Assessment EWAN Final – CCNA 4 Exploration: Accessing the WAN (Version 4.0)
1. Which two statements are true about creating and applying access lists? (Choose two.)
- There is an implicit deny at the end of all access lists.
- One access list per port, per protocol, per direction is permitted.
- Access list entries should filter in the order from general to specific.
- The term “inbound” refers to traffic that enters the network from the router interface where the ACL is applied.
- Standard ACLs should be applied closest to the source while extended ACLs should be applied closest to the destination.
2. Refer to the exhibit. Based on the output as shown, which two statements correctly define how the router will treat Telnet traffic that comes into interface FastEthernet 0/1? (Choose two).
- Telnet to 172.16.10.0/24 is denied.
- Telnet to 172.16.20.0/24 is denied.
- Telnet to 172.16.0.0/24 is permitted.
- Telnet to 172.16.10.0/24 is permitted.
- Telnet to 172.16.20.0/24 is permitted.
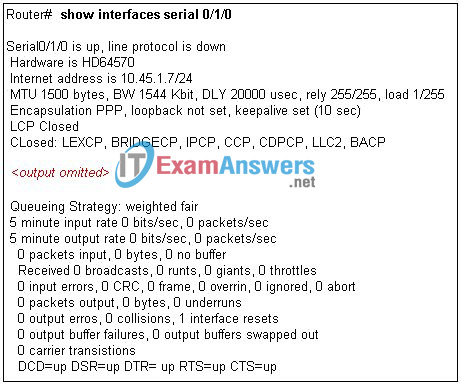
3. Refer to the exhibit. A technician issues the show interface s0/0/0 command on R1 while troubleshooting a network problem. What two conclusions can be determined by from the output shown? (Choose two.)
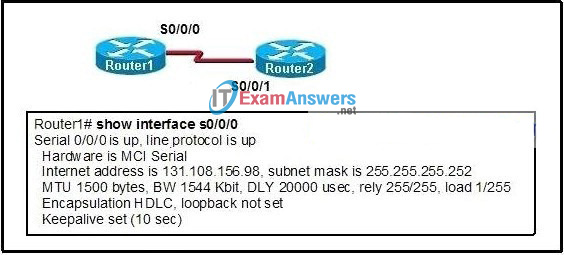
- The bandwidth has been set to the value of a T1 line.
- This interface should be configured for PPP encapsulation.
- There is no failure indicated in an OSI Layer 1 or Layer 2.
- The physical connection between the two routers has failed.
- The IP address of S0/0/0 is invalid, given the subnet mask being used.
4. A company is looking for a WAN solution to connect its headquarters site to four remote sites. What are two advantages that dedicated leased lines provide compared to a shared Frame Relay solution? (Choose two.)
- reduced jitter
- reduced costs
- reduced latency
- the ability to burst above guaranteed bandwidth
- the ability to borrow unused bandwidth from the leased lines of other customers
5. Which three physical network problems should be checked when a bottom-up troubleshooting approach has been chosen to troubleshoot network performance? (Choose three.)
- cable connectivity
- high collision counts
- STP failures and loops
- address mapping errors
- high CPU utilization rates
- excess packets that are filtered by the firewall
6. A network administrator determines that falsified routing information is propagating through the network. What action can be used to address this threat?
- Update the IOS images.
- Change console passwords.
- Employ end-user authentication.
- Configure routing protocol authentication.
7. Refer to the exhibit. A host connected to Fa0/0 is unable to acquire an IP address from this DHCP server. The output of the debug ip dhcp server command shows “DHCPD: there is no address pool for 192.168.1.1”. What is the problem?
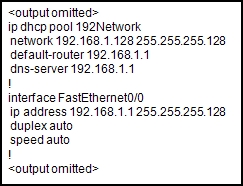
- The 192.168.1.1 address has not been excluded from the DHCP pool.
- The pool of addresses for the 192Network pool is incorrect.
- The default router for the 192Network pool is incorrect.
- The 192.168.1.1 address is already configured on Fa0/0.
8. Which statement is true about wildcard masks?
- Inverting the subnet mask will always create the wildcard mask.
- The wildcard mask performs the same function as a subnet mask.
- A network or subnet bit is identified by a “1” in the wildcard mask.
- IP address bits that must be checked are identified by a “0” in the wildcard mask.
