Networking Essentials 3.0: Course Final Exam
1. To which component of the CIA triad security information principle does tokenization apply?
- confidentiality
- availability
- authorization
- integrity
2. Which troubleshooting method involves swapping a device suspected of having issues with a known good device to see if the problem is solved?
- educated guess
- comparison
- substitution
- divide-and-conquer
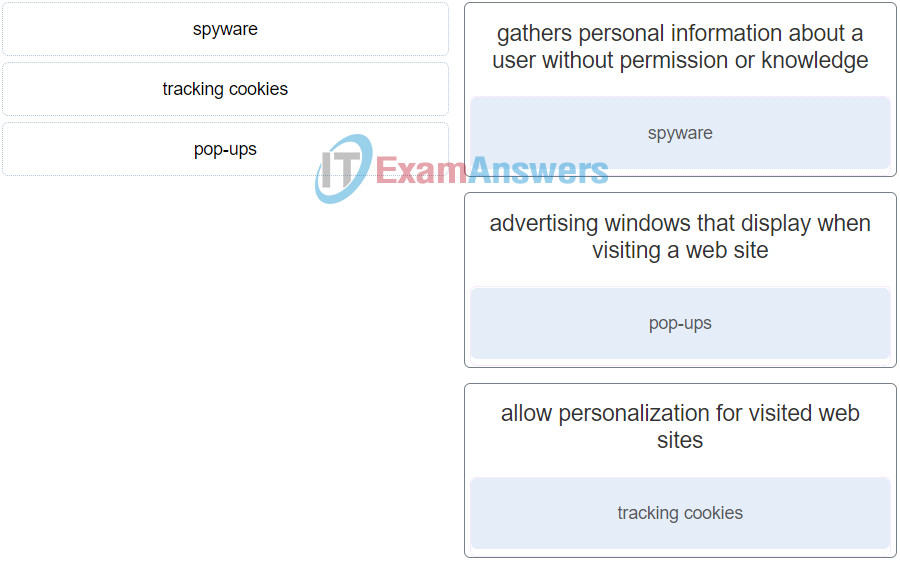
3. Match the examples of cyber threat to the description.
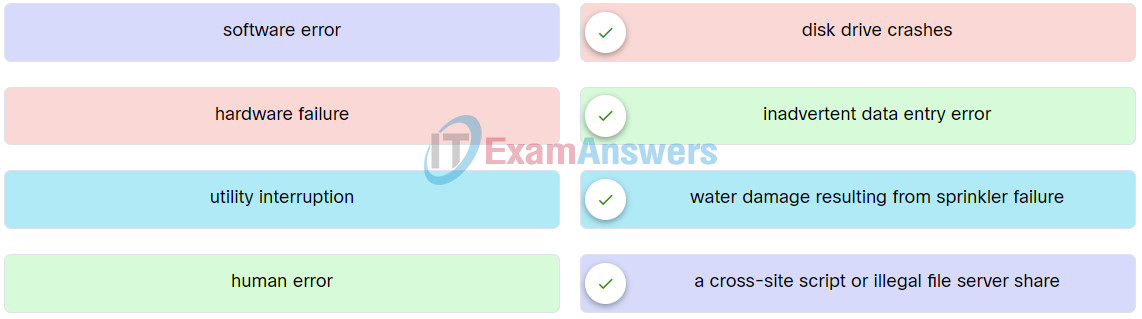
Network Support and Security Final Exam Q15
4. Which statement describes an advanced persistent threat (APT)?
- an attack that modifies the operating system through malware and creates a backdoor on the infected system.
- an attack that takes advantage of algorithms in a piece of legitimate software to generate unintended behaviors.
- an attack by threat actors performing unauthorized network probing and port scanning on the targeted network.
- a continuous attack that uses elaborated espionage tactics involving multiple threat actors and sophisticated malware to gain access to the targeted network.
5. Match the authentication method to description.
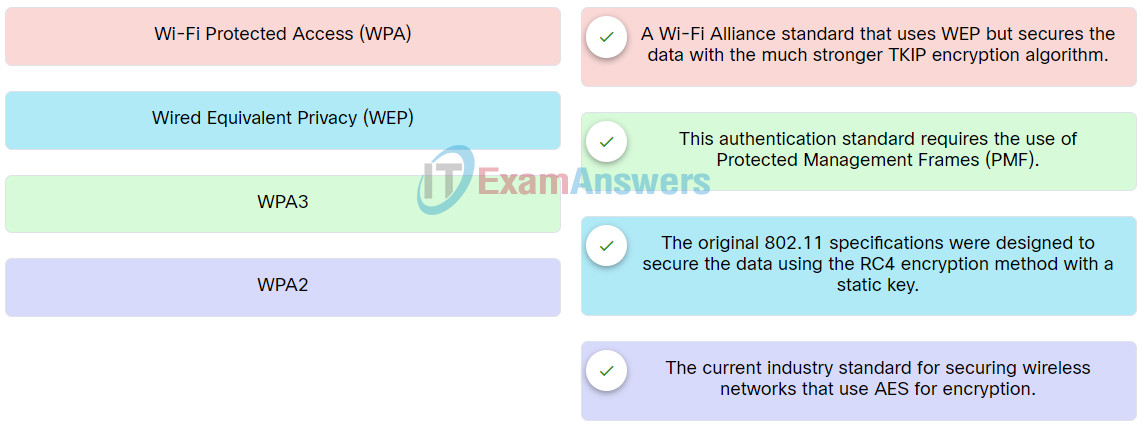
Network Support and Security Course Final Exam Q24
6. Which Apple security feature ensures that only authentic, digitally-signed software that an Apple-notarized software developer has created is permitted to be installed?
- XProtect
- Security-focused hardware
- Gatekeeper
- MRT
7. Which type of cyber threat would cause electrical power outages?
- human error
- sabotage
- utility interruption
- hardware failure
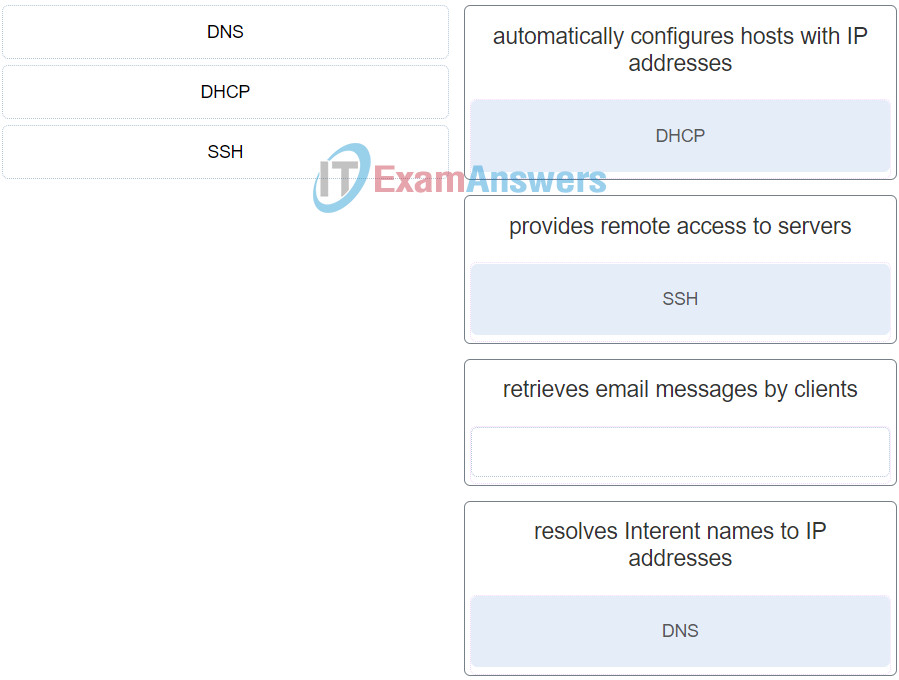
8. Employees in an organization report that they cannot access the customer database on the main server. Further investigation reveals that the database file is now encrypted. Shortly afterward, the organization receives a threatening email demanding payment for the decryption of the database file. What type of attack has the organization experienced?
- trojan horse
- ransomware
- DoS attack
- man-in-the-middle attack
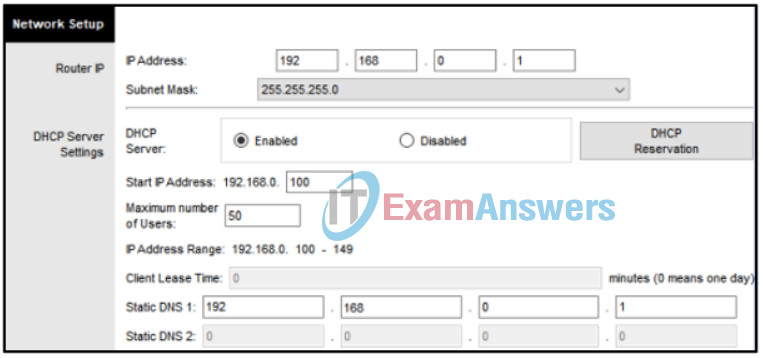
9. Refer to the exhibit. How many bits are represented by each group of four hexadecimal values contained between the colons in an IPv6 address?
- 16
- 64
- 4
- 32
- 8
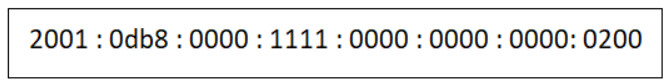
10. Which network design has the fewest broadcast domains?
11. A company uses DHCP servers to dynamically assign IPv4 addresses to employee workstations. The address lease duration is set as 5 days. An employee returns to the office after an absence of one week. When the employee boots the workstation, it sends a message to obtain an IP address. Which Layer 2 and Layer 3 destination addresses will the message contain?
- FF-FF-FF-FF-FF-FF and 255.255.255.255
- MAC address of the DHCP server and 255.255.255.255
- FF-FF-FF-FF-FF-FF and IPv4 address of the DHCP server
- both MAC and IPv4 addresses of the DHCP server
12. What are two characteristics of multicast transmission? (Choose two.)
- The source address of a multicast transmission is in the range of 224.0.0.0 to 224.0.0.255.
- Multicast transmission can be used by routers to exchange routing information.
- A single packet can be sent to a group of hosts.
- Multicast messages map lower layer addresses to upper layer addresses.
- Computers use multicast transmission to request IPv4 addresses.
13. All employees in an organization receive an email stating that their account password will expire immediately and that they should reset their password within five minutes. Which of the following statements best describes this email?
- It is a DDoS attack.
- It is a hoax.
- It is a piggyback attack.
- It is an impersonation attack.
14. Which is an example of a behavioral characteristic?
- voice
- ear features
- face
- DNA
15. What is the limitation of using a stateful firewall in a network?
- Less information is provided in the logs compared to a packet-filtering firewall.
- No defense against spoofing and DoS attacks.
- Weak packet filtering.
- Difficult to defend against dynamic port negotiation.
16. Which Windows utility would a technician use to discover which user was logged in to the system when a critical problem occurred?
- Event Viewer
- Device Manager
- Task Manager
- Users and Groups MMC
17. Which statement describes the principle of availability in the CIA information security triad?
- Cryptographic encryption algorithms such as AES may be required to encrypt and decrypt data.
- Data must be protected from unauthorized alteration.
- Only authorized individuals, entities, or processes can access sensitive information.
- Redundant services, gateways, and links must be implemented.
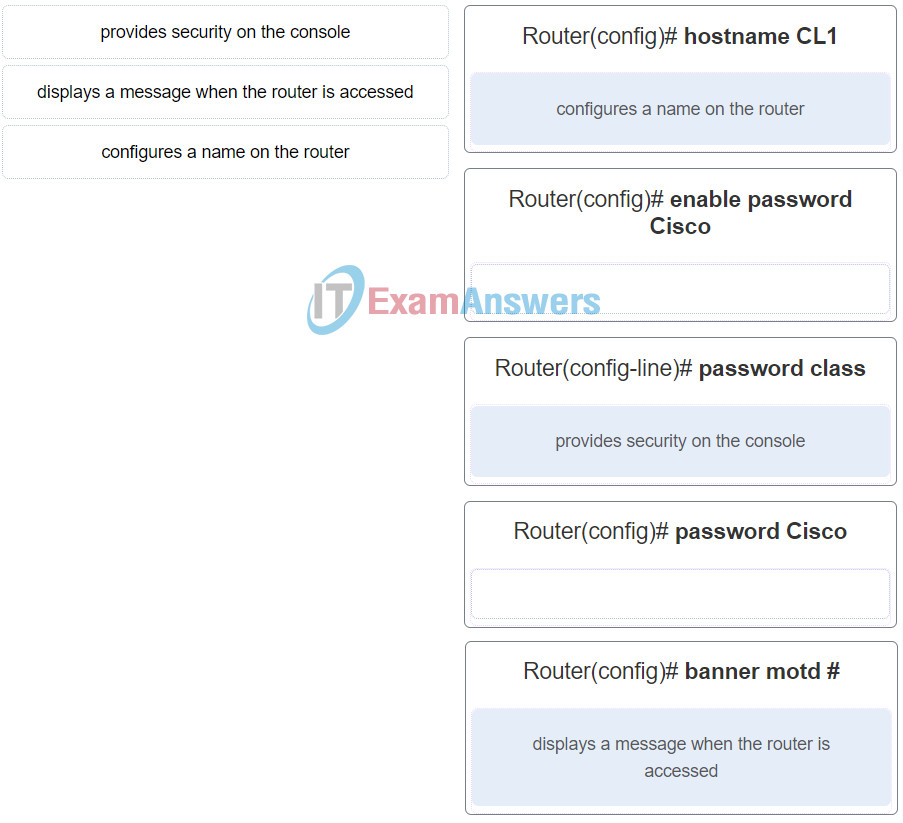
18. Which scenario is suitable for deploying twisted-pair cables?
- to connect network devices in backbone networks
- to connect a TV set to the wall plug at home
- to connect data centers with high bandwidth requirements over long distances
- to connect PC workstations in an office
19. Which three types of nodes should be assigned static IP addresses on a network? (Choose three.)
- desktop PCs
- printers
- mobile laptops
- gateways
- tablets
- servers
20. Match the host-based security solution to the description.
21. What layer is responsible for routing messages through an internetwork in the TCP/IP model?
- network access
- session
- transport
- internet
22. What data encoding technology is used in copper cables?
- electrical pulses
- modulation of specific frequencies of electromagnetic waves
- modulation of light rays
- pulses of light
23. What information is added to the switch table from incoming frames?
- destination IP address and incoming port number
- source MAC address and incoming port number
- source IP address and incoming port number
- destination MAC address and incoming port number
24. At which layer of the OSI model would a logical address be added during encapsulation?
- network layer
- physical layer
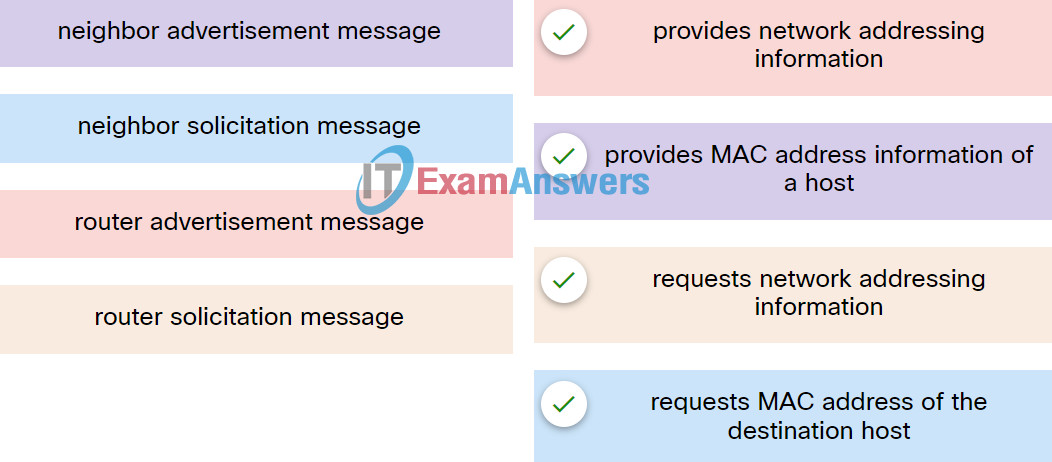
- transport layer
- data link layer
25. Which type of network model describes the functions that must be completed at a particular layer, but does not specify exactly how each protocol should work?
