Check answers here:
Modules 1 – 3: Basic Network Connectivity and Communications Exam Answers
Quiz-summary
0 of 75 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
Information
CCNA 1 v7 Modules 1 – 3: Basic Network Connectivity and Communications - Test Online
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 75 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- Answered
- Review
-
Question 1 of 75
1. Question
1 pointsDuring a routine inspection, a technician discovered that software that was installed on a computer was secretly collecting data about websites that were visited by users of the computer. Which type of threat is affecting this computer?Correct
Incorrect
-
Question 2 of 75
2. Question
1 pointsWhich term refers to a network that provides secure access to the corporate offices by suppliers, customers and collaborators?Correct
Incorrect
-
Question 3 of 75
3. Question
1 pointsA large corporation has modified its network to allow users to access network resources from their personal laptops and smart phones. Which networking trend does this describe?Correct
Incorrect
-
Question 4 of 75
4. Question
1 pointsWhat is an ISP?Correct
Incorrect
-
Question 5 of 75
5. Question
1 pointsMatch the requirements of a reliable network with the supporting network architecture. (Not all options are used.)Sort elements
- security
- fault tolerance
- Nothing
- scalability
- Nothing
-
Protect the network from unauthorized access.
-
Provide redundant links and devices.
-
Match the type of communication with a specific priority.
-
Expand the network without degrading the service for existing users.
-
Ensure that streaming data is provided over high speed links.
Correct
Incorrect
-
Question 6 of 75
6. Question
1 pointsAn employee at a branch office is creating a quote for a customer. In order to do this, the employee needs to access confidential pricing information from internal servers at the Head Office. What type of network would the employee access?Correct
Incorrect
Hint
Intranet is a term used to refer to a private connection of LANs and WANs that belongs to an organization. An intranet is designed to be accessible only by the organization’s members, employees, or others with authorization. -
Question 7 of 75
7. Question
1 pointsWhich statement describes the use of powerline networking technology?Correct
Incorrect
-
Question 8 of 75
8. Question
1 pointsA networking technician is working on the wireless network at a medical clinic. The technician accidentally sets up the wireless network so that patients can see the medical records data of other patients. Which of the four network characteristics has been violated in this situation?Correct
Incorrect
Hint
Network security includes protecting the confidentiality of data that is on the network. In this case, because confidential data has been made available to unauthorized users, the security characteristic of the network has failed. -
Question 9 of 75
9. Question
1 pointsMatch each characteristic to its corresponding Internet connectivity type. (Not all options are used.)Sort elements
- high bandwidth connection that runs over telephone line
- typically has very low bandwidth
- not suited for heavily wooded areas
- uses coaxial cable as a medium
- typically uses a T1/E1 or T3/E3 circuit
-
DSL
-
dialup telephone
-
satellite
-
cable
Correct
Incorrect
Hint
DSL is an always-on, high bandwidth connection that runs over telephone lines. Cable uses the same coaxial cable that carries television signals into the home to provide Internet access. Dialup telephone is much slower than either DSL or cable, but is the least expensive option for home users because it can use any telephone line and a simple modem. Satellite requires a clear line of sight and is affected by trees and other obstructions. None of these typical home options use dedicated leased lines such as T1/E1 and T3/E3. -
Question 10 of 75
10. Question
1 pointsWhat two criteria are used to help select a network medium from various network media? (Choose two.)Correct
Incorrect
Hint
Criteria for choosing a network medium are the distance the selected medium can successfully carry a signal, the environment in which the selected medium is to be installed, the amount of data and the speed at which the data must be transmitted, and the cost of the medium and its installation. -
Question 11 of 75
11. Question
1 pointsWhat type of network traffic requires QoS?Correct
Incorrect
-
Question 12 of 75
12. Question
1 pointsA user is implementing security on a small office network. Which two actions would provide the minimum security requirements for this network? (Choose two.)Correct
