7.3.4 Lab – Risk Analysis (Answers)
Objectives
Part 1: Use Risk Analysis Methods
Part 2: Calculate Risks
Background / Scenario
A risk analysis determines possible vulnerabilities and threats, their likelihood and consequences, and the tolerances for such events. The results of this process may be expressed by using a quantitative method or a qualitative method. Quantitative risk analysis involves calculations to assign a value to a potential vulnerability or threat. This option works best when dealing with tangible assets such as buildings, computers, or inventory. Qualitative risk analysis assigns a level used to prioritize potential risk so organizations can take a logical approach to address the most critical threats. This method works best for intangible assets such as intellectual property, company reputation, or accounts receivable.
Required Resources
PC or mobile device with internet access
Instructions
Part 1: Use Risk Analysis Methods
Quantitative Risk
Quantitative risk analysis is the process of objectively determining the impact of an event by using metrics and models. A quantitative analysis relies on historical information and trends to predict future performance. The result of the analysis is a value.
Calculating the annualized loss expectancy (ALE) is a common method to estimate the decrease in value or capability of an asset after an adverse event occurs.
Step 1: Calculate the Asset Value.
In this step, you will demonstrate how to calculate the asset value.
Initial Cost of the Asset
The asset value is the total expenditure it takes to replace an asset. For example, the total value of an asset may include purchasing and licensing or developing along with maintenance and support costs. In this example, the organization’s customer database server cost approximately $20,000. This includes the hardware, software, and configuration.
Organizational Value
An intangible value is more difficult to calculate because it may include the cost of creating, acquiring, and recreating information, and the business impact or loss if the information is lost or compromised. It can also include liability costs. In this example, the cost to create the customer website is $40,000.
Public Value
An intangible cost that includes loss of proprietary information, or processes, or loss of business reputation. This value is estimated at $75,000.
Questions:
What is the total asset value of the server?
The server’s tangible and intangible value is approximately $135,000.
Why is the intangible cost so high? Is this realistic?
Consider the value of an organization’s reputation. The reputation of a business is very difficult to build and maintain. Damage to the reputation can be very costly and permanent. So – yes, this valuation is realistic.
Step 2: Calculate the Exposure Factor
Exposure factor is expressed as a percentage (or decimal equivalent) loss of an asset if a specific threat or vulnerability is realized. The exposure factor is a subjective value. If the asset is completely lost, the exposure factor would be 100% or 1. The exposure factor could be a fraction of the value such as 40% or .4, for example.
Question:
Given an example, what is the impact on the server if the server room floods and the cost to restore the server is $30,000?
Asset Value: $135,000
Restoration Cost: $30,000
Exposure Factor:
Exposure factor is 30,000 / 135,000 = 22% or 0.22
Step 3: Calculate the Single Loss Expectancy
Calculate the single loss expectancy (SLE) by taking the asset value and multiplying it by the exposure factor. The result is the dollar loss that you expect due to the occurrence of a single event. A single asset can have multiple potential threats or vulnerabilities, and a single loss expectancy can be calculated for each occurrence.
For example, a denial-of-service attack is estimated to have a 20% or 0.2 impact or exposure factor. This would mean the SLE is $135,000 x 0.2 = $27,000.
Estimate the SLE if a hard drive or storage unit failure occurs where the same asset value is estimated at $135,000. This type of loss would result in an exposure factor of 0.5.
Questions:
What is the SLE?
SLE equals 135,000 x 0.5 = $67,500
Calculate the SLE of a Ransomware attack with an exposure facture of 100% or 1.0.
SLE equals 135,000 x 1.0 = $135.000
Step 4: Calculate the Annualized Rate of Occurrence
The annualized rate of occurrence (ARO) is a measure of how often an event occurs in a single year. ARO is always expressed in an annual rating even if an incident occurs and is recorded in other time measures. In our example, the customer database server is impacted by a DoS or DDoS attack every 120 days or 4 months on average. This means the event will occur three times in a calendar year on average, so the DoS/DDoS attack has an ARO of 3.
a. In this scenario, calculate the ARO of a ransomware attack on the business customer database server. On average the server experiences a ransomware attacks every 24 months or two years.
Question:
What is the ARO of a ransomware attack on the customer database server?
If the event occurs every twenty-four months, the ARO would be 12 / 24 = 0.5.
b. In this scenario, calculate the ARO of a hardware failure with the customer database server. On average, the server experiences hardware failures every 30 months.
Question:
What is the ARO of hardware failures with the customer database server?
If the event occurs every thirty months, the ARO would be 12 / 30 = 0.4.