- reference model
- hierarchical design model
- protocol model
- TCP/IP model
26. What type of route is indicated by the code C in an IPv4 routing table on a Cisco router?
- directly connected route
- default route
- dynamic route learned from another router
- static route
27. A small accounting office is setting up a wireless network to connect end devices and to provide internet access. In which two scenarios does a wireless router perform Network Address Translation (NAT)? (Choose two.)
- when a host is sending packets to the ISP in order to request a speed increase for Internet services
- when a host is sending packets to a local server in order to update the network media settings and music playlists
- when a host is sending packets to a remote site owned by the manufacturer of the wireless router in order to request a digital copy of the device manual
- when a host is sending a print job to a network printer on the LAN
- when a host is sending HTTP packets to the wireless router in order to update the network addressing of the LAN
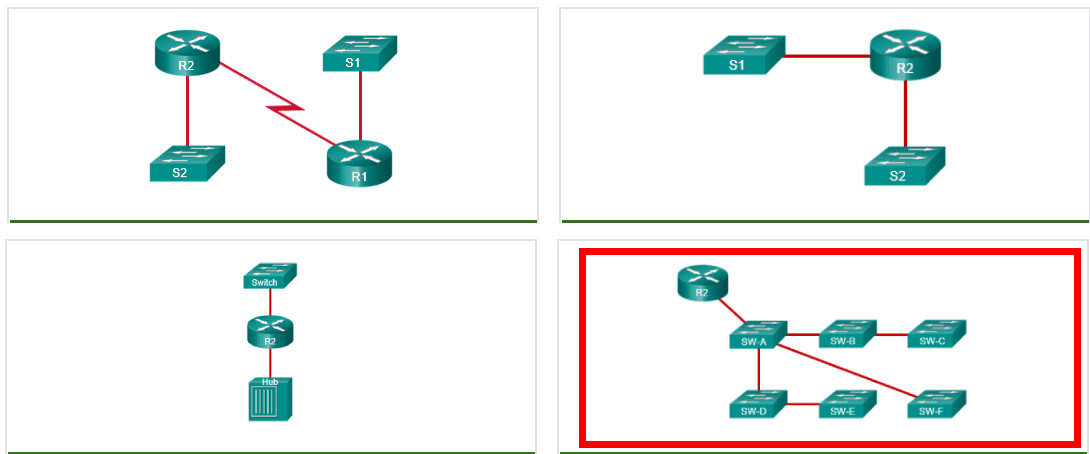
28. Refer to the exhibit. A switch with a default configuration connects four hosts. The ARP table for host A is shown. What happens when host A wants to send an IP packet to host D?
- Host A sends out the packet to the switch. The switch sends the packet only to the host D, which in turn responds.
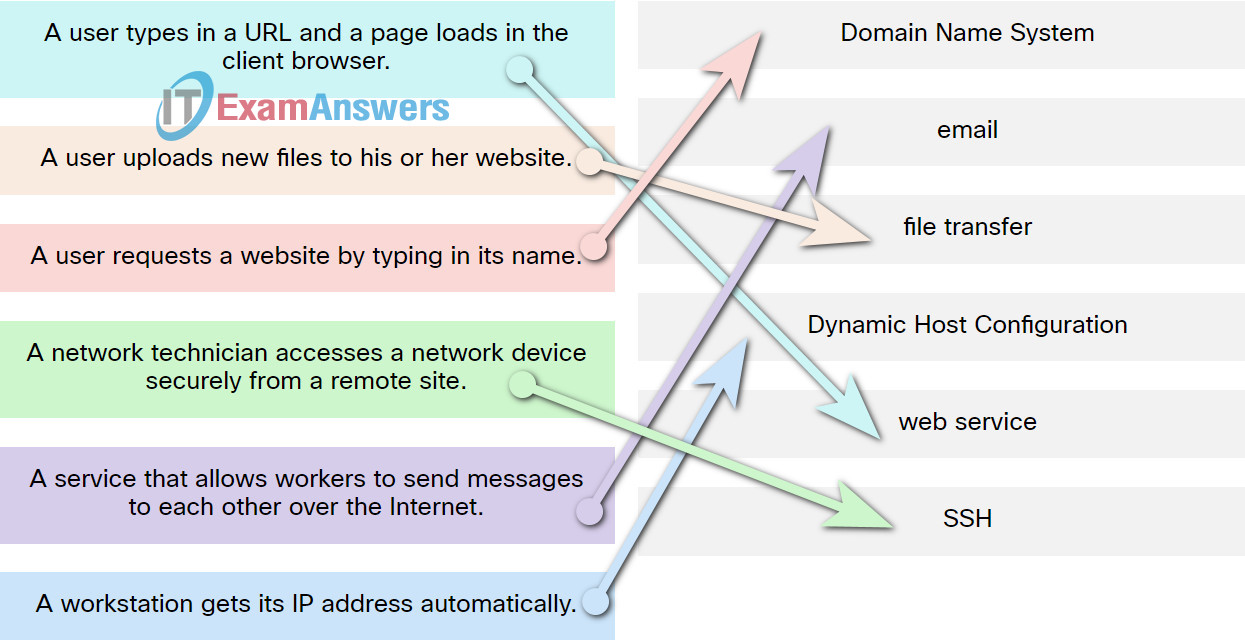
- Host D sends an ARP request to host A.
- Host A sends an ARP request to the MAC address of host D.
- Host A sends out a broadcast of FF:FF:FF:FF:FF:FF. Every other host connected to the switch receives the broadcast and host D responds with its MAC address.
29. What will a Cisco LAN switch do if it receives an incoming frame and the destination MAC address is not listed in the MAC address table?
- Send the frame to the default gateway address.
- Drop the frame.
- Forward the frame out all ports except the port where the frame is received.
- Use ARP to resolve the port that is related to the frame.
30. Which number grouping is a valid IPv6 address?
- 1234:1230::1238::1299:1000::
- 1b10::1100::2001::2900::ab11::1102::0000::2900
- 2001:0db8:3c55:0015:1010:0000:abcd:ff13
- 12aa::1298:1200::129b
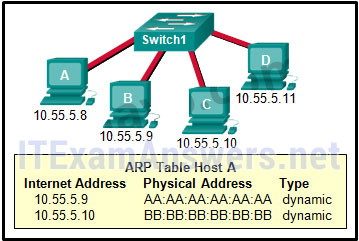
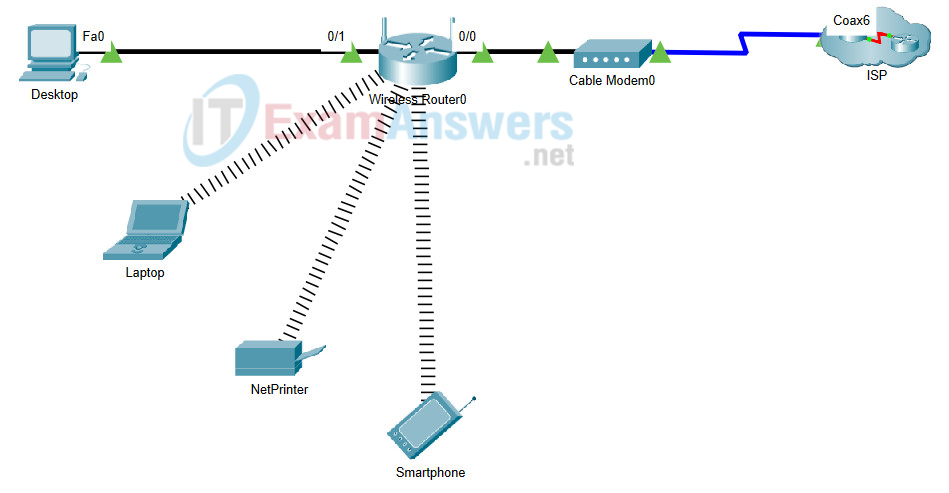
31. Refer to the exhibit. A newly purchased client laptop has just connected to the local area network. The local area network is using a wireless router that is providing dynamic addressing as shown. Which IP address does the laptop use as a destination address when requesting a dynamically assigned address?
- 192.168.0.100
- 255.255.255.255
- 192.168.0.255
- 255.255.255.0
- 192.168.0.1
32. Two pings were issued from a host on a local network. The first ping was issued to the IP address of the default gateway of the host and it failed. The second ping was issued to the IP address of a host outside the local network and it was successful. What is a possible cause for the failed ping?
- The default gateway is not operational.
- The TCP/IP stack on the default gateway is not working properly.
- Security rules are applied to the default gateway device, preventing it from processing ping requests.
- The default gateway device is configured with the wrong IP address.
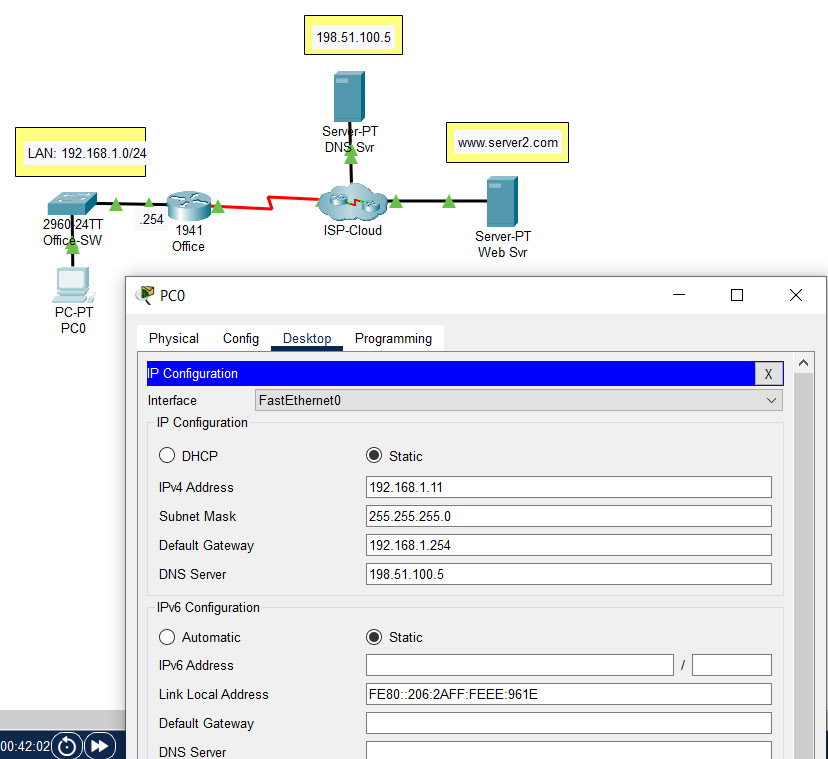
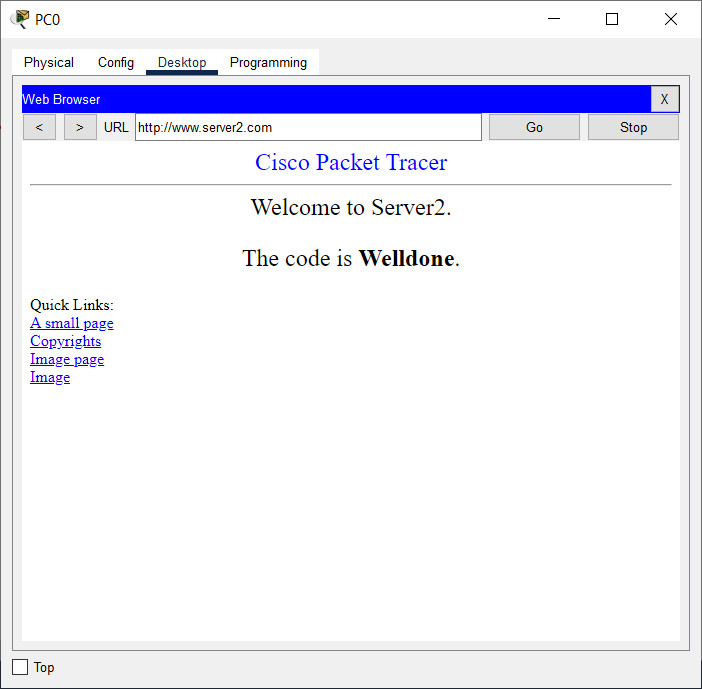
33. Open the PT activity. Perform the tasks in the activity instructions and then answer the question. What is the code displayed on the web page?
- Success
- Correct
- Welldone
- Configured Right
34. What process involves placing one message format inside of another message format?
- flow control
- encapsulation
- encoding
- segmentation
35. A cable installation company is trying to convince a customer to use fiber-optic cabling instead of copper cables for a particular job. What is one advantage of using fiber-optic cabling compared to copper cabling?
- The installation skills required for fiber-optic cabling are lower.
- Fiber-optic cabling can transmit signals without attenuation.
- Fiber-optic cabling is completely immune to EMI and RFI.
- The cost of fiber-optic connectors is lower.
36. Open the PT activity. Perform the tasks in the activity instructions and then answer the question. Which IP address should be used as the default gateway address on PC0?
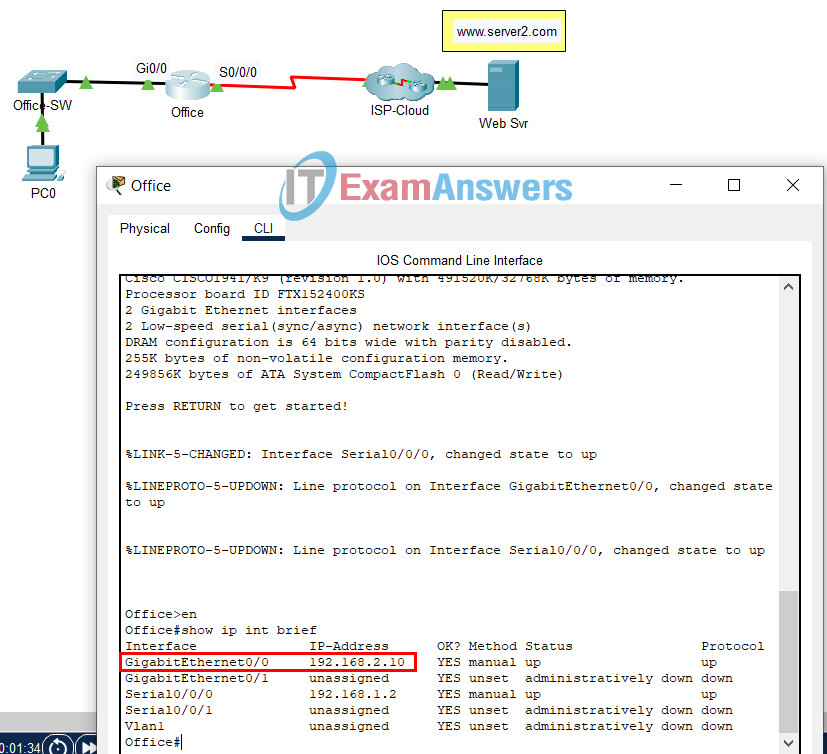
Networking Basics Course Final Exam
- 192.168.2.10
- 192.168.1.1
- 192.168.2.5
- 192.168.1.2
37. Refer to the exhibit. The IP address of which device interface should be used as the default gateway setting of host H1?
