from the headquarters office to the branch office can only be opened with a predetermined code. This code is changed every day. Which two algorithms can be used to achieve this task? (Choose two.)Correct
Incorrect
Hint
The task to ensure that only authorized personnel can open a file is data confidentiality, which can be implemented with encryption. AES and 3DES are two encryption algorithms. HMAC can be used for ensuring origin authentication. MD5 and SHA-1 can be used to ensure data integrity. -
Question 54 of 152
54. Question
1 pointsA network technician has been asked to design a virtual private network between two branch routers. Which type of cryptographic key should be used in this scenario?Correct
Incorrect
Hint
A symmetric key requires that both routers have access to the secret key that is used to encrypt and decrypt exchanged data. -
Question 55 of 152
55. Question
1 pointsWhich two options can limit the information discovered from port scanning? (Choose two.)Correct
Incorrect
Hint
Using an intrusion prevention system (IPS) and firewall can limit the information that can be discovered with a port scanner. Authentication, encryption, and passwords provide no protection from loss of information from port scanning. -
Question 56 of 152
56. Question
1 pointsAn administrator discovers that a user is accessing a newly established website that may be detrimental to company security. What action should the administrator take first in terms of the security policy?Correct
Incorrect
-
Question 57 of 152
57. Question
1 pointsIf AAA is already enabled, which three CLI steps are required to configure a router with a specific view? (Choose three.)Correct
Incorrect
Hint
There are five steps involved to create a view on a Cisco router. 1) AAA must be enabled. 2) the view must be created. 3) a secret password must be assigned to the view. 4) commands must be assigned to the view. 5) view configuration mode must be exited. -
Question 58 of 152
58. Question
1 pointsRefer to the exhibit. A network administrator configures a named ACL on the router. Why is there no output displayed when the show command is issued?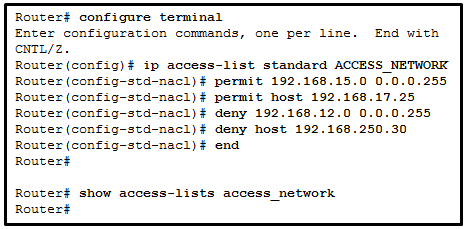 Correct
Correct
Incorrect
-
Question 59 of 152
59. Question
1 pointsACLs are used primarily to filter traffic. What are two additional uses of ACLs? (Choose two.):Correct
Incorrect
Hint
ACLs are used to filter traffic to determine which packets will be permitted or denied through the router and which packets will be subject to policy-based routing. ACLs can also be used to identify traffic that requires NAT and QoS services. Prefix lists are used to control which routes will be redistributed or advertised to other routers. -
Question 60 of 152
60. Question
1 pointsWhat two features are added in SNMPv3 to address the weaknesses of previous versions of SNMP? (Choose two.)Correct
Incorrect
-
Question 61 of 152
61. Question
1 pointsWhat network testing tool is used for password auditing and recovery?Correct
Incorrect
-
Question 62 of 152
62. Question
1 pointsWhich type of firewall makes use of a server to connect to destination devices on behalf of clients?Correct
Incorrect
Hint
An application gateway firewall, also called a proxy firewall, filters information at Layers 3, 4, 5, and 7 of the OSI model. It uses a proxy server to connect to remote servers on behalf of clients. Remote servers will see only a connection from the proxy server, not from the individual clients. -
Question 63 of 152
63. Question
1 pointsRefer to the exhibit. What will be displayed in the output of the show running-config object command after the exhibited configuration commands are entered on an ASA 5506-X?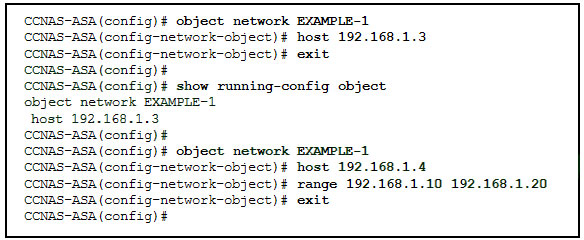 Correct
Correct
Incorrect
Hint
The show running-config object command is used to display or verify the IP address/mask pair within the object. There can only be one statement in the network object. Entering a second IP address/mask pair will replace the existing configuration. -
Question 64 of 152
64. Question
1 pointsRefer to the exhibit. According to the command output, which three statements are true about the DHCP options entered on the ASA? (Choose three.)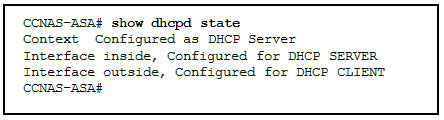 Correct
Correct
Incorrect
-
Question 65 of 152
65. Question
1 pointsWhich two statements describe the characteristics of symmetric algorithms? (Choose two.)Correct
Incorrect
Hint
Symmetric encryption algorithms use the same key (also called shared secret) to encrypt and decrypt the data. In contrast, asymmetric encryption algorithms use a pair of keys, one for encryption and another for decryption. -
Question 66 of 152
66. Question
1 pointsA web server administrator is configuring access settings to require users to authenticate first before accessing certain web pages. Which requirement of information security is addressed through the configuration?Correct
Incorrect
Hint
Confidentiality ensures that data is accessed only by authorized individuals. Authentication will help verify the identity of the individuals. -
Question 67 of 152
67. Question