9. Refer to the exhibit. Router RT is not receiving routing updates from router RTA. What is causing the problem?
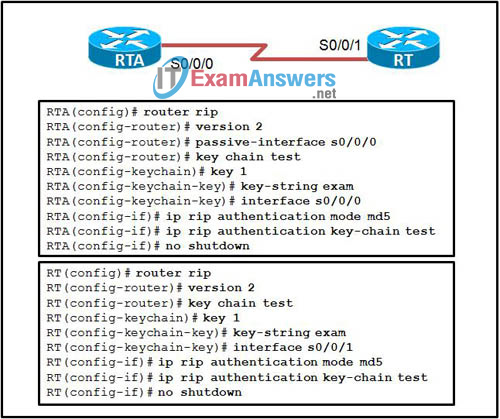
- The ip rip authentication key-chain command specifies exam rather than test.
- The name of the keystring is not the name of the neighboring router.
- The key chains are given the same name on both routers.
- The passive-interface command was issued for RTA.
10. What are two major characteristics of a worm? (Choose two.)
- exploits known vulnerabilities
- attaches itself to another program
- executed by a predefined time or event
- masquerades as an accepted program
- copies itself to the host and selects new targets
11. Which two protocols in combination should be used to establish a link with secure authentication between a Cisco and a non-Cisco router? (Choose two.)
- HDLC
- PPP
- SLIP
- PAP
- CHAP
12. At what physical location does the responsibilty for a WAN connection change from the user to the service provider?
- demilitarized zone (DMZ)
- demarcation point
- local loop
- cloud
13. A light manufacturing company wishes to replace its DSL service with a non-line-of-sight broadband wireless solution that offers comparable speeds. Which solution should the customer choose?
- Wi-Fi
- satellite
- WiMAX
- Metro Ethernet
14. Refer to the exhibit. The corporate network that is shown has been assigned network 172.16.128.0/19 for use at branch office LANs. If VLSM is used, what mask should be used for addressing hosts at Branch4 with minimal waste from unused addresses?
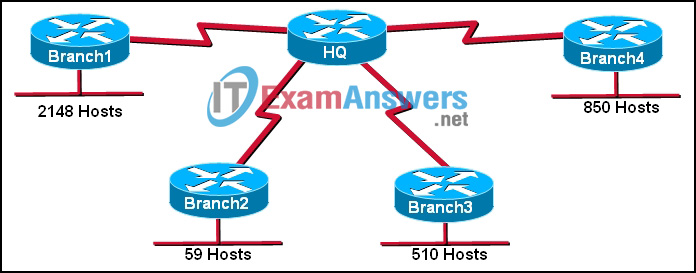
- /19
- /20
- /21
- /22
- /23
- /24
15. Refer to the exhibit. From the output of the show interfaces and ping commands, at which layer of the OSI model is a fault indicated?
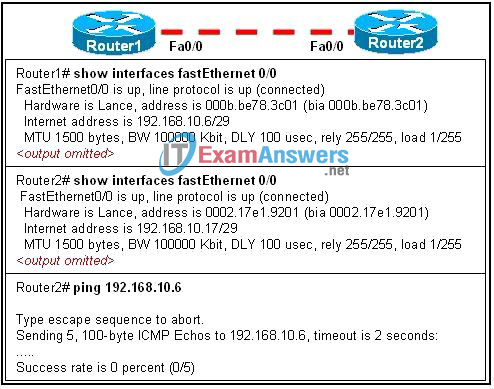
- application
- transport
- network
- data link
- physical
16. When NAT is in use, what is used to determine the addresses that can be translated on a Cisco router?
- access control list
- routing protocol
- inbound interface
- ARP cache
17. Refer to the exhibit. Which VLAN will carry untagged traffic on FastEthernet 0/1?

- VLAN 1
- VLAN 2
- VLAN 11
- VLAN 12
- VLAN 30
- VLAN 999
18. An issue of response time has recently arisen on an application server. The new release of a software package has also been installed on the server. The configuration of the network has changed recently. To identify the problem, individuals from both teams responsible for the recent changes begin to investigate the source of the problem. Which statement applies to this situation?
- Scheduling will be easy if the network and software teams work independently.
- It will be difficult to isolate the problem if two teams are implementing changes independently.
- Results from changes will be easier to reconcile and document if each team works in isolation.
- Only results from the software package should be tested as the network is designed to accommodate the proposed software platform.
19. While configuring a router using RIPng and dual-stack technology with IPv4 and IPv6, the administrator receives an error message when inputting IPv4 routes. What could cause the error message?