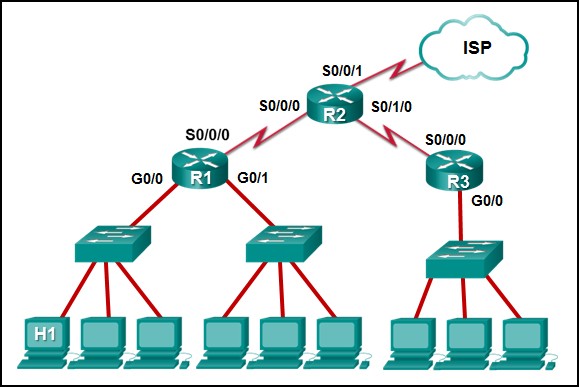
- R1: G0/0
- R2: S0/0/1
- R1: S0/0/0
- R2: S0/0/0
38. A network administrator has a multi-floor LAN to monitor and maintain. Through careful monitoring, the administrator has noticed a large amount of broadcast traffic slowing the network. Which device would you use to best solve this problem?
- switch
- router
- host
- server
39. Which two criteria are used to help select a network medium for a network? (Choose two.)
- the environment where the selected medium is to be installed
- the cost of the end devices that are used in the network
- the number of intermediate devices that are installed in the network
- the distance the selected medium can successfully carry a signal
- the types of data that need to be prioritized
40. What benefit does DHCP provide to a network?
- DHCP allows users to refer to locations by a name rather than an IP address.
- Hosts always have the same IP address and are therefore always reachable.
- Hosts can connect to the network and get an IP address without manual configuration.
- Duplicate addresses cannot occur on a network that issues dynamic addresses using DHCP and has static assignments.
41. Which wireless technology allows a customer to connect to a payment terminal in the store with a smartphone?
- Wi-Fi
- GPS
- NFC
- Bluetooth
42. What are two methods typically used on a mobile device to provide internet connectivity? (Choose two.)
- Bluetooth
- cellular
- NFC
- GPS
- Wi-Fi
43. What information does an Ethernet switch examine and use to build its address table?
- destination IP address
- destination MAC address
- source IP address
- source MAC address
44. Which two OSI model layers have the same functionality as two layers of the TCP/IP model? (Choose two.)
- transport
- network
- data link
- session
- physical
45. Refer to the exhibit. A technician is attempting to configure the IPv6 address 2001:db8::1111::0200 on a device. Why does the device return an error message that indicates the address is not valid?
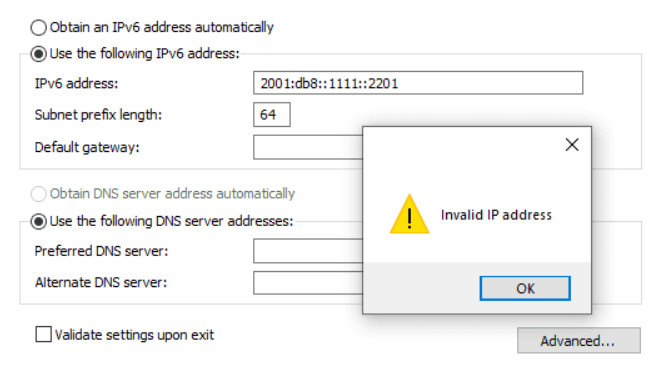
Networking Basics Course Final Exam 30
- The IPv6 address notation is incorrect.
- IPv6 is not implemented on this network.
- The device already is configured with an IPv4 address.
- The address is already in use on the network.
46. An employee is having connectivity issues. Why might a network technician try to ping the default gateway from the employee laptop?
- to verify connectivity with the device that provides access to remote networks
- to verify that an IP address was provided by the DHCP server
- to determine if the laptop address is included in the DNS server
- to verify that the SVI interface on the switch is configured correctly
47. Refer to the exhibit. PC1 issues an ARP request because it needs to send a packet to PC3. In this scenario, what will happen next?
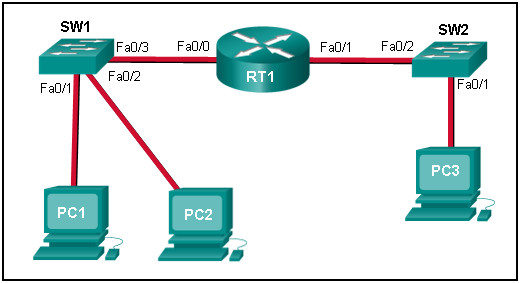
- SW1 will send an ARP reply with its Fa0/1 MAC address.
- RT1 will send an ARP reply with its own Fa0/0 MAC address.
- RT1 will send an ARP reply with the PC3 MAC address.
- RT1 will forward the ARP request to PC3.
- RT1 will send an ARP reply with its own Fa0/1 MAC address.
48. Which three addresses are valid public addresses? (Choose three.)
- 198.133.219.17
- 128.107.12.117
- 172.31.1.25
- 10.15.250.5
- 64.104.78.227
- 192.168.1.245
49. A technician is troubleshooting a network connectivity problem. Pings to the local wireless router are successful but pings to a server on the Internet are unsuccessful. Which CLI command could assist the technician to find the location of the networking problem?
- msconfig
- ipconfig/renew
- tracert
- ipconfig
50. Which two TCP header fields are used to confirm receipt of data? (Choose two.)
- FCS
- acknowledgment number
- sequence number
- preamble
- checksum
51. When analog voice signals are converted for use on a computer network, in what format are they encapsulated?
- IP packets
- segments
- frames
- bits
52. Refer to the exhibit. An administrator is trying to troubleshoot connectivity between PC1 and PC2 and uses the tracert command from PC1 to do it. Based on the displayed output, where should the administrator begin troubleshooting?
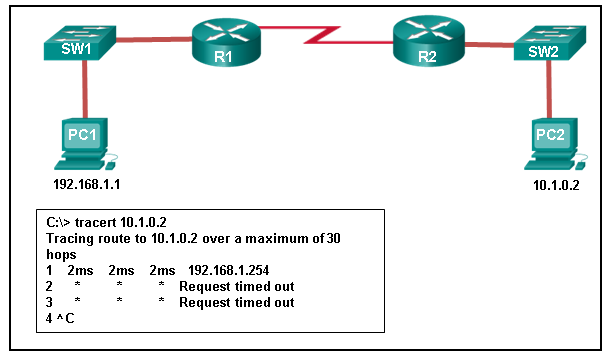
- SW1
- R1
- SW2
- PC2
- R2
53. A network technician attempts to ping www.example.net from a customer computer, but the ping fails. Access to mapped network drives and a shared printer are working correctly. What are two potential causes for this problem? (Choose two.)
- The Windows domain or workgroup name that is configured on the computer is incorrect.
- The computer has been assigned a static IP address.
- The target web server is down.
- DNS service is unavailable on the customer network.
- The HTTP protocol is not working properly on the target server.
54. A data center has recently updated a physical server to host multiple operating systems on a single CPU. The data center can now provide each customer with a separate web server without having to allocate an actual discrete server for each customer. What is the networking trend that is being implemented by the data center in this situation?
- maintaining communication integrity
- online collaboration
- virtualization
- BYOD
55. What is an example of cloud computing?
- a service that offers on-demand access to shared resources
- a network infrastructure that spans a large geographic area
- an architectural style of the World Wide Web
- a continuous interaction between people, processes, data, and things
56. Which two scenarios would benefit the user the most by adding quality of service (QoS) to the network? (Choose two.)
- Students are updating information about their sport activities on the class Facebook page.
- A student is sending emails to a friend.
- A student is communicating via Skype with a friend in another country.
- Students are watching a lecture from a YouTube site.
57. An employee of a large corporation remotely logs into the company using the appropriate username and password. The employee is attending an important video conference with a customer concerning a large sale. It is important for the video quality to be excellent during the meeting. The employee is unaware that after a successful login, the connection to the company ISP failed. The secondary connection, however, activated within seconds. The disruption was not noticed by the employee or other employees.
What three network characteristics are described in this scenario? (Choose three.)
- scalability
- security
- integrity
- fault tolerance
- quality of service
- powerline networking
58. Which three statements describe the functions of the Cisco hierarchical network design model? (Choose three.)
- The goal of the core layer is maximizing throughput.
- The distribution layer distributes network traffic directly to end users.
- The distribution layer is responsible for traffic filtering and isolating failures from the core.
- The access layer provides a means of connecting end devices to the network.
- Route summarization is not necessary at the core and distribution layers.
- The core layer usually employs a star topology.
59. What is the key difference between a type 1 hypervisor and a type 2 hypervisor?
- A type 1 hypervisor runs directly on the system hardware and a type 2 hypervisor requires a host OS to run.
- A type 1 hypervisor supports server virtualizations and a type 2 hypervisor only supports workstation virtualization.
- A type 1 hypervisor supports all server OS virtualization and a type 2 hypervisor supports Linux and Mac virtualization.
- A type 1 hypervisor runs on specialized systems and a type 2 hypervisor runs on desktop computers.
60. Open the PT activity. Perform the tasks in the activity instructions and then answer the question. What is the IP address of this server?
- 209.165.201.4
- 192.168.10.100
- 209.165.201.3
- 192.168.10.1
61. Refer to the exhibit. Host H2 sends a unicast message to host H6. Which destination IP address is contained in the header of the packet when it reaches host H6?
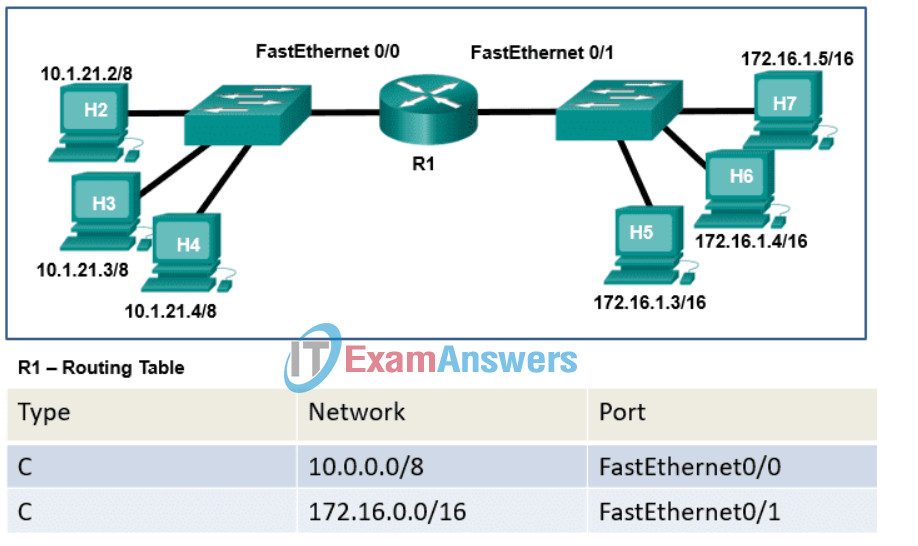
- the IP address assigned to the network adapter on host H2
- the IP address assigned to the network adapter on host H6
- the IP address of the FastEthernet0/1 interface on router R1
- the IP address of the FastEthernet0/0 interface on router R1
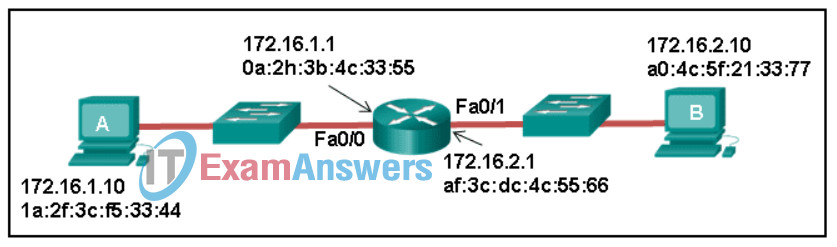
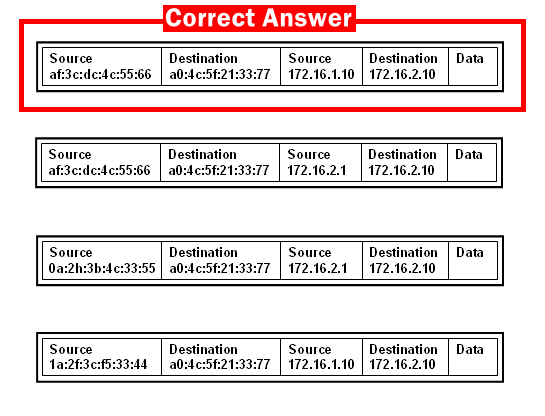
62. Refer to the exhibit. Host A sends a data packet to host B. What will be the addressing information of the data packet when it reaches host B?
63. Which command would a technician use to display network connections on a host computer?
- ipconfig
- nslookup
- tracert
- netstat
64. Refer to the exhibit. PC1 attempts to connect to File_server1 and sends an ARP request to obtain a destination MAC address. Which MAC address will PC1 receive in the ARP reply?

- the MAC address of the G0/0 interface on R2
- the MAC address of S2
- the MAC address of S1
- the MAC address of File_server1
- the MAC address of the G0/0 interface on R1
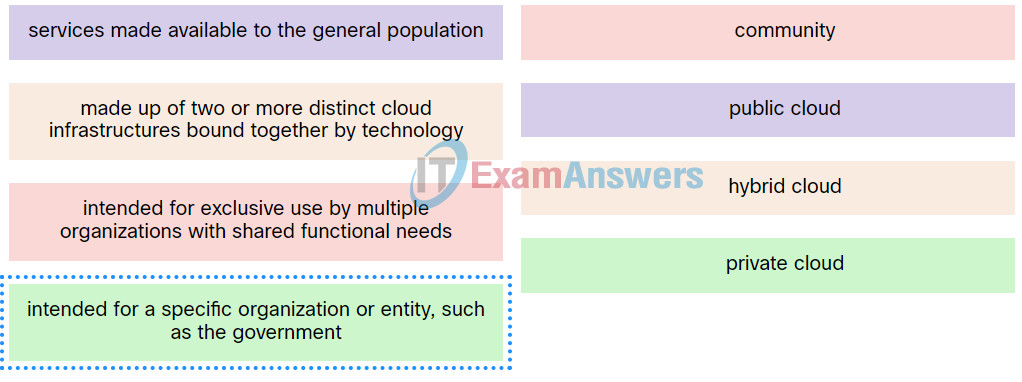
65. Match the definition to the type of cloud.
66. Refer to the exhibit. Host A has sent a packet to host B. What will be the source MAC and IP addresses on the packet when it arrives at host B?
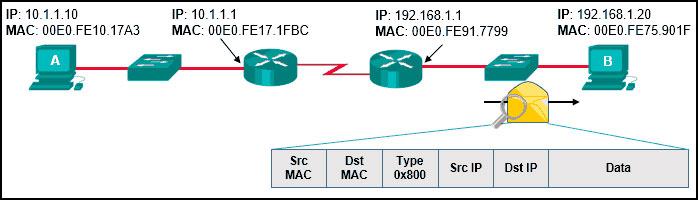
Source MAC: 00E0.FE91.7799
Source IP: 10.1.1.10
Source MAC: 00E0.FE91.7799
Source IP: 10.1.1.1
Source MAC: 00E0.FE10.17A3
Source IP: 10.1.1.10
Source MAC: 00E0.FE91.7799
Source IP: 192.168.1.1
Source MAC: 00E0.FE10.17A3
Source IP: 192.168.1.1
67. Which two statements are correct in a comparison of IPv4 and IPv6 packet headers? (Choose two.)
- The Time-to-Live field from IPv4 has been replaced by the Hop Limit field in IPv6.
