Checkpoint Exam: Cisco Devices and Troubleshooting Network Issues: Network Addressing and Basic Troubleshooting Module 7 – 8 Checkpoint Exam Answers (NABT)
1. After several configuration changes are made to a router, the copy running-configuration startup-configuration command is issued. Where will the changes be stored?
- NVRAM
- RAM
- flash
- ROM
2. A technician is troubleshooting a network device and suspects there might be a duplex mismatch. What could cause a duplex mismatch?
- interface misconfiguration
- data corruption
- interconnection of unlike devices
- auto-MDIX detection failure
3. Which statement describes the half-duplex mode of data transmission?
- Data that is transmitted over the network can only flow in one direction.
- Data that is transmitted over the network flows in both directions at the same time.
- Data that is transmitted over the network flows in one direction to many different destinations simultaneously.
- Data that is transmitted over the network flows in one direction at a time.
4. What is the first action in the boot sequence when a switch is powered on?
- load boot loader software
- load a power-on self-test program
- load the default Cisco IOS software
- low-level CPU initialization
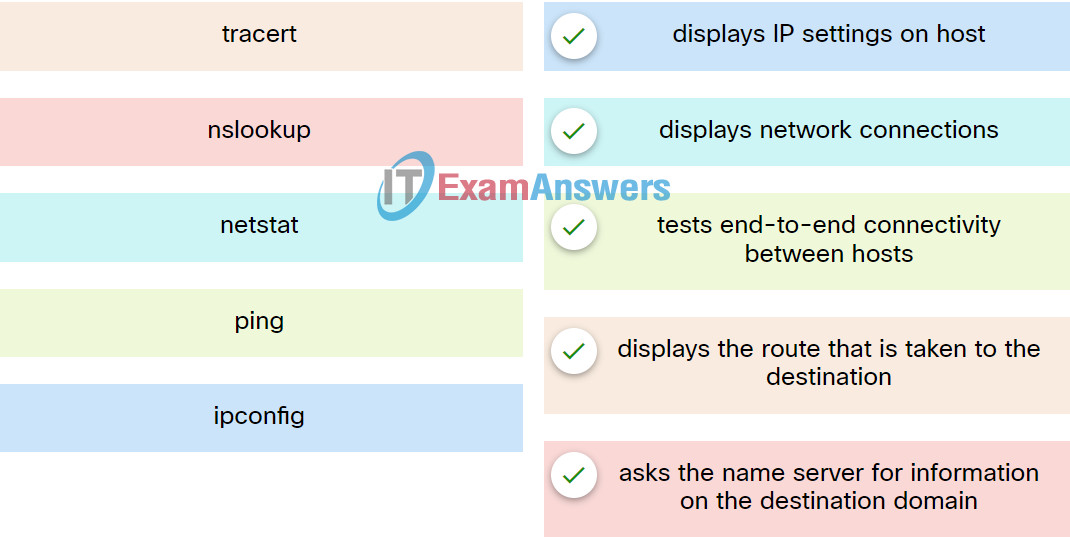
5. Match the command to the function.
6. Which two statements are true about half-duplex and full-duplex communications? (Choose two.)
- Half-duplex is supported on Gigabit Ethernet links.
- Full duplex enables transmission in only one direction at a time.
- Half duplex links do not experience collisions.
- Full duplex allows both ends to transmit and receive simultaneously.
- Full duplex increases the effective bandwidth.
7. Which two access methods can be used for in-band configuration of a Cisco device? (Choose two.)
- CLI
- AUX
- console
- SSH
- Telnet
8. What is required for a network administrator to perform out-of-band management tasks on a Cisco device?
- a computer directly connected to the console port of the device
- an active network connection available to the device
- a valid IP address configured on VLAN 1
- SSH enabled and functional on the device
9. A network technician is attempting to connect an older device to a FastEthernet port on a Cisco switch. The technician has manually configured the device to full-duplex mode in order to enhance the network performance of the device. However, when the device is attached to the network, performance degrades and excessive collisions are detected on the switch. What is the likely cause of this problem?
- The host is configured in a different subnet from the subnet of the switch.
- There is a duplex mismatch between the device and switch port.
- The switch port is running at a different speed from the speed of the device NIC.
- The host has been configured with a default gateway that is different from that of the switch.
10. A router boots and enters setup mode. What is the reason for this?
- The configuration file is missing from NVRAM.
- The POST process has detected hardware failure.
- Cisco IOS is missing from flash memory.
- The IOS image is corrupt.
11. Local workstations are unable to access web pages located on the www.cisco.com web server. Pings from the workstations to the server using the ping www.cisco.com command are successful. What settings should the administrator check to determine the cause of the problem?
- firewall settings
- DNS server settings
- IP address settings
- MAC address settings
12. Users in a recently installed wireless network are complaining of slow data transfer and frequent loss of connectivity. The technician checks that the wireless security is correctly implemented, and there is no evidence of unauthorized users on the network. Which two problems might the technician suspect? (Choose two.)
- The wireless signal is too weak.
- The DHCP server is faulty.
- The antenna on the access point is too powerful.
- The network passwords need to be reissued to the users.
- There is interference from outside sources.
13. Refer to the exhibit. The command output is from a wireless DHCP host connected to a Linksys integrated router. What can be determined from the output?