- IPv4 is not compatible with RIPng
- RIPng is incompatible with dual-stack technology.
- The router interfaces have been configured with incorrect addresses.
- When IPv4 and IPv6 are configured on the same interface, all IPv4 addresses are shut down in favor of the newer technology.
20. Refer to the exhibit. RIPv2 has been configured on all routers in the network. Routers R1 and R3 have not received any RIP routing updates. What will fix the issue?
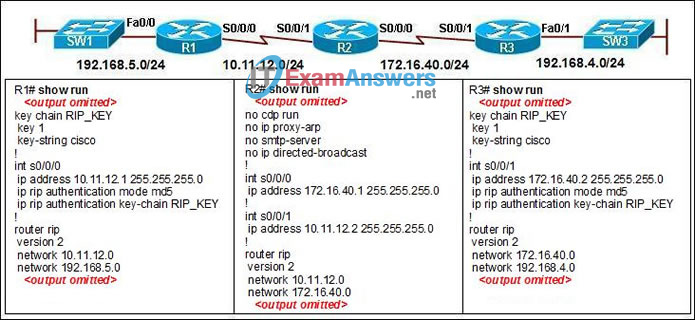
- Enable RIP authentication on R2.
- Issue the ip directed-broadcast command on R2.
- Change the subnet masks to 10.11.12.0/8 and 172.16.40.0/16 on R2.
- Enable CDP on R2 so that the other routers will receive routing updates.
21. What is the result when the command permit tcp 10.25.132.0 0.0.0.255 any eq smtpis added to a named access control list and applied on the inbound interface of a router?
- TCP traffic with a destination to the 10.25.132.0/24 is permitted.
- Only Telnet traffic is permitted to the 10.24.132.0/24 network
- Traffic from 10.25.132.0/24 is permitted to anywhere on using any port.
- Traffic using port 25 from the 10.25.132.0/24 is permitted to all destinations.
22. Refer to the exhibit. Which statement correctly describes how Router1 processes an FTP request packet that enters interface S0/0/0, and is destined for an FTP server at IP address 172.16.1.5?
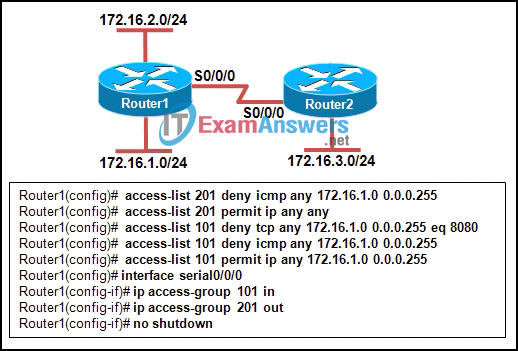
- The router matches the incoming packet to the statement that is created by access-list 201 permit ip any any command and allows the packet into the router.
- The router reaches the end of ACL 101 without matching a condition and drops the packet because there is no statement that was created by access-list 101 permit ip any any command.
- The router matches the incoming packet to the statement that was created by theaccess-list 101 permit ip any 172.16.1.0 0.0.0.255 command, ignores the remaining statements in ACL 101, and allows the packet into the router.
- The router matches the incoming packet to the statement that was created by theaccess-list 201 deny icmp 172.16.1.0 0.0.0.255 any command, continues comparing the packet to the remaining statements in ACL 201 to ensure that no subsequent statements allow FTP, and then the router drops the packet.
23. Refer to the exhibit. A network administrator is considering updating the IOS on Router1. What version of IOS is currently installed on Router1?
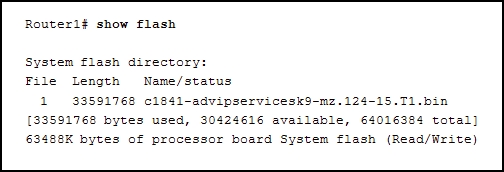
- 1
- 12.4
- 15
- 1841
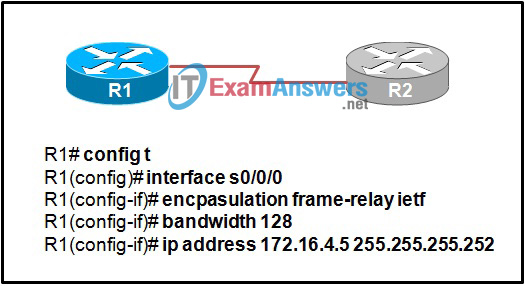
24. Refer to the exhibit. A network administrator is attempting to configure a Frame Relay network. The administrator enters the commands as shown in the exhibit on R2, but the Frame Relay PVCs are inactive. What is the problem?