- The Version field from IPv4 is not kept in IPv6.
- The Destination Address field is new in IPv6.
- The Source Address field name from IPv4 is kept in IPv6.
- The Header Checksum field name from IPv4 is kept in IPv6.
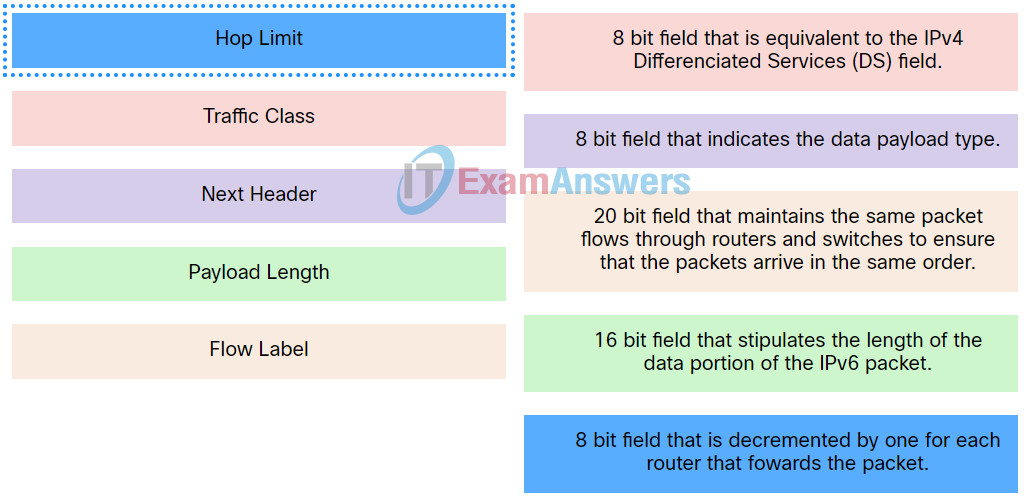
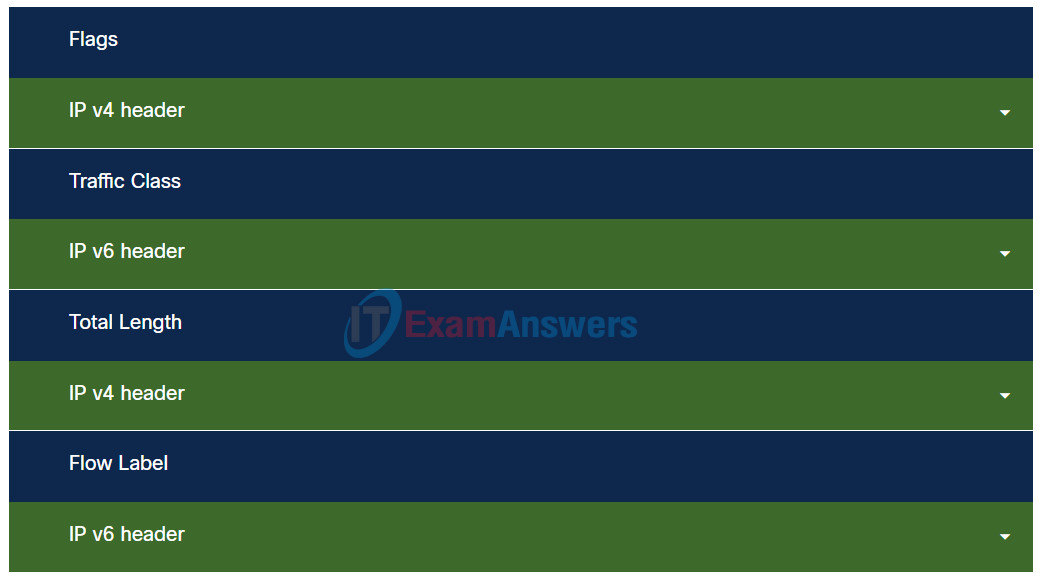
68. Match the IPv6 packet header field with the description.
69. Which three IPv4 header fields have no equivalent in an IPv6 header? (Choose three.)
- protocol
- fragment offset
- TTL
- version
- identification
- flag
70. Which two items are used by a host device when performing an ANDing operation to determine if a destination address is on the same local network? (Choose two.)
- network number
- destination IP address
- source MAC address
- destination MAC address
- subnet mask
71. A home network has both wired and wireless connectivity. From a laptop computer, the user issues a ping to the wireless printer located in another room. The first two echo requests fail, but the last two succeed. Additional pings are all successful. Why do the first two echo requests fail?
- The computer and the printer must join the wireless network first and that process takes time.
- The distance between the computer and the printer causes delay on the first two pings.
- The wireless printer must be activated and that takes time.
- The computer must use ARP to obtain the MAC address of the printer and this process takes time.
72. Which statement is true regarding the UDP client process during a session with a server?
- A session must be established before datagrams can be exchanged.
- Datagrams that arrive in a different order than that in which they were sent are not placed in order.
- Application servers have to use port numbers above 1024 in order to be UDP capable.
- A three-way handshake takes place before the transmission of data begins.
73. Match each DHCP message type with its description.
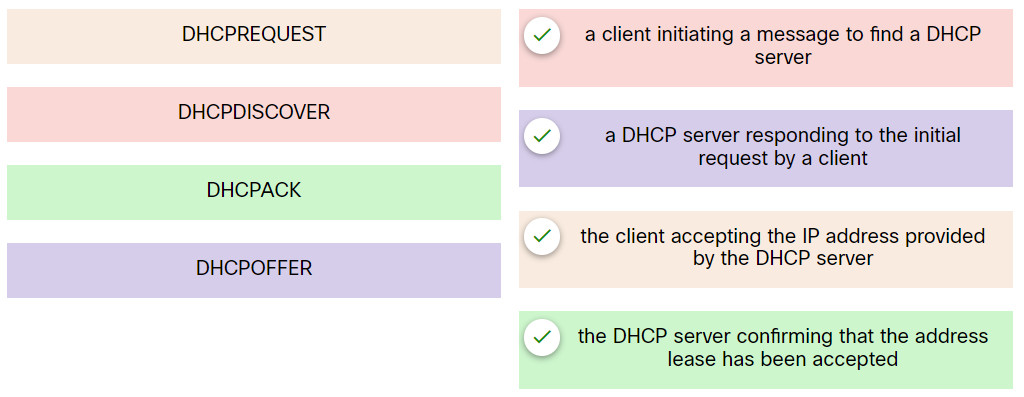
Networking Devices and Initial Configuration Course Final Exam 18
74. Refer to the exhibit. Which protocol was responsible for building the table that is shown?
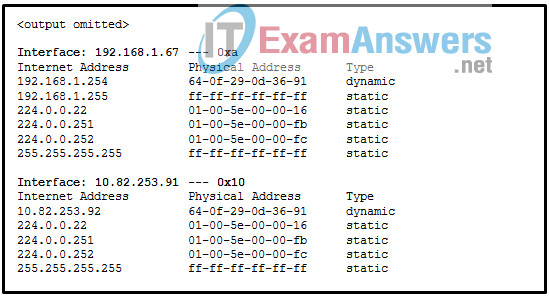
- ARP
- DHCP
- ICMP
- DNS
75. Refer to the exhibit. A web designer calls to report that the web server web-s1.cisco.com is not reachable through a web browser. The technician uses command line utilities to verify the problem and to begin the troubleshooting process. Which two things can be determined about the problem? (Choose two.)
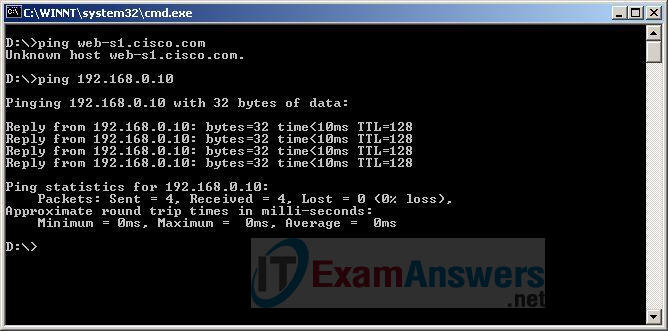
- A router is down between the source host and the server web-s1.cisco.com.
- The web server at 192.168.0.10 is reachable from the source host.
- The default gateway between the source host and the server at 192.168.0.10 is down.
- DNS cannot resolve the IP address for the server web-s1.cisco.com.
- There is a problem with the web server software on web-s1.cisco.com.
76. What are two potential network problems that can result from ARP operation? (Choose two.)
- Multiple ARP replies result in the switch MAC address table containing entries that match the MAC addresses of hosts that are connected to the relevant switch port.
- Network attackers could manipulate MAC address and IP address mappings in ARP messages with the intent of intercepting network traffic.
- On large networks with low bandwidth, multiple ARP broadcasts could cause data communication delays.
- Manually configuring static ARP associations could facilitate ARP poisoning or MAC address spoofing.
- Large numbers of ARP request broadcasts could cause the host MAC address table to overflow and prevent the host from communicating on the network.
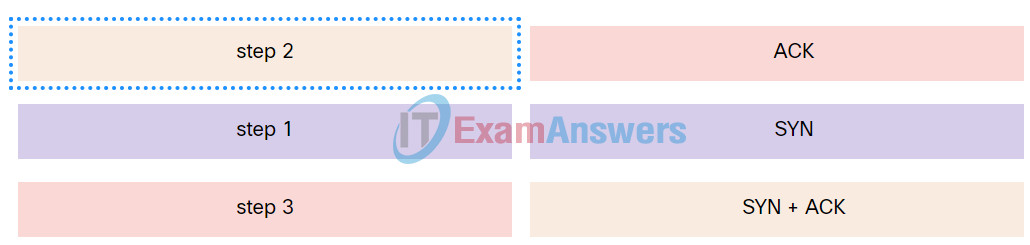
77. Match the TCP flag to the correct step in the session establishment sequence.
78. What is the difference between the terms keyword and argument in the IOS command structure?
- A keyword is entered with a predefined length. An argument can be any length.
- A keyword always appears directly after a command. An argument does not.
- A keyword is required to complete a command. An argument is not.
- A keyword is a specific parameter. An argument is not a predefined variable.
79. Which three commands are used to set up secure access to a router through a connection to the console interface? (Choose three.)
- line vty 0 4
- password cisco
- interface fastethernet 0/0
- line console 0
- enable secret cisco
- login
80. What three configuration steps must be performed to implement SSH access to a router? (Choose three.)
- a unique hostname
- a password on the console line
- an IP domain name
- a user account
- an enable mode password
- an encrypted password
81. Refer to the exhibit. What is the maximum TTL value that is used to reach the destination www.cisco.com?
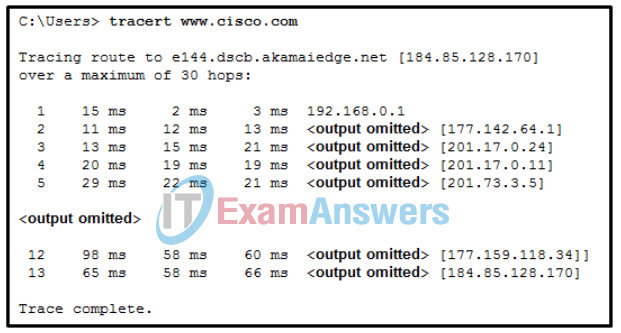
Networking Devices and Initial Configuration Course Final Exam 26
- 12
- 13
- 11
- 14
82. Refer to the exhibit. A ping to PC2 is issued from PC0, PC1, and PC3 in this exact order. Which MAC addresses will be contained in the S1 MAC address table that is associated with the Fa0/1 port?
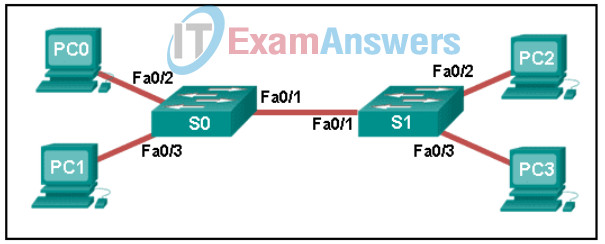
Networking Devices and Initial Configuration Course Final Exam 12
- just the PC1 MAC address
- just PC0 and PC1 MAC addresses
- just the PC0 MAC address
- PC0, PC1, and PC2 MAC addresses
- just the PC2 MAC address
83. Match field names to the IP header where they would be found.
84. What is the dotted decimal representation of the IPv4 address
11001011.00000000.01110001.11010011?
- 203.0.113.211
- 209.165.201.223
- 198.51.100.201
- 192.0.2.199
85. Which protocol is used by IPv4 and IPv6 to provide error messaging?
- NDP
- ARP
- ICMP
- DHCP
86. The global configuration command ip default-gateway 172.16.100.1 is applied to a switch. What is the effect of this command?
- The switch can communicate with other hosts on the 172.16.100.0 network.
- The switch can be remotely managed from a host on another network.
- The switch will have a management interface with the address 172.16.100.1.
- The switch is limited to sending and receiving frames to and from the gateway 172.16.100.1.
87. Match the router prompt to the configuration task.
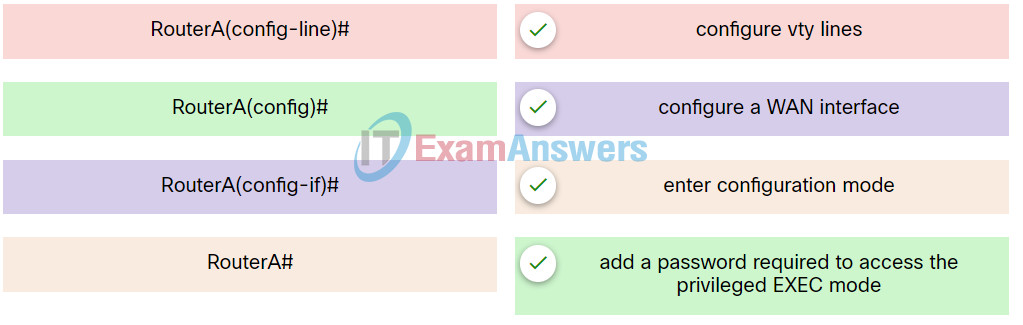
Networking Devices and Initial Configuration Course Final Exam 29
88. While troubleshooting a network problem, a network administrator issues the show version command on a router. What information can be found by using this command?
- the amount of NVRAM, DRAM, and flash memory installed on the router
- the bandwidth, encapsulation, and I/O statistics on the interfaces
- differences between the backup configuration and the current running configuration
- the version of the routing protocol that is running on the router
89. Refer to the exhibit. PC1 sends a frame with the destination MAC address 3c97.0e07.a1b2. Switch S1 looks up the destination MAC address in its CAM table but the address is not there. What will the switch do?
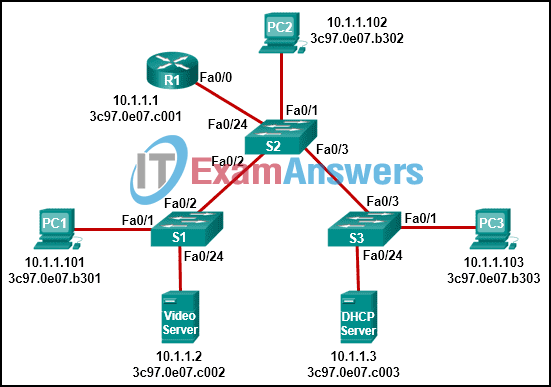
- It willl add the destination MAC address to the CAM table.
