Packet Tracer – Skills Integration Challenge
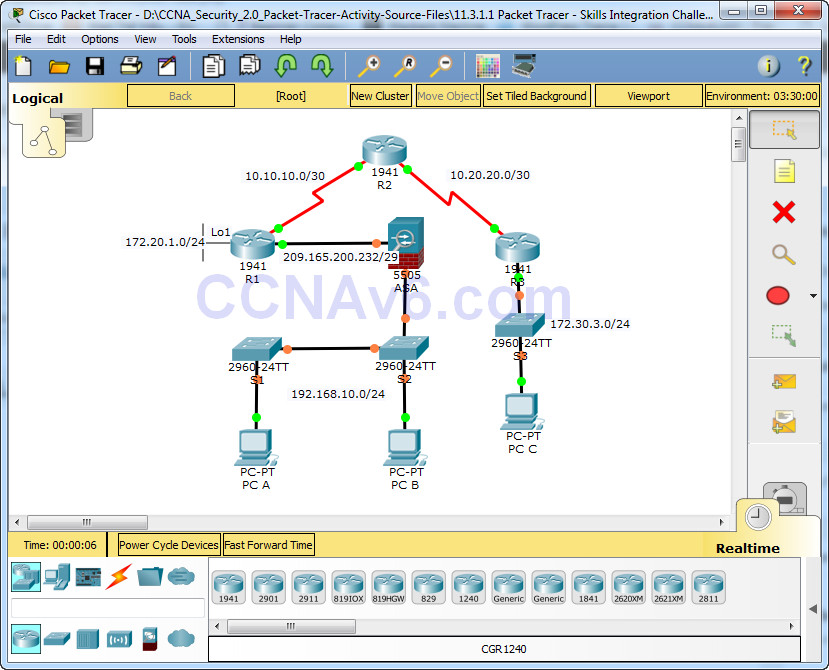
Topology
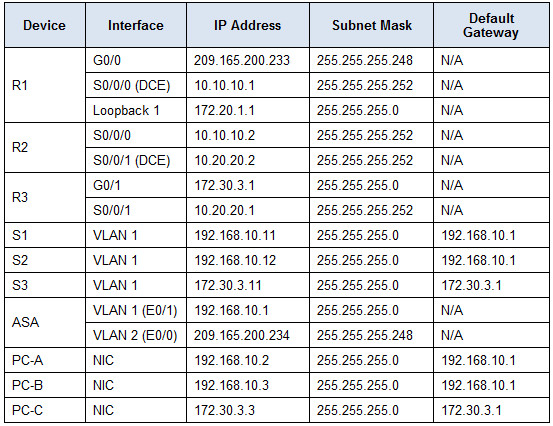
Addressing Table
Objectives
• Configure basic router security
• Configure basic switch security
• Configure AAA local authentication
• Configure SSH
• Secure against login attacks
• Configure site-to-site IPsec VPNs
• Configure firewall and IPS settings
• Configure ASA basic security and firewall settings
Scenario
This culminating activity includes many of the skills that you have acquired during this course. The routers and switches are preconfigured with the basic device settings, such as IP addressing and routing. You will secure routers using the CLI to configure various IOS features, including AAA, SSH, and Zone-Based Policy Firewall (ZPF). You will configure a site-to-site VPN between R1 and R3. You will secure the switches on the network. In addition, you will also configure firewall functionality on the ASA.
Requirements
Note: Not all security features will be configured on all devices, however, they would be in a production network.
Configure Basic Router Security
• Configure the following on R1:
º Minimum password length is 10 characters.
º Encrypt plaintext passwords.
º Privileged EXEC mode secret password is ciscoenapa55.
º Console line password is ciscoconpa55, timeout is 15 minutes, and console messages should not interrupt command entry.
º A message-of-the-day (MOTD) banner should include the word unauthorized.
• Configure the following on R2:
º Privileged EXEC mode secret password is ciscoenapa55.
º Password for the VTY lines is ciscovtypa55, timeout is 15 minutes, and login is required.
Configure Basic Switch Security
• Configure the following on S1:
º Encrypt plaintext passwords.
º Privileged EXEC mode secret password is ciscoenapa55.
º Console line password is ciscoconpa55, timeout is 5 minutes, and consoles messages should not interrupt command entry.
º Password for the VTY lines is ciscovtypa55, timeout is 5 minutes, and login is required.
º An MOTD banner should include the word unauthorized.
• Configure trunking between S1 and S2 with the following settings:
º Set the mode to trunk and assign VLAN 99 as the native VLAN.
º Disable the generation of DTP frames.
• Configure the S1 with the following port settings:
º F0/6 should only allow access mode, set to PortFast, and enable BPDU guard.
º F0/6 uses basic default port security with dynamically learned MAC addresses added to the running configuration.
º All other ports should be disabled.
Note: Although not all ports are checked, your instructor may want to verify that all unused ports are disabled.
Configure AAA Local Authentication
• Configure the following on R1:
º Create a local user account of Admin01, a secret password of Admin01pa55, and a privilege level of 15.
º Enable AAA services.
º Implement AAA services using the local database as the first option and then the enable password as the backup option.
Configure SSH
• Configure the following on R1:
º The domain name is ccnasecurity.com
º The RSA key should be generated with 1024 modulus bits.
º Only SSH version 2 is allowed.
º Only SSH is allowed on VTY lines.
