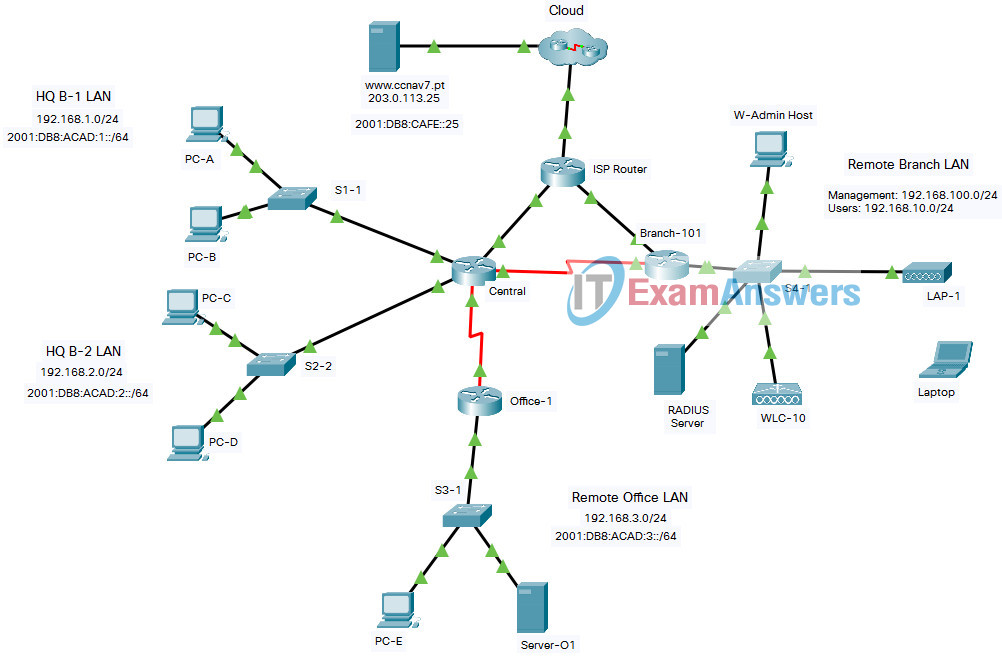
CCNA 2 v7 – SRWE Practice PT Skills Assessment (PTSA) – Part 2 Answers
[Updated on Sep 2021 – 100% Scored]
CCNAv7: Switching, Routing, and Wireless Essentials v7.0 (SRWE)
Final Packet Tracer Skills Assessment - Part 2
Addressing Table
| Device | Interface | Address and Prefix |
|---|---|---|
| Central | G0/0/0 | 192.168.1.1/24 |
| 2001:db8:acad:1::1/64 | ||
| fe80::1 | ||
| G0/0/1 | 192.168.2.1/24 | |
| 2001:db8:acad:2::1/64 | ||
| fe80::1 | ||
| G0/0/2 | 10.1.0.1/30 | |
| 2001:db8:acad:a::1/64 | ||
| fe80::2 | ||
| S0/1/0 | 10.2.0.1/30 | |
| 2001:db8:acad:b::1/64 | ||
| fe80::2 | ||
| S0/1/1 | 10.4.0.1/30 | |
| 2001:db8:acad:d::1/64 | ||
| Office-1 | S0/1/1 | 10.4.0.2/30 |
| 2001:db8:acad:d::2/64 | ||
| fe80::2 | ||
| G0/0/0 | 192.168.3.1/24 | |
| 2001:db8:acad:3::1/64 | ||
| fe80::1 | ||
| Branch-101 | G0/0/0.10 | 192.168.10.1/24 |
| G0/0/0.100 | 192.168.100.1/24 | |
| G0/0/0.172 | 172.16.1.1/24 | |
| G0/0/1 | DHCP | |
| 2001:db8:acad:c::2/64 | ||
| S0/1/0 | 10.2.0.2/30 | |
| 2001:db8:acad:b::2/64 | ||
| ISP Router | G0/0/0 | 10.1.0.2/24 |
| 2001:DB8:ACAD:A::2/64 | ||
| G0/0/1 | 10.3.0.1/24 | |
| 2001:DB8:ACAD:C::1/64 | ||
| WLC-10 | management | 192.168.100.254 |
| WLAN 10 | 192.168.10.254/24 | |
| Server-O1 | NIC | 192.168.3.122 |
| 2001:db8:acad:3::122 | ||
| Internet Server | NIC | 203.0.113.25 |
| 2001:db8:acad:cafe:25 | ||
| DNS Server | NIC | 198.51.100.163 |
| 2001:DB8:face::163 | ||
| Management Host | NIC | 192.168.100.23 |
| Wireless Host | NIC | DHCP |
| RADIUS server | NIC | 172.16.1.100/24 |
| PC-A | NIC | 192.168.1.10/24 |
| 2001:db8:acad:1::10/64 | ||
| PC-B | NIC | 192.168.1.11/24 |
| 2001:db8:acad:1::11/64 | ||
| PC-C | NIC | 192.168.2.20/24 |
| 2001:db8:acad:2::20/64 | ||
| PC-D | NIC | 192.168.2.11/24 |
| 2001:db8:acad:2::21/64 | ||
| PC-E | NIC | 192.168.3.30/24 |
| 2001:db8:acad:3::30/64 |
Objectives
In this assessment, you will configure the following:
- Floating static and default routes in IPv4 and IPv6.
