Assessment ESwitching Chapter 3 – CCNA 3 Exploration: LAN Switching and Wireless (Version 4.0)
1. Refer to the exhibit. The network administrator has just added VLAN 50 to Switch1 and Switch2 and assigned hosts on the IP addresses of the VLAN in the 10.1.50.0/24 subnet range. Computer A can communicate with computer B, but not with computer C or computer D. What is the most likely cause of this problem?
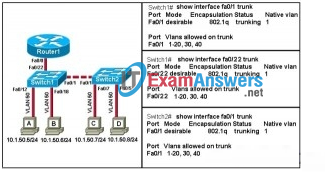
- There is a native VLAN mismatch.
- The link between Switch1 and Switch2 is up but not trunked.
- The router is not properly configured for inter-VLAN routing.
- VLAN 50 is not allowed to entering the trunk between Switch1 and Switch2.
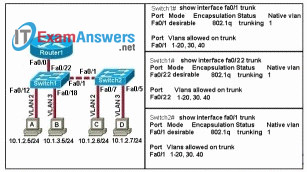
2. Refer to the exhibit. The exhibited configurations do not allow the switches to form a trunk. What is the most likely cause of this problem?

- Cisco switches only support the ISL trunking protocol.
- The trunk cannot be negotiated with both ends set to auto.
- By default, Switch1 will only allow VLAN 5 across the link.
- A common native VLAN should have been configured on the switches.
3. Refer to the exhibit. Which two conclusions can be drawn regarding the switch that produced the output shown? (Choose two.)
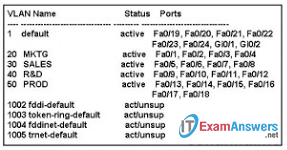
- The network administrator configured VLANs 1002-1005.
- The VLANs are in the active state and are in the process of negotiatingconfiguration parameters.
- A FDDI trunk has been configured on this switch.
- The command switchport access vlan 20 was entered in interface configurationmode for Fast Ethernet interface 0/1.
- Devices attached to ports fa0/5 through fa0/8 cannot communicate with devices attached to ports fa0/9 through fa0/12 without the use of a Layer 3 device.
4. What statements describe how hosts on VLANs communicate?
- Hosts on different VLANs use VTP to negotiate a trunk.
- Hosts on different VLANs communicate through routers.
- Hosts on different VLANs should be in the same IP network.
- Hosts on different VLANs examine VLAN ID in the frame tagging to determine if the frame for their network.
5. Switch port fa0/1 was manually configured as a trunk, but now it will be used to connect a host to the network. How should the network administrator reconfigure switch port Fa0/1?
- Disable DTP.
- Delete any VLANs currently being trunked through port Fa0/1.
- Administratively shut down and re-enable the interface to return it to default.
- Enter the switchport mode access command in interface configuration mode.
6. Refer to the exhibit. SW1 and SW2 are new switches being installed in the topology shown in the exhibit. Interface Fa0/1 on switch SW1 has been configured with trunk mode “on”. Which statement is true about forming a trunk link between the switches SW1 and SW2?
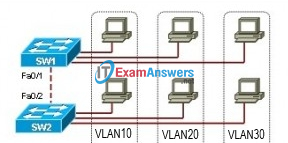
- Interface Fa0/2 on switch SW2 will negotiate to become a trunk link if it supports DTP.
- Interface Fa0/2 on switch SW2 can only become a trunk link if statically configured as a trunk.
- Interface Fa0/1 converts the neighboring link on the adjacent switch into a trunk link if the neighboring interface is configured in nonegotiate mode.
- Interface Fa0/1 converts the neighboring link on the adjacent switch into a trunk link automatically with no consideration of the configuration on the neighboring interface.
7. The network administrator wants to separate hosts in Building A into two VLANs numbered 20 and 30. Which two statements are true concerning VLAN configuration? (Choose two.)
- The VLANs may be named.
- VLAN information is saved in the startup configuration.
- Non-default VLANs created manually must use the extended range VLAN numbers.
- The network administrator may create the VLANs in either global configurationmode or VLAN database mode.
- Both VLANs may be named BUILDING_A to distinguish them from other VLANs in different geographical locations.
8. What is a valid consideration for planning VLAN traffic across multiple switches?
- Configuring interswitch connections as trunks will cause all hosts on any VLAN to receive broadcasts from the other VLANs.
- A trunk connection is affected by broadcast storms on any particular VLAN that is carried by that trunk.
- Restricting trunk connections between switches to a single VLAN will improve efficiency of port usage.
- Carrying all required VLANs on a single access port will ensure proper traffic separation.
9. What are two characteristics of VLAN1 in a default switch configuration? (Choose two.)
- VLAN1 should renamed.
- VLAN 1 is the management VLAN.
- All switch ports are members of VLAN1.
- Only switch port 0/1 is assigned to VLAN1.
- Links between switches must be members of VLAN1.
10. Refer to the exhibit. Which statement is true concerning interface Fa0/5?
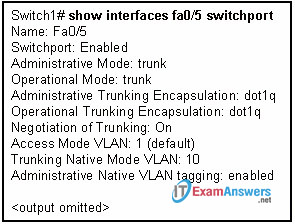
- The default native VLAN is being used.