- It will forward the frame out all ports except Fa0/1.
- It will send a destination unreachable message back to PC1.
- The switch will drop the frame.
- It will forward the frame out port Fa0/2 towards the router.
90. Which forwarding action does a switch take when the destination MAC address of an Ethernet frame is an unknown unicast?
- The switch forwards the frame to the default gateway.
- The switch forwards the frame the same way it does for broadcast and multicast MAC addresses.
- The switch drops the frame.
- The switch forwards the frame out a specified port for this type of address.
91. Refer to the exhibit. An administrator is troubleshooting connectivity on the office network. PC1 is able to send print jobs to Printer1, but is unable to access File Server1. Which action would correct the problem?
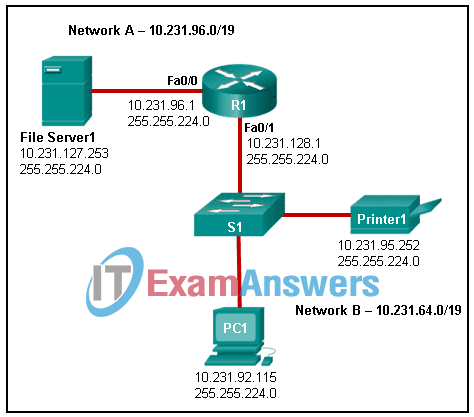
- Change the R1 Fa0/1 interface IP address to 10.231.64.1.
- Change the R1 Fa0/0 interface subnet mask to 255.255.0.0.
- Change the File Server1 IP address to 10.231.96.253.
- Change the PC1 IP address to 10.231.64.115.
92. Match the characteristic to the protocol category.

93. The ARP table in a switch maps which two types of address together?
- Layer 3 address to a Layer 4 address
- Layer 4 address to a Layer 2 address
- Layer 2 address to a Layer 4 address
- Layer 3 address to a Layer 2 address
94. A network administrator issues the Switch# show running-config command on a Cisco switch. Which term is used to describe the part “running-config” in the command?
- command
- argument
- hot key
- keyword
95. The global configuration command ip default-gateway 172.16.100.1 is applied to a switch. What is the effect of this command?
- The switch can be remotely managed from a host on another network.
- The switch can communicate with other hosts on the 172.16.100.0 network.
- The switch will have a management interface with the address 172.16.100.1.
- The switch is limited to sending and receiving frames to and from the gateway 172.16.100.1.
96. What is the purpose of the MAC address which is added to an e-mail message that is sent from a teacher to a student?
- It identifies the network to which the sending computer belongs.
- It identifies the computer on the Internet.
- It identifies the TCP/IP network application to which the reply can be sent.
- It identifies the computer on the LAN.
97. What is the purpose of assigning an IP address to the VLAN1 interface on a Cisco Layer 2 switch?
- to enable remote access to the switch to manage it
- to permit IP packets to be forwarded by the switch
- to create a new IP local network on the switch
- to enable the switch to route packets between networks
98. Which command should be used to test connectivity to the loopback interface?
- ping 255.255.255.255
- ping 0.0.0.0
- ping 127.0.0.1
- ping loopback
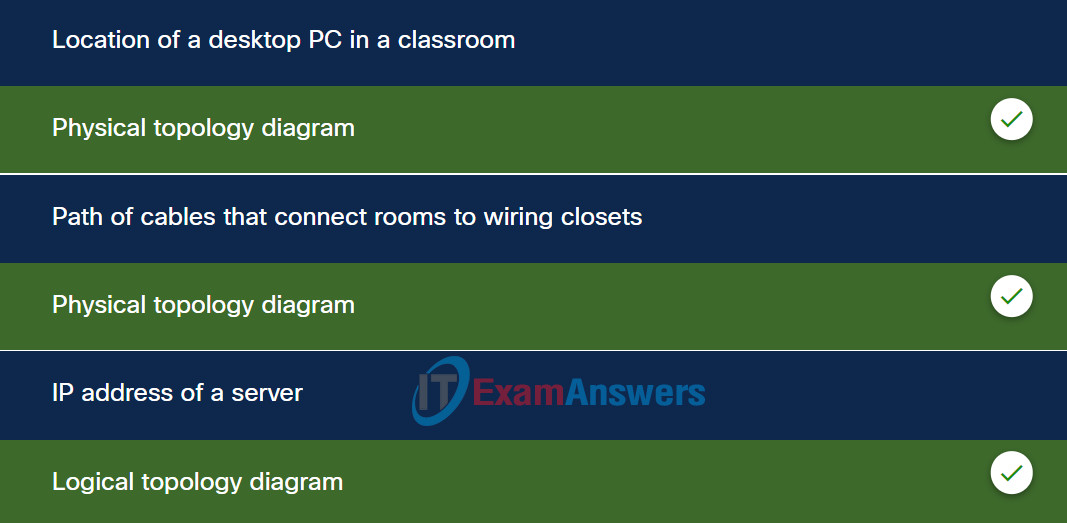
99. Match each item to the type of topology diagram on which it is typically identified.
100. Refer to the exhibit. The IP address of which device interface should be used as the default gateway setting of host H1?
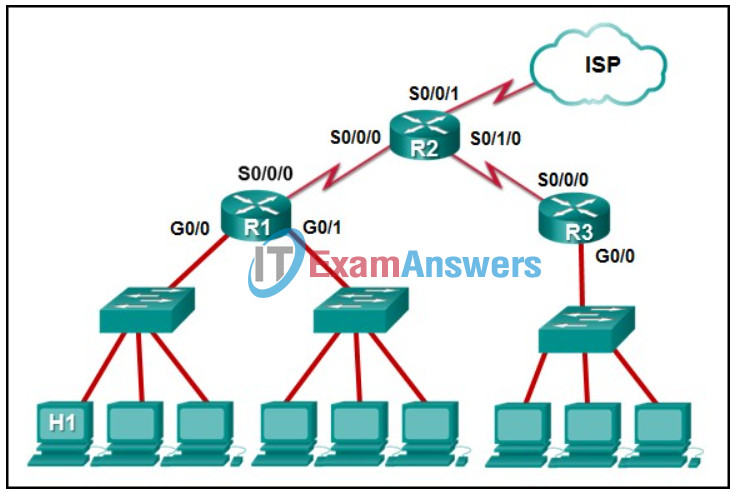
- R1: G0/0
- R2: S0/0/1
- R2: S0/0/0
- R1: S0/0/0
101. What are two advantages of using fiber-optic cabling to interconnect devices? (Choose two.)
- Fiber-optic cables can extend several miles.
- Fiber-optic cable is immune from EMI and RFI.
- Fiber-optic cables are easy to install..
- Fiber-optic cables are commonly found in both homes and small businesses.
- Fiber-optic cables use extra shielding to protect copper wires.
102. Which statement is true about the CSMA/CD access method that is used in Ethernet?
- When a device hears a carrier signal and transmits, a collision cannot occur.
- All network devices must listen before transmitting.
- A jamming signal causes only devices that caused the collision to execute a backoff algorithm.
- Devices involved in a collision get priority to transmit after the backoff period.
103. Which two characteristics describe the use of a logical topology? (Choose two.)
- showing the physical connections of end devices
- identifying the interconnection of routers and switches
- describing the infrastructure
- identifying the virtual connections between devices
- identifying the type of media access control used
- identifying cable length requirements
104. Which command can be used on a Windows host to display the routing table?
- show ip route
- tracert
- netstat –r
- netstat –s
105. Refer to the exhibit. Consider the IP address configuration shown from PC1. What is a description of the default gateway address?
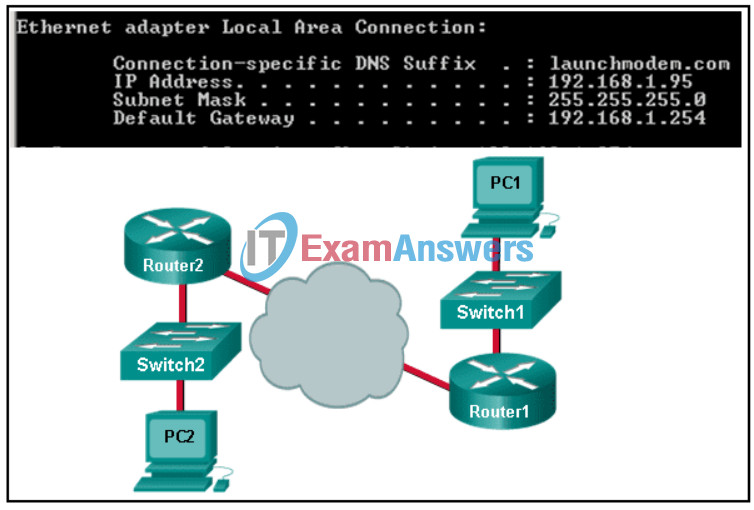
- It is the IP address of the Router1 interface that connects the PC1 LAN to Router1.
- It is the IP address of the Router1 interface that connects the company to the Internet.
- It is the IP address of Switch1 that connects PC1 to other devices on the same LAN.
- It is the IP address of the ISP network device located in the cloud.
106. Match the characteristics to the correct type of fiber.

107. A user can access a file share resource on a server located in the same office but cannot access the internet. What is the possible cause?
- The IPv4 address and subnet mask are misconfigured on the PC.
- The default gateway address is misconfigured on the PC.
- The switch is malfunctioning.
- The DHCP server is disconnected.
108. Which statement describes the operation of devices accessing an Ethernet network?
- Each device monitors the media and sends a notification for its intention to send data first.
- To send data, each device waits for a token to be available.
- Each device monitors the media and sends data when the media is free.
- Each device in turn receives a frame. If the frame is not intended for the device, the device passes it along.
109. A PC has sent an RS message to an IPv6 router attached to the same network. Which two pieces of information will the router send to the client? (Choose two.)
- subnet mask in dotted decimal notation
- administrative distance
- domain name
- prefix length
- DNS server IP address
- prefix
110. Which two types of messages are used in place of ARP for address resolution in IPv6? (Choose two.)
- echo reply
- neighbor solicitation
- broadcast
- neighbor advertisement
- anycast
- echo request
111. A site administrator has been told that a particular network at the site must accommodate 126 hosts. Which subnet mask would be used that contains the required number of host bits?
- 255.255.255.240
- 255.255.255.0
- 255.255.255.224
- 255.255.255.128
112. An IPv6 enabled device sends a data packet with the destination address of FF02::1. What is the target of this packet?
- only IPv6 configured routers
- only IPv6 DHCP servers
- all IPv6 enabled devices on the local link or network
- the one IPv6 device on the link that has been uniquely configured with this address
113. What are two services provided by IPv6 neighbor discovery protocol? (Choose two.)
- maximum IPv6 packet size for end-to-end transmission
- IPv6 dynamic routing
- domain name resolving
- router discovery
- address resolution
114. A secretary receives a phone call from someone claiming that their manager is about to give an important presentation but the presentation files are corrupted.
The caller sternly asks that the secretary email the presentation right away to a personal email address. The caller also states that the secretary is being held personally responsible for the success of this presentation.
What type of social engineering tactic is the caller using?
- intimidation
- familiarity
- urgency
- trusted partners
115. The awareness and identification of vulnerabilities is a critical function of a cybersecurity specialist. Which of the following resources can they use to identify specific details about vulnerabilities?
- ISO/IEC 27000 model
- Infragard
- NIST/NICE framework
- CVE national database
116. Which three security services are part of the concept of administrative access controls?
- data in transit, data at rest, and data in process
- confidentiality, integrity, and availability
- technology, policy and practices, and people
- authentication, authorization, and accounting
117. Which statement describes the use of powerline networking technology?
- A device connects to an existing home LAN using an adapter and an existing electrical outlet.
- New “smart” electrical cabling is used to extend an existing home LAN.
- Wireless access points use powerline adapters to distribute data through the home LAN.
- A home LAN is installed without the use of physical cabling.
118. A user is configuring a wireless access point and wants to prevent any neighbors from discovering the network. What action does the user need to take?
- Configure DMZ settings.
- Disable SSID broadcast.
- Configure a DNS server.
- Enable WPA encryption.
119. A tourist is traveling through the countryside and needs to connect to the internet from a laptop. However, the laptop only has Wi-Fi and Ethernet connections. The tourist has a smartphone with 3G/4G connectivity. What can the tourist do to allow the laptop to connect to the internet?
- Enable tethering and create a hotspot.
- Use the smartphone to access web pages and then pass the web pages to the laptop.
- Use the smartphone to access the internet through a satellite connection and then share that connection with the laptop.
- Use an Ethernet cable to connect the smartphone to the laptop.
120. Match the ICMPv6 messages to the description.
121. A network administrator is assigned the 172.16.0.0/24 block of addresses to use in designing an IP addressing scheme. The administrator submits this design for approval:
- 172.16.0.0/26
- 172.16.0.64/27
- 172.16.0.96/26
- 172.16.0.128/27
What should be the response from the senior network engineer regarding this design?
- This design is flawed because the 172.16.0.96/26 network is not a valid block of addresses.
- This design is flawed because the 172.16.0.96/26 network overlaps with other addresses.
- This design is flawed because no design could have two networks that use a /26 mask and are not consecutive blocks of addresses.
- This design is flawed because the 172.16.0.128/27 network number is invalid.
- This design will work for the branch office.
122. What is the prefix for the host address 2001:DB8:BC15:A:12AB::1/64?
- 2001:DB8:BC15:A
- 2001:DB8:BC15:A:1
- 2001:DB8:BC15:A:12
- 2001:DB8:BC15
123. How are port numbers used in the TCP/IP encapsulation process?
- Source port and destination port numbers are randomly generated.
- Source port numbers and destination port numbers are not necessary when UDP is the transport layer protocol being used for the communication.
- If multiple conversations occur that are using the same service, the source port number is used to track the separate conversations.
- Destination port numbers are assigned automatically and cannot be changed.
124. What is the shortest valid representation of the IPv6 address 2001:0DB8:0000:1470:0000:0000:0000:0200?
- 2001:DB8::1470::200
- 2001:0DB8:0:147::02
- 2001:0DB8::1470:0:0:0:2
- 2001:DB8:0:1470::200
125. A college has five campuses. Each campus has IP phones installed. Each campus has an assigned IP address range. For example, one campus has IP addresses that start with 10.1.x.x. On another campus the address range is 10.2.x.x. The college has standardized that IP phones are assigned IP addresses that have the number 4X in the third octet. For example, at one campus the address ranges used with phones include 10.1.40.x, 10.1.41.x, 10.1.42.x, etc. Which two groupings were used to create this IP addressing scheme? (Choose two.)
- personnel type
- device type
- geographic location
- department
- support model
126. Refer to the exhibit. If all devices are using a subnet mask of 255.255.255.0, which laptop would have an IP address with the same network number as the server?
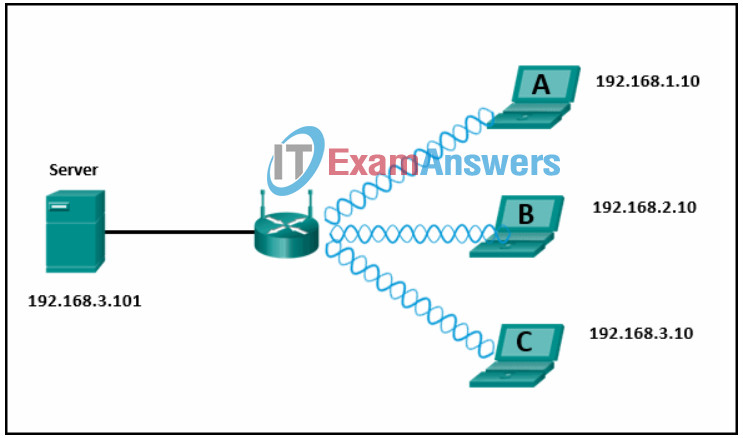
- B
- A
- C
127. For what purpose are IPv4 addresses utilized?
- An IPv4 address is burned into the network card to uniquely identify a device.
