3.3.2.5 Packet Tracer – Threat Modeling at the IoT Device Layer (Instructor Version)
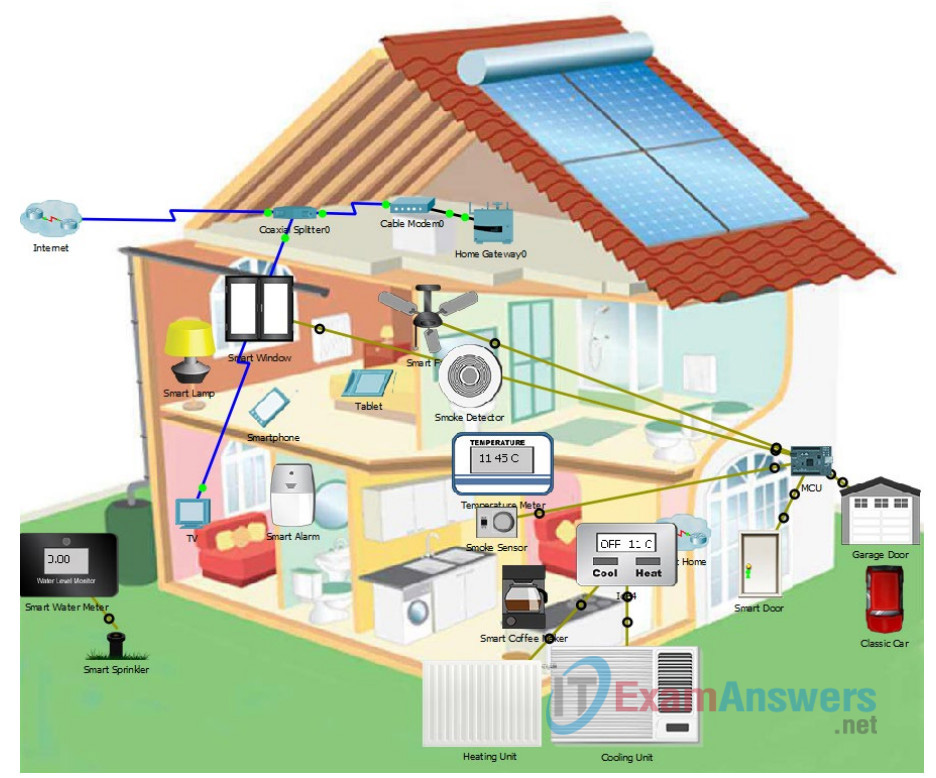
Topology
The topology is a home IoT system that has been prototyped in Packet Tracer. It shows a cutaway view of a home with different sensors, actuators, and connections shown.
Objectives
In this Packet Tracer, you will begin the threat modeling process for the device layer of the IoT attack surface.
- Part 1: Identifying the Security Objectives
- Part 2: Exploring and Diagraming the Physical Network
- Part 3: Creating an Inventory of Assets of the Physical Device Attack Surface
- Part 4: Identifying Potential Threats with the STRIDE Model
Background / Scenario
A home owner has been reading about the IoT and is very enthusiastic about the capabilities of home automation IoT systems. The home owner wants to install such a system in his house but does not know how to do so. He has contacted a company that can design and install the system. The company focuses on security throughout the system design, provisioning, and development process. They are currently developing a threat model for the system. You have been hired by the company and your first task is to complete the threat model.
The house is 3500 sq. ft. and includes two stories and an attic. The customers are away from home regularly and have requested the safest house possible. The customer wants to be able to remotely monitor the house and wants the following IoT-supported systems:
- Climate control
- Smoke / fire
- Temperature issues out of the normal range
- Door and window locks
- Lawn watering
- Local alarm and emergency department messaging
The system should be controllable locally and through the cloud. The user should be able to access the controller from a web browser from inside the network as well as remotely through a smartphone app. This will allow the customers to monitor or control the system when they are away.