1 pointsThe use of 3DES within the IPsec framework is an example of which of the five IPsec building blocks?Correct
Incorrect
Hint
The IPsec framework consists of five building blocks. Each building block performs a specific securty function via specific protocols. The function of providing confidentiality is provided by protocols such as DES, 3DES, and AES. -
Question 68 of 152
68. Question
1 pointsWhat function is provided by Snort as part of the Security Onion?Correct
Incorrect
Hint
Snort is a NIDS integrated into Security Onion. It is an important source of the alert data that is indexed in the Sguil analysis tool. Snort uses rules and signatures to generate alerts. -
Question 69 of 152
69. Question
1 pointsWhat are two drawbacks to using HIPS? (Choose two.)Correct
Incorrect
-
Question 70 of 152
70. Question
1 pointsIn an AAA-enabled network, a user issues the configure terminal command from the privileged executive mode of operation. What AAA function is at work if this command is rejected?Correct
Incorrect
Hint
Authentication must ensure that devices or end users are legitimate. Authorization is concerned with allowing and disallowing authenticated users access to certain areas and programs on the network. The configure terminal command is rejected because the user is not authorized to execute the command. -
Question 71 of 152
71. Question
1 pointsA company has a file server that shares a folder named Public. The network security policy specifies that the Public folder is assigned Read-Only rights to anyone who can log into the server while the Edit rights are assigned only to the network admin group. Which component is addressed in the AAA network service framework?Correct
Incorrect
Hint
After a user is successfully authenticated (logged into the server), the authorization is the process of determining what network resources the user can access and what operations (such as read or edit) the user can perform. -
Question 72 of 152
72. Question
1 pointsWhat is a characteristic of a DMZ zone?Correct
Incorrect
Hint
The characteristics of a DMZ zone are as follows: Traffic originating from the inside network going to the DMZ network is permitted. Traffic originating from the outside network going to the DMZ network is selectively permitted. Traffic originating from the DMZ network going to the inside network is denied. -
Question 73 of 152
73. Question
1 pointsWhich measure can a security analyst take to perform effective security monitoring against network traffic encrypted by SSL technology?Correct
Incorrect
Hint
Deploy a Cisco SSL Appliance to decrypt SSL traffic and send it to intrusion prevention system (IPS) appliances to identify risks normally hidden by SSL. -
Question 74 of 152
74. Question
1 pointsRefer to the exhibit. Port security has been configured on the Fa 0/12 interface of switch S1. What action will occur when PC1 is attached to switch S1 with the applied configuration?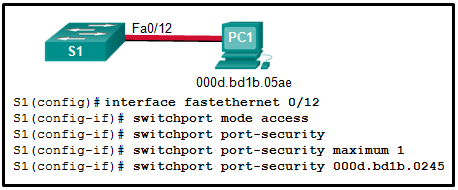 Correct
Correct
Incorrect
Hint
Manual configuration of the single allowed MAC address has been entered for port fa0/12. PC1 has a different MAC address and when attached will cause the port to shut down (the default action), a log message to be automatically created, and the violation counter to increment. The default action of shutdown is recommended because the restrict option might fail if an attack is underway. -
Question 75 of 152
75. Question
1 pointsWhat security countermeasure is effective for preventing CAM table overflow attacks?Correct
Incorrect
Hint
Port security is the most effective method for preventing CAM table overflow attacks. Port security gives an administrator the ability to manually specify what MAC addresses should be seen on given switch ports. It provides a method for limiting the number of MAC addresses that can be dynamically learned over a switch port. -
Question 76 of 152
76. Question
1 pointsWhat are two examples of DoS attacks? (Choose two.)Correct
Incorrect
Hint
The buffer overflow and ping of death DoS attacks exploit system memory-related flaws on a server by sending an unexpected amount of data or malformed data to the server. -
Question 77 of 152
77. Question
1 pointsWhich method is used to identify interesting traffic needed to create an IKE phase 1 tunnel?Correct
Incorrect
-
Question 78 of 152
78. Question
1 pointsWhen the CLI is used to configure an ISR for a site-to-site VPN connection, which two items must be specified to enable a crypto map policy? (Choose two.)Correct
Incorrect
Hint
After the crypto map command in global configuration mode has been issued, the new crypto map will remain disabled until a peer and a valid access list have been configured. -
Question 79 of 152
79. Question
1 pointsHow does a firewall handle traffic when it is originating from the public network and traveling to the DMZ network?Correct
Incorrect
Hint
Traffic originating from the public network and traveling toward the DMZ is selectively permitted and inspected. This type of traffic is typically email, DNS, HTTP, or HTTPS traffic. Return traffic from the DMZ to the public network is dynamically permitted. -