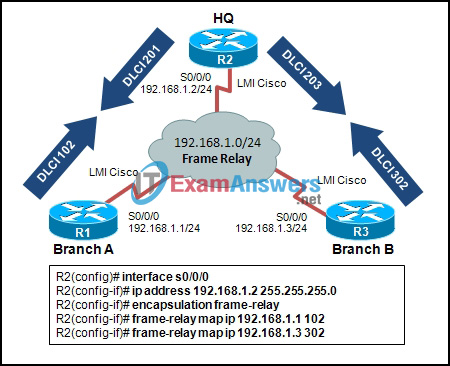
- The incorrect DLCI numbers are being configured on R2.
- The S0/0/0 interface on R2 needs to be point-to-point.
- The frame-relay map commands are missing the cisco keyword at the end.
- A single router interface cannot connect to more than one Frame Relay peer at a time.
25. Refer to the exhibit. Which data transmission technology is being represented?
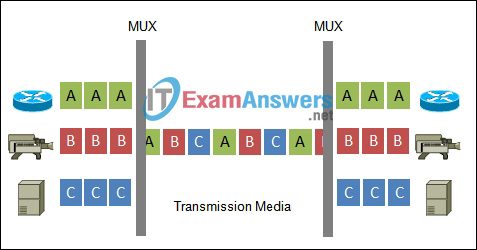
- TDM
- PPP
- HDLC
- SLIP
26. Refer to the exhibit. Which configuration command would result in the output in the exhibit?
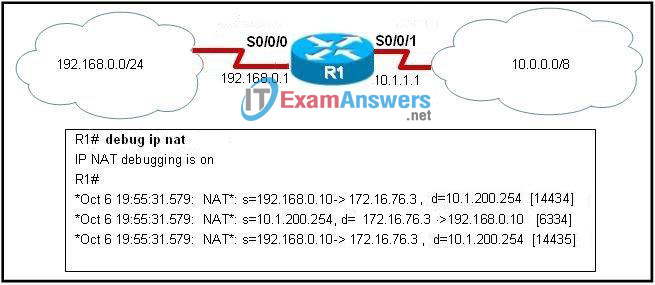
- ip nat inside source static 10.1.200.254 172.16.76.3
- ip nat inside source static 10.1.200.254 192.168.0.10
- ip nat inside source static 172.16.76.3 10.1.200.254
- ip nat inside source static 172.16.76.3 192.168.0.10
- ip nat inside source static 192.168.0.10 172.16.76.3
- ip nat inside source static 192.168.0.10 10.1.200.254
27. Refer to the exhibit. A technician is teaching a trainee to interpret the results of various Frame Relay troubleshooting commands. What conclusion can be drawn from the output that is shown?
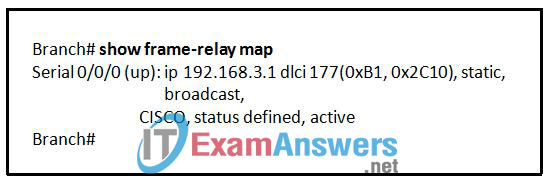
- Neighboring routers should use DLCI 177 to reach the Branch router.
- DLCI 177 will be used to identify all broadcasts that are sent out the Branch router.
- The Branch router has the address 192.168.3.1 configured for the S0/0/0 interface.
- To reach 192.168.3.1, the Branch router will use the virtual circuit that is identified by DLCI 177.
28. At what point in the PPP connection process does the authentication phase occur?
- after NCP establishes Layer 3 parameters
- before LCP begins the link establishment process
- after the initial Configure-Request message from the link initiator
- after the link initiator receives a Configure-Ack message from the responder
29. Refer to the exhibit. Communication between two peers has failed. Based on the output that is shown, what is the most likely cause?
- interface reset
- unplugged cable
- improper LMI type
- PPP negotiation failure
30. Refer to the exhibit. A Cisco router, R1, and a non-Cisco router, R2, were able to communicate successfully using Frame Relay before they were removed from production. An administrator decided to reuse R1 and R2 for another purpose by implementing a direct connection between the two routers, but the Frame Relay configurations were saved. When Frame Relay encapsulation is removed from both routers the connection fails. What will correct the problem?