- Host routes in IPv4 and IPv6.
- DHCP pools and scopes.
- Switch security including port security.
- Enhanced LAN security with DHCP snooping, dynamic ARP inspection, PortFast, and BPDU guard.
- Wireless LAN Controller-based wireless LAN with enterprise authentication.
You will only configure the Central and Branch-101 routers, the S1-1 switch, and the WLC-10 wireless LAN controller. Access to other devices is not available.
Background / Scenario
Netacad PLC is reworking their network. You have been asked to prototype the network in Packet Tracer for evaluation by senior network staff.
Instructions
Part 1: Configure Switch Security
In this part of the assessment you will configure switch S1-1 with switch security features. Switch ports FastEthernet0/1 to FastEthernet0/5 are the active switch ports. Port GigabitEthernet0/1 is a dedicated link to router Central. All other ports should be secured.
Step 1: Configure VLANs
- a. Configure VLAN 10 with name users.
- b. Configure VLAN 999 with the name unused.
S1-1 Switch
S1-1(config)#vlan 10 S1-1(config-vlan)#name users S1-1(config-vlan)#vlan 999 S1-1(config-vlan)#name unused
Step 2: Configure active switch ports.
On the active switch ports configure the following:
a. Configure FastEthernet 0/1 through 0/5 and GigabitEthernet 0/1 as static access ports in VLAN 10.
S1-1(config)#interface range f0/1-5, g0/1 S1-1(config-if-range)#switchport mode access S1-1(config-if-range)#switchport access vlan 10
b. Activate port security on the ports.
- Configure the active ports to accept a maximum of 4 MAC addresses.
- If a violation occurs, configure the ports to drop frames from the unauthorized MAC address, log it, and send an alert.
- MAC addresses should be present in the MAC address table for a maximum of 10 minutes before they are removed.
- Ports should add the learned MAC addresses to the running configuration.
- Configure the MAC address of PC-A as a static address on port FastEthernet0/1.
S1-1(config)#interface range f0/1-5 S1-1(config-if-range)#switchport port-security S1-1(config-if-range)#switchport port-security maximum 4 S1-1(config-if-range)#switchport port-security violation restrict S1-1(config-if-range)#switchport port-security aging time 10 S1-1(config-if-range)#switchport port-security mac-address sticky S1-1(config-if-range)#exit S1-1(config)#interface f0/1 S1-1(config-if)#switchport port-security mac-address 00D0.D3DC.2825 S1-1(config-if)#exit
c. Protect against DHCP snooping.
Note: In this simulated network, DHCP snooping may not operate correctly in Packet Tracer. Configure it as you would normally. You will receive full credit for a configuration that meets the requirements below.
- Activate DHCP snooping globally.
- Activate DHCP snooping for the two VLANs that you configured.
- Configure the ports to limit the rate to 5 DHCP packets per second.
- Configure the port that links to the router as trusted.
S1-1(config)#ip dhcp snooping S1-1(config)#ip dhcp snooping vlan 10,999 S1-1(config)#interface range f0/1-5, g0/1 S1-1(config-if-range)#ip dhcp snooping limit rate 5 S1-1(config-if-range)#exit S1-1(config)#interface g0/1 S1-1(config-if)#ip dhcp snooping trust S1-1(config-if)#exit
d. Guard against ARP attacks by implementing DAI.
- Activate DAI globally.
- Activate DAI on the two VLANs.
- Configure the port that links to the router as trusted.
S1-1(config)#ip arp inspection vlan 10,999 S1-1(config)#interface g0/1 S1-1(config-if)#ip arp inspection trust S1-1(config-if)#exit
e. Mitigate STP attacks by configuring BPDUguard and PortFast on the active ports.
S1-1(config)#interface range f0/1-5 S1-1(config-if-range)#spanning-tree portfast S1-1(config-if-range)#spanning-tree bpduguard enable
Step 3: Secure unused switch ports.
a. Move all unused switch ports to VLAN 999.
b. Configure all unused switch ports as static access ports.
c. Deactivate all unused switch ports.
