Assessment ESwitching Practice Final – CCNA 3 Exploration: LAN Switching and Wireless (Version 4.0)
1. Refer to the exhibit. After receiving a console notification on Switch2, the network administrator begins to troubleshoot the trunk link between Switch1 and Switch2. Which configuration change can be made to correct the problem with the trunk link?
- Set the Fa0/1 interface on Switch2 to trunk mode.
- Change the trunk encapsulation on Switch2 Fa0/1 to dot1q.
- Change the native VLAN on Switch2 interface Fa0/1 to VLAN 100.
- Change the access mode VLAN on Switch2 to the default VLAN 1.
2. Which two statements about a service set identifier (SSID) are true? (Choose two.)
- provides strong wireless security
- responsible for determining the signal strength
- tells a wireless device to which WLAN it belongs
- used to encrypt data sent across the wireless network
- all wireless devices on the same WLAN must have the same SSID
3. What is a possible impact of setting too short an aging time in the MAC address table of a switch?
- overly large address table
- unnecessary flooding of packets
- excessive timeouts of static addresses
- impaired ability to dynamically learn new addresses
4. Which three statements accurately describe VLAN types? (Choose three).
- A management VLAN is any VLAN that is configured to access management features of the switch.
- A data VLAN is used to carry VLAN management data and user-generated traffic.
- After the initial boot of an unconfigured switch, all ports are members of the default VLAN.
- An 802.1Q trunk port, with a native VLAN assigned, supports both tagged and untagged traffic.
- Voice VLANs are used to support user phone and e-mail traffic on a network.
- VLAN 1 is always used as the management VLAN.
5. Refer to the exhibit. Hosts B and C attempt to transmit a frame at the same time, but a collision occurs. Which hosts will receive the collision jamming signal?
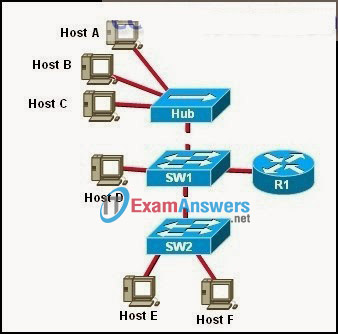
- all hosts that are shown
- only hosts B and C
- only hosts A, B, and C
- only hosts A, B, C, and D
- only hosts A, D, E, and F
- only hosts D, E, and F
6. Refer to the exhibit. Which password allows the administrator to enter the privileged exec mode?
- cisco1
- cisco2
- cisco3
- cisco
7. Refer to the exhibit. Which switch will be elected as the root bridge of the spanning tree topology?
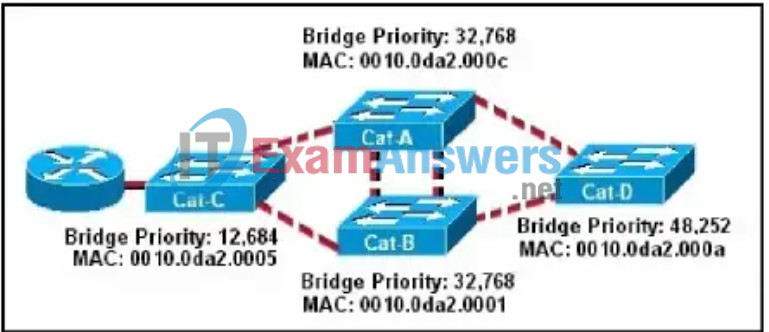
- Cat-A
- Cat-B
- Cat-C
- Cat-D
8. Refer to the exhibit. Host A is sending a frame to host C. How does switch SWA tag the frame?
- It tags the frame with VLAN 1 and sends it to host C.
- It tags the frame with VLAN 10 and sends it to host C.
- It tags the frame with VLAN 99 and sends it to host C.
- It does not tag the frame and sends it to host C.
9. Refer to the exhibit. What three statements describe why Host1 and Host2 are unable to communicate? (Choose three.)
- The switch ports are on different VLANs.
- The switch IP address is on the wrong subnet.
- The hosts are configured on different logical networks.
- A router is required to forward traffic between Host1 and Host2.
- The VLAN port assignments must be contiguous for each VLAN.
- The host default gateway addresses must be on the same logical network.
10. Which parameter is associated with wireless authentication?
- shared key
- SSID
- ad hoc
- channel
11. Which benefit is gained by designing a network with a small network diameter?
- lower latency
- improved security
- increased redundancy
- higher interface bandwidth
12. A network technician is investigating a problem on a switch that seems to have overflowing buffers and is dropping packets on many incoming ports. On examination the technician discovers that the problem exists because the destination port attaches to a busy server. What is the best way to address this problem?