- Configure both routers to use PPP encapsulation.
- Clear the frame maps on both routers and reboot.
- Set up a routing protocol to communicate between the two routers.
- Configure both routers to use HDLC encapsulation and remove the bandwidth statements.
31. Where will a router operating system image be copied after the copy flash: tftpcommand is issued?
- flash
- DRAM
- NVRAM
- remote server
32. Which data link layer encapsulation protocol is used by default for serial connections between two Cisco routers?
- ATM
- Frame Relay
- HDLC
- PPP
- SDLC
33. Refer to the exhibit. An ACL called Managers already exists on this router. What happens if the network administrator issues the commands as shown in the exhibit?
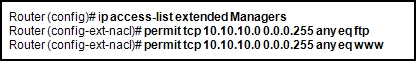
- The commands are added to the end of the existing ACL.
- The existing Managers ACL will be overwritten by the new ACL.
- The router will output an error message and no changes will be made.
- A duplicate Managers ACL will be created that will contain only the new commands.
34. Which statement about a VPN is true?
- VPN link establishment and maintenance is provided by LCP.
- DLCI addresses are used to identify each end of the VPN tunnel.
- VPNs use virtual Layer 3 connections that are routed through the Internet.
- Only IP packets can be encapsulated by a VPN for tunneling through the Internet.
35. Which type of device is located at the central office of a carrier and combines individual DSL connections from multiple users into one high-capacity link to the Internet?
- splitter
- DSLAM
- microfilter
- transceiver
- layer 3 switch
36. Which three guidelines would help contribute to creating a strong password policy? (Choose three.)
- Once a good password is created, do not change it.
- Deliberately misspell words when creating passwords.
- Create passwords that are at least 8 characters in length.
- Use combinations of upper case, lower case, and special characters.
- Write passwords in locations that can be easily retrieved to avoid being locked out.
- Use long words found in the dictionary to make passwords that are easy to remember.
37. What are the symptoms when the s0/0/0 interface on a router is attached to an operational CSU/DSU that is generating a clock signal, but the far end router on the point-to-point link has not been activated?
- show controllers indicates cable type DCE V.35. show interfaces s0/0/0 indicates serial down, line protocol down.
- show controllers indicates cable type DCE V.35. show interfaces s0/0/0 indicates serial up, line protocol down.
- show controllers indicates cable type DTE V.35. show interfaces s0/0/0 indicates serial up, line protocol down.
- show controllers indicates cable type DTE V.35. show interfaces s0/0/0 indicates serial down, line protocol down.
38. Which Frame Relay flow control mechanism is used to signal routers that they should reduce the flow rate of frames?
- DE
- BE
- CIR
- FECN
- CBIR
39. When implementing a dynamic ACL, why is it necessary to include an extended ACL as part of the configuration process?
- to disable the router vty lines
- to reduce the dynamic ACL filtering load
- to override any previous ACL that might be applied to the router
- to provide a controlled situation of allowing traffic through a router
40. Refer to the exhibit. The link between the CTRL and BR_1 routers is configured as shown in the exhibit. Why are the routers unable to establish a PPP session?
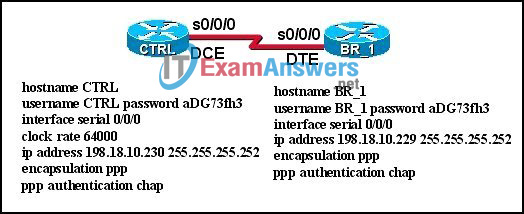
- The clock rate must be 56000.
- The usernames are misconfigured.
- The IP addresses are on different subnets.
- The clock rate is configured on the wrong end of the link.
- The CHAP passwords must be different on the two routers.
- Interface serial 0/0/0 on CTRL must connect to interface serial 0/0/1 on BR_1.
41. What is tunneling?
- using digital certificates to ensure that data endpoints are authentic
- creating a hash to ensure the integrity of data as it traverses a network
- using alternate paths to avoid access control lists and bypass security measures
- encapsulating an entire packet within another packet for transmission over a network
42. Refer to the exhibit. Headquarters is connected through the Internet to branch office A and branch office B. Which WAN technology would be best suited to provide secure connectivity between headquarters and both branch offices?