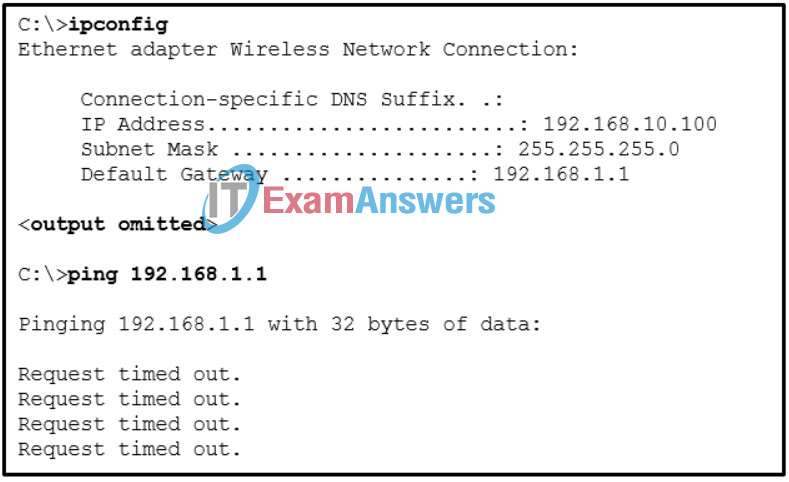
- A new wireless NIC needs to be installed.
- There is a DNS problem.
- The DHCP configuration needs to be checked.
- The connection to the SSID needs to be verified.
- An incorrect cable is being used between the host and the router.
14. A network technician enters the command ipconfig /release followed by ipconfig /renew in order to ensure that the DHCP IP configuration on a workstation is updated. However, the workstation does not receive a valid IP configuration for the network. Which two problems may exist on the network? (Choose two.)
- There is no network connectivity to the DHCP server.
- There is a DHCP server issue.
- The DHCP lease time is misconfigured.
- The ipconfig /all command must be issued to restore all IP configurations.
- The gateway router address needs to be updated.
15. Which step in the troubleshooting process describes steps that were taken and repair processes that were performed previously?
- documentation of the problem and its solution
- preparation of a plan of action
- identification of the problem
- implementation of the solution
16. A medium-sized company uses APs, WLCs, and laptops for employee workstations. An employee reports the inability to connect to the Internet. A technician verifies that other workstations can successfully connect to the Internet. What are two possible reasons for the problem? (Choose two.)
- The workstation is out of range.
- A default gateway is improperly configured on the AP.
- A bad cable exists between the client and the WLC.
- The wireless client is not configured for DHCP.
- The AP does not have power.
17. A user has taken a personal laptop to work. The laptop is unable to discover the name of the office wireless network. What are two potential causes of this problem? (Choose two.)
- The wireless router is set to mixed mode.
- The laptop has not received an IP address from the wireless router.
- The network does not support the wireless protocol in use by the laptop.
- The wireless router is not broadcasting the SSID.
- The laptop must be configured with the office workgroup name.
18. Refer to the exhibit. A network engineer is troubleshooting why PC1 cannot communicate with hosts in other networks. What is the problem?
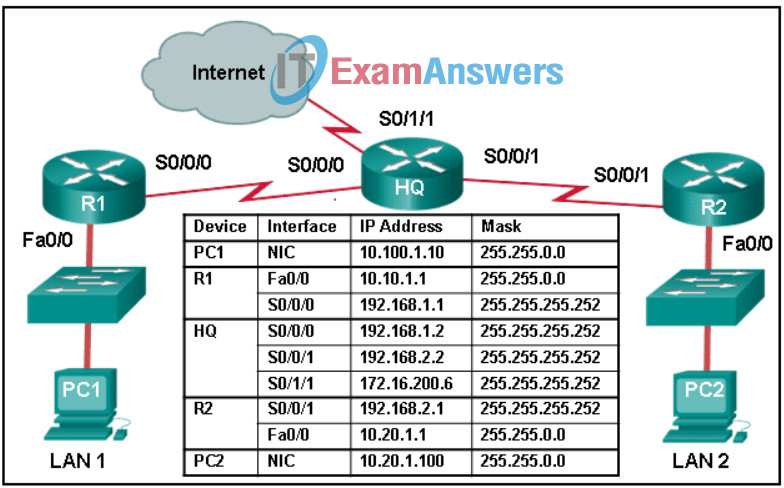
- The subnet mask that is configured on PC1 is the same as the mask that is configured on the router R1 interface.
- The IP address that is configured on PC1 is in a different network than the gateway address on router R1.
- A default route has not been configured on router R1.
- A default gateway IP address of 10.20.1.1 needs to be configured on PC1.
19. Which statement describes the ping and tracert commands?
- Ping shows whether the transmission is successful; tracert does not.
- Tracert shows each hop, while ping shows a destination reply only.
- Both ping and tracert can show results in a graphical display.
- Tracert uses IP addresses; ping does not.
20. A laptop cannot connect to a wireless access point. Which two troubleshooting steps should be taken first? (Choose two.)
- Ensure that the wireless SSID is chosen.
- Ensure that the correct network media is selected.
- Ensure that the NIC is configured for the proper frequency.
- Ensure that the laptop antenna is attached.
- Ensure that the wireless NIC is enabled.
21. What characteristic of store-and-forward switching is important when a network supports voice over IP (VoIP)?
- It stores only the first 64 bytes of the frame.
- It is required for QoS analysis in converged networks to prioritize traffic.
- It offers a lower level of latency compared to the fragment-free switching method.
- It computes the CRC based on the first 64 bits of the frame.
22. What type of Ethernet cable would be used to connect one switch to another switch when neither switch supports the auto-MDIX feature?
- straight-through
- rollover
- crossover
- coaxial
23. Following default settings, what is the next step in the router boot sequence after the IOS loads from flash?
- Load the running-config file from RAM.
- Load the bootstrap program from ROM.
- Perform the POST routine.
- Locate and load the startup-config file from NVRAM.