Question 80 of 152
80. Question
1 pointsA client connects to a Web server. Which component of this HTTP connection is not examined by a stateful firewall?Correct
Incorrect
Hint
Stateful firewalls cannot prevent application layer attacks because they do not examine the actual contents of the HTTP connection. -
Question 81 of 152
81. Question
1 pointsWhich network monitoring technology uses VLANs to monitor traffic on remote switches?Correct
Incorrect
Hint
Remote SPAN (RSPAN) enables a network administrator to use the flexibility of VLANs to monitor traffic on remote switches. -
Question 82 of 152
82. Question
1 pointsWhich rule action will cause Snort IPS to block and log a packet?Correct
Incorrect
Hint
Snort IPS mode can perform all the IDS actions plus the following: – Drop – Block and log the packet. – Reject – Block the packet, log it, and then send a TCP reset if the protocol is TCP or an ICMP port unreachable message if the protocol is UDP. – Sdrop – Block the packet but do not log it. -
Question 83 of 152
83. Question
1 pointsWhat is typically used to create a security trap in the data center facility?Correct
Incorrect
Hint
Security traps provide access to the data halls where data center data is stored. As shown in the figure below, a security trap is similar to an air lock. A person must first enter the security trap using their badge ID proximity card. After the person is inside the security trap, facial recognition, fingerprints, or other biometric verifications are used to open the second door. The user must repeat the process to exit the data hall. -
Question 84 of 152
84. Question
1 pointsA company is concerned with leaked and stolen corporate data on hard copies. Which data loss mitigation technique could help with this situation?Correct
Incorrect
Hint
Confidential data should be shredded when no longer required. Otherwise, a thief could retrieve discarded reports and gain valuable information. -
Question 85 of 152
85. Question
1 pointsUpon completion of a network security course, a student decides to pursue a career in cryptanalysis. What job would the student be doing as a cryptanalyst?Correct
Incorrect
Hint
Cryptanalysis is the practice and study of determining the meaning of encrypted information (cracking the code), without access to the shared secret key. This is also known as codebreaking. -
Question 86 of 152
86. Question
1 pointsWhat command is used on a switch to set the port access entity type so the interface acts only as an authenticator and will not respond to any messages meant for a supplicant?Correct
Incorrect
Hint
Sets the Port Access Entity (PAE) type. dot1x pae [supplicant | authenticator | both] supplicant—The interface acts only as a supplicant and does not respond to messages that are meant for an authenticator. authenticator-—The interface acts only as an authenticator and does not respond to any messages meant for a supplicant. both—The interface behaves both as a supplicant and as an authenticator and thus does respond to all dot1x messages. -
Question 87 of 152
87. Question
1 pointsWhat are two disadvantages of using an IDS? (Choose two.)Correct
Incorrect
Hint
The disadvantage of operating with mirrored traffic is that the IDS cannot stop malicious single-packet attacks from reaching the target before responding to the attack. Also, an IDS often requires assistance from other networking devices, such as routers and firewalls, to respond to an attack. An advantage of an IDS is that by working offline using mirrored traffic, it has no impact on traffic flow. -
Question 88 of 152
88. Question
1 pointsWhat ports can receive forwarded traffic from an isolated port that is part of a PVLAN?Correct
Incorrect
Hint
PVLANs are used to provide Layer 2 isolation between ports within the same broadcast domain. The level of isolation can be specified with three types of PVLAN ports: – Promiscuous ports that can forward traffic to all other ports – Isolated ports that can only forward traffic to promiscuous ports – Community ports that can forward traffic to other community ports and promiscuous ports -
Question 89 of 152
89. Question
1 pointsA user complains about being locked out of a device after too many unsuccessful AAA login attempts. What could be used by the network administrator to provide a secure authentication access method without locking a user out of a device?Correct
Incorrect
Hint
The login delay command introduces a delay between failed login attempts without locking the account. This provides a user with unlimited attempts at accessing a device without causing the user account to become locked and thus requiring administrator intervention. -
Question 90 of 152
90. Question
1 pointsWhat are two drawbacks in assigning user privilege levels on a Cisco router? (Choose two.)Correct
Incorrect
Hint