Step 5: Calculate the Annualized Loss Expectancy
The annualized loss expectancy (ALE) is the product of the ARO and the SLE. To calculate the ALE, take the SLE and multiply it by the ARO. For example, if a power outage is determined to have an SLE of $50,000.00 and an ARO of 0.5 the ALE would be $25,000.
Questions:
What is the ALE of a hardware failure with the customer database server if the SLE= $5,000 and ARO=2.5?
Answer: ALE = 5000 x 2.5 = 12500
What is the ALE of a hacking attack with the customer database server if the SLE= $10,000 and ARO=0.5?
Answer: ALE = 10,000 x 0.5 = 5,000
Step 6: Calculate the Qualitative Risk Analysis
A qualitative analysis compares the impact of a threat with the probability of its occurrence and uses labels such as low, medium, or high. The impact of an event is a measure of the loss when a threat exploits a vulnerability. The probability is the chance that the threat event will occur.
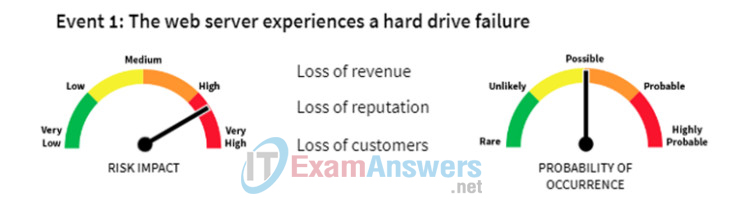
Qualitative risk analysis examines the level of overall impact on the organization. These issues include loss of revenue, loss of reputation, and loss of customers.
Use the tables to record the qualitative impact of the events described below.
Questions:
In the first event, the web server experiences a hard drive failure causing a loss of revenue, reputation, and customers. This is a very high risk impact and a possible probability of occurrence.
The correct answer is Major.
| Event 1: Web Server Hard Drive Failure Risk Impact Matrix |
|||||
|---|---|---|---|---|---|
| Probability of Occurrence | Very Low | Low | Medium | High | High |
| Highly Probable | Moderate | Major | Major | Severe | Severe |
| Probable | Moderate | Moderate | Major | Major | Severe |
| Possible | Minor | Moderate | Moderate | Moderate | Major |
| Unlikely | Minor | Moderate | Moderate | Moderate | Major |
| Rare | Minor | Minor | Minor | Moderate | Moderate |
In the second event, a denial-of service attack launches against the web server. This is a high risk impact and a probable probability of occurrence.
The correct answer is Major
| Event 2: A DoS/DDoS Attack Risk Impact Matrix |
|||||
|---|---|---|---|---|---|
| Probability of Occurrence | Very Low | Low | Medium | High | Very High |
| Highly Probable | Moderate | Major | Major | Severe | Severe |
| Probable | Moderate | Moderate | Major | Major | Severe |
| Possible | Minor | Moderate | Moderate | Moderate | Major |
| Unlikely | Minor | Moderate | Moderate | Moderate | Major |
| Rare | Minor | Minor | Minor | Moderate | Moderate |
In the third event, there is a fire in the server room. This is a very high risk impact and a rare probability of occurrence.
The correct answer is Moderate.
| Event 3: Fire in the Server Room Risk Impact Matrix |
|||||
|---|---|---|---|---|---|
| Probability of Occurrence | Very Low | Low | Medium | High | Very High |
| Highly Probable | Moderate | Major | Major | Severe | Severe |
| Probable | Moderate | Moderate | Major | Major | Severe |
| Possible | Minor | Moderate | Moderate | Moderate | Major |
| Unlikely | Minor | Moderate | Moderate | Moderate | Major |
| Rare | Minor | Minor | Minor | Moderate | Moderate |
In the fourth event, credit card data has been stolen. This is a very high risk impact and an unlikely probability of occurrence.
The correct answer is Major.
| Event 4: Data Breach/Credit Card Data Stolen Risk Impact Matrix |
|||||
|---|---|---|---|---|---|
| Probability of Occurrence | Very Low | Low | Medium | High | Very High |
| Highly Probable | Moderate | Major | Major | Severe | Severe |
| Probable | Moderate | Moderate | Major | Major | Severe |
| Possible | Minor | Moderate | Moderate | Moderate | Major |
| Unlikely | Minor | Moderate | Moderate | Moderate | Major |
| Rare | Minor | Minor | Minor | Moderate | Moderate |
In the fifth event, there is a tornado in the area. This is a low risk impact and a rare probability of occurrence.