S1-1(config)#interface range f0/6-24, g0/2 S1-1(config-if-range)#switchport mode access S1-1(config-if-range)#switchport access vlan 999 S1-1(config-if-range)#shutdown
Part 2: Configure Addressing and DHCP
You will configure DHCP and interface addressing on router Branch-101 to prepare for implementing the wireless LAN controller network.
Step 1: Configure and address a subinterface for the WLAN user network.
a. Configure subinterface 10 on the router interface that is connected to the switch S4-1.
b. The router should provide router-on-a-stick routing to VLAN 10.
c. Configure the subinterface with the address from the Addressing Table.
Brand-101 Router
Branch-101(config)#interface g0/0/0.10 Branch-101(config-subif)#description WLAN users Branch-101(config-subif)#encapsulation dot1q 10 Branch-101(config-subif)#ip address 192.168.10.1 255.255.255.0
Step 2: Configure a DHCP pool for WLAN user network.
a. Exclude the router interface address and the management address of the WLC.
Branch-101(config)#ip dhcp excluded-address 192.168.10.1 Branch-101(config)#ip dhcp excluded-address 192.168.10.254
b. Configure a DHCP pool that will be used by hosts that are connecting to the WLAN.
- Name the pool WLAN-hosts.
- Configure the pool to use addresses in the 192.168.10.0/24 network.
- The pool should also provide the default gateway and DNS server addresses.
Branch-101(config)#ip dhcp pool WLAN-hosts Branch-101(dhcp-config)#network 192.168.10.0 255.255.255.0 Branch-101(dhcp-config)#default-router 192.168.10.1 Branch-101(dhcp-config)#dns-server 198.51.100.163
Step 3: Configure an interface as a DHCP client.
On Branch-101, configure the interface that is connected to ISP Router to receive its address over DHCP.
Branch-101(config)#interface g0/0/1 Branch-101(config-if)#ip address dhcp Branch-101(config-if)#exit
Part 3: Configure Static Routes
In this part of the assessment you will configure static, default, floating static, and host routes in both IPv4 and IPv6. You will configure the Central and Branch-101 routers. Netacad PLC has decided that it wants to use static routing between all its networks. In addition, the company wants to use the Ethernet links between routers for most data traffic and reserve serial link between Central and Branch-101 for backup purposes in case one of the Ethernet links becomes unavailable. You will be configuring floating static and default routes.
Step 1: Configure static routes on Central.
a. Configure IPv4 default routes to the cloud using the Ethernet link as the preferred link and the serial link as the floating backup. Use an administrative distance of 10 for the backup route. These routes should be configured as directly connected routes.
Note: Ethernet interfaces will give a warning when configured without a next-hop address. In this configuration, the interface is point-to-point, so the warning can be ignored.
Central(config)#ip route 0.0.0.0 0.0.0.0 g0/0/2 Central(config)#ip route 0.0.0.0 0.0.0.0 s0/1/0 10
b. Configure IPv4 static routes to the Remote Branch LAN WLAN user network following the same guidelines as above for type of route and administrative distance.
Central(config)#ip route 192.168.10.0 255.255.255.0 g0/0/2 Central(config)#ip route 192.168.10.0 255.255.255.0 s0/1/0 10
c. Configure an IPv4 host route on Central to the Server-O1 on the Remote Office LAN. Create a directly connected route.
Central(config)#ip route 192.168.3.122 255.255.255.255 s0/1/1
Note: For the purpose of this assessment, please enter the IPv4 static routes in the following order:
1) IPv4 default route
2) IPv4 floating default route
3) IPv4 host route
4) IPv4 static route to Remote Branch LAN
5) IPv4 floating static route to Remote Branch LAN
d. Ensure that the device is configured to route IPv6.
e. Configure IPv6 default routes to the cloud. Use the Ethernet link as the primary route, and the serial link as the floating backup. Use an administrative distance of 10 for the backup route. These routes should specify the next hop interface address.
Central(config)#ipv6 unicast-routing Central(config)#ipv6 route ::/0 2001:DB8:ACAD:A::2 Central(config)#ipv6 route ::/0 2001:db8:acad:b::2 10
f. Configure an IPv6 host route on Central to the Server-O1 on the Remote Office LAN It should be a next-hop route.
Central(config)#ipv6 route 2001:db8:acad:3::122/128 2001:db8:acad:d::2
Note: For the purpose of this assessment, please enter the IPv6 static routes in the following order:
1) IPv6 default route
2) IPv6 floating default route
3) IPv6 host route
Step 2: Configure static routes on Branch-101.