- Increase the amount of RAM on the switch.
- Change the switch to a symmetric switch.
- Use a switch that uses store-and-forward switching.
- Change the switch to one that uses shared memory buffering.
13. Which switching method provides error-free data transmission?
- fragment-free
- fast-forward
- integrity-checking
- store-and-forward
14. When implementing a router-on-a-stick, what must be configured on the router to ensure connectivity between different VLANs?
- subinterfaces
- routing protocol
- switched virtual circuits
- dynamic trunking protocol
15. After unpacking a new Linksys WRT300N wireless multifunction device, a user needs to change the default administrator password and make other configuration changes. What must the user do to access the device in order to make these changes?
- Use a wireless client to associate with the WRT300N and then open a HyperTerminal session with the device.
- Establish a wired connection with the device and then reboot the attached computer to launch the configuration software.
- Establish a wired connection from a computer in the same IP subnet as the WRT300N and enter the default IP address of the device into a web browser on the computer.
- Modify the TCP/IP properties of the computer that is connected to the WRT300N so that the computer and the WRT300N exist on the same network. Then reboot the computer to establish a connection.
16. Which statement accurately describes routing between VLANs when the default gateway addresses of the VLANs are applied to physical interfaces.
- There is no bandwidth contention on the router interface.
- This solution will be less expensive than if subinterfaces are used.
- Trunking will be established between the router and switch ports.
- Only one physical router interface will be required for multiple VLANs.
17. Refer to the exhibit. After the listed commands are entered into router R1 and switch S1, PC1 and PC2 cannot ping each other. The network administrator enters the show interfaces trunk command and gets the results that are shown. What is the likely problem?
- The router has not been configured with a routing protocol.
- The trunk is established, but no VLANs have been configured to use it.
- The trunk has not been established because the switch port has not been configured for trunking.
- The switch, the router, or both must be configured with the dynamic desirable option for the Dynamic Trunking Protocol to establish a trunk.
18. Refer to the exhibit. Switch SW2 has been newly purchased and added to the network. What configuration should be applied to SW2 so that it participates in the same VTP domain as switch SW1, receives VLAN information from SW1, and synchronizes VLAN information?
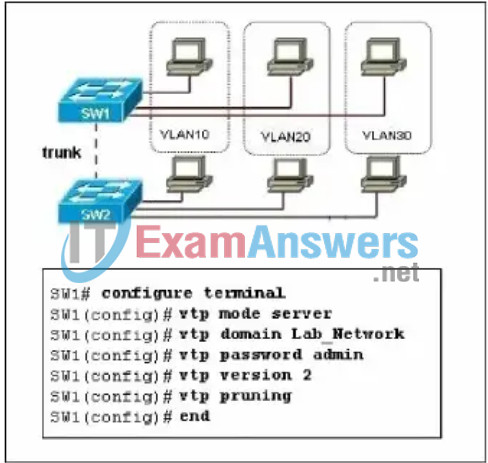
- Disable VTP pruning on SW2.
- Configure SW2 in VTP transparent mode.
- Configure SW2 with the VTP domain password.
- Configure SW2 as a VTP server with a higher revision number.
19. Refer to the exhibit. What is the purpose of the configuration commands that are shown?
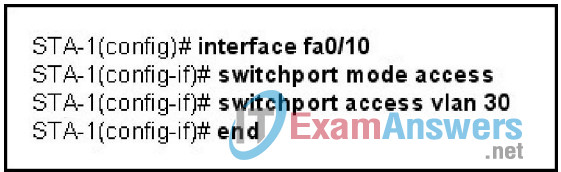
- to activate port Fa0/10
- to make the port a member of VLAN 30
- to activate port security on port Fa0/10
- to add VLAN 30 to the trunk that is connected to port Fa0/10
20. Refer to the exhibit. A network administrator needs to download a previously saved configuration file from the TFTP server to Switch1. Which command will accomplish this task?
- Switch1# copy tftp://192.168.0.253/backup-confg nvram:startup-config
- Switch1# copy tftp://192.168.0.254/backup-confg nvram:startup-config
- Switch1# copy nvram:startup-config tftp://192.168.0.253/backup-config
- Switch1# copy nvram:startup-config tftp://192.168.0.254/backup-config
21. Which layers should support QoS in a hierarchical network?
- only the access layer
- only the distribution and core layers
- only the access and distribution layers
- the access, distribution, and core layers
22. Refer to the exhibit. A company has acquired a new office in a campus environment. Switches in the existing office and the new office are directly connected by a trunk link. The VLANs and IP addressing are setup as shown in the exhibit. The computers in each office are not able to ping each other. What will fix the problem?