Incorrect
Hint
Technically complex security measures such as intrusion prevention and intrusion prevention systems are usually associated with business networks rather than home networks. Installing antivirus software, antimalware software, and implementing a firewall will usually be the minimum requirements for home networks. Installing a home wireless network will not improve network security, and will require further security actions to be taken. -
Question 13 of 75
13. Question
1 pointsPasswords can be used to restrict access to all or parts of the Cisco IOS. Select the modes and interfaces that can be protected with passwords. (Choose three.)Correct
Incorrect
Hint
Access to the VTY and console interfaces can be restricted using passwords. Out-of-band management of the router can be restricted in both user EXEC and privileged EXEC modes. -
Question 14 of 75
14. Question
1 pointsWhich interface allows remote management of a Layer 2 switch?Correct
Incorrect
Hint
In a Layer 2 switch, there is a switch virtual interface (SVI) that provides a means for remotely managing the device. -
Question 15 of 75
15. Question
1 pointsWhat function does pressing the Tab key have when entering a command in IOS?Correct
Incorrect
Hint
Pressing the Tab key after a command has been partially typed will cause the IOS to complete the rest of the command. -
Question 16 of 75
16. Question
1 pointsWhile trying to solve a network issue, a technician made multiple changes to the current router configuration file. The changes did not solve the problem and were not saved. What action can the technician take to discard the changes and work with the file in NVRAM?Correct
Incorrect
Hint
The technician does not want to make any mistakes trying to remove all the changes that were done to the running configuration file. The solution is to reboot the router without saving the running configuration. The copy startup-config running-config command does not overwrite the running configuration file with the configuration file stored in NVRAM, but rather it just has an additive effect. -
Question 17 of 75
17. Question
1 pointsAn administrator uses the Ctrl-Shift-6 key combination on a switch after issuing the ping command. What is the purpose of using these keystrokes?Correct
Incorrect
Hint
To interrupt an IOS process such as ping or traceroute, a user enters the Ctrl-Shift-6 key combination. Tab completes the remainder of parameters or arguments within a command. To exit from configuration mode to privileged mode use the Ctrl-Z keystroke. CTRL-R will redisplay the line just typed, thus making it easier for the user to press Enter and reissue the ping command. -
Question 18 of 75
18. Question
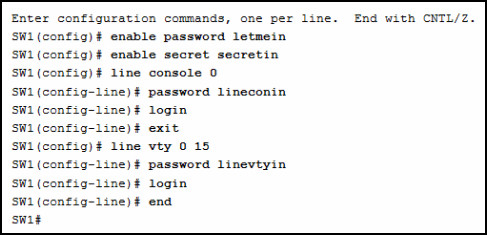
1 pointsRefer to the exhibit. A network administrator is configuring access control to switch SW1. If the administrator uses a console connection to connect to the switch, which password is needed to access user EXEC mode?
 Correct
Correct
Incorrect
Hint
Telnet accesses a network device through the virtual interface configured with the line VTY command. The password configured under this is required to access the user EXEC mode. The password configured under the line console 0 command is required to gain entry through the console port, and the enable and enable secret passwords are used to allow entry into the privileged EXEC mode. -
Question 19 of 75
19. Question
1 pointsA technician configures a switch with these commands:SwitchA(config)# interface vlan 1 SwitchA(config-if)# ip address 192.168.1.1 255.255.255.0 SwitchA(config-if)# no shutdown
What is the technician configuring?Correct
Incorrect
Hint
For a switch to have an IP address, a switch virtual interface must be configured. This allows the switch to be managed remotely over the network. -
Question 20 of 75
20. Question
1 pointsWhich command or key combination allows a user to return to the previous level in the command hierarchy?Correct
Incorrect
Hint
End and CTRL-Z return the user to the privileged EXEC mode. Ctrl-C ends a command in process. The exit command returns the user to the previous level. -
Question 21 of 75
21. Question
1 pointsWhat are two characteristics of RAM on a Cisco device? (Choose two.)Correct
Incorrect
Hint
RAM stores data that is used by the device to support network operations. The running configuration is stored in RAM. This type of memory is considered volatile memory because data is lost during a power cycle. Flash memory stores the IOS and delivers a copy of the IOS into RAM when a device is powered on. Flash memory is nonvolatile since it retains stored contents during a loss of power. -