Privilege levels may not provide desired flexibility and specificity because higher levels always inherit commands from lower levels, and commands with multiple keywords give the user access to all commands available for each keyword. Privilege levels cannot specify access control to interfaces, ports, or slots. AAA is not required to set privilege levels, but is required in order to create role-based views. The role of root user does not exist in privilege levels. -
Question 91 of 152
91. Question
1 pointsRefer to the exhibit. Which conclusion can be made from the show crypto map command output that is shown on R1?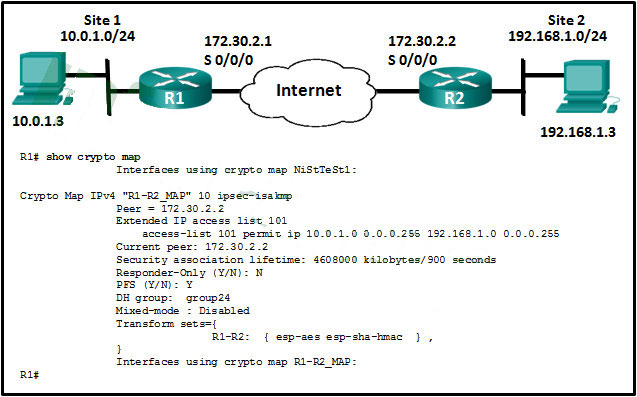 Correct
Correct
Incorrect
Hint
According to the show crypto map command output, all required SAs are in place, but no interface is currently using the crypto map. To complete the tunnel configuration, the crypto map has to be applied to the outbound interface of each router. -
Question 92 of 152
92. Question
1 pointsWhat are two reasons to enable OSPF routing protocol authentication on a network? (Choose two.)Correct
Incorrect
Hint
The reason to configure OSPF authentication is to mitigate against routing protocol attacks like redirection of data traffic to an insecure link, and redirection of data traffic to discard it. OSPF authentication does not provide faster network convergence, more efficient routing, or encryption of data traffic. -
Question 93 of 152
93. Question
1 pointsWhich three functions are provided by the syslog logging service? (Choose three.)Correct
Incorrect
Hint
Syslog operations include gathering information, selecting which type of information to capture, and directing the captured information to a storage location. The logging service stores messages in a logging buffer that is time-limited, and cannot retain the information when a router is rebooted. Syslog does not authenticate or encrypt messages. -
Question 94 of 152
94. Question
1 pointsWhat two ICMPv6 message types must be permitted through IPv6 access control lists to allow resolution of Layer 3 addresses to Layer 2 MAC addresses? (Choose two.)Correct
Incorrect
-
Question 95 of 152
95. Question
1 pointsWhich three services are provided through digital signatures? (Choose three.)Correct
Incorrect
Hint
Digital signatures use a mathematical technique to provide three basic security services:Integrity; Authenticity; Nonrepudiation -
Question 96 of 152
96. Question
1 pointsA technician is to document the current configurations of all network devices in a college, including those in off-site buildings. Which protocol would be best to use to securely access the network devices?Correct
Incorrect
Hint
Telnet sends passwords and other information in clear text, while SSH encrypts its data. FTP and HTTP do not provide remote device access for configuration purposes. -
Question 97 of 152
97. Question
1 pointsAn administrator is trying to develop a BYOD security policy for employees that are bringing a wide range of devices to connect to the company network. Which three objectives must the BYOD security policy address? (Choose three.)Correct
Incorrect
-
Question 98 of 152
98. Question
1 pointsWhat is the function of the pass action on a Cisco IOS Zone-Based Policy Firewall?Correct
Incorrect
Hint
The pass action performed by Cisco IOS ZPF permits forwarding of traffic in a manner similar to the permit statement in an access control list. -
Question 99 of 152
99. Question
1 pointsRefer to the exhibit. Based on the security levels of the interfaces on ASA1, what traffic will be allowed on the interfaces?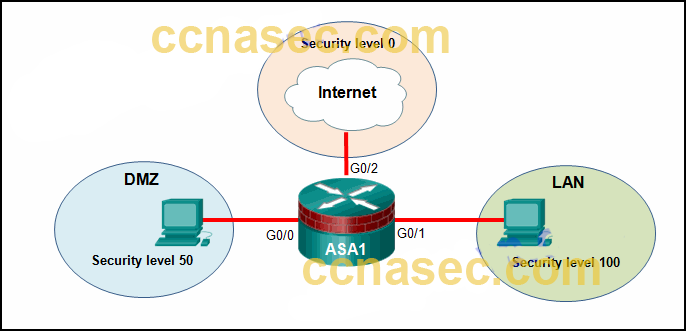 Correct
Correct
Incorrect
Hint
ASA devices have security levels assigned to each interface that are not part of a configured ACL. These security levels allow traffic from more secure interfaces, such as security level 100, to access less secure interfaces, such as level 0. By default, they allow traffic from more secure interfaces (higher security level) to access less secure interfaces (lower security level). Traffic from the less secure interfaces is blocked from accessing more secure interfaces. -
Question 100 of 152
100. Question
1 pointsWhat network testing tool can be used to identify network layer protocols running on a host?Correct
Incorrect
-
Question 101 of 152
101. Question
1 pointsIn the implementation of security on multiple devices, how do ASA ACLs differ from Cisco IOS ACLs?Correct
Incorrect
Hint
The Cisco IOS ACLs are configured with a wildcard mask and the Cisco ASA ACLs are configured with a subnet mask. Both devices use an implicit deny, top down sequential processing, and named or numbered ACLs. -
Question 102 of 152
102. Question
1 pointsWhich statement describes an important characteristic of a site-to-site VPN?Correct
Incorrect
Hint
A site-to-site VPN is created between the network devices of two separate networks. The VPN is static and stays established. The internal hosts of the two networks have no knowledge of the VPN. -
Question 103 of 152
103. Question
1 pointsWhich two options are security best practices that help mitigate BYOD risks? (Choose two.)Correct
Incorrect
Hint