• Verify that PC-C can remotely access R1 (209.165.200.233) using SSH.
Secure Against Login Attacks
• Configure the following on R1:
º If a user fails to log in twice within a 30-second time span, disable logins for one minute.
º Log all failed login attempts.
Configure Site-to-Site IPsec VPNs
Note: Some VPN configurations are not scored. However, you should be able to verify connectivity across the IPsec VPN tunnel.
• Enable the Security Technology package license on R1.
º Save the running configuration before reloading.
• Configure the following on R1:
º Create an access list to identify interesting traffic on R1.
º Configure ACL 101 to allow traffic from the R1 Lo1 network to the R3 G0/1 LAN.
• Configure the crypto isakmp policy 10 Phase 1 properties on R1 and the shared crypto key ciscovpnpa55. Use the following parameters:
º Key distribution method: ISAKMP
º Encryption: aes 256
º Hash: sha
º Authentication method: pre-shared
º Key exchange: DH Group 5
º IKE SA lifetime: 3600
º ISAKMP key: ciscovpnpa55
• Create the transform set VPN-SET to use esp-aes 256 and esp-sha-hmac. Then create the crypto map CMAP that binds all of the Phase 2 parameters together. Use sequence number 10 and identify it as an ipsec-isakmp map. Use the following parameters:
º Transform set: VPN-SET
º Transform encryption: esp-aes 256
º Transform authentication: esp-sha-hmac
º Perfect Forward Secrecy (PFS): group5
º Crypto map name: CMAP
º SA establishment: ipsec-isakmp
º Bind the crypto map (CMAP) to the outgoing interface.
• Verify that the Security Technology package license is enabled. Repeat the site-to-site VPN configurations on R3 so that they mirror all configurations from R1.
• Ping the Lo1 interface (172.20.1.1) on R1 from PC-C. On R3, use the show crypto ipsec sa command to verify that the number of packets is more than 0, which indicates that the IPsec VPN tunnel is working.
Configure Firewall and IPS Settings
• Configure a ZPF on R3 using the following requirements:
º Create zones named IN-ZONE and OUT-ZONE.
º Create an ACL number 110 that defines internal traffic, which permits all IP protocols from the 172.30.3.0/24 source network to any destination.
• Create a class map named INTERNAL-CLASS-MAP that uses the match-all option and ACL 110.
• Create a policy map named IN-2-OUT-PMAP that uses the class map INTERNAL-CLASS-MAP to inspect all matched traffic.
• Create a zone pair named IN-2-OUT-ZPAIR that identifies IN-ZONE as the source zone and OUT-ZONE as the destination zone.
º Specify that the IN-2-OUT-PMAP policy map is to be used to inspect traffic between the two zones.
º Assign G0/1 as an IN-ZONE member and S0/0/1 as an OUT-ZONE member.
• Configure an IPS on R3 using the following requirements:
Note: Within Packet Tracer, the routers already have the signature files imported and in place. They are the default XML files in flash. For this reason, it is not necessary to configure the public crypto key and complete a manual import of the signature files.
º Create a directory in flash named ipsdir and set it as the location for IPS signature storage.
º Create an IPS rule named IPS-RULE.
º Retire the all signature category with the retired true command (all signatures within the signature release).
º Unretire the IOS_IPS Basic category with the retired false command.
º Apply the rule inbound on the S0/0/1 interface.
Configure ASA Basic Security and Firewall Settings
• Configure VLAN interfaces with the following settings:
º For the VLAN 1 interface, configure the addressing to use 192.168.10.1/24.
º For the VLAN 2 interface, remove the default DHCP setting and configure the addressing to use 209.165.200.234/29.
• Configure hostname, domain name, enable password, and console password using the following settings:
º The ASA hostname is CCNAS-ASA.
º The domain name is ccnasecurity.com.
º The enable mode password is ciscoenapa55.
• Create a user and configure AAA to use the local database for remote authentication.
º Configure a local user account named admin with the password adminpa55. Do not use the encrypted attribute.
º Configure AAA to use the local ASA database for SSH user authentication.
º Allow SSH access from the outside host 172.30.3.3 with a timeout of 10 minutes.
• Configure the ASA as a DHCP server using the following settings:
º Assign IP addresses to inside DHCP clients from 192.168.10.5 to 192.168.10.30.
º Enable DHCP to listen for DHCP client requests.
• Configure static routing and NAT.
º Create a static default route to the next hop router (R1) IP address.
º Create a network object named inside-net and assign attributes to it using the subnet and nat commands.
º Create a dynamic NAT translation to the outside interface.
• Modify the Cisco Modular Policy Framework (MPF) on the ASA using the following settings:
º Configure class-map inspection_default to match default-inspection-traffic, and then exit to global configuration mode.
º Configure the policy-map list global_policy. Enter the class inspection_default and enter the command to inspect icmp. Then exit to global config mode.
º Configure the MPF service-policy to make the global_policy apply globally.

failed
no password
you can enter for password
For accesslist 110 on R3 try this script
conf t
no access-list 110
access-list 110 permit ip 172.30.3.0 0.0.0.255 any
I did this but I only got 98 percent when I checked the result it says the only thing that’s wrong is under R3 and the ACL 110 wasn’t applied i need help ASAP
Try putting only this, without the implicit deny ip any any statement:
access-list 110 permit ip 172.30.3.0 0.0.0.255 any
It checks out as correct in the Assessment items for access list 110 on R3.