Question 22 of 75
22. Question
1 pointsWhich two host names follow the guidelines for naming conventions on Cisco IOS devices? (Choose two.)Correct
Incorrect
Hint
Some guidelines for naming conventions are that names should: Start with a letter Contain no spaces End with a letter or digit Use only letters, digits, and dashes Be less than 64 characters in length -
Question 23 of 75
23. Question
1 pointsHow is SSH different from Telnet?Correct
Incorrect
Hint
SSH is the preferred protocol for connecting to a device operating system over the network because it is much more secure than Telnet. Both SSH and Telnet are used to connect to devices over the network, and so are both used in-band. PuTTY and Terra Term can be used to make both SSH and Telnet connections. -
Question 24 of 75
24. Question
1 pointsAn administrator is configuring a switch console port with a password. In what order will the administrator travel through the IOS modes of operation in order to reach the mode in which the configuration commands will be entered? (Not all options are used.)Correct
Incorrect
Hint
The configuration mode that the administrator first encounters is user EXEC mode. After the enable command is entered, the next mode is privileged EXEC mode. From there, the configure terminal command is entered to move to global configuration mode. Finally, the administrator enters the line console 0 command to enter the mode in which the configuration will be entered. -
Question 25 of 75
25. Question
1 pointsWhat are three characteristics of an SVI? (Choose three.)Correct
Incorrect
Hint
Switches have one or more switch virtual interfaces (SVIs). SVIs are created in software since there is no physical hardware associated with them. Virtual interfaces provide a means to remotely manage a switch over a network that is using IP. Each switch comes with one SVI appearing in the default configuration “out-of-the-box.” The default SVI interface is VLAN1. -
Question 26 of 75
26. Question
1 pointsWhat command is used to verify the condition of the switch interfaces, including the status of the interfaces and a configured IP address?Correct
Incorrect
Hint
The show ip interface brief command is used to display a brief synopsis of the condition of the device interfaces. The ipconfig command is used to verify TCP/IP properties on a host. The ping command is used to verify Layer 3 connectivity. The traceroute command is used to trace the network path from source to destination. -
Question 27 of 75
27. Question
1 pointsMatch the description with the associated IOS mode. (Not all options are used.)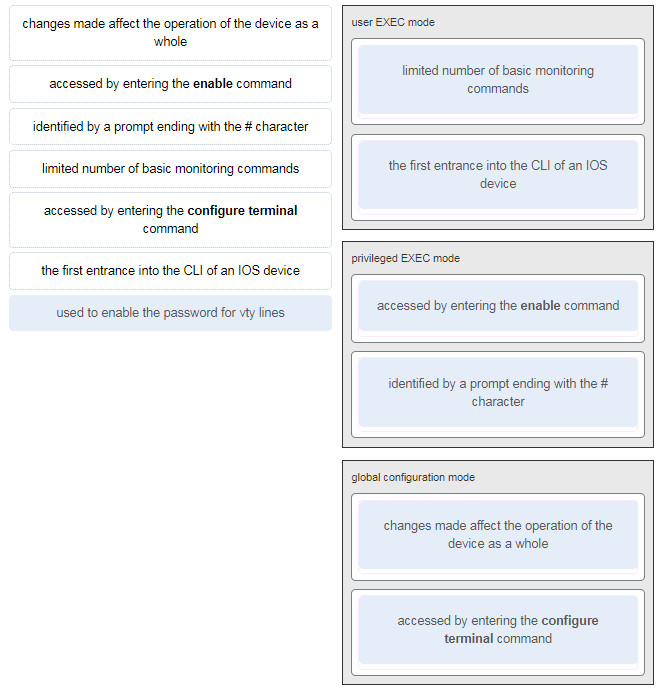 Correct
Correct
Incorrect
-
Question 28 of 75
28. Question
1 pointsMatch the definitions to their respective CLI hot keys and shortcuts. (Not all options are used.)Sort elements
- space bar
- Up Arrow
- ?
- Tab
- Ctrl-Shift-6
- Ctrl-C
-
displays the next screen
-
scrolls backwards through previously entered commands
-
provides context-sensitive help
-
completes abbreviated commands and parameters
-
aborts commands such as trace and ping
Correct
Incorrect
-
Question 29 of 75
29. Question
1 pointsIn the show running-config command, which part of the syntax is represented by running-config?Correct
Incorrect
Hint
The first part of the syntax, show, is the command, and the second part of the syntax, running-config, is the keyword. The keyword specifies what should be displayed as the output of the show command. -
Question 30 of 75
30. Question
1 pointsAfter making configuration changes on a Cisco switch, a network administrator issues a copy running-config startup-config command. What is the result of issuing this command?Correct
Incorrect
-
Question 31 of 75
31. Question
1 pointsWhat command will prevent all unencrypted passwords from displaying in plain text in a configuration file?Correct
Incorrect
Hint
To prevent all configured passwords from appearing in plain text in configuration files, an administrator can execute the service password-encryption command. This command encrypts all configured passwords in the configuration file. -
Question 32 of 75
32. Question
1 pointsA network administrator enters the service password-encryption command into the configuration mode of a router. What does this command accomplish?Correct
Incorrect
Hint
The startup-config and running-config files display most passwords in plaintext. Use the service password-encryption global config command to encrypt all plaintext passwords in these files. -