- Use an access link between S2 and S3.
- Connect S2 and S3 to a common router.
- Set the subnet mask in the new office to /24.
- Configure the new office default gateway to 172.17.10.1
- Change the port assignments in the new office to a different VLAN.
23. In the implementation of PVST+ in a specific VLAN where all switches have default spanning tree priorities, which spanning-tree command setting could be assigned to force one of the Catalyst switches to become and remain the root bridge?
- root primary
- priority 8192
- priority 2048
- spanning-tree mode rapid pvst
24. A network technician notes that ports Fa0/9 through Fa0/12 on a switch have been assigned to VLAN 40. VLAN 40, however, was improperly named and the technician deletes it. What happens to the ports that were assigned to VLAN 40?
- All ports will automatically become members of VLAN 1.
- The ports will automatically become members of the native VLAN.
- All VLAN 40 member ports will be unable to communicate with any other stations.
- All ports will remain assigned to VLAN 40 because it cannot be deleted if any ports are currently assigned to it.
25. Refer to the exhibit. What is true of the configuration of switch S1?
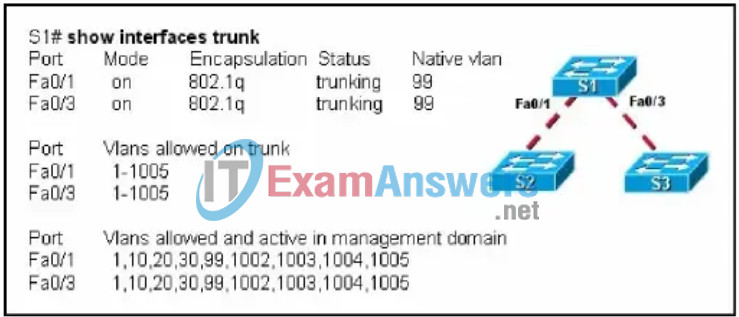
- A Cisco proprietary protocol is in use for ports Fa0/1 and Fa0/3.
- Switch ports Fa0/1 and Fa0/3 have been configured with the switchport mode access command.
- Untagged frames received on ports Fa0/1 and Fa0/3 will be placed on VLAN 1.
- Switch ports Fa0/1 and Fa0/3 are configured to carry data from multiple VLANs.
26. How are data frames identified and sent to the correct VLAN when exiting an Ethernet trunk?
- Frames are forwarded to the correct VLAN based on the VLAN tag.
- Frames are always forwarded to the native VLAN when exiting a trunk.
- Frames are forwarded to the correct VLAN based on the source IP address.
- Frames are forwarded to the correct VLAN based on information in the MAC address table.
27. Refer to the exhibit. What will allow a host that is connected to switch X in VLAN 10 to communicate with a host that is connected to switch Y in VLAN 10?
- QoS
- routing
- trunking
- VPN
- VoIP
- subinterfaces
28. What provides an authentication mechanism for 802.11-based wireless networks?
- DSSS
- OFDM
- SSID
- WPA
29. Which statement regarding the service password-encryption command is true?
- The service password-encryption command is entered at the privileged EXEC mode prompt.
- The service password-encryption command encrypts only passwords for the console and VTY ports.
- The service password-encryption command encrypts all previously unencrypted passwords in the running configuration.
- To see the passwords encrypted by the service password-encryption command, enter the no service password-encryption command.
30. Which STP port type can only appear once on a segment, and must be present in order for traffic to flow on that segment?
- non-root port
- disabled port
- designated port
- non-designated port
31. Refer to the exhibit. The switches are configured for VTP as shown. Which two statements correctly describe the operation of these switches? (Choose two.)
- A new VLAN can be added to Switch1 and that information will be added only to Switch2.
- A new VLAN can be added to Switch1 and that information will be added to Switch2 and Switch4.
- An existing VLAN can be deleted from Switch4 and that VLAN will be deleted from Switch1 and Switch2.
- An existing VLAN can be deleted from Switch2 and that VLAN will be deleted from Switch1 and Switch4.
- A new VLAN can be added to Switch4 and that information will be added to Switch1, Switch2, and Switch3.
- A new VLAN can be added to Switch3 and that information will be added to Switch1, Switch2, and Switch4.
32. Which statement correctly describes a function of a Layer 2 switch?
- It routes packets between different LAN segments.
- It uses the destination MAC address to selectively forward a frame.
- It performs switching and filtering based on the destination network layer address.