Branch-101 must also be configured with static routes to the other three networks in the Netacad PLC network. It will require floating static and default routes in IPv4 and IPv6 following the same guidelines as were used for the Central static routes.
- IPv6 routes use next-hop address arguments.
- IPv4 routes use exit interface arguments.
- All routes should prefer the Ethernet links over the serial link.
- Backup floating routes use an administrative distance of 10.
a. Configure IPv4 default routes to the cloud using the Ethernet link as the preferred link and the serial link as the backup.
Note: For the purpose of this assessment, please enter the IPv4 static routes in the following order:
1) IPv4 default route
2) IPv4 floating default route
Branch-101(config)#ip route 0.0.0.0 0.0.0.0 g0/0/1 Branch-101(config)#ip route 0.0.0.0 0.0.0.0 s0/1/0 10
b. Ensure that the device is configured to route IPv6.
c. Configure IPv6 default routes to the cloud. Use the Ethernet link as the primary route, and the serial link as backup. Use an administrative distance of 10 for the backup route. These routes should specify the next hop interface address.
Branch-101(config)#ipv6 unicast-routing Branch-101(config)#ipv6 route ::/0 2001:DB8:ACAD:C::1 Branch-101(config)#ipv6 route ::/0 2001:DB8:ACAD:B::1 10
Note: For the purpose of this assessment, please enter the IPv6 static routes in the following order:
1) IPv6 default route
2) IPv6 floating default route
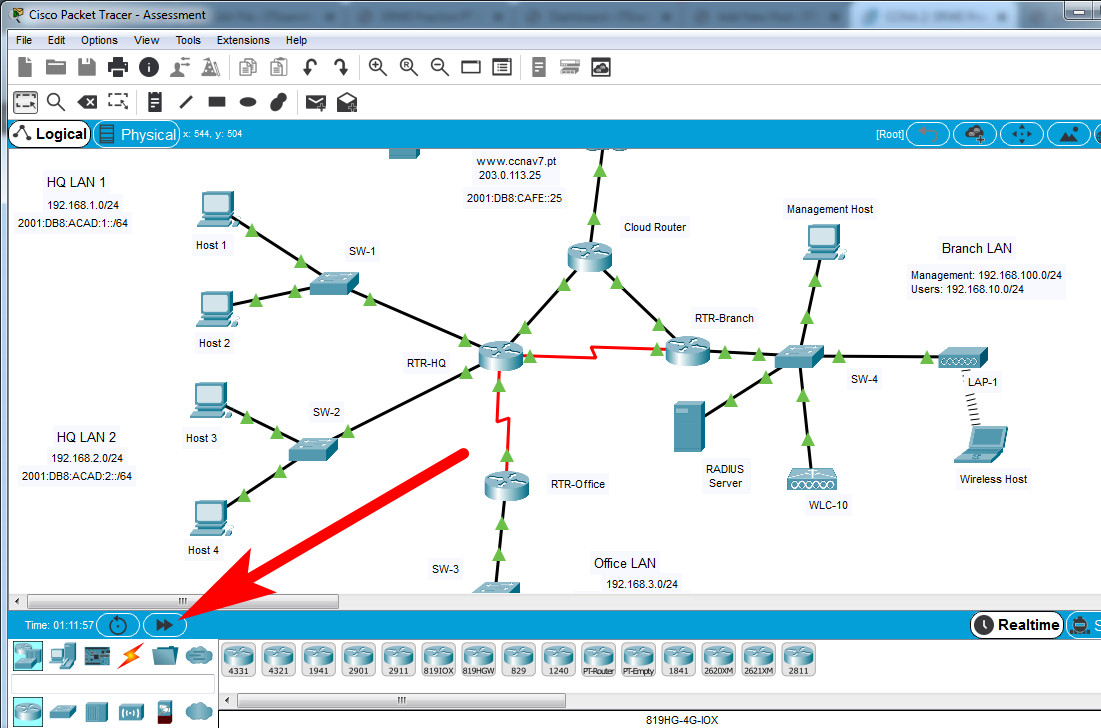
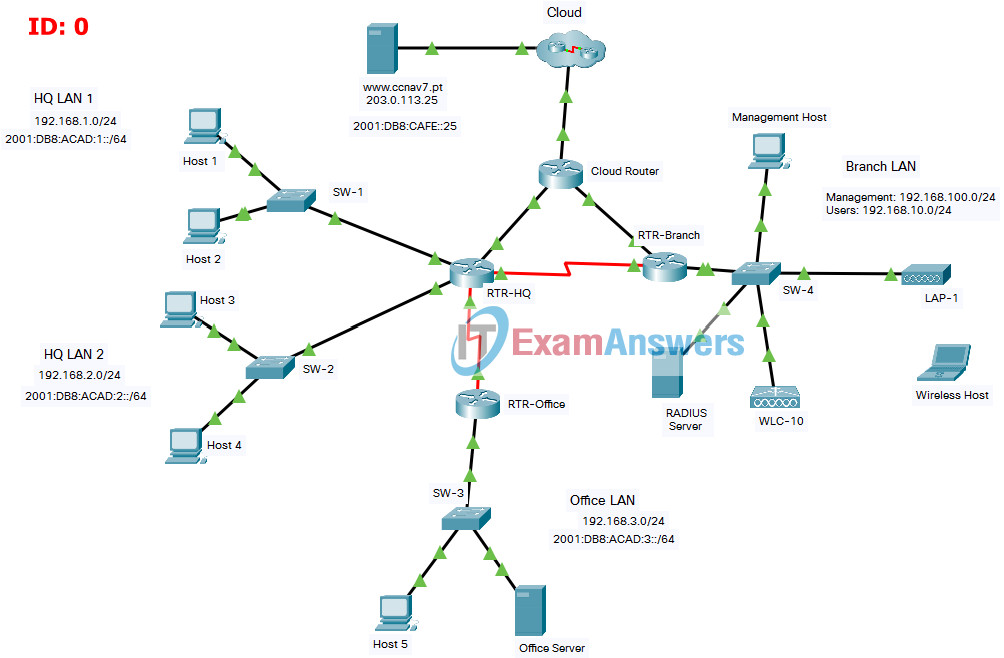
Final Packet Tracer Skills Assessment - Part 2
Addressing Table
| Device | Interface | Address and Prefix |
|---|---|---|
| RTR-HQ | G0/0/0 | 192.168.1.1/24 |