Question 33 of 75
33. Question
1 pointsWhat method can be used by two computers to ensure that packets are not dropped because too much data is being sent too quickly?Correct
Incorrect
Hint
In order for two computers to be able to communicate effectively, there must be a mechanism that allows both the source and destination to set the timing of the transmission and receipt of data. Flow control allows for this by ensuring that data is not sent too fast for it to be received properly. -
Question 34 of 75
34. Question
1 pointsWhich statement accurately describes a TCP/IP encapsulation process when a PC is sending data to the network?Correct
Incorrect
Hint
When the data is traveling from the PC to the network, the transport layer sends segments to the internet layer. The internet layer sends packets to the network access layer, which creates frames and then converts the frames to bits. The bits are released to the network media. -
Question 35 of 75
35. Question
1 pointsWhat three application layer protocols are part of the TCP/IP protocol suite? (Choose three.)Correct
Incorrect
Hint
DNS, DHCP, and FTP are all application layer protocols in the TCP/IP protocol suite. ARP and PPP are network access layer protocols, and NAT is an internet layer protocol in the TCP/IP protocol suite. -
Question 36 of 75
36. Question
1 pointsMatch the description to the organization. (Not all options are used.)Sort elements
- IANA
- ISO
- ISOC
- EIA
-
This organization is responsible for overseeing and managing IP address allocation, domain name management, and protocol identifiers.
-
This organization is the largest developer of international standards in the world for a wide variety of products and services. It is known for its Open Systems Interconnection (OSI) reference model.
-
This organization promotes the open development, evolution, and use of the Internet throughout the world.
Correct
Incorrect
-
Question 37 of 75
37. Question
1 pointsWhich name is assigned to the transport layer PDU?Correct
Incorrect
Hint
Application data is passed down the protocol stack on its way to be transmitted across the network media. During the process, various protocols add information to it at each level. At each stage of the process, a PDU (protocol data unit) has a different name to reflect its new functions. The PDUs are named according to the protocols of the TCP/IP suite: Data – The general term for the PDU used at the application layer. Segment – transport layer PDU Packet – network layer PDU Frame – data link layer PDU Bits – A physical layer PDU used when physically transmitting data over the medium -
Question 38 of 75
38. Question
1 pointsWhen IPv4 addressing is manually configured on a web server, which property of the IPv4 configuration identifies the network and host portion for an IPv4 address?Correct
Incorrect
Hint
There are several components that need to be entered when configuring IPv4 for an end device: IPv4 address – uniquely identifies an end device on the network Subnet mask – determines the network address portion and host portion for an IPv4 address Default gateway – the IP address of the router interface used for communicating with hosts in another network DNS server address – the IP address of the Domain Name System (DNS) server DHCP server address (if DHCP is used) is not configured manually on end devices. It will be provided by a DHCP server when an end device requests an IP address. -
Question 39 of 75
39. Question
1 pointsWhat process involves placing one PDU inside of another PDU?Correct
Incorrect
Hint
When a message is placed inside of another message, this is known as encapsulation. On networks, encapsulation takes place when one protocol data unit is carried inside of the data field of the next lower protocol data unit. -
Question 40 of 75
40. Question
1 pointsWhat layer is responsible for routing messages through an internetwork in the TCP/IP model?Correct
Incorrect
Hint
The TCP/IP model consists of four layers: application, transport, internet, and network access. Of these four layers, it is the internet layer that is responsible for routing messages. The session layer is not part of the TCP/IP model but is rather part of the OSI model. -
Question 41 of 75
41. Question
1 pointsFor the TCP/IP protocol suite, what is the correct order of events when a Telnet message is being prepared to be sent over the network?Sort elements
- Third
- Second
- Fourth
- First
-
The IP header is added.
-
The TCP header is added.
-
The Ethernet header is added.
-
The Telnet-formatted data is provided to the next layer.