The system should collect and store data from the remote sensors and various actions should take place based on the input from those sensors. For example, if the temperature goes above the maximum range, it probably means the AC is not working and someone needs to be notified ASAP. If the system detects smoke, the local alarm should sound, and the customer and the fire department should be alerted. Data from the system should be retained and analyzed. In addition, the customer should be able to change the threshold values that trigger different actuators and events as necessary, either locally or through the mobile app. The triggers and behaviors, data analytics, and remote-control access are all available through a home automation cloud application service that the system will interface with.
The home owners should have password protected accounts for access to the system. In addition, the company should have access to system diagnostics in case problems occur with the system. Only the homeowner should have access to the cloud applications.
It is also important to make note of these other details of the house:
- 3 bedrooms, 1 den, 2 baths
- 2 stories and an attic
- 1 main front door and 1 side door entry
- 2 sliding doors to the backyard – one coming from the master bedroom
- 2-car garage
The team has designed the system and it is your job to perform threat modeling on the design.
You will start by creating a threat model for system. The home automation system has been prototyped in Packet Tracer. The system is very similar to the home IoT system that you explored earlier in the course. Because the threat modeling process is very detailed, we will be breaking it up into four linked labs. The first three labs are for each layer of the IoT attack surface. In the final Packet Tracer, you will rate the risks and determine how the risks will be managed.
Required Resources
- Packet Tracer 7.1 or later
Part 1: Identifying the Security Objectives
The first activity in the threat modeling process is to establish the security objectives for the system.
Step 1: Provide objectives for each of the six categories.
There are six categories of security objectives that are often used to define the security needs of a system or organization. Answer the questions to help develop these objectives. Answer the questions from the point of view of both the company and the customer, where appropriate.
Identity
Visualize the application and identify the security objectives of this system based on the requirements.
What access and authorization controls should be in place to document who is accessing the IoT system?
Access to network resources should be placed and adjusted according to the necessary criteria because they should not be accessible to anyone, and these should be living documents, that is, frequently updated.
Should there be any machine-to-machine (M2M) access controls in place?
If it is only used for data, it is a good idea to implement it, and aside from that, these do not consume a large amount of bandwidth.
Financial
Document the financial losses that could occur due to a failure of the system, system components, or security breech.
What is the potential financial impact to the customer if components of the system malfunction?
There would be a significant financial loss because the data is extremely valuable, and any failure would result in wasted time attempting to repair the system’s failure.
If a threat actor was able to gain access to the home network in a security breech, what losses could occur?
A threat actor which gains access to a home network in a security breech makes the system vulnerable thus giving access to certain information for the attacker. The information stolen will be used depending on the motivation of the attacker. The attacker can publicize the attacked to show how vulnerable a system built by a certain organization. This will lead to bad publicity, possible loss of customer, and eventually financial crisis. The stolen credentials of an individual can be use to harvest contacts for phishing purpose and identity theft which may lead to possible financial losses. Others might use this stolen information to conduct exploitation or campaign espionage and use personal, financial, and medical information as to gain other types of intelligence. We can therefore conclude that possible security breech in one’s network will greatly impact to the safety of the individual’s information leading to financial losses and worst one’s own life depending on information and motivation of the person behind the attack.
Reputation
Document any possible impact on the customer’s reputation if the IoT safety/security system is attacked.
What would be the repercussions for the owner if their home-based safety/security system was attacked?
Yes, because your privacy has been violated.
Privacy and Regulation
Document the impact of any privacy concerns as well as regulation requirements for this system.
Are there any privacy concerns for any of the data collected or used by this system?
If we communicate with the data but the coffee maker or temperature meter does not, it can become somewhat irrelevant. However, there may be a risk to the data collected, such as the cell phone or modem.
Does the owner care that logs are being kept about their access and movement throughout the house (motion sensors)?
YES, Because the main purpose of motion sensor is to sense an intruder and send an alert to your control panel, which alerts your monitoring center. Sensors work when you’re not home or when you tell the system you are not there.
Identify any data that could cause privacy concerns for the owner of this system.
The house sensors
Availability Guarantees
Document the expected availability and guaranteed uptime of the IoT system. Is this system required to be available at all times?