The correct answer is Minor.
| Event 5: Weather/Tornado Risk Impact Matrix |
|||||
|---|---|---|---|---|---|
| Probability of Occurrence | Very Low | Low | Medium | High | Very High |
| Highly Probable | Moderate | Major | Major | Severe | Severe |
| Probable | Moderate | Moderate | Major | Major | Severe |
| Possible | Minor | Moderate | Moderate | Moderate | Major |
| Unlikely | Minor | Moderate | Moderate | Moderate | Major |
| Rare | Minor | Minor | Minor | Moderate | Moderate |
Part 2: Calculate Risks
Step 1: ABC Company Laptops Scenario
Question:
ABC Company owns 65 laptops. Each laptop cost $1,200. You will base your calculations on the value of one laptop. The team identified three threats. Based on internal data, calculate the ARO, and ALE given the information provided. Enter the missing values in the table.
| Threat Event | SLE | EF | Rate of Occurrence | ARO | ALE |
|---|---|---|---|---|---|
| Theft of Equipment | $1200 | 100% (1.0) | Once every 2 years | 0.5 | $600 |
| Damage by Dropping | $720 | 60%(0.6) | Once every 5 years | 0.2 | $144 |
| Malware | $240 | 20% (0.2) | Twice a year | 2 | $480 |
| Total ALE for all threats | $1,224 | ||||
Step 2: ABC Company Storage Area Network Scenario
Questions:
The ABC Company is performing a risk analysis for its storage area network. The total asset value is $250,000. The team identified the three threats shown in the table. Manufacturer’s data and company records provided the data given in the table. Enter the missing values in the table.
| Threat Event | SLE | EF | Rate of Occurrence | ARO | ALE |
|---|---|---|---|---|---|
| Drive Failure | $12,500 | 5% (.05) | Twice a year | 2 | $25,000 |
| Power Outage | $250,000 | 100% (1.0) | Once every 8 years | 0.125 | $31,250 |
| DOS/DDOS Attack | $25,000 | 10% (0.1) | Once every 2 years | 0.5 | $12,500 |
| Total ALE for all threats | $68,750 | ||||
Step 3: ABC Company Database Server Threats Scenario
Question:
ABC Company spent $18,000 on a database server. Configuration and installation totaled $2,000. Complete the risk analysis challenge table based on the four threats identified by the team at ABC. Enter the missing values in the table
| Threat Event | SLE | EF | Rate of Occurrence | ARO | ALE |
|---|---|---|---|---|---|
| Device Failure | $1,000 | 5% (.05) | Once every 18 months | 0.66 | $666 |
| Power Outage | $20,000 | 100% (1.0) | Once every 5 years | 0.2 | $4,000 |
| DOS/DDOS Attack | $3,000 | 15% (0.15) | Once every 4 years | 0.25 | $750 |
| Theft of Information | $8,000 | 40% (0.4) | Once every 2 years | 0.5 | $4,000 |
| Configuration Mistakes | $200 | 1% (0.01) | Once a month | 12 | $2,400 |
| Total ALE for all threats | $11,816 | ||||
Step 4: ABC Company Point-of-Sale System Challenge Scenario
Question:
ABC Company spent $10,000 on their remote point-of-sale system. Configuration and installation totaled $5,000. Complete the table based on the four threats identified by the team at ABC. Enter the missing values in the table.
| Threat Event | SLE | EF | Rate of Occurrence | ARO | ALE |
|---|---|---|---|---|---|
| Theft of Equipment | $15,000 | 100% (1.0) | Once every 5 years | 0.2 | $3,000 |
| Equipment Failure | $1,500 | 10% (0.1) | Twice a year | 2 | $3,000 |
| Ransomware | $3,000 | 20% (.2) | Once every 10 years | 0.1 | $300 |
| Data Breach | $6,000 | 40% (0.4) | Once every 5 years | 0.2 | $1,200 |
| Total ALE for all threats | $7,500 | ||||
Step 5: ABC Company Private Cloud Facility Challenge Scenario
Question:
BC Company spent $500,000 on the development and purchase of a private cloud facility. Configuration and installation totaled $50,000 and the programming and application development cost another $450,000.
Complete the Risk analysis Challenge table based on the four threats identified by the team at ABC. Enter the missing values in the table.
| Threat Event | SLE | EF | Rate of Occurrence | ARO | ALE |
|---|---|---|---|---|---|
| Power Outage | $500,000 | 50% (0.5) | Once every 5 years | .2 | $100,000 |
| DOS/DDOS Attack | $400,000 | 40% (0.4) | Once every 2 years | .5 | $200,000 |
| Data Breach | $400,000 | 40% (0.4) | Once every 10 years | .1 | $40,000 |
| Flood | $1,000,000 | 100% (1.0) | Once every 20 years | .05 | $50,000 |
| Total ALE for all threats | $390,000 | ||||