Correct
Incorrect
-
Question 42 of 75
42. Question
1 pointsWhich PDU format is used when bits are received from the network medium by the NIC of a host?Correct
Incorrect
Hint
When received at the physical layer of a host, the bits are formatted into a frame at the data link layer. A packet is the PDU at the network layer. A segment is the PDU at the transport layer. A file is a data structure that may be used at the application layer. -
Question 43 of 75
43. Question
1 pointsRefer to the exhibit. ServerB is attempting to contact HostA. Which two statements correctly identify the addressing that ServerB will generate in the process? (Choose two.)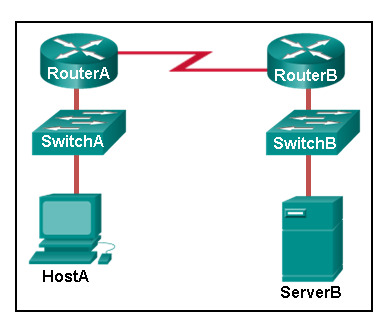 Correct
Correct
Incorrect
-
Question 44 of 75
44. Question
1 pointsWhich method allows a computer to react accordingly when it requests data from a server and the server takes too long to respond?Correct
Incorrect
-
Question 45 of 75
45. Question
1 pointsA web client is receiving a response for a web page from a web server. From the perspective of the client, what is the correct order of the protocol stack that is used to decode the received transmission?Correct
Incorrect
Hint
1. HTTP governs the way that a web server and client interact. 2. TCP manages individual conversations between web servers and clients. 3. IP is responsible for delivery across the best path to the destination. 4. Ethernet takes the packet from IP and formats it for transmission. -
Question 46 of 75
46. Question
1 pointsWhich two OSI model layers have the same functionality as a single layer of the TCP/IP model? (Choose two.)Correct
Incorrect
Hint
The OSI data link and physical layers together are equivalent to the TCP/IP network access layer. The OSI transport layer is functionally equivalent to the TCP/IP transport layer, and the OSI network layer is equivalent to the TCP/IP internet layer. The OSI application, presentation, and session layers are functionally equivalent to the application layer within the TCP/IP model. -
Question 47 of 75
47. Question
1 pointsAt which layer of the OSI model would a logical address be added during encapsulation?Correct
Incorrect
-
Question 48 of 75
48. Question
1 pointsWhat is a characteristic of multicast messages?Correct
Incorrect
Hint
Multicast is a one-to-many type of communication. Multicast messages are addressed to a specific multicast group. -
Question 49 of 75
49. Question
1 pointsWhich statement is correct about network protocols?Correct
Incorrect
-
Question 50 of 75
50. Question
1 pointsWhat is an advantage of network devices using open standard protocols?Correct
Incorrect
Hint
An advantage of network devices implementing open standard protocols, such as from the TCP/IP suite, is that clients and servers running different operating systems can communicate with each other. Open standard protocols facilitate innovation and competition between vendors and across markets, and can reduce the occurrence of monopolies in networking markets. -
Question 51 of 75
51. Question
1 pointsWhich device performs the function of determining the path that messages should take through internetworks?Correct
Incorrect
Hint
A router is used to determine the path that the messages should take through the network. A firewall is used to filter incoming and outgoing traffic. A DSL modem is used to provide Internet connection for a home or an organization. -
Question 52 of 75
52. Question
1 pointsOpen the PT Activity. Perform the tasks in the activity instructions and then answer the question.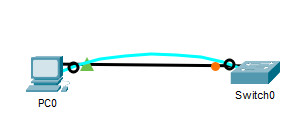 What is the IP address of the switch virtual interface (SVI) on Switch0? Correct
What is the IP address of the switch virtual interface (SVI) on Switch0? Correct
Incorrect
Hint
After the enable command is issued, the show running-configuration command or the show ip interfaces brief command will display the IP address of the switch virtual interface (SVI). -
Question 53 of 75
53. Question
1 pointsWhy would a Layer 2 switch need an IP address?Correct
Incorrect
Hint
A switch, as a Layer 2 device, does not need an IP address to transmit frames to attached devices. However, when a switch is accessed remotely through the network, it must have a Layer 3 address. The IP address must be applied to a virtual interface rather than to a physical interface. Routers, not switches, function as default gateways. -
Question 54 of 75
54. Question
1 pointsRefer to the exhibit. An administrator is trying to configure the switch but receives the error message that is displayed in the exhibit. What is the problem?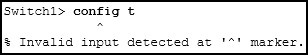 Correct
Correct
Incorrect
Hint
In order to enter global configuration mode, the command configure terminal, or a shortened version such as config t, must be entered from privileged EXEC mode. In this scenario the administrator is in user EXEC mode, as indicated by the > symbol after the hostname. The administrator would need to use the enable command to move into privileged EXEC mode before entering the configure terminal command. -