Definitely necessary, because the system must be “living.”
Is there any acceptable downtime that can be tolerated for this system? Explain.
No, not really, because it is a home system that must be turned on.
Safety
Document the potential impacts to physical welfare of people and physical damage to equipment and facilities. This is particularly important in industrial control system (ICS) environments.
Of course, because it is associated with instruments used for industrial process control.
Part 2: Exploring and Diagraming the Physical Network
Step 1: Open the Packet Tracer Network.
The Packet Tracer network is an interactive demonstration of a home automation IoT network. It is the same network that was used in Chapter 1.
a. Open the Packet Tracer – Threat Modeling at the IoT Device Layer.pka file.
b. Follow the instructions to become familiar with some of the functions of the network if you do not know how it works.
c. Feel free to explore the network further.
Step 2: Diagram the network.
Use the blank floor plans that are included in Appendix A of the PDF version of these Packet Tracer instructions. Diagram the IoT devices on the floor plan. Place the sensors, actuators, and devices at the locations on the floor plan that seem to match the PT network. Label each device.
Part 3: Creating an Inventory of Assets of the Physical Device Attack Surface
You will now complete an inventory of the devices in the IoT network by entering them into a table.
Step 1: List all the assets.
Fill in the table that is provided in Appendix B of this Packet Tracer with all the IoT device physical assets
that are part of the home automation network. Also add the device role.
What are some roles that devices can take in an IoT network?
Tracking and monitoring of assets.
Traceability control through smart labels.
Automation of manual processes
Obtaining relevant data
Step 2: Determine the interactions between assets.
Continue to work in the table from Step 1. Fill-in the relationships between the devices in the Works With column. Which sensors and actuators work together?
| Device | Device Role | Works With |
|---|---|---|
| Part 1: Physical Device | ||
| Smoke Sensor | Smoke control | Sensor |
| Smart Window | Open Automatically | Actuator |
| Smoke Detector | Check smoke levels in the home | Sensor and actuator |
| Smart alarm | Turn on in an emergency | Actuator |
| Temperature Gauge | Measures house temperature | Sensor |
| Water Meter | Measure the amount of water | Sensor and Actuator |
| Smart Sprinkle | Water Sprinkle | Actuator |
| Smart Solar Panel | Electric Power | Sensor and Actuator |
| Smart Door | Main door lock | Actuator |
| Smart Battery | Current | Sensor |
| Smart Fan | Ventilation | Sensor and Actuator |
| Thermostat | Open or close electrical circuits of the temperature | Sensor and Actuator |
| Garage Door | Garage lock | Sensor and Actuator |
| Smart Lamp | Remotely turn on | Actuator |
| Air Conditioning | Turn on remotely and reduce humidity by 2% per hour and cool | Sensor |
| Smart Coffee Maker | Remotely turn on | Actuator |
Part 4: Identifying Potential Threats with the STRIDE Model
In this part, you will identify threats using the STRIDE methodology. Try to describe as many threats as possible based on your experience in the course, the OWASP IoT vulnerabilities page, and other information sources.
Use the STRIDE model to create a list of potential threats
Complete this table with threats for each category in the STRIDE threat model. Add potential threats that could occur for each STRIDE category. Include the type of threat using the OWASP terminology where possible.