- An IPv4 address is used to identify the number of IP networks available.
- An IPv4 address is used to uniquely identify a device on an IP network.
- An IPv4 address is used to uniquely identify the application that requested the information from a remote device.
128. A user is setting up a home wireless network. A global address is to be used in NAT translations for traffic flowing through the wireless router. How is this global address assigned?
- The wireless router will act as a DHCP client in order to receive global addressing from the ISP.
- The default gateway IP address of the LAN device is used as the global address for NAT translations through the wireless router.
- The network administrator will choose an available IP address from the LAN and configure the global addressing of the wireless router.
- The host devices will select an unused IP address on the LAN for performing NAT through the wireless router.
129. Match the protocol function to the description while taking into consideration that a network client is visiting a web site.
130. Refer to the exhibit. PC1 needs to resolve the host name of the web server into an IP address by using DNS. What destination IP address and destination port number will PC1 assign to the DNS query packet?
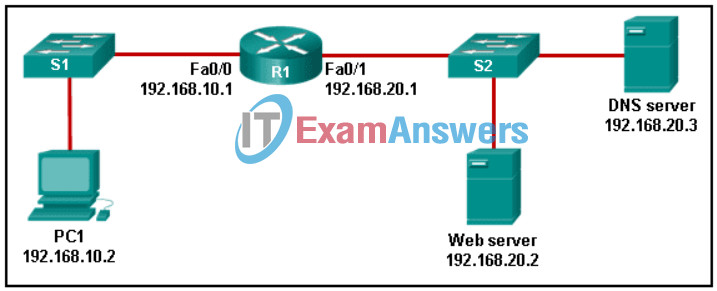
Networking Basics: Course Completion Assessment & Survey Q61
- 192.168.20.3 port 53
- 192.168.10.1 port 53
- 192.168.20.3 port 80
- 192.168.20.2 port 80
- 192.168.20.2 port 53
131. How many bits are in an IPv4 address?
- 32
- 256
- 128
- 64
132. A company is contemplating whether to use a client/server or a peer-to-peer network. What are three characteristics of a peer-to-peer network? (Choose three.)
- better security
- scalable
- easy to create
- better device performance when acting as both client and server
- less cost to implement
- lacks centralized administration
133. A production switch is reloaded and finishes with a Switch> prompt. What two facts can be determined? (Choose two.)
- The switch did not locate the Cisco IOS in flash, so it defaulted to ROM.
- The boot process was interrupted.
- A full version of the Cisco IOS was located and loaded.
- There is not enough RAM or flash on this router.
- POST occurred normally.
134. A user is complaining that an external web page is taking longer than normal to load.The web page does eventually load on the user machine. Which tool should the technician use with administrator privileges in order to locate where the issue is in the network?
- tracert
- nslookup
- ipconfig /displaydns
- ping
135. When a host sends a packet, how does it determine if the destination of the packet is on the same local network or on a remote network?
- It compares the source and destination MAC addresses.
- It queries the DNS server with the destination IP address.
- It checks to see if the default gateway is configured.
- It uses the subnet mask to compare the source and destination IP address.
136. Match the network with the correct IP address and prefix that will satisfy the usable host addressing requirements for each network.
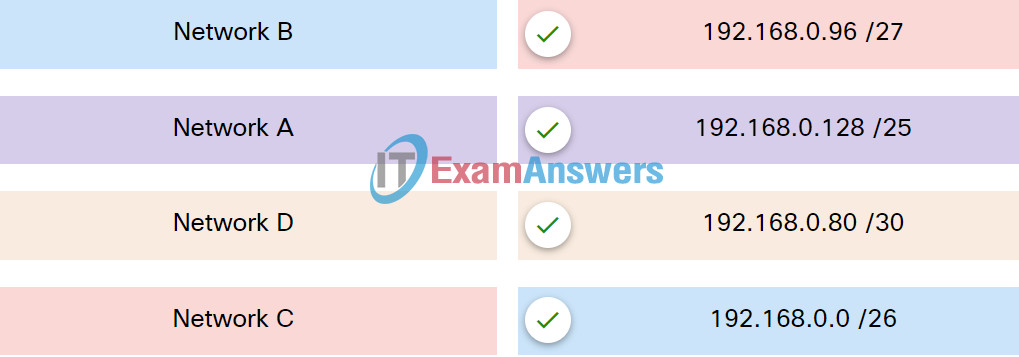
137. Which wireless RF band do IEEE 802.11b/g devices use?
- 60 GHz
- 2.4 GHz
- 900 MHz
- 5 GHz
138. Refer to the exhibit. Which term correctly identifies the device type that is included in the area B?
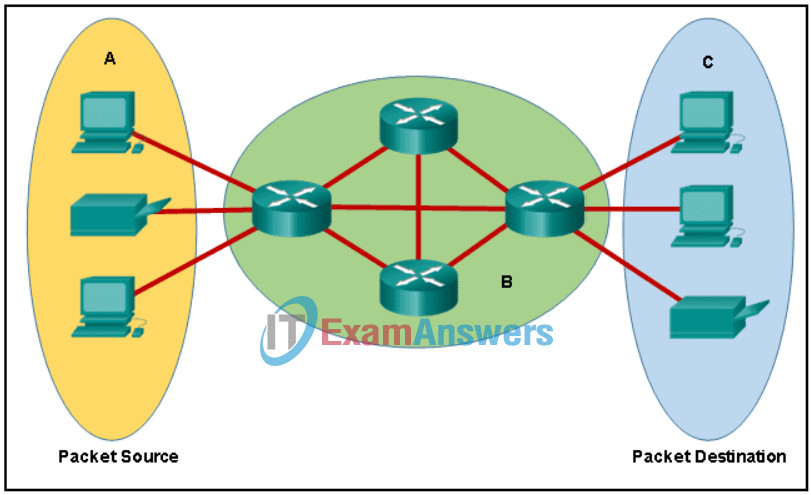
Networking Basics Course Final Exam 3
- end
- transfer
- source
- intermediary
139. What is a disadvantage of deploying a peer-to-peer network model?
- lack of centralized administration
- high cost
- difficulty of setup
- high degree of complexity
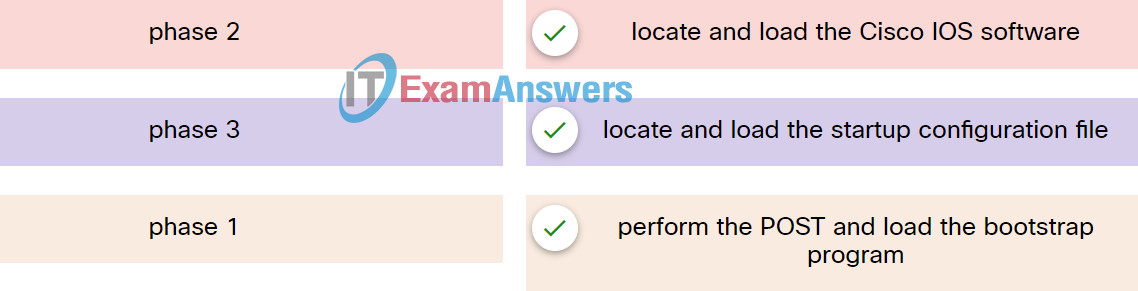
140. Match the phases to the functions during the boot up process of a Cisco router.
141. Which troubleshooting tool can be used to determine the current TCP open connections on a PC?
- tracrt
- nslookup
- netstat
- ping
- ipconfig
142. A group of Windows PCs in a new subnet has been added to an Ethernet network. When testing the connectivity, a technician finds that these PCs can access local network resources but not the Internet resources. To troubleshoot the problem, the technician wants to initially confirm the IP address and DNS configurations on the PCs, and also verify connectivity to the local router. Which three Windows CLI commands and utilities will provide the necessary information? (Choose three.)
- netsh interface ipv6 show neighbor
- tracert
- nslookup
- ping
- arp -a
- ipconfig
- telnet
143. Refer to the exhibit. PC1 is unable to access PC2. To troubleshoot this problem, the technician needs to confirm that the next hop interface is operational. Which default gateway address should the technician ping from PC1 to confirm this?
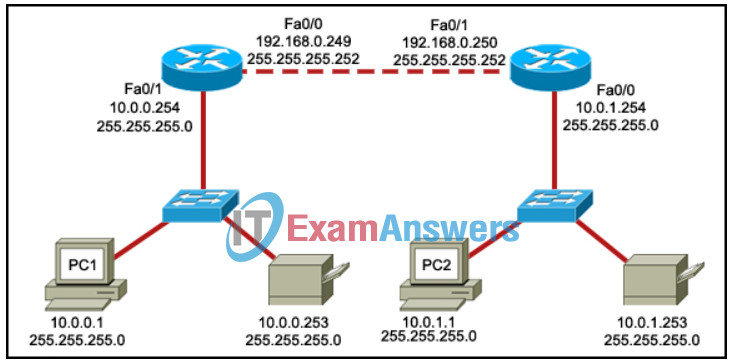
- 10.0.0.254
- 10.0.1.254
- 192.168.0.250
- 192.168.0.249
144. Refer to the exhibit. An IT consulting firm is helping a mid-sized marketing and advertising company for updating the campus network. Which three network design features are covered in the diagram? (Choose three.)
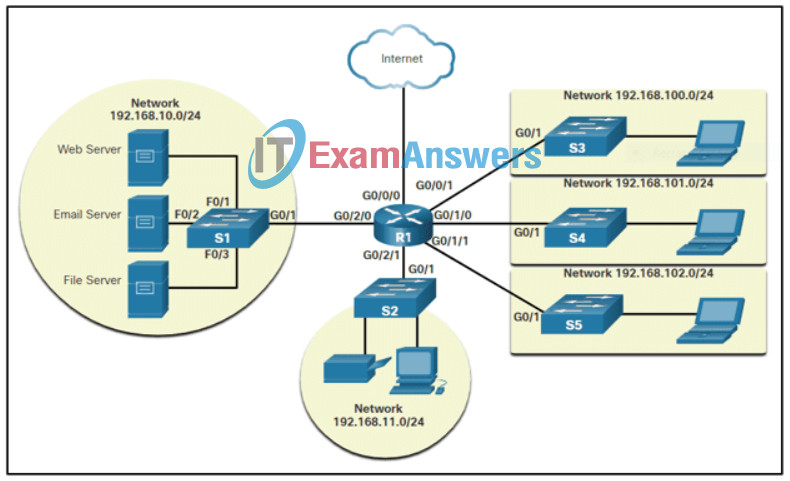
- flow of information in the network including addressing
- network devices that might be needed
- network segmentation
- data packet routing and protocol needs
- IP network subnetting consideration
- locations of network devices in the company
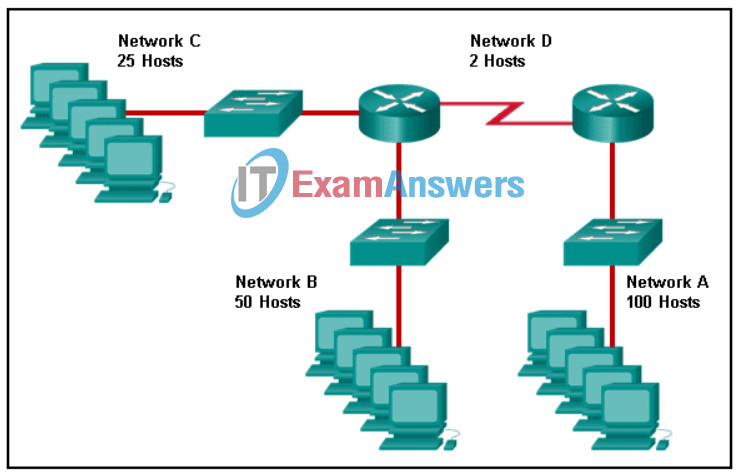
145. Refer to the exhibit. Using VLSM, what is the largest and smallest subnet mask required on this network, including the links between routers, in order to minimize address waste?
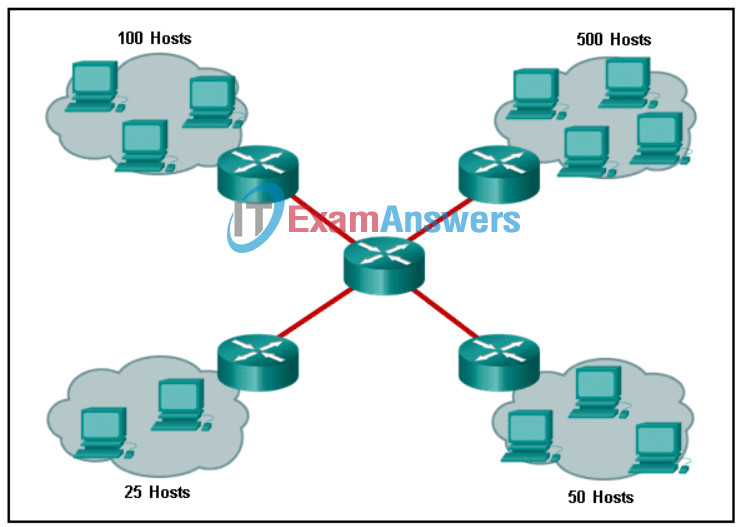
- 255.255.255.0 and 255.255.255.252
- 255.255.254.0 and 255.255.255.252
- 255.255.255.128 and 255.255.255.224
- 255.255.254.0 and 255.255.255.224
146. IPv6 host A is sending a neighbor solicitation message to IPv6 host B on the same Ethernet network. Which statement describes the destination MAC address host A uses to build the Ethernet frame of the neighbor solicitation message?
- It maps the special braodcast address reserved for neighbor discovery protocol.
- It maps the special solicited-node multicast address of the destination IPv6 address.
- It maps the special IPv6 unicast address reserved for neighbor discovery protocol.
- It maps the special address from the router advertisement message.
147. Which three steps must be completed to manually connect an Android or IOS device to a secured wireless network? (Choose three.)
- Change the MAC address.
- Set the IP address.
- Enter the network SSID.
- Activate the Bluetooth antenna.
- Input the authentication password.
- Choose the correct security type.
148. What are two characteristics of RAM on a Cisco device? (Choose two.)
- RAM is able to store multiple versions of IOS and configuration files.
- The configuration that is actively running on the device is stored in RAM.
- The contents of RAM are lost during a power cycle.
- RAM provides nonvolatile storage.
- RAM is a component in Cisco switches but not in Cisco routers.
149. Which type of device provides an Internet connection through the use of a phone jack?
- satellite modem
- Wi-Fi AP
- DSL modem
- cable modem
150. A traveling sales representative uses a cell phone to interact with the home office and customers, track samples, make sales calls, log mileage, and upload/download data while at a hotel. Which internet connectivity method would be a preferred method to use on the mobile device due to the low cost?
- cellular
- Wi-Fi
- DSL
- cable
151. IPv6 host A is communicating with a remote IPv6 host B. Which device would send ICMPv6 redirect messages to inform that a better next-hop device should be used?