| 2001:db8:acad:1::1/64 | ||
| fe80::1 | ||
| G0/0/1 | 192.168.2.1/24 | |
| 2001:db8:acad:2::1/64 | ||
| fe80::1 | ||
| G0/0/2 | 10.1.0.1/30 | |
| 2001:db8:acad:a::1/64 | ||
| fe80::2 | ||
| S0/1/0 | 10.2.0.1/30 | |
| 2001:db8:acad:b::1/64 | ||
| fe80::2 | ||
| S0/1/1 | 10.4.0.1/30 | |
| 2001:db8:acad:d::1/64 | ||
| RTR-Office | S0/1/1 | 10.4.0.2/30 |
| 2001:db8:acad:d::2/64 | ||
| fe80::2 | ||
| G0/0/0 | 192.168.3.1/24 | |
| 2001:db8:acad:3::1/64 | ||
| fe80::1 | ||
| RTR-Branch | G0/0/0.10 | 192.168.10.1/24 |
| G0/0/0.100 | 192.168.100.1/24 | |
| G0/0/0.172 | 172.16.1.1/24 | |
| G0/0/1 | DHCP | |
| 2001:db8:acad:c::2/64 | ||
| S0/1/0 | 10.2.0.2/30 | |
| 2001:db8:acad:b::2/64 | ||
| Cloud Router | G0/0/0 | 10.1.0.2/24 |
| 2001:DB8:ACAD:A::2/64 | ||
| G0/0/1 | 10.3.0.1/24 | |
| 2001:DB8:ACAD:C::1/64 | ||
| WLC-10 | management | 192.168.100.254 |
| WLAN 10 | 192.168.10.254/24 | |
| Office Server | NIC | 192.168.3.122 |
| 2001:db8:acad:3::122 | ||
| Web Server | NIC | 203.0.113.25 |
| 2001:db8:acad:cafe:25 | ||
| DNS Server | NIC | 198.51.100.163 |
| 2001:DB8:face::163 | ||
| Management Host | NIC | 192.168.100.23 |
| Wireless Host | NIC | DHCP |
| RADIUS server | NIC | 172.16.1.100/24 |
| Host 1 | NIC | 192.168.1.10/24 |
| 2001:db8:acad:1::10/64 | ||
| Host 2 | NIC | 192.168.1.11/24 |
| 2001:db8:acad:1::11/64 | ||
| Host 3 | NIC | 192.168.2.20/24 |
| 2001:db8:acad:2::20/64 | ||
| Host 4 | NIC | 192.168.2.11/24 |
| 2001:db8:acad:2::21/64 | ||
| Host 5 | NIC | 192.168.3.30/24 |
| 2001:db8:acad:3::30/64 |
Objectives
In this assessment, you will configure the following:
- Floating static and default routes in IPv4 and IPv6.
- Host routes in IPv4 and IPv6.