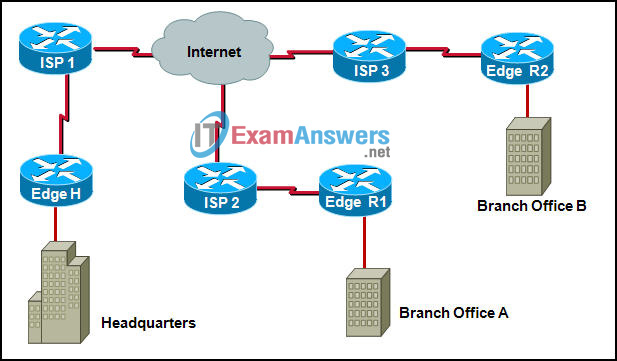
- ATM
- VPN
- ISDN
- Frame Relay
- broadband DSL
43. Refer to the exhibit. A packet is being sent from Host A to Host B through the VPN tunnel between R1 and R3. When the packet first arrives at R3, what are the source and destination IP addresses of the packet?
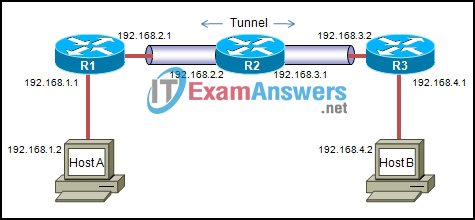
- Source 192.168.1.2 – Destination 192.168.4.2
- Source 192.168.3.1 – Destination 192.168.3.2
- Source 192.168.2.1 – Destination 192.168.3.2
- Source 192.168.3.1 – Destination 192.168.4.2
44. Refer to the exhibit. Company ABC expanded its business and recently opened a new branch office in another country. IPv6 addresses have been used for the company network. The data servers Server1 and Server2 run applications which require end-to-end functionality, with unmodified packets that are forwarded from the source to the destination. The edge routers R1 and R2 support dual stack configuration. What solution should be deployed at the edge of the company network in order to successfully interconnect both offices?
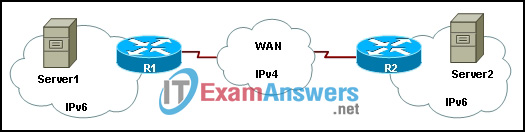
- a new WAN service supporting only IPv6
- NAT overload to map inside IPv6 addresses to outside IPv4 address
- a manually configured IPv6 tunnel between the edge routers R1 and R2
- static NAT to map inside IPv6 addresses of the servers to an outside IPv4 address and dynamic NAT for the rest of the inside IPv6 addresses
45. What function does NCP perform in the establishment of a PPP session?
- It opens the connections and negotiates configuration options.
- It completes the specific configuration of the network layer protocol that is being used.
- It tests the link to determine whether the link quality is sufficient to bring up network layer protocols.
- It provides automatic configuration of the interfaces at each end including detecting common configuration errors.
46. Refer to the exhibit. Results of the show vlan and show vtp status commands for switches S1 and S2 are displayed in the exhibit. VLAN 11 was created on S1. Why is VLAN 11 missing from S2?
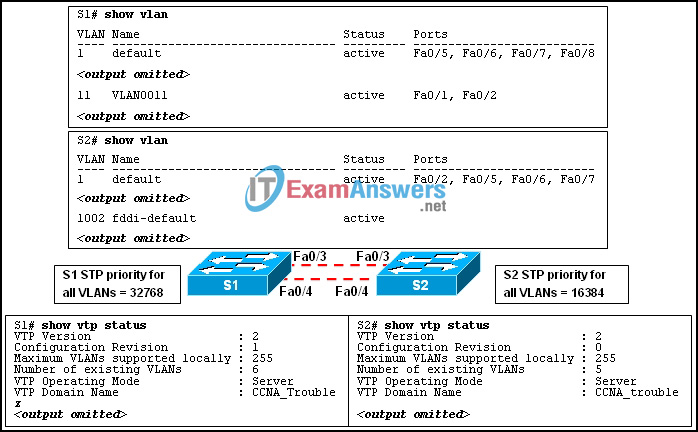
- There is a Layer 2 loop.
- The VTP domain names do not match.
- Only one switch can be in server mode.
- S2 has a higher spanning-tree priority for VLAN 11 than S1 does.
47. A network administrator has changed the VLAN configurations on his network switches over the past weekend. How can the administrator determine if the additions and changes improved performance and availability on the company intranet?
- Conduct a performance test and compare with the baseline that was established previously.