- The trunking mode is set to auto.
- Trunking can occur with non-Cisco switches.
- VLAN information about the interface encapsulates the Ethernet frames.
11. What statement about the 802.1q trunking protocol is true?
- 802.1q is Cisco proprietary.
- 802.1q frames are mapped to VLANs by MAC address.
- 802.1q does NOT require the FCS of the original frame to be recalculated.
- 802.1q will not perform operations on frames that are forwarded out access ports.
12. What is the effect of the switchport mode dynamic desirable command?
- DTP cannot negotiate the trunk since the native VLAN is not the default VLAN.
- The remote connected interface cannot negotiate a trunk unless it is also configured as dynamic desirable.
- The connected devices dynamically determine when data for multiple VLANs must be transmitted across the link and bring the trunk up as needed.
- A trunk link is formed if the remote connected device is configured with the switchport mode dynamic auto or switchport mode trunk commands.
13. A network administrator is removing several VLANs from a switch. When the administrator enters the no vlan 1 command, an error is received. Why did this command generate an error?
- VLAN 1 can never be deleted.
- VLAN 1 can only be deleted by deleting the vlan.dat file.
- VLAN 1 can not be deleted until all ports have been removed from it.
- VLAN 1 can not be deleted until another VLAN has been assigned its responsibilities.
14. Refer to the exhibit. Company HR is adding PC4, a specialized application workstation, to a new company office. The company will add a switch, S3, connected via a trunk link to S2, another switch. For security reasons the new PC will reside in the HR VLAN, VLAN 10. The new office will use the 172.17.11.0/24 subnet. After installation, users on PC1 are unable to access shares on PC4. What is the likely cause?
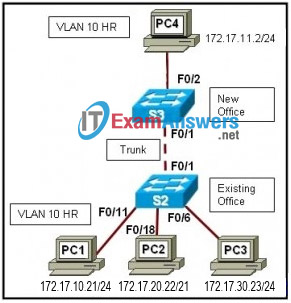
- The switch to switch connection must be configured as an access port to permit access to VLAN 10 on S3.
- The new PC is on a different subnet so Fa0/2 on S3 must be configured as a trunk port.
- PC4 must use the same subnet as PC1.
- A single VLAN cannot span multiple switches.
15. Refer to the exhibit. Computer 1 sends a frame to computer 4. On which links along the path between computer 1 and computer 4 will a VLAN ID tag be included with the frame?
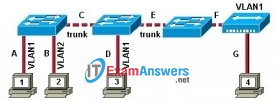
- A
- A, B
- A, B, D, G
- A, D, F
- C, E
- C, E, F
16. Refer to the exhibit. Computer B is unable to communicate with computer D. What is the most likely cause of this problem?
- The link between the switches is up but not trunked.
- VLAN 3 is not an allowed VLAN to enter the trunk between the switches.
- The router is not properly configured to route traffic between the VLANs.
- Computer D does not have a proper address for the VLAN 3 address space.
17. What happens to the member ports of a VLAN when the VLAN is deleted?
- The ports cannot communicate with other ports.
- The ports default back to the management VLAN.
- The ports automatically become a part of VLAN1.
- The ports remain a part of that VLAN until the switch is rebooted. They then become members of the management VLAN.
18. Which two statements describe the benefits of VLANs? (Choose two.)
- VLANs improve network performance by regulating flow control and window size.
- VLANs enable switches to route packets to remote networks via VLAN ID filtering.
- VLANs reduce network cost by reducing the number of physical ports required on switches.
- VLANs improve network security by isolating users that have access to sensitive data and applications.
- VLANs divide a network into smaller logical networks, resulting in lower susceptibility to broadcast storms.
19. What switch port modes will allow a switch to successfully form a trunking link if the neighboring switch port is in “dynamic desirable” mode?
- dynamic desirable mode
- on or dynamic desirable mode
- on, auto, or dynamic desirable mode
- on, auto, dynamic desirable, or nonegotiate mode
20. What must the network administrator do to remove Fast Ethernet port fa0/1 from VLAN 2 and assign it to VLAN 3?
- Enter the no vlan 2 and the vlan 3 commands in global configuration mode.
- Enter the switchport access vlan 3 command in interface configuration mode.
- Enter the switchport trunk native vlan 3 command in interface configuration mode.
- Enter the no shutdown in interface configuration mode to return it to the default configuration and then configure the port for VLAN 3.
21. Refer to the exhibit. How far is a broadcast frame that is sent by computer A propagated in the LAN domain?
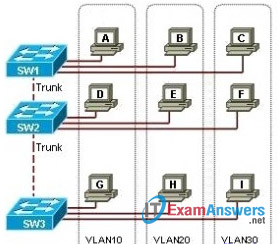
- none of the computers will receive the broadcast frame
- computer A, computer B, computer C
- computer A, computer D, computer G
- computer B, computer C
- computer D, computer G
- computer A, computer B, computer C, computer D, computer E, computer F, computer G, computer H, computer I