| Threat type | Asset type | Threats |
|---|---|---|
| (S)poofing – can an attacker pretend to be someone he is not, or falsify data? | Sensors | People are being watched and their privacy is being invaded. |
| Actuators | Smart device electrical failures or breakdowns | |
| (T)ampering – can an attacker successfully inject falsified data into the system? | Sensors | You can modify the detector values for your malicious targets. |
| Actuators | You can make a device do something because the sensor, for example, can change the values and do something completely different. | |
| (R)epudiation – can a user pretend that a transaction did not happen? | Sensors | If you can prevent the sensors from detecting a particular object. |
| Actuators | As a result, the actuators would be unable to finish the job. | |
| (I)nformation Disclosure – can the device leak confidential data to unauthorized parties? | Sensors | They can detect when the ventilation system is turned on, for example, indicating the presence of the owners. |
| Actuators | They can take the data from the sensor and put it to their own creative use. | |
| (D)enial of Service – can the device be shut down or made unavailable maliciously? | Sensors | If an attack can disable it and it is unable to detect anything. |
| Actuators | It can be switched off in the same manner it can’t finish its job. | |
| (E)scalation of Privilege – can users get access to privileged resources meant only for admins or superusers? | Sensors | You can access the network from a sensor connected to it, where all the devices are located, and have total control and relevant information. |
| Actuators | In the same way that the sensor can duplicate the same concept in these devices. |
Appendix A: Floor Plans
Ground floor
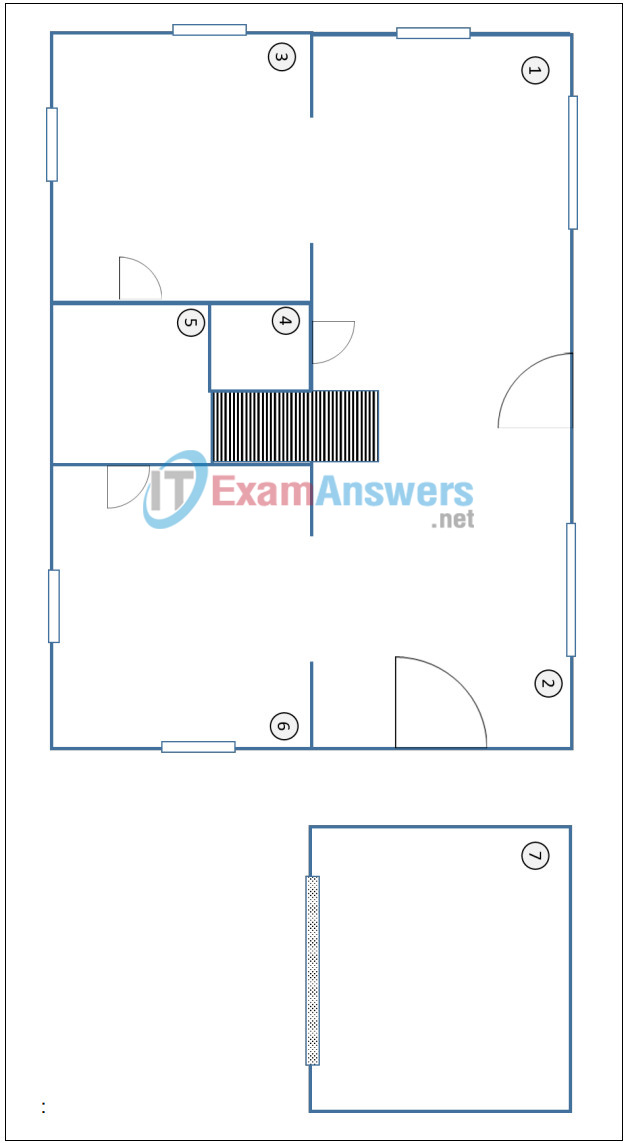
Ground Floor Legend:
| Number | Room |
|---|---|
| 1 | living room |
| 2 | dining room |
| 3 | TV room |
| 4 | closet |
| 5 | bathroom |
| 6 | kitchen |
| 7 | garage |
Upper Floor:
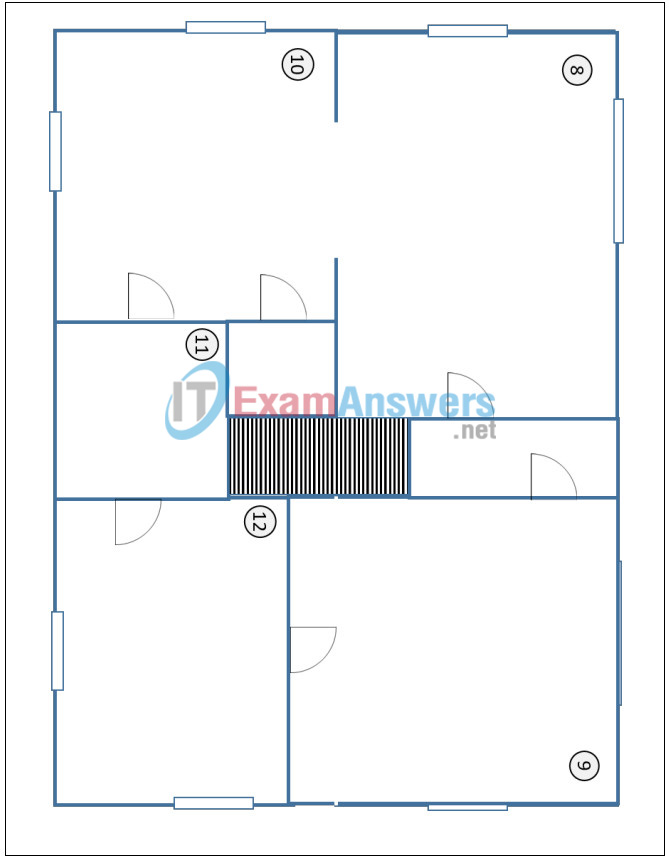
Upper Floor Legend:
| Number | Room |
|---|---|
| 8 | bedroom |
| 9 | bedroom |
| 10 | bedroom |
| 11 | closet |
| 12 | bathroom |
Appendix B: Asset Table
| Device | Device Role | Works With… |
|---|---|---|
| Part 1: Physical Device | ||
| Smart Coffee Maker | Remotely turn on | Actuator |
| Smart Lamp | Remotely turn on | Actuator |
| Smart Sprinkle | Water Sprinkle | Actuator |
| Smart Door | Main door lock | Actuator |