Many companies now support employees and visitors attaching and using wireless devices that connect to and use the corporate wireless network. This practice is known as a bring-your-own-device policy or BYOD. Commonly, BYOD security practices are included in the security policy. Some best practices that mitigate BYOD risks include the following: Use unique passwords for each device and account. Turn off Wi-Fi and Bluetooth connectivity when not being used. Only connect to trusted networks. Keep the device OS and other software updated. Backup any data stored on the device. Subscribe to a device locator service with a remote wipe feature. Provide antivirus software for approved BYODs. Use Mobile Device Management (MDM) software that allows IT teams to track the device and implement security settings and software controls. -
Question 104 of 152
104. Question
1 pointsRefer to the exhibit. A network administrator configures AAA authentication on R1. Which statement describes the effect of the keyword single-connection in the configuration?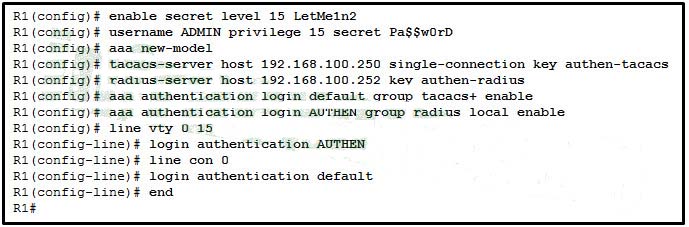 Correct
Correct
Incorrect
Hint
The single-connection keyword enhances TCP performance with TACACS+ by maintaining a single TCP connection for the life of the session. Without the single-connection keyword, a TCP connection is opened and closed per session. -
Question 105 of 152
105. Question
1 pointsA recently created ACL is not working as expected. The admin determined that the ACL had been applied inbound on the interface and that was the incorrect direction. How should the admin fix this issue?Correct
Incorrect
-
Question 106 of 152
106. Question
1 pointsWhat characteristic of the Snort term-based subscriptions is true for both the community and the subscriber rule sets?Correct
Incorrect
Hint
There are two types of term-based subscriptions: – Community Rule Set – Available for free, this subscription offers limited coverage against threats. The community rule set focuses on reactive response to security threats versus proactive research work. There is also a 30-day delayed access to updated signatures meaning that newest rule will be a minimum of 30 days old. In addition, there is no Cisco customer support available. – Subscriber Rule Set – Available for a fee, this service provides the best protection against threats. It includes coverage of advance exploits by using the research work of the Cisco Talos security experts. The Subscriber Rule Set also provides the fastest access to updated signatures in response to a security incident or the proactive discovery of a new threat. This subscription is fully supported by Cisco. -
Question 107 of 152
107. Question
1 pointsA security analyst is configuring Snort IPS. The analyst has just downloaded and installed the Snort OVA file. What is the next step?Correct
Incorrect
Hint
To deploy Snort IPS on supported devices, perform the following steps: – Step 1. Download the Snort OVA file. – Step 2. Install the OVA file. – Step 3. Configure Virtual Port Group interfaces. – Step 4. Activate the virtual services. – Step 5. Configure Snort specifics. – Step 6. Enable IPS globally or on desired interfaces. – Step 7. Verify Snort IPS. -
Question 108 of 152
108. Question
1 pointsThe security policy in a company specifies that employee workstations can initiate HTTP and HTTPS connections to outside websites and the return traffic is allowed. However, connections initiated from outside hosts are not allowed. Which parameter can be used in extended ACLs to meet this requirement?Correct
Incorrect
-
Question 109 of 152
109. Question
1 pointsA researcher is comparing the differences between a stateless firewall and a proxy firewall. Which two additional layers of the OSI model are inspected by a proxy firewall? (Choose two.)Correct
Incorrect
Hint
Packet filtering firewalls are usually part of a router firewall, which permits or denies traffic based on Layer 3 and Layer 4 information. An application gateway firewall (proxy firewall), as shown in the figure, filters information at Layers 3, 4, 5, and 7 of the OSI reference model. -
Question 110 of 152
110. Question
1 pointsRefer to the exhibit. A network administrator is configuring a VPN between routers R1 and R2. Which commands would correctly configure a pre-shared key for the two routers? Correct
Correct
Incorrect
-
Question 111 of 152
111. Question
1 pointsRefer to the exhibit. Which statement is true about the effect of this Cisco IOS zone-based policy firewall configuration?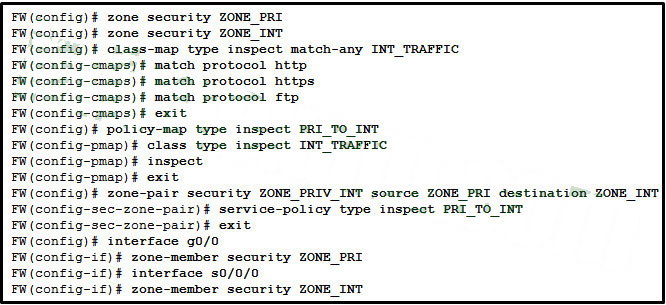 Correct
Correct
Incorrect
-
Question 112 of 152
112. Question
1 pointsWhich privilege level has the most access to the Cisco IOS?Correct
Incorrect
-
Question 113 of 152
113. Question
1 pointsRefer to the exhibit. A network administrator has configured NAT on an ASA device. What type of NAT is used?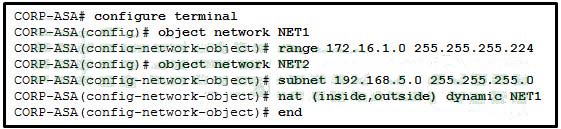 Correct
Correct
Incorrect
Hint