- DHCP pools and scopes.
- Switch security including port security.
- Enhanced LAN security with DHCP snooping, dynamic ARP inspection, PortFast, and BPDU guard.
- Wireless LAN Controller-based wireless LAN with enterprise authentication.
You will only configure the RTR-HQ and RTR-Branch routers, the SW-1 switch, and the WLC-10 wireless LAN controller. Access to other devices is not available.
Background / Scenario
XYZ Corp. is reworking their network. You have been asked to prototype the network in Packet Tracer for evaluation by senior network staff.
Instructions
Part 1: Configure Switch Security
In this part of the assessment you will configure switch SW-1 with switch security features. Switch ports FastEthernet0/1 to FastEthernet0/5 are the active switch ports. Port GigabitEthernet0/1 is a dedicated link to router RTR-HQ. All other ports should be secured.
Step 1: Configure VLANs
- a. Configure VLAN 10 with name users.
- b. Configure VLAN 999 with the name unused.
SW-1 Switch
SW-1(config)#vlan 10 SW-1(config-vlan)#name users SW-1(config-vlan)#vlan 999 SW-1(config-vlan)#name unused
Step 2: Configure active switch ports.
On the active switch ports configure the following:
a. Configure FastEthernet 0/1 through 0/5 and GigabitEthernet 0/1 as static access ports in VLAN 10.
SW-1(config)#interface range f0/1-5, g0/1 SW-1(config-if-range)#switchport mode access SW-1(config-if-range)#switchport access vlan 10
b. Activate port security on the ports.
- Configure the active ports to accept a maximum of 4 MAC addresses.
- If a violation occurs, configure the ports to drop frames from the unauthorized MAC address, log it, and send an alert.
- MAC addresses should be present in the MAC address table for a maximum of 10 minutes before they are removed.
- Ports should add the learned MAC addresses to the running configuration.
- Configure the MAC address of Host 1 as a static address on port FastEthernet0/1.
SW-1(config)#interface range f0/1-5 SW-1(config-if-range)#switchport port-security SW-1(config-if-range)#switchport port-security maximum 4 SW-1(config-if-range)#switchport port-security violation restrict SW-1(config-if-range)#switchport port-security aging time 10 SW-1(config-if-range)#switchport port-security mac-address sticky SW-1(config-if-range)#exit SW-1(config)#interface f0/1 SW-1(config-if)#switchport port-security mac-address 00D0.D3DC.2825 SW-1(config-if)#exit
c. Protect against DHCP snooping.
Note: In this simulated network, DHCP snooping may not operate correctly in Packet Tracer. Configure it as you would normally. You will receive full credit for a configuration that meets the requirements below.
- Activate DHCP snooping globally.
- Activate DHCP snooping for the two VLANs that you configured.
- Configure the ports to limit the rate to 5 DHCP packets per second.
- Configure the port that links to the router as trusted.
SW-1(config)#ip dhcp snooping SW-1(config)#ip dhcp snooping vlan 10,999 SW-1(config)#interface range f0/1-5, g0/1 SW-1(config-if-range)#ip dhcp snooping limit rate 5 SW-1(config-if-range)#exit SW-1(config)#interface g0/1 SW-1(config-if)#ip dhcp snooping trust SW-1(config-if)#exit
d. Guard against ARP attacks by implementing DAI.
- Activate DAI globally.
- Activate DAI on the two VLANs.
- Configure the port that links to the router as trusted.
SW-1(config)#ip arp inspection vlan 10,999 SW-1(config)#interface g0/1 SW-1(config-if)#ip arp inspection trust SW-1(config-if)#exit
e. Mitigate STP attacks by configuring BPDUguard and PortFast on the active ports.
SW-1(config)#interface range f0/1-5 SW-1(config-if-range)#spanning-tree portfast SW-1(config-if-range)#spanning-tree bpduguard enable
Step 3: Secure unused switch ports.
a. Move all unused switch ports to VLAN 999.
b. Configure all unused switch ports as static access ports.
c. Deactivate all unused switch ports.
SW-1(config)#interface range f0/6-24, g0/2 SW-1(config-if-range)#switchport mode access SW-1(config-if-range)#switchport access vlan 999 SW-1(config-if-range)#shutdown
Part 2: Configure Addressing and DHCP
You will configure DHCP and interface addressing on router RTR-Branch to prepare for implementing the wireless LAN controller network.
Step 1: Configure and address a subinterface for the WLAN user network.
a. Configure subinterface 10 on the router interface that is connected to the switch S4-1.
b. The router should provide router-on-a-stick routing to VLAN 10.
c. Configure the subinterface with the address from the Addressing Table.