| Smart Window | Open Automatically | Actuator |
| Smart alarm | Turn on in an emergency | Actuator |
| Smoke Sensor | Smoke control | Sensor |
| Temperature Gauge | Measure house temperature | Sensor |
| Smart Battery | current | Sensor |
| Air Conditioning | Turn on remotely and reduce humidity by 2% per hour and cool | Sensor |
| Smoke Detector | Check smoke levels in the home | Sensor and actuator |
| Water Meter | Measure the amount of water | Sensor and Actuator |
| Smart Solar Panel | Electric Power | Sensor and Actuator |
| Smart Fan | Ventilation | Sensor and Actuator |
Appendix C: STRIDE Table
| Threat type | Asset type | Threats |
|---|---|---|
| (S)poofing – can an attacker pretend to be someone he’s not or falsify data? | Sensors | People’s privacy is being infringed upon because they are being monitored. |
| Actuators | Smart device electrical failures or breakdowns | |
| (T)ampering – can an attacker successfully inject tampered data into the system? | Sensors | You can modify the detector values for your malicious targets. |
| Actuators | You can make a device do something because the sensor, for example, can change the values and do something completely different. | |
| (R)epudiation – can a user pretend that a transaction didn’t happen? | Sensors | if you can prevent the sensors from detecting a particular object. |
| Actuators | As a result, the actuators would be unable to finish the job. | |
| (I)nformation Disclosure – can the application leaking confidential data to unauthorized parties? |
Sensors | They can detect when the ventilation system is turned on, for example, indicating the presence of the owners. |
| Actuators | They can take the data from the sensor and put it to their own creative use. | |
| (D)enial of Service – can the device be shut down or made unavailable maliciously? | Sensors | If an attack can disable it and it is unable to detect anything |
| Actuators | It can be switched off in the same manner it can’t finish its job. | |
| (E)scalation of Privilege – can users get access to privileged resources meant only for admins or superusers? | Sensors | You can access the network from a sensor connected to it, where all the devices are located, and have total control and relevant information. |
| Actuators | In the same way that the sensor can duplicate the same concept in these devices. |
Download 3.3.2.5 Packet Tracer – Threat Modeling at the IoT Device Layer