NAT can be deployed on an ASA using one of these methods: inside NAT – when a host from a higher-security interface has traffic destined for a lower-security interface and the ASA translates the internal host address to a global address outside NAT – when traffic from a lower-security interface destined for a host on the higher-security interface is translated bidirectional NAT – when both inside NAT and outside NAT are used together Because the nat command is applied so that the inside interface is mapped to the outside interface, the NAT type is inside. Also, the dynamic keyword in the nat command indicates that it is a dynamic mapping. -
Question 114 of 152
114. Question
1 pointsA network analyst is configuring a site-to-site IPsec VPN. The analyst has configured both the ISAKMP and IPsec policies. What is the next step?Correct
Incorrect
-
Question 115 of 152
115. Question
1 pointsMatch the type of ASA ACLs to the description. (Not all options are used.)Correct
Incorrect
-
Question 116 of 152
116. Question
1 pointsMatch the network monitoring technology with the description.Correct
Incorrect
-
Question 117 of 152
117. Question
1 pointsMatch each IPS signature trigger category with the description.Correct
Incorrect
-
Question 118 of 152
118. Question
1 pointsPlace the steps for configuring zone-based policy (ZPF) firewalls in order from first to last. (Not all options are used.)Correct
Incorrect
-
Question 119 of 152
119. Question
1 pointsRefer to the exhibit. The ip verify source command is applied on untrusted interfaces. Which type of attack is mitigated by using this configuration?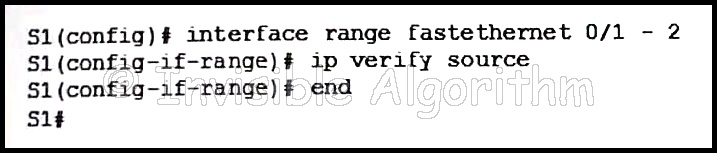 Correct
Correct
Incorrect
Hint
To protect against MAC and IP address spoofing, apply the IP Source Guard security feature, using the ip verify source command, on untrusted ports. -
Question 120 of 152
120. Question
1 pointsWhen an inbound Internet-traffic ACL is being implemented, what should be included to prevent the spoofing of internal networks?Correct
Incorrect
Hint
Common ACEs to assist with antispoofing include blocking packets that have a source address in the 127.0.0.0/8 range, any private address, or any multicast addresses. Furthermore, the administrator should not allow any outbound packets with a source address other than a valid address that is used in the internal networks of the organization. -
Question 121 of 152
121. Question
1 pointsMatch the security term to the appropriate description. (Not all options are used.)Correct
Incorrect
-
Question 122 of 152
122. Question
1 points122. Which two types of attacks are examples of reconnaissance attacks? (Choose two.)Correct
Incorrect
Hint
Reconnaissance attacks attempt to gather information about the targets. Ping sweeps will indicate which hosts are up and responding to pings, whereas port scans will indicate on which TCP and UDP ports the target is listening for incoming connections. Man-in-the-middle and brute force attacks are both examples of access attacks, and a SYN flood is an example of a denial of service (DoS) attack. -
Question 123 of 152
123. Question
1 pointsWhich Cisco solution helps prevent ARP spoofing and ARP poisoning attacks?Correct
Incorrect
-
Question 124 of 152
124. Question
1 pointsWhen the Cisco NAC appliance evaluates an incoming connection from a remote device against the defined network policies, what feature is being used?Correct
Incorrect
-
Question 125 of 152
125. Question
1 pointsWhich two steps are required before SSH can be enabled on a Cisco router? (Choose two.)Correct
Incorrect
Hint
There are four steps to configure SSH on a Cisco router. First, set the host name and domain name. Second, generate a set of RSA keys to be used for encrypting and decrypting the traffic. Third, create the user IDs and passwords of the users who will be connecting. Lastly, enable SSH on the vty lines on the router. SSH does not need to be set up on any physical interfaces, nor does an external authentication server need to be used. While it is a good idea to configure a banner to display legal information for connecting users, it is not required to enable SSH. -
Question 126 of 152
126. Question
1 pointsThe network administrator for an e-commerce website requires a service that prevents customers from claiming that legitimate orders are fake. What service provides this type of guarantee?Correct
Incorrect
-
Question 127 of 152
127. Question
1 pointsMatch the security technology with the description.Correct
Incorrect
-
Question 128 of 152
128. Question
1 pointsWhat functionality is provided by Cisco SPAN in a switched network?Correct
Incorrect
Hint
SPAN is a Cisco technology used by network administrators to monitor suspicious traffic or to capture traffic to be analyzed. -
Question 129 of 152
129. Question
1 pointsWhich three statements are generally considered to be best practices in the placement of ACLs? (Choose three.)Correct
Incorrect
Hint
Extended ACLs should be placed as close as possible to the source IP address, so that traffic that needs to be filtered does not cross the network and use network resources. Because standard ACLs do not specify a destination address, they should be placed as close to the destination as possible. Placing a standard ACL close to the source may have the effect of filtering all traffic, and limiting services to other hosts. Filtering unwanted traffic before it enters low-bandwidth links preserves bandwidth and supports network functionality. Decisions on placing ACLs inbound or outbound are dependent on the requirements to be met. -