RTR-Branch Router
RTR-Branch(config)#interface g0/0/0.10 RTR-Branch(config-subif)#description WLAN users RTR-Branch(config-subif)#encapsulation dot1q 10 RTR-Branch(config-subif)#ip address 192.168.10.1 255.255.255.0
Step 2: Configure a DHCP pool for WLAN user network.
a. Exclude the router interface address and the management address of the WLC.
RTR-Branch(config)#ip dhcp excluded-address 192.168.10.1 RTR-Branch(config)#ip dhcp excluded-address 192.168.10.254
b. Configure a DHCP pool that will be used by hosts that are connecting to the WLAN.
- Name the pool WLAN-hosts.
- Configure the pool to use addresses in the 192.168.10.0/24 network.
- The pool should also provide the default gateway and DNS server addresses.
RTR-Branch(config)#ip dhcp pool WLAN-hosts RTR-Branch(dhcp-config)#network 192.168.10.0 255.255.255.0 RTR-Branch(dhcp-config)#default-router 192.168.10.1 RTR-Branch(dhcp-config)#dns-server 198.51.100.163
Step 3: Configure an interface as a DHCP client.
On RTR-Branch, configure the interface that is connected to Cloud Router to receive its address over DHCP.
RTR-Branch(config)#interface g0/0/1 RTR-Branch(config-if)#ip address dhcp RTR-Branch(config-if)#exit
Part 3: Configure Static Routes
In this part of the assessment you will configure static, default, floating static, and host routes in both IPv4 and IPv6. You will configure the RTR-HQ and RTR-Branch routers. XYZ Corp. has decided that it wants to use static routing between all its networks. In addition, the company wants to use the Ethernet links between routers for most data traffic and reserve serial link between RTR-HQ and RTR-Branch for backup purposes in case one of the Ethernet links becomes unavailable. You will be configuring floating static and default routes.
Step 1: Configure static routes on RTR-HQ.
a. Configure IPv4 default routes to the cloud using the Ethernet link as the preferred link and the serial link as the floating backup. Use an administrative distance of 10 for the backup route. These routes should be configured as directly connected routes.
Note: Ethernet interfaces will give a warning when configured without a next-hop address. In this configuration, the interface is point-to-point, so the warning can be ignored.
RTR-HQ(config)#ip route 0.0.0.0 0.0.0.0 g0/0/2 RTR-HQ(config)#ip route 0.0.0.0 0.0.0.0 s0/1/0 10
b. Configure IPv4 static routes to the Remote Branch LAN WLAN user network following the same guidelines as above for type of route and administrative distance.
RTR-HQ(config)#ip route 192.168.10.0 255.255.255.0 g0/0/2 RTR-HQ(config)#ip route 192.168.10.0 255.255.255.0 s0/1/0 10
c. Configure an IPv4 host route on RTR-HQ to the Office Server on the Remote Office LAN. Create a directly connected route.
RTR-HQ(config)#ip route 192.168.3.122 255.255.255.255 s0/1/1
Note: For the purpose of this assessment, please enter the IPv4 static routes in the following order:
1) IPv4 default route
2) IPv4 floating default route
3) IPv4 host route
4) IPv4 static route to Remote Branch LAN
5) IPv4 floating static route to Remote Branch LAN
d. Ensure that the device is configured to route IPv6.
e. Configure IPv6 default routes to the cloud. Use the Ethernet link as the primary route, and the serial link as the floating backup. Use an administrative distance of 10 for the backup route. These routes should specify the next hop interface address.
RTR-HQ(config)#ipv6 unicast-routing RTR-HQ(config)#ipv6 route ::/0 2001:DB8:ACAD:A::2 RTR-HQ(config)#ipv6 route ::/0 2001:db8:acad:b::2 10
f. Configure an IPv6 host route on RTR-HQ to the Office Server on the Remote Office LAN It should be a next-hop route.
RTR-HQ(config)#ipv6 route 2001:db8:acad:3::122/128 2001:db8:acad:d::2
Note: For the purpose of this assessment, please enter the IPv6 static routes in the following order:
1) IPv6 default route
2) IPv6 floating default route
3) IPv6 host route
Step 2: Configure static routes on RTR-Branch.
RTR-Branch must also be configured with static routes to the other three networks in the XYZ Corp. network. It will require floating static and default routes in IPv4 and IPv6 following the same guidelines as were used for the RTR-HQ static routes.
- IPv6 routes use next-hop address arguments.
- IPv4 routes use exit interface arguments.
- All routes should prefer the Ethernet links over the serial link.
- Backup floating routes use an administrative distance of 10.
a. Configure IPv4 default routes to the cloud using the Ethernet link as the preferred link and the serial link as the backup.