- Host A
- a router in the traffic path
- the switch connected to Host A
- Host B
- the switch connected to Host B
152. Refer to the exhibit. The PC is connected to the console port of the switch. All the other connections are made through FastEthernet links. Which types of UTP cables can be used to connect the devices?
1 – rollover, 2 – crossover, 3 – straight-through
1 – rollover, 2 – straight-through, 3 – crossover
1 – crossover, 2 – rollover, 3 – straight-through
1 – crossover, 2 – straight-through, 3 – rollover
153. A workstation connected to an Ethernet switch port is experiencing connectivity problems. The network technician chooses to use the bottom-up troubleshooting method to identify the issue. What are two possible causes of physical layer network problems that the technician should check? (Choose two.)
- logical addressing issues
- incorrect MAC address assigned
- cables plugged into wrong ports
- incorrect subnet mask on an interface
- improperly terminated cables
- packets received out of sequence
154. An ISP help desk technician receives a call from a customer who reports that no one at their business can reach any websites or get their e-mail. After testing the communication line and finding everything fine, the technician instructs the customer to run nslookup from the command prompt. What does the technician suspect is causing the customer’s problem?
- improper IP address configuration on the host
- failure of DNS to resolve names to IP addresses
- hardware failure of the ISR used to connect the customer to the ISP
- bad cables or connections at the customer site
155. Which information does the show startup-config command display?
- the contents of the current running configuration file in the RAM
- the IOS image copied into RAM
- the bootstrap program in the ROM
- the contents of the saved configuration file in the NVRAM
156. What is true concerning physical and logical topologies?
- Physical topologies are concerned with how a network transfers frames.
- The logical topology is always the same as the physical topology.
- Physical topologies display the IP addressing scheme of each network.
- Logical topologies refer to how a network transfers data between devices.
157. After making configuration changes on a Cisco switch, a network administrator issues a copy running-config startup-config command. What is the result of issuing this command?
- The configuration changes will be removed and the original configuration will be restored.
- The new configuration will be stored in flash memory.
- The current IOS file will be replaced with the newly configured file.
- The new configuration will be loaded if the switch is restarted.
158. In the OSI model, what three functional areas are addressed by physical layer standards? (Choose three.)
- frame encapsulation
- error detection and retransmission
- encoding
- physical components
- signaling
- media access control
159. Which two types of signal interference are reduced more by STP than by UTP? (Choose two.)
- dispersion
- MDF
- RFI
- EMI
- white noise
160. An IPv6 host receives an ICMPv6 message requesting MAC address resolution. Which message should the host return to provide the MAC address?
- neighbor solicitation message
- neighbor advertisement message
- router advertisement message
- router solicitation message
161. A technician must accommodate at least 500 subnets from address 172.16.0.0/16. What is an appropriate subnet mask and corresponding number of available host IP addresses per subnet to meet the requirement?
- 255.255.255.192 and 126 hosts
- 255.255.255.0 and 128 hosts
- 255.255.255.128 and 126 hosts
- 255.255.255.224 and 128 hosts
162. Which two statements correctly describe the components of a router? (Choose two.)
- ROM contains diagnostics executed on hardware modules.
- NVRAM stores a backup copy of the IOS used during the boot sequence.
- Flash memory does not lose its contents during a reboot.
- RAM permanently stores the configuration file used during the boot sequence.
- ROM contains the most current and most complete version of the IOS.
- Flash contains boot system commands to identify the location of the IOS.
163. Refer to the exhibit. Considering the addresses already used and having to remain within the 10.16.10.0/24 network range, which subnet address could be assigned to the network containing 25 hosts?
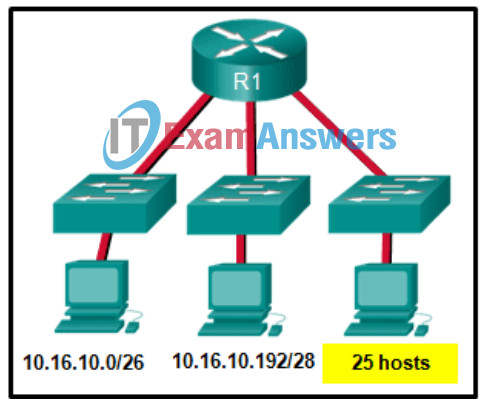
- 10.16.10.240/28
- 10.16.10.240/27
- 10.16.10.160/26
- 10.16.10.64/27
- 10.16.10.128/28
- 10.16.10.224/26
164. Which IPv6 prefix is reserved for communication between devices on the same link?
- FE80::/10
- 2001::/32
- FDFF::/7
- FC00::/7
165. Refer to the exhibit. A user has configured a NIC on the PC as shown but finds that the PC is unable to access the Internet. What is the problem?
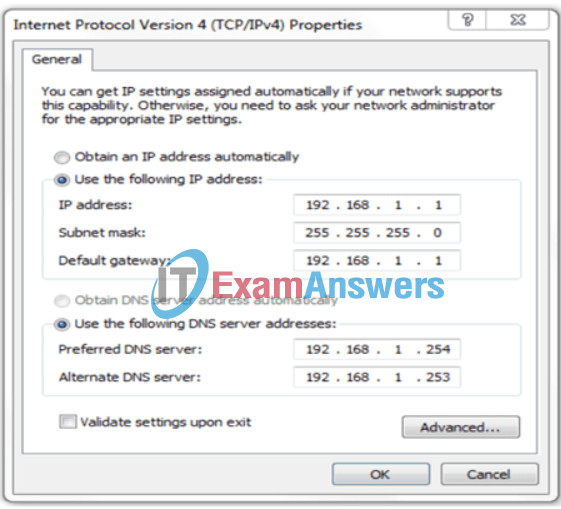
- There should not be an alternate DNS server.
- The preferred DNS address is incorrect.
- The default gateway address is incorrect.
- The settings were not validated upon exit.
166. What type of communication rule would best describe CSMA/CD?
- message encoding
- flow control
- access method
- message encapsulation
167. What are three parts of an IPv6 global unicast address? (Choose three.)
- a global routing prefix that is used to identify the network portion of the address that has been provided by an ISP
- an interface ID that is used to identify the local network for a particular host
- a global routing prefix that is used to identify the portion of the network address provided by a local administrator
- a subnet ID that is used to identify networks inside of the local enterprise site
- an interface ID that is used to identify the local host on the network
168. Which attack takes control over a user’s mobile device and instructs the device to exfiltrate user-sensitive information and send it to threat actors?
- MitMo
- SMiShing
- Bluejacking
- Grayware
169. What do you call an impersonation attack that takes advantage of a trusted relationship between two systems?
- man-in-the-middle
- sniffing
- spoofing
- spamming
170. Match the type of firewall to the description.
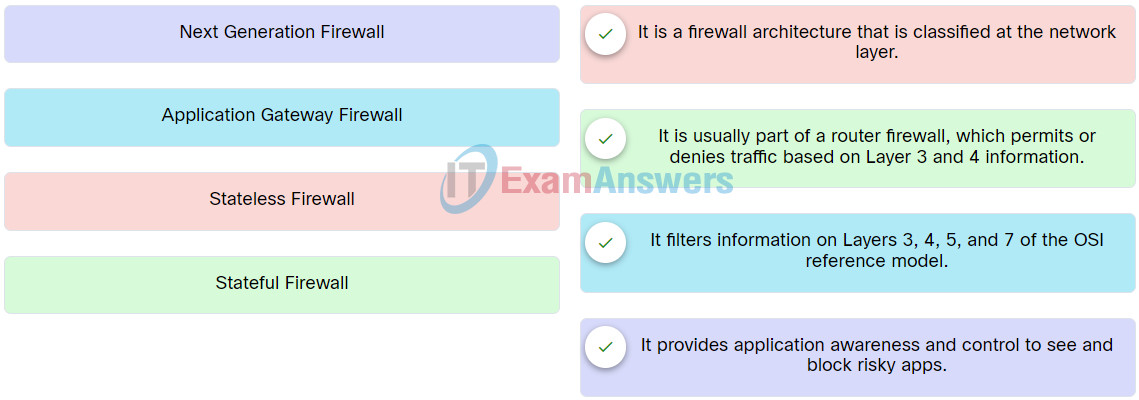
Network Support and Security Course Final Exam Q21
171. What is one of the safeguards according to the third dimension of the cybersecurity cube?
- accountability
- confidentiality
- integrity
- technology
172. Which type of static route creates a gateway of last resort?
- standard static route
- floating static route
- summary static route
- default static route
173. What is the interface ID of the IPv6 address 2001:DB8::1000:A9CD:47FF:FE57:FE94/64?
- 47FF:FE57:FE94
- FE57:FE94
- A9CD:47FF:FE57:FE94
- 1000:A9CD:47FF:FE57:FE94
- FE94
174. Refer to the exhibit. A technician is attempting to map the local network using CDP. According to the output shown, which two statements are true about router Branch01? (Choose two.)
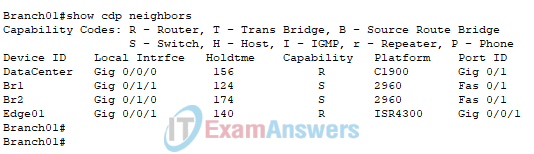
- Router Branch01 is directly connected to port Gi0/1/0 on device BR2.
- Router Branch01 is directly connected to three Cisco switches.
- Router Branch01 is directly connected to another router named DataCenter.
- Router Branch01 port Gi0/0/0 is directly connected to a Layer 2 switch.
- Router Branch01 is directly connected to port Fa0/1 on device BR1.
175. A technician receives a trouble ticket from a user reporting that a website is no longer accessible. What two questions would the technician ask to narrow down the potential problem? (Choose two.)
- Could you access this web site previously from this device?
- What model computer are you using to access this site?
- What operating system is installed on your computer?
- Do you remember your password to this web site?
- Can you access other web sites from this computer browser?
176. Which type of cloud service is a user accessing when using Google Sheets to create a financial report?
- SaaS
- FaaS
- IaaS
- PaaS
177. What would be the interface ID of an IPv6 enabled interface with a MAC address of 1C-6F-65-C2-BD-F8 when the interface ID is generated by using the EUI-64 process?
- 1E6F:65FF:FEC2:BDF8
- C16F:65FF:FEC2:BDF8
- 0C6F:65FF:FEC2:BDF8
- 106F:65FF:FEC2:BDF8
178. Consider the following command:
ip route 192.168.10.0 255.255.255.0 10.10.10.2 5
Which route would have to go down in order for this static route to appear in the routing table?
- a default route
- a static route to the 192.168.10.0/24 network
- an EIGRP-learned route to the 192.168.10.0/24 network
- an OSPF-learned route to the 192.168.10.0/24 network
179. A technician has been asked to develop a physical topology for a network that provides a high level of availability. Which physical topology requires that every node is attached to every other node on the network?
- hierarchical
- bus
- ring
- mesh
- star
180. Refer to the exhibit. The image shows a firewall filtering network traffic based on information at highlighted OSI model Layers. Which type of firewall is represented?
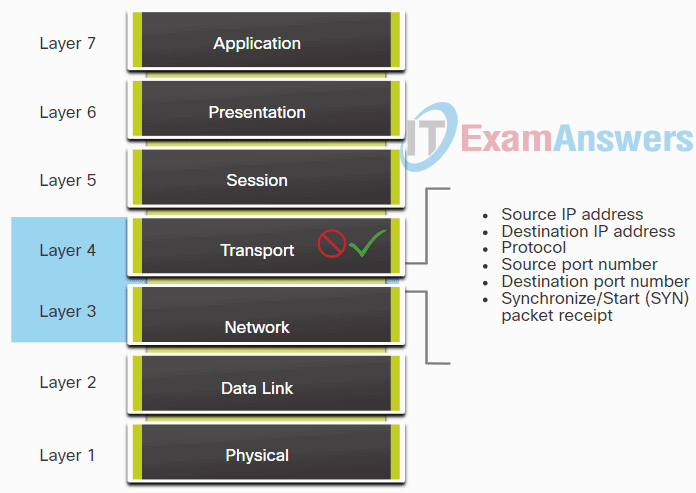
Network Support and Security Course Final Exam Q23
- Next Generation
- Application Gateway
- Stateful
- Packet filtering (stateless)
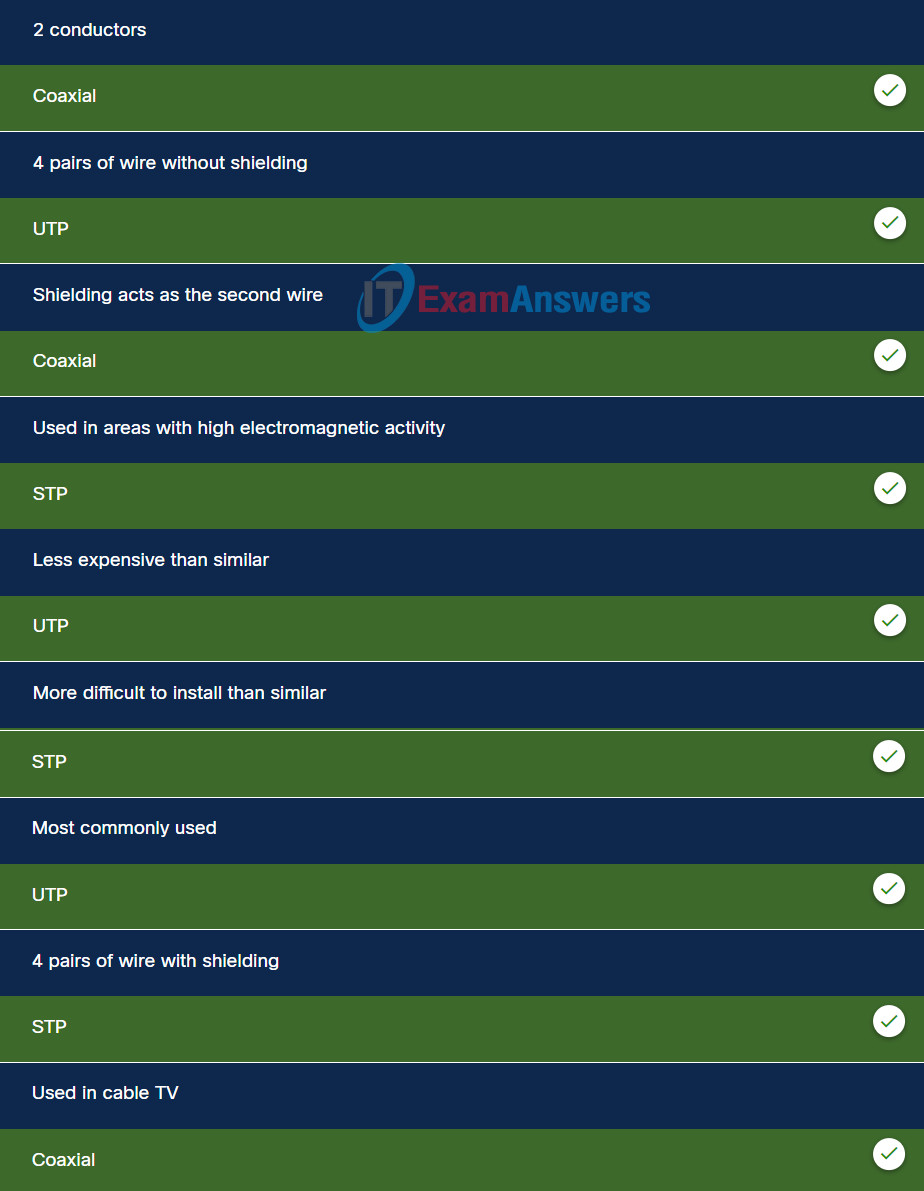
181. Match the characteristic with the appropriate copper media.
182. What security benefit is provided by SSH?
- protection from threat actors deciphering remote access session data.