Question 130 of 152
130. Question
1 pointsWhat function is performed by the class maps configuration object in the Cisco modular policy framework?Correct
Incorrect
Hint
There are three configuration objects in the MPF; class maps, policy maps, and service policy. The class maps configuration object uses match criteria to identify interesting traffic. -
Question 131 of 152
131. Question
1 pointsIn an attempt to prevent network attacks, cyber analysts share unique identifiable attributes of known attacks with colleagues. What three types of attributes or indicators of compromise are helpful to share? (Choose three.)Correct
Incorrect
Hint
Many network attacks can be prevented by sharing information about indicators of compromise (IOC). Each attack has unique identifiable attributes. Indicators of compromise are the evidence that an attack has occurred. IOCs can be identifying features of malware files, IP addresses of servers that are used in the attack, filenames, and characteristic changes made to end system software. -
Question 132 of 152
132. Question
1 pointsWhat two assurances does digital signing provide about code that is downloaded from the Internet? (Choose two.)Correct
Incorrect
Hint
Digitally signing code provides several assurances about the code: The code is authentic and is actually sourced by the publisher. The code has not been modified since it left the software publisher. The publisher undeniably published the code. This provides nonrepudiation of the act of publishing. -
Question 133 of 152
133. Question
1 pointsRefer to the exhibit. What algorithm is being used to provide public key exchange?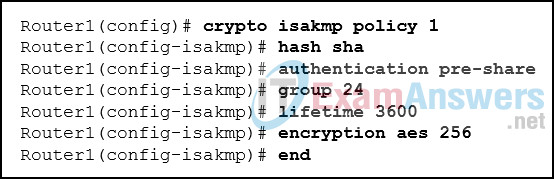 Correct
Correct
Incorrect
Hint
The IPsec framework uses various protocols and algorithms to provide data confidentiality, data integrity, authentication, and secure key exchange. DH (Diffie-Hellman) is an algorithm used for key exchange. DH is a public key exchange method and allows two IPsec peers to establish a shared secret key over an insecure channel. -
Question 134 of 152
134. Question
1 pointsWhich two statements describe the use of asymmetric algorithms? (Choose two.)Correct
Incorrect
Hint
Asymmetric algorithms use two keys: a public key and a private key. Both keys are capable of the encryption process, but the complementary matched key is required for decryption. If a public key encrypts the data, the matching private key decrypts the data. The opposite is also true. If a private key encrypts the data, the corresponding public key decrypts the data. -
Question 135 of 152
135. Question
1 pointsWhich statement is a feature of HMAC?Correct
Incorrect
Hint
A keyed-hash message authentication code (HMAC or KHMAC) is a type of message authentication code (MAC). HMACs use an additional secret key as input to the hash function, adding authentication to data integrity assurance. -
Question 136 of 152
136. Question
1 pointsWhat is the purpose of the webtype ACLs in an ASA?Correct
Incorrect
Hint
The webtype ACLs are used in a configuration that supports filtering for clientless SSL VPN users. -
Question 137 of 152
137. Question
1 pointsWhich two statements describe the effect of the access control list wildcard mask 0.0.0.15? (Choose two.)Correct
Incorrect
Hint
A wildcard mask uses 0s to indicate that bits must match. 0s in the first three octets represent 24 bits and four more zeros in the last octet, represent a total of 28 bits that must match. The four 1s represented by the decimal value of 15 represents the four bits to ignore. -
Question 138 of 152
138. Question
1 pointsWhich type of firewall is the most common and allows or blocks traffic based on Layer 3, Layer 4, and Layer 5 information?Correct
Incorrect
-
Question 139 of 152
139. Question
1 pointsWhich protocol or measure should be used to mitigate the vulnerability of using FTP to transfer documents between a teleworker and the company file server?Correct
Incorrect
Hint
File transfer using FTP is transmitted in plain text. The username and password would be easily captured if the data transmission is intercepted. Secure Copy Protocol (SCP) conducts the authentication and file transfer under SSH, thus the communication is encrypted. Like FTP, TFTP transfers files unencrypted. ACLs provide network traffic filtering but not encryption. Using an out-of-band communication channel (OOB) either requires physical access to the file server or, if done through the internet, does not necessarily encrypt the communication. -
Question 140 of 152
140. Question
1 pointsRefer to the exhibit. The IPv6 access list LIMITED_ACCESS is applied on the S0/0/0 interface of R1 in the inbound direction. Which IPv6 packets from the ISP will be dropped by the ACL on R1?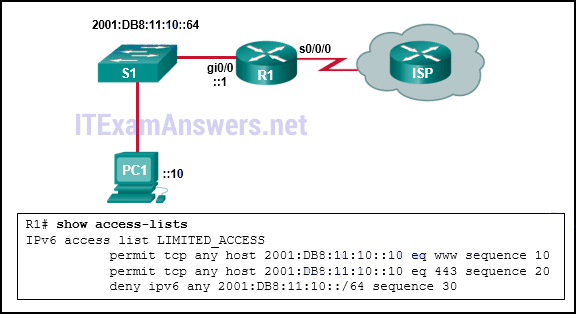 Correct
Correct
Incorrect
Hint