- Interview departmental secretaries and determine if they think load time for web pages has improved.
- Determine performance on the intranet by monitoring load times of company web pages from remote sites.
- Compare the hit counts on the company web server for the current week to the values that were recorded in previous weeks.
48. Technicians from Company A and Company B are comparing DSL transfer rates at their respective companies. Both companies are in the same city, use the same service provider, and have the same rate/service plan. Company A, however, reports higher download speeds than Company B. Which option best explains the reason for Company A having the higher download speeds?
- Company A only uses microfilters on branch locations.
- Company B has a higher volume of POTS voice traffic than does Company A.
- Company B shares the connection to the DSLAM with a larger number of clients than Company A shares.
- The length of the local loop between Company A and the CO is shorter than the length of the local loop between Company B and CO.
49. Refer to the exhibit. A network administrator has issued the commands that are shown on Router1 and Router2. A later review of the routing tables reveals that neither router is learning the LAN network of the neighbor router. What is most likely the problem with the RIPng configuration?
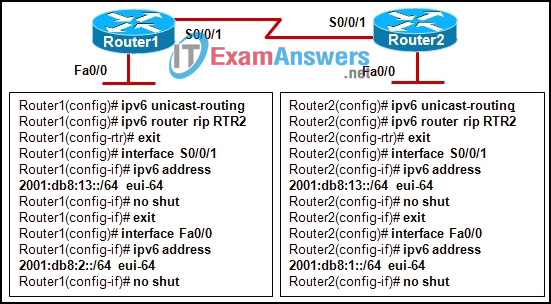
- The serial interfaces are in different subnets.
- The RIPng process is not enabled on interfaces.
- The RIPng network command is not configured.
- The RIPng processes do not match between Router1 and Router2.
50. A network administrator is instructing a technician on best practices for applying ACLs. Which two suggestions should the administrator provide? (Choose two.)
- Named ACLs are less efficient than numbered ACLs.
- Standard ACLs should be applied inside the core layer.
- Place standard ACLs as close to the destination as possible.
- ACLs applied to outbound interfaces require fewer router resources.
- Extended ACLs should be applied closest to the source that is specified by the ACL.
51. Which two statements are true about creating and applying access lists? (Choose two.)
- One access list per port, per protocol, per direction is permitted.
- Access list entries should filter in the order from general to specific.
- Statements are processed sequentially from top to bottom until a match is found.
- The term “inbound” refers to traffic entering the network from the router interface where the ACL is applied.
- Standard ACLs should be applied closest to the source while extended ACLs should be applied closest to the destination.
52. Refer to the exhibit. Computers on the internal network need access to all servers in the external network. The only traffic that is permitted from the external network must be responses to requests that are initiated on the internal network. Which security measure would satisfy this requirement?

- a numbered extended ACL
- a named standard ACL
- a reflexive ACL
- a dynamic ACL
53. Refer to the exhibit. What is placed in the address field in the header of a frame that will travel from the San Jose router to the DC router?
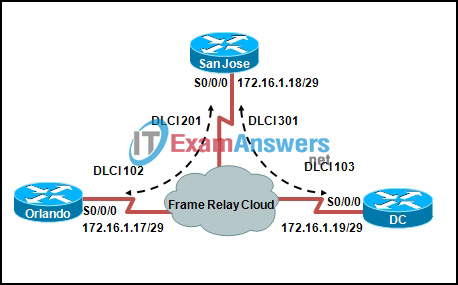
- DLCI 103
- DLCI 301
- 172.16.1.18
- 172.16.1.19
54. An administrator is unable to receive e-mail. While troubleshooting the problem, the administrator is able to ping the local mail server IP address successfully from a remote network and can successfully resolve the mail server name to an IP address via the use of the nslookup command. At what OSI layer is the problem most likely to be found?
- physical layer
- data link layer
- network layer
- application layer
55. Which security solution has the responsibility of monitoring suspicious processes that are running on a host and that might indicate infection of Trojan horse applications?
- antivirus application
- operating system patches
- intrusion prevention system
- Cisco Adaptive Security Appliance

I have the exam in like 3 days, from what I know this is probs the closest ull get, if youve been doing version 4 for ccna123, then in the practise final they changed them up, so id say this is probs the best, its defs the most recent one ive found online,
Did this work for anyone this year??
Did this work for any of you guys?
My question to Mesut Ozil
Are these the answers to the exam this year because ive got my exam in a couple of days