Time limit: 0
Quiz-summary
0 of 24 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
Information
Good luck!
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 24 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- Answered
- Review
-
Question 1 of 24
1. Question
1 pointsRefer to the exhibit. The Fa0/2 interface on switch S1 has been configured with the switchport port-security mac-address 0023.189d.6456 command and a workstation has been connected. What could be the reason that the Fa0/2 interface is shutdown?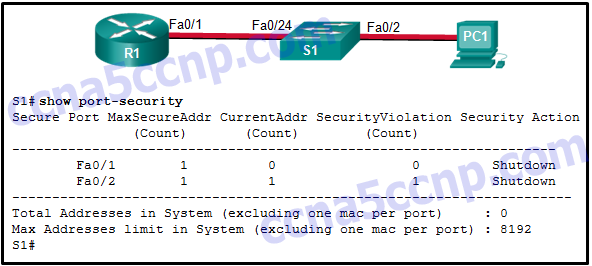 Correct
Correct
Incorrect
-
Question 2 of 24
2. Question
1 pointsTwo devices that are connected to the same switch need to be totally isolated from one another. Which Cisco switch security feature will provide this isolation?Correct
Incorrect
-
Question 3 of 24
3. Question
1 pointsWhich two functions are provided by Network Admission Control? (Choose two.)Correct
Incorrect
-
Question 4 of 24
4. Question
1 pointsWhich spanning-tree enhancement prevents the spanning-tree topology from changing by blocking a port that receives a superior BPDU?Correct
Incorrect
-
Question 5 of 24
5. Question
1 pointsWhich security feature should be enabled in order to prevent an attacker from overflowing the MAC address table of a switch?Correct
Incorrect
-
Question 6 of 24
6. Question
1 pointsIn what situation would a network administrator most likely implement root guard?Correct
Incorrect
-
Question 7 of 24
7. Question
1 pointsWhat component of Cisco NAC is responsible for performing deep inspection of device security profiles?Correct
Incorrect
-
Question 8 of 24
8. Question
1 pointsWhat is the role of the Cisco NAC Manager in implementing a secure networking infrastructure?Correct
Incorrect
-
Question 9 of 24
9. Question
1 pointsWhat is the role of the Cisco NAC Server within the Cisco Secure Borderless Network Architecture?Correct
Incorrect
-
Question 10 of 24
10. Question
1 pointsWhat is the role of the Cisco NAC Guest Server within the Cisco Borderless Network architecture?Correct
Incorrect
-
Question 11 of 24
11. Question
1 pointsWhich three functions are provided under Cisco NAC framework solution? (Choose three.)Correct
Incorrect
-
Question 12 of 24
12. Question
1 pointsWhich feature is part of the Antimalware Protection security solution?Correct
Incorrect
-
Question 13 of 24
13. Question
1 pointsWhat security countermeasure is effective for preventing CAM table overflow attacks?Correct
Incorrect
-
Question 14 of 24
14. Question
1 pointsWhat is the behavior of a switch as a result of a successful CAM table attack?Correct
Incorrect
-
Question 15 of 24
15. Question
1 pointsWhat additional security measure must be enabled along with IP Source Guard to protect against address spoofing?Correct
Incorrect
-
Question 16 of 24
16. Question
1 pointsWhat are three techniques for mitigating VLAN hopping attacks? (Choose three.)Correct
Incorrect
-
Question 17 of 24
17. Question
1 pointsWhat two mechanisms are used by Dynamic ARP inspection to validate ARP packets for IP addresses that are dynamically assigned or IP addresses that are static? (Choose two.)Correct
Incorrect
-
Question 18 of 24
18. Question
1 pointsWhat protocol should be disabled to help mitigate VLAN hopping attacks?Correct
Incorrect
-
Question 19 of 24
19. Question
1 pointsWhat network attack seeks to create a DoS for clients by preventing them from being able to obtain a DHCP lease?Correct
Incorrect
-
Question 20 of 24
20. Question
1 pointsWhat is the only type of port that an isolated port can forward traffic to on a private VLAN?Correct
Incorrect
-
Question 21 of 24
21. Question
1 pointsWhich STP stability mechanism is used to prevent a rogue switch from becoming the root switch?Correct
Incorrect
-
Question 22 of 24
22. Question
1 pointsHow can a user connect to the Cisco Cloud Web Security service directly?Correct
Incorrect
-
Question 23 of 24
23. Question
1 pointsWhat security benefit is gained from enabling BPDU guard on PortFast enabled interfaces?Correct
Incorrect
-
Question 24 of 24
24. Question
1 pointsFill in blanks- DHCP (snooping) is a mitigation technique to prevent rogue DHCP servers from providing false IP configuration parameters.
Correct
Incorrect