Question 55 of 75
55. Question
1 pointsWhat term describes a network owned by one organization that provides safe and secure access to individuals who work for a different organization?Correct
Incorrect
-
Question 56 of 75
56. Question
1 pointsWhat term describes storing personal files on servers over the internet to provide access anywhere, anytime, and on any device?Correct
Incorrect
-
Question 57 of 75
57. Question
1 pointsWhat term describes a network where one computer can be both client and server?Correct
Incorrect
-
Question 58 of 75
58. Question
1 pointsWhat term describes a type of network used by people who work from home or from a small remote office?Correct
Incorrect
-
Question 59 of 75
59. Question
1 pointsWhat term describes a computing model where server software runs on dedicated computers?Correct
Incorrect
-
Question 60 of 75
60. Question
1 pointsWhat term describes a type of network used by people who work from home or from a small remote office?Correct
Incorrect
-
Question 61 of 75
61. Question
1 pointsWhat term describes a technology that allows devices to connect to the LAN using an electrical outlet?Correct
Incorrect
-
Question 62 of 75
62. Question
1 pointsWhat term describes a policy that allows network devices to manage the flow of data to give priority to voice and video?Correct
Incorrect
-
Question 63 of 75
63. Question
1 pointsWhat term describes a private collection of LANs and WANs that belongs to an organization?Correct
Incorrect
-
Question 64 of 75
64. Question
1 pointsWhat term describes the ability to use personal devices across a business or campus network?Correct
Incorrect
-
Question 65 of 75
65. Question
1 pointsAt which OSI layer is a source IP address added to a PDU during the encapsulation process?Correct
Incorrect
-
Question 66 of 75
66. Question
1 pointsAt which OSI layer is a destination port number added to a PDU during the encapsulation process?Correct
Incorrect
-
Question 67 of 75
67. Question
1 pointsAt which OSI layer is data added to a PDU during the encapsulation process?Correct
Incorrect
-
Question 68 of 75
68. Question
1 pointsAt which OSI layer is a source IP address added to a PDU during the encapsulation process?Correct
Incorrect
-
Question 69 of 75
69. Question
1 pointsAt which OSI layer is data added to a PDU during the encapsulation process?Correct
Incorrect
-
Question 70 of 75
70. Question
1 pointsAt which OSI layer is a destination IP address added to a PDU during the encapsulation process?Correct
Incorrect
-
Question 71 of 75
71. Question
1 pointsAt which OSI layer is a source MAC address added to a PDU during the encapsulation process?Correct
Incorrect
-
Question 72 of 75
72. Question
1 pointsAt which OSI layer is a source port number added to a PDU during the encapsulation process?Correct
Incorrect
-
Question 73 of 75
73. Question
1 pointsAt which OSI layer is a destination MAC address added to a PDU during the encapsulation process?Correct
Incorrect
-
Question 74 of 75
74. Question
1 pointsWhen data is encoded as pulses of light, which media is being used to transmit the data?Correct
Incorrect
-
Question 75 of 75
75. Question
1 pointsWhich two devices are intermediary devices? (Choose two)Correct
Incorrect

Is there anyway to practice the individual v7 Questions?
Is still good answer ?
I’m gonna check tomorrow I let you know if you still need it
Hey, does it still work?
good for revision
Q number 24 I was nervous because I thought I’m wrong how i hve been memorized the answer but I knew my answer is not wrong I think how they hve prepared is something wrong because they are human as we known human is not like a Robot let them give a chance to fix them our Question after that thank you ,your help guys✔.
Good one
#24 is wrong.
An administrator is configuring a switch console port with a password. In what order will the administrator travel through the IOS modes of operation in order to reach the mode in which the configuration commands will be entered? (Not all options are used.)
1-User exe mode
2-Priveled exe mode
3-Global Configuration Mode
4-Lince conf….
nice digga danke für den test
Did an attempt very nice quizez here. Can i pass my CCNA with content from here?
yes its the same questions
can you pls fix Q 24
Je n’arrive pas à faire le test en ligne pour réviser car star quiz ne marche pas, dites moi si vous avez enlever le test en ligne pour moi seul ou bien c’est pour tout le monde?
SVP j’ai besoin d’aide
Great quiz.
Fantastic Stuff!
Great quiz bro
Great Quiz
24 is badly incorrect
C’est vraiment intéressant.
Ce site va beaucoup m’aider pour passer ma certification.
Merçi et bon courage !
I love this page, admin, the question 24,28, have a problem, i secure i done well, and always mark bad, thank
Hello How can I take this quiz?
Admin why “Start quiz” doesn’t work for me? Need Help !
Please try again
080-20 ITN
thank u, good quiz!
Excelente Trabajo. Estes test me ayudo a encontrar mis devilidades.
Hasta la vista du bauer