- protection from viruses and malware for endpoints.
- protection from malicious data reaching servers and clients.
- protection from DoS attacks against routers and Layer 3 switches.
183. What information can a technician obtain by running the tracert command on a Windows PC?
- the available routes in the PC routing table to reach a destination.
- the available bandwidth between the PC and a destination.
- the verification of Layer 2 connectivity between the PC and a destination.
- layer 3 hops a packet crosses as it travels to a destination.
184. What are the two characteristics of a site-to-site VPN? (Choose two.)
- The client initiates the VPN connection.
- Traffic between clients and the VPN gateway is automatically encrypted.
- A VPN gateway device is needed at both ends of the tunnel.
- The VPN is established between the client PC and a VPN gateway.
- Clients have no awareness of the VPN.
185. What type of connection is used when a teleworker must have secure access to devices and services located on an enterprise network?
- RTP
- VPN
- HTTP
- FTP
186. The IT department of a high school is developing cybersecurity policies. One policy item regulates the blocking of obtaining movies and sounds through peer-to-peer networks on school computers. Which two user threats does this policy address? (Choose two.)
- data theft
- unauthorized downloads and media
- no awareness of security
- poorly enforced security policies
- unauthorized websites
187. A penetration test carried out by an organization identified a backdoor on the network. What action should the organization take to find out if their systems have been compromised?
- Look for policy changes in Event Viewer.
- Look for unauthorized accounts.
- Scan the systems for viruses.
- Look for usernames that do not have passwords.
188. What non-technical method could a cybercriminal use to gather sensitive information from an organization?
- ransomware
- pharming
- social engineering
- man-in-the-middle
189. What type of attack occurs when data goes beyond the memory areas allocated to an application?
- SQL injection
- RAM spoofing
- Buffer overflow
- RAM injection
190. A network administrator needs to segment the local area network to isolate traffic from different departments so that network permissions unique to each department can be implemented. Which network topology provides a solution to achieve the objective?
- MAN
- VLAN
- WLAN
- PAN
191. Which output of a ping command can determine two important pieces of information? (Choose two.)
- the round-trip time for the request to reach the destination and the response to return
- the IP address of the gateway router that connects the source device to the internet
- the number of domains that the packet travels through from the source to the destination
- which network device is causing delays in delivering the packet to the destination IP address
- whether or not the destination IP address is reachable through the network
192. Which protocol is used by network management systems to collect data from network devices?
- SNMP
- TFTP
- SMTP
- RDP
Networking Essentials 2.0: Course Final Exam
1. Using default settings, what is the next step in the switch boot sequence after the IOS loads from flash?
- Search for a backup IOS in ROM.
- Load the bootstrap program from ROM.
- Load the running-config file from RAM.
- Perform the POST routine.
- Locate and load the startup-config file from NVRAM.
4. What is an inherent security vulnerability of SSID broadcasting?
- It sends traffic unencrypted between the wireless access point and the client.
- It broadcasts the identity of the network.
- It allows unauthenticated access to the wireless network.
- It allows any host to join the wireless network.
5. A network administrator installs a network device that focuses on interconnecting independent local networks. At which layer of devices does this technology reside?
- access
- internet
- distribution
- core
6. What are three characteristics of multicast transmission? (Choose three.)
- Multicast transmission can be used by routers to exchange routing information.
- The range of 224.0.0.0 to 224.0.0.255 is reserved to reach multicast groups on a local network.
- The source address of a multicast transmission is in the range of 224.0.0.0 to 224.0.0.255.
- Multicast messages map lower layer addresses to upper layer addresses.
- Computers use multicast transmission to request IPv4 addresses.
- A single packet can be sent to a group of hosts.
7. What are two common media used in networks? (Choose two.)
- fiber
- wood
- nylon
- water
- copper
8. Refer to the exhibit. Which router port connects to the modem provided by the service provider?
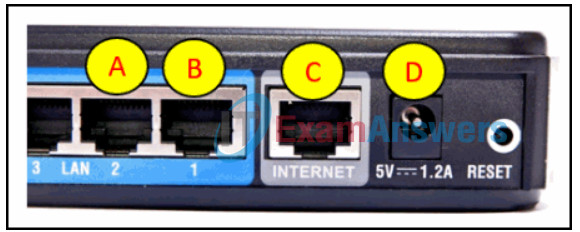
- C
- A
- B
- D
9. A consumer places a smartphone close to a pay terminal at a store and the shopping charge is successfully paid. Which type of wireless technology was used?
- 3G
- Bluetooth
- NFC
- Wi-Fi
11. What type of technology converts analog voice signals into digital data?
- SMTP
- VoIP
- POP3
- SNMP
12. What are two wiring schemes defined by the TIA/EIA organization for Ethernet installation in homes and businesses? (Choose two.)
- T568B
- RJ-45
- STP
- UTP
- T568A
14. What is the effect of setting the security mode to WEP on a small wireless router?
- It translates an internal address or group of addresses into an outside, public address.
- It encrypts data between the wireless client and the access point.
- It allows the access point to inform clients of its presence.
- It translates IP addresses into easy-to-remember domain names.
- It identifies the wireless LAN.
15. A network administrator issues the Switch(config)# Interface FastEthernet 0/1 command on a Cisco switch. Which term is used to describe the “0/1” part in the command?
- command
- hot key
- keyword
- argument
16. What is the purpose of the subnet mask in conjunction with an IP address?
- to identify whether the address is public or private
- to mask the IP address to outsiders
- to uniquely identify a host on a network
- to determine the subnet to which the host belongs
17. If the default gateway is configured incorrectly on a host, what is the impact on communications?
- The host is unable to communicate on the local network.
- The host is unable to communicate with hosts on remote networks.
- The host is unable to communicate with hosts on both the local and remote networks.
- The host cannot get an IP address from the DHCP server.
18. What is a characteristic of a peer-to-peer application?
- The resources required for the application are centralized.
- Both devices initiate a three-way handshake to determine who is initiating the communication.
- Each device using the application provides a user interface and runs a background service.
- Each device can act both as a client and a server, but not simultaneously.
19. In software defined network architecture, what function is removed from network devices and performed by an SDN controller?
- application policies
- data plane
- security
- control plane
21. Which network migration technique encapsulates IPv6 packets inside IPv4 packets to carry them over IPv4 network infrastructures?
- translation
- dual-stack
- tunneling
- encapsulation
22. Which two types of interference may affect the data throughput on UTP cables? (Choose two.)
- moisture
- EMI
- crosstalk
- temperature
- noise
24. Match the type of malware with the definition.
25. Which statement correctly describes data transmission at the transport layer?
- Segmentation is provided by the window size field when the TCP protocol is used.
- Segmentation is provided by sequence numbers when UDP is used.
- Retransmission of lost packets is provided by both TCP and UDP.
- A single datagram can include both a TCP and a UDP header.
- Both UDP and TCP use port numbers.
26. What are two benefits of using a layered network model? (Choose two.)
- It speeds up packet delivery.
- It prevents technology in one layer from affecting other layers.
- It ensures a device at one layer can function at the next higher layer.
- It assists in protocol design.
- It prevents designers from creating their own model.
27. Which two devices are considered end devices? (Choose two.)
- switch
- hub
- laptop
- printer
- router
28. Which three attacks exploit human behavior? (Choose three.)
- pretexting
- brute force
- phishing
- zombies
- vishing
- malware
29. A user is setting up a home wireless network. Which type of device must the user have in order to establish the wireless network and provide access to the internet for multiple home devices?
- hub
- wireless router
- switch
- patch panel
30. Match the protocol with the function.
31. What are two features of protocols used within the TCP/IP protocol stack? (Choose two.)
- The Internet Layer IP protocol has built in mechanisms for ensuring the reliable transmission and receipt of data.
- The same Transport Layer source port is used for all of the tabs opened at the same time within a web browser.
- UDP is used when an application must be delivered as quickly as possible and some loss of data can be tolerated.
- TCP and UDP destination port numbers are dynamically generated by the sending device in order to track the responses to requests.
- TCP mechanisms retransmit data when an acknowledgment is not received from the destination system within a set period of time.
33. Which command can an administrator execute to determine what interface a router will use to reach remote networks?
- show protocols
- show interfaces
- show ip route
- show arp
34. While a network security product is being deployed, a customizable list of allowable protocols is shown. Which three protocols should be allowed to provide for the use of email on a network? (Choose three.)
- POP3
- Telnet
- IMAP4
- TFTP
- SMTP
- HTTP
- DNS
36. A client device on an Ethernet segment needs an IP address in order to communicate on the network. A DHCP server with IP address 192.168.1.1 has been configured and enabled on the network. How will a client device obtain a usable IP address for this network?
- Send a DHCPACK packet to the default gateway address.
- Use a statically configured IP address from the pool of IP addresses that is offered by the DHCP server.
- Send a DHCPDISCOVER message to physical address FF-FF-FF-FF-FF-FF.
- Send a DHCPREQUEST packet to IP address 255.255.255.255.
37. Which two files, if found, are copied into RAM as a router with the default configuration register setting boots up? (Choose two.)
- IOS image file
- running configuration
- POST diagnostics
- startup configuration
39. A network administrator establishes a connection to a switch via SSH. What characteristic uniquely describes the SSH connection?
- on-site access to a switch through the use of a directly connected PC and a console cable
- remote access to the switch through the use of a telephone dialup connection
- direct access to the switch through the use of a terminal emulation program
- remote access to a switch where data is encrypted during the session
- out-of-band access to a switch through the use of a virtual terminal with password authentication
40. Using a systematic troubleshooting approach, a help desk technician suspects a problem at Layer 3 of the OSI model. In gathering information, which two questions are associated with Layer 3? (Choose two.)
- Does a browser connection to www.cisco.com work?
- Is there a link light on the network card?
- Is the PC configured for DHCP?
- Is the network cable plugged in?
- From the PC, is the default gateway reachable using the ping command?
41. During a move, employee workstations were disconnected from the network and reconnected in new offices. However, after the move a few workstations cannot get a valid IP address. What should be checked first to identify the root cause of the problem?
- Install all software updates.
- Check the operation status of the DHCP server.
- Make sure the cables are functional and properly plugged.
- Test if these workstations can ping the default gateway.
42. Which solution allows external users to access only an internal FTP server on a private network?
- dynamic NAT
- port forwarding
- NAT with overload
- static NAT
43. Which type of address does a switch use to build the MAC address table?
- destination MAC address
- source MAC address
- source IP address
- destination IP address
45. Which factor does not influence throughput?
- the amount of data that is being sent and received on the connection
- the type of data that is being transmitted
- the operating system that is used by end devices
- the latency that is created by the number of network devices encountered between source and destination
46. A DHCP server is used to assign IP addresses dynamically to the hosts on a network. The address pool is configured with 192.168.10.0/24. There are 3 printers on this network that need to use reserved static IP addresses from the pool. How many IP addresses in the pool are left to be assigned to other hosts?
- 252
- 254
- 253
- 251
47. What is an advantage of using standards to develop and implement protocols?
- Different manufacturers are free to apply different requirements when implementing a protocol.
- A particular protocol can only be implemented by one manufacturer.
- Standards provide flexibility for manufacturers to create devices that comply with unique requirements.
- Products from different manufacturers can interoperate successfully.
48. An intruder tries a large number of possibilities in rapid succession to guess a password. As a result, other users on the network are locked out. What type of attack has occurred?
- brute force
- DDoS
- SYN flooding
- ping of death
49. Match the commands to the correct actions.
50. Which type of access is secured on a Cisco router or switch with the enable secret command?
- console line
- virtual terminal
- AUX port
- privileged EXEC
51. Which type of device filtering can be enabled on some wireless access points or wireless routers?
- IP address
- user ID
- authentication
- MAC address
52. A host needs to reach another host on a remote network, but the ARP cache has no mapping entries. To what destination address will the host send an ARP request?
- the broadcast MAC address
- the subnet broadcast IP address
- the unicast IP address of the remote host
- the unicast MAC address of the remote host
53. When configuring SSH on a router to implement secure network management, a network engineer has issued the login local and transport input ssh line vty commands. What three additional configuration actions have to be performed to complete the SSH configuration? (Choose three.)
- Configure the correct IP domain name.
- Manually enable SSH after the RSA keys are generated.
- Generate the asymmetric RSA keys.
- Create a valid local username and password database.
- Configure role-based CLI access.
- Set the user privilege levels.
54. A computer has to send a packet to a destination host in the same LAN. How will the packet be sent?
- The packet will be sent to the default gateway first, and then, depending on the response from the gateway, it may be sent to the destination host.
- The packet will be sent directly to the destination host.
- The packet will first be sent to the default gateway, and then from the default gateway it will be sent directly to the destination host.
- The packet will be sent only to the default gateway.
55. Refer to the exhibit. What three facts can be determined from the viewable output of the show ip interface brief command? (Choose three.)
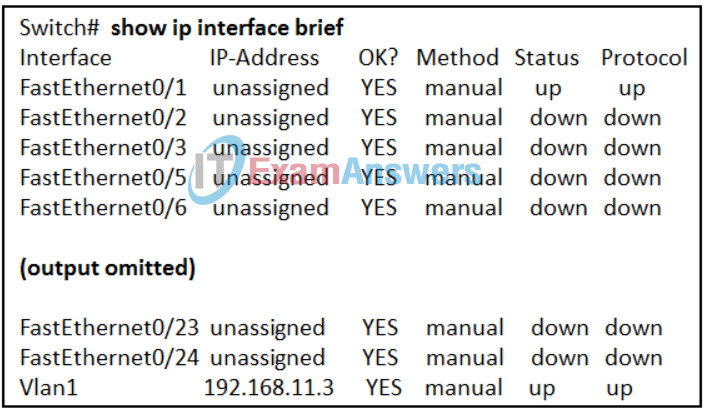
- Two devices are attached to the switch.
- The switch can be remotely managed.
- One device is attached to a physical interface.
- The default SVI has been configured.
- Two physical interfaces have been configured.
- Passwords have been configured on the switch.
56. Which two statements describe characteristics of network addresses? (Choose two.)
- DHCP is used to dynamically assign both MAC and IP addresses to devices connected to the network.
- The MAC address of a device will change when that device moves from one Ethernet network to another.
- A MAC address is also referred to as a physical address because it is permanently embedded on the NIC.
- A statically assigned IP address will be valid on any network to which the device connects.
- A valid public IPv4 or IPv6 address is needed in order for devices to communicate over the internet.
57. When troubleshooting network problems, where would a network administrator find the configuration information, such as the computer names and the IP addresses that are used?
- DNS server
- physical topology diagram
- DHCP server
- logical topology diagram
58. A student is uploading files from a phone to a server on another network. Which layer of the TCP/IP model is responsible for providing an addressing scheme to transmit the data between the devices?
- network access
- internet
- transport
- application
59. If the default gateway is configured incorrectly on the host, what is the impact on communications?
- The host can communicate with other hosts on the local network, but is unable to communicate with hosts on remote networks.
- The host can communicate with other hosts on remote networks, but is unable to communicate with hosts on the local network.
- The host is unable to communicate on the local network.
- There is no impact on communications.
60. A customer calls the help line to report a computer problem. The help line technician responds and works with the customer for some time. However, the technician cannot identify the root cause of the problem. What should the technician do to help the customer?
- Suggest that the customer visit the support website for more detailed information.
- Tell the customer that a replacement computer will be shipped immediately.
- Ask for the email address of the customer in order to send all the support documents for the computer.
- Tell the customer that a ticket is created and another technician will contact the user soon.