The access list LIMITED_ACCESS will block ICMPv6 packets from the ISP. Both port 80, HTTP traffic, and port 443, HTTPS traffic, are explicitly permitted by the ACL. The neighbor advertisements from the ISP router are implicitly permitted by the implicit permit icmp any any nd-na statement at the end of all IPv6 ACLs. -
Question 141 of 152
141. Question
1 pointsWhat tool is available through the Cisco IOS CLI to initiate security audits and to make recommended configuration changes with or without administrator input?Correct
Incorrect
-
Question 142 of 152
142. Question
1 pointsRefer to the exhibit. Which pair of crypto isakmp key commands would correctly configure PSK on the two routers?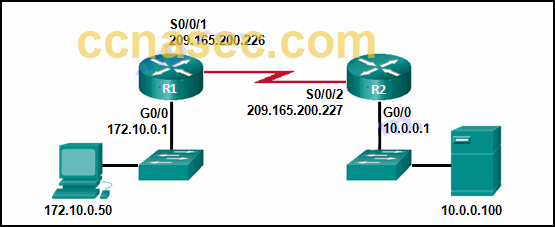 Correct
Correct
Incorrect
Hint
The correct syntax of the crypto isakmp key command is as follows: crypto isakmp key keystring address peer-address or crypto isakmp keykeystring hostname peer-hostnameSo, the correct answer would be the following: R1(config)# crypto isakmp key cisco123 address 209.165.200.227 R2(config)# crypto isakmp key cisco123 address 209.165.200.226 -
Question 143 of 152
143. Question
1 pointsWhich two technologies provide enterprise-managed VPN solutions? (Choose two.)Correct
Incorrect
-
Question 144 of 152
144. Question
1 pointsWhat are the three components of an STP bridge ID? (Choose three.)Correct
Incorrect
-
Question 145 of 152
145. Question
1 pointsWhat are two differences between stateful and packet filtering firewalls? (Choose two.)Correct
Incorrect
Hint
There are many differences between a stateless and stateful firewall. Stateless firewalls (packet filtering firewalls): – are susceptible to IP spoofing – do not reliably filter fragmented packets – use complex ACLs, which can be difficult to implement and maintain – cannot dynamically filter certain services – examine each packet individually rather than in the context of the state of a connection Stateful firewalls: – are often used as a primary means of defense by filtering unwanted, unnecessary, or undesirable traffic – strengthen packet filtering by providing more stringent control over security – improve performance over packet filters or proxy servers – defend against spoofing and DoS attacks by determining whether packets belong to an existing connection or are from an unauthorized source – provide more log information than a packet filtering firewall -
Question 146 of 152
146. Question
1 pointsWhich portion of the Snort IPS rule header identifies the destination port?alert tcp $HOME_NET any -> $EXTERNAL_NET $HTTP_PORTS
Correct
Incorrect
-
Question 147 of 152
147. Question
1 pointsMatch each SNMP operation to the corresponding description. (Not all options are used.)Correct
Incorrect
-
Question 148 of 152
148. Question
1 pointsWhat port state is used by 802.1X if a workstation fails authorization?Correct
Incorrect
-
Question 149 of 152
149. Question
1 pointsMatch the ASA special hardware modules to the description.Correct
Incorrect
Hint
The advanced threat control and containment services of an ASA firewall are provided by integrating special hardware modules with the ASA architecture. These special modules include: – Advanced Inspection and Prevention (AIP) module – supports advanced IPS capability. – Content Security and Control (CSC) module – supports antimalware capabilities. – Cisco Advanced Inspection and Prevention Security Services Module (AIP-SSM) and Cisco Advanced Inspection and Prevention Security Services Card (AIP-SSC) – support protection against tens of thousands of known exploits. -
Question 150 of 152
150. Question
1 pointsRefer to the exhibit. Which two ACLs, if applied to the G0/1 interface of R2, would permit only the two LAN networks attached to R1 to access the network that connects to R2 G0/1 interface? (Choose two.)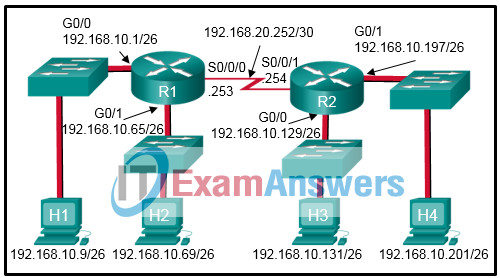 Correct
Correct
Incorrect
Hint
The permit 192.168.10.0 0.0.0.127 command ignores bit positions 1 through 7, which means that addresses 192.168.10.0 through 192.168.10.127 are allowed through. The two ACEs of permit 192.168.10.0 0.0.0.63 and permit 192.168.10.64 0.0.0.63 allow the same address range through the router. -
Question 151 of 152
151. Question
1 pointsWhich two characteristics apply to role-based CLI access superviews? (Choose two.)Correct
Incorrect
Hint
By using a superview an administrator can assign users or groups of users to CLI views which contain a specific set of commands those users can access. Commands cannot be added directly to a superview but rather must be added to a CLI view and the CLI view added to the superview. -
Question 152 of 152
152. Question
1 pointsMatch the IPS alarm type to the description.Correct
Incorrect

The correct answers here is not the same as in the pure answer page. Like question 40 and 41
Fixed it, thanks!
How does a firewall handle traffic when it is originating from the private network and traveling to the DMZ network?
The answer says The traffic is selectively permitted and inspected.
But isn’t it: The traffic is usually permitted with little or no restrictions.
Hello, the number of question in quiz is different to solutions. Can you fix it?