- It drops a frame whose destination MAC address is not in the MAC address table.
33. Which two statements describe Spanning Tree Protocol? (Choose two.)
- It is only used at Layer 2.
- It is configured on routers.
- It eliminates Layer 2 loops in network topologies.
- It limits the number of valid MAC addresses allowed on a port.
- It allows VLAN information to propagate to other switches in the network.
34. Refer to the exhibit. The network administrator configures both switches as displayed. However, host C is unable to ping host D and host E is unable to ping host F. What action should the administrator take to enable this communication?
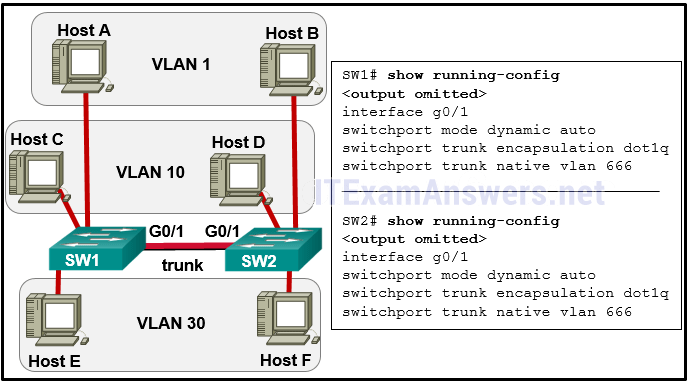
- Include a router in the topology.
- Associate hosts A and B with VLAN 10 instead of VLAN 1.
- Remove the native VLAN from the trunk.
- Configure one trunk port in the dynamic desirable mode.
- Add the switchport nonegotiate command to the configuration of S2.
35. Refer to the exhibit. Switch SW2 was tested in a lab environment and then inserted into a production network without reloading its configuration. After the trunk link between SW1 and SW2 was brought up, all users lost connectivity to the network. What could be the source of the problem?
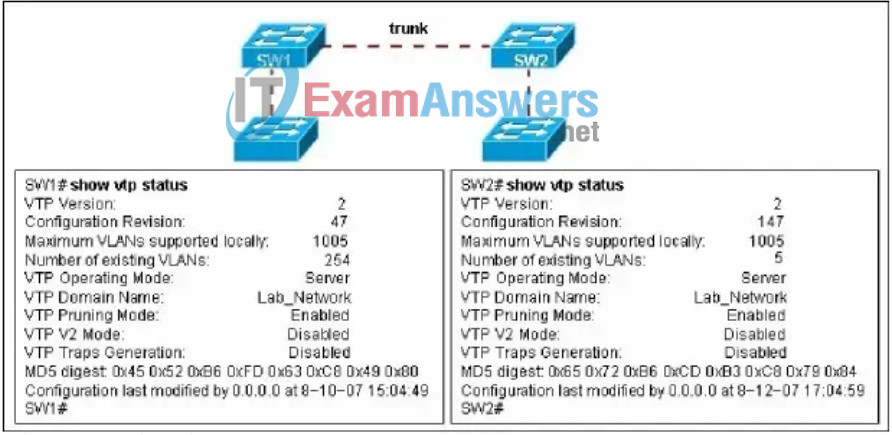
- All the VLANs were pruned from the trunk port between SW1 and SW2.
- SW1 and SW2 cannot be both set as VTP servers in the same VTP domain.
- VTP configuration revision number of SW2 was higher than the configuration revision number of SW1.
- The additional VLANs from SW2 created more VLANs than the VLAN database of SW1 could contain.
36. A network administrator enables sticky learning on all access mode interfaces of a Catalyst switch, saves the configuration, then connects hosts to the switch. After the switch operates for several days, the administrator reboots the switch without saving the running configuration. What is the result?
- All previously learned MAC addresses are lost.
- The switch reverts to non-sticky dynamic learning.
- Connected hosts are no longer able to communicate with the switch.
- Previously learned sticky addresses are retained in the switch configuration.
37. Refer to the exhibit. What is the result of issuing these commands?
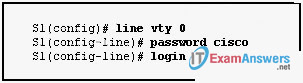
- The enable password will be set.
- The password will be set for the first Telnet connection.
- The password will be set for the console connection.
- The password will be set for the auxiliary connection.
38. Refer to the exhibit. Switch1 is configured for VTP as shown. An administrator connects four switches to Switch1 and configures trunk links between them. Which of the four switches will successfully receive and install VTP updates from Switch1?
- Option 4
39. A network administrator is implementing a Layer 2 solution for a legacy network that uses a combination of switches. Many of the older devices support only ISL trunking while others support both ISL and 802.1Q trunking. Which STP variant would be best suited for this network?
