Time limit: 0
Quiz-summary
0 of 23 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
Information
Good luck for you!
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 23 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- Answered
- Review
-
Question 1 of 23
1. Question
1 pointsRefer to the exhibit. If a hacker on the outside network sends an IP packet with source address 172.30.1.50, destination address 10.0.0.3, source port 23, and destination port 2447, what does the Cisco IOS firewall do with the packet?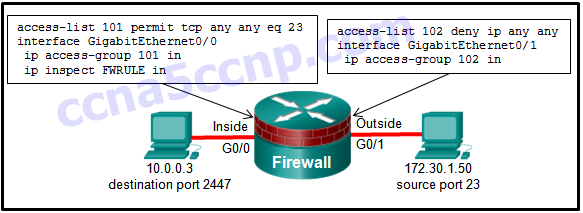 Correct
Correct
Incorrect
-
Question 2 of 23
2. Question
1 pointsTo facilitate the troubleshooting process, which inbound ICMP message should be permitted on an outside interface?Correct
Incorrect
-
Question 3 of 23
3. Question
1 pointsWhich command is used to activate an IPv6 ACL named ENG_ACL on an interface so that the router filters traffic prior to accessing the routing table?Correct
Incorrect
-
Question 4 of 23
4. Question
1 pointsWhich statement describes a typical security policy for a DMZ firewall configuration?Correct
Incorrect
-
Question 5 of 23
5. Question
1 pointsRefer to the exhibit. Which statement describes the function of the ACEs?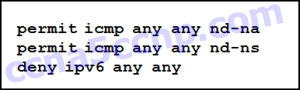 Correct
Correct
Incorrect
-
Question 6 of 23
6. Question
1 pointsWhen an inbound Internet-traffic ACL is being implemented, what should be included to prevent the spoofing of internal networks?Correct
Incorrect
-
Question 7 of 23
7. Question
1 pointsIn addition to the criteria used by extended ACLs, what conditions are used by a classic firewall to filter traffic?Correct
Incorrect
-
Question 8 of 23
8. Question
1 pointsA router has been configured as a classic firewall and an inbound ACL applied to the external interface. Which action does the router take after inbound-to-outbound traffic is inspected and a new entry is created in the state table?Correct
Incorrect
-
Question 9 of 23
9. Question
1 pointsIf the provided ACEs are in the same ACL, which ACE should be listed first in the ACL according to best practice?Correct
Incorrect
-
Question 10 of 23
10. Question
1 pointsA company is deploying a new network design in which the border router has three interfaces. Interface Serial0/0/0 connects to the ISP, GigabitEthernet0/0 connects to the DMZ, and GigabitEthernet/01 connects to the internal private network. Which type of traffic would receive the least amount of inspection (have the most freedom of travel)?Correct
Incorrect
-
Question 11 of 23
11. Question
1 pointsRefer to the exhibit. The ACL statement is the only one explicitly configured on the router. Based on this information, which two conclusions can be drawn regarding remote access network connections? (Choose two.) Correct
Correct
Incorrect
-
Question 12 of 23
12. Question
1 pointsConsider the following access list.access-list 100 permit ip host 192.168.10.1 any access-list 100 deny icmp 192.168.10.0 0.0.0.255 any echo access-list 100 permit ip any any Which two actions are taken if the access list is placed inbound on a router Gigabit Ethernet port that has the IP address 192.168.10.254 assigned? (Choose two.)Correct
Incorrect
-
Question 13 of 23
13. Question
1 pointsWhat is one benefit of using a stateful firewall instead of a proxy server?Correct
Incorrect
-
Question 14 of 23
14. Question
1 pointsWhat is one limitation of a stateful firewall?Correct
Incorrect
-
Question 15 of 23
15. Question
1 pointsWhen a Cisco IOS Zone-Based Policy Firewall is being configured via CLI, which step must be taken after zones have been created?Correct
Incorrect
-
Question 16 of 23
16. Question
1 pointsA network administrator is implementing a Classic Firewall and a Zone-Based Firewall concurrently on a router. Which statement best describes this implementation?Correct
Incorrect
-
Question 17 of 23
17. Question
1 pointsWhich two rules about interfaces are valid when implementing a Zone-Based Policy Firewall? (Choose two.)Correct
Incorrect
Hint
The rules for traffic transiting through the router are as follows: If neither interface is a zone member, then the resulting action is to pass the traffic. If both interfaces are members of the same zone, then the resulting action is to pass the traffic. If one interface is a zone member, but the other is not, then the resulting action is to drop the traffic regardless of whether a zone-pair exists. If both interfaces belong to the same zone-pair and a policy exists, then the resulting action is inspect, allow, or drop as defined by the policy. -
Question 18 of 23
18. Question
1 pointsWhich command will verify a Zone-Based Policy Firewall configuration?Correct
Incorrect
-
Question 19 of 23
19. Question
1 pointsRefer to the exhibit. The network “A” contains multiple corporate servers that are accessed by hosts from the Internet for information about the corporation. What term is used to describe the network marked as “A”?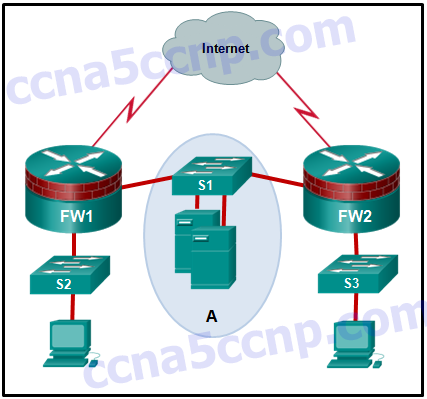 Correct
Correct
Incorrect
-
Question 20 of 23
20. Question
1 pointsWhich type of packet is unable to be filtered by an outbound ACL?Correct
Incorrect
-
Question 21 of 23
21. Question
1 pointsWhen a Cisco IOS Zone-Based Policy Firewall is being configured, which two actions can be applied to a traffic class? (Choose two.)Correct
Incorrect
-
Question 22 of 23
22. Question
1 pointsFill in the blank.- A (stateful) firewall monitors the state of connections as network traffic flows into and out of the organization.
Correct
Incorrect
-
Question 23 of 23
23. Question
1 pointsFill in the blank.- The (pass) action in a Cisco IOS Zone-Based Policy Firewall is similar to a permit statement in an ACL.
Correct
Incorrect

The question “Which two rules about interfaces are valid when implementing a Zone-Based Policy Firewall? (Choose two.)” officially requires two answers, but only one answer can be selected due to the radio buttons.
Fixed, thanks you