- RSTP
- MSTP
- PVST
- PVST+
40. Which type of frame contains information that is used in the election of the spanning tree root bridge?
- BID
- LSA
- LSU
- BPDU
41. Refer to the exhibit. Why must the NIC of host H1 operate in half-duplex mode?
- H1 must be able to detect collisions.
- All other hosts have been configured for half-duplex.
- The collision detect circuit on Switch1 has been disabled.
- Port Fa0/1 on Switch1 has been configured for half-duplex.
42. Refer to the graphic. In the Wireless menu option of a Linksys integrated router, what does the Network Mode option Mixed mean?
- The router supports encryption and authentication.
- The router supports both wired and wireless connections.
- The router supports 802.11b, 802.11g, and 802.11n devices.
- The router supports connectivity through infrared and radio frequencies.
43. Refer to the exhibit. What will happen when frames with a source address other than 0019.d2e4.d9f7 enters interface Fa0/24?
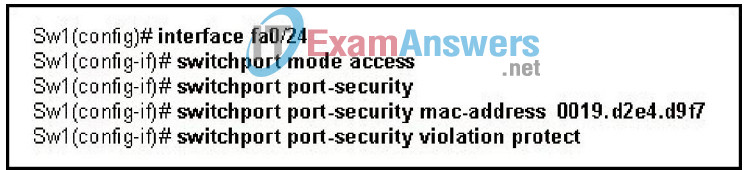
- Fa0/24 will become error-disabled.
- The incoming frames will be dropped.
- The Fa0/24 port LED will be turned off.
- The security violation count will be incremented.
44. Refer to the exhibit. The network administrator is planning five additional VLANs to be shared throughout the VTP domain on S3. What action should the administrator take before creating the additional VLANs?
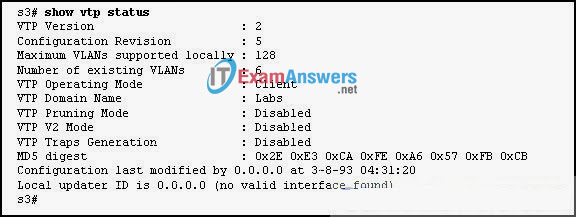
- Create the VLANs on a switch in VTP server mode and allow them to propogate to the other switches in the domain.
- Modify the configuration revision to 10 to support the additional VLANs.
- Enable the VTP pruning mode in order to create the VLANs on S3.
- Enable the VTP v2 mode.
45. Which statement correctly describes the spanning-tree path cost?
- It is calculated based on the total number of switches connected in a loop.
- It is calculated based on the utilization of all the switches along a given path.
- It is calculated based on the bridge priority of the switches along a given path.
- It is calculated based on the sum of the port cost value, determined by link speed, for each switch port along a given path.
46. Refer to the exhibit. A wireless infrastructure has been established in a company building as shown. The design goal was to allow roaming between the three APs for handheld devices. However, the devices lose connectivity when the users roam. How can this problem be fixed?
- Assign different SSIDs to each AP.
- Reconfigure all APs to the same channel.
- Use the same BSSID address for each AP.
- Reposition the APs so that each area of signal strength overlaps the neighbor by at least 10-15%.
47. Refer to the exhibit. Computer A sends a broadcast message. Which devices will see the broadcast?
- computer B
- computer B and Router1
- computer C and Router1
- computer B, computer D, computer E and Router1
- computer B, computer C, computer D, computer E and Router1
- computer A, computer B, computer C, computer D, computer E and Router1
48. Refer to the exhibit. The configuration steps that are listed in the exhibit have been entered in switch S1 via the console. Subsequent attempts to telnet to the switch are not successful. What is causing the problem?
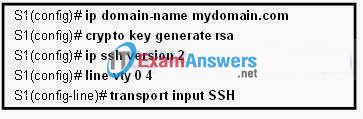
- The switch must be configured with SSH version 1.
- The transport input command must specify Telnet access.
- The RSA keys must be returned to zero before SSH will permit Telnet access.
- The ip domain-name command must also be entered in line configuration mode for the vty lines.
49. Refer to the exhibit. Switches SW3 and SW4 are brand new switches with default configurations. The links between the switches are configured as trunk links and all VLANs are allowed on the trunks. On the basis of the show running-config output that is provided, which VLANs will be available on SW3 and SW4?
- Option2
50. Which device must be installed in each computer to allow a wireless connection to be established?
- DSL modem
- wireless NIC
- wireless router
- wireless access point