Note: For the purpose of this assessment, please enter the IPv4 static routes in the following order:
1) IPv4 default route
2) IPv4 floating default route
RTR-Branch(config)#ip route 0.0.0.0 0.0.0.0 g0/0/1 RTR-Branch(config)#ip route 0.0.0.0 0.0.0.0 s0/1/0 10
b. Ensure that the device is configured to route IPv6.
c. Configure IPv6 default routes to the cloud. Use the Ethernet link as the primary route, and the serial link as backup. Use an administrative distance of 10 for the backup route. These routes should specify the next hop interface address.
RTR-Branch(config)#ipv6 unicast-routing RTR-Branch(config)#ipv6 route ::/0 2001:DB8:ACAD:C::1 RTR-Branch(config)#ipv6 route ::/0 2001:DB8:ACAD:B::1 10
Note: For the purpose of this assessment, please enter the IPv6 static routes in the following order:
1) IPv6 default route
2) IPv6 floating default route
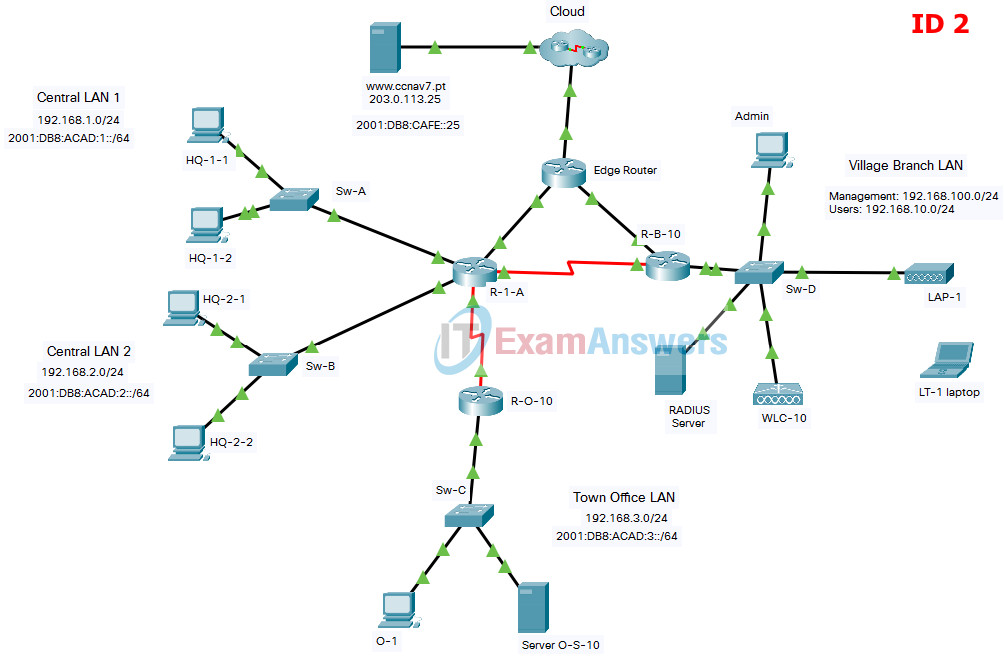
Final Packet Tracer Skills Assessment - Part 2
Addressing Table
| Device | Interface | Address and Prefix |
|---|---|---|
| R-1-A | G0/0/0 | 192.168.1.1/24 |
| 2001:db8:acad:1::1/64 | ||
| fe80::1 | ||
| G0/0/1 | 192.168.2.1/24 | |
| 2001:db8:acad:2::1/64 | ||
| fe80::1 | ||
| G0/0/2 | 10.1.0.1/30 | |
| 2001:db8:acad:a::1/64 | ||
| fe80::2 | ||
| S0/1/0 | 10.2.0.1/30 | |
| 2001:db8:acad:b::1/64 | ||
| fe80::2 | ||
| S0/1/1 | 10.4.0.1/30 | |
| 2001:db8:acad:d::1/64 | ||
| R-O-10 | S0/1/1 | 10.4.0.2/30 |
| 2001:db8:acad:d::2/64 | ||
| fe80::2 | ||
| G0/0/0 | 192.168.3.1/24 | |
| 2001:db8:acad:3::1/64 | ||
| fe80::1 | ||
| R-B-10 | G0/0/0.10 | 192.168.10.1/24 |
| G0/0/0.100 | 192.168.100.1/24 | |
| G0/0/0.172 | 172.16.1.1/24 | |
| G0/0/1 | DHCP | |
| 2001:db8:acad:c::2/64 | ||
| S0/1/0 | 10.2.0.2/30 | |
| 2001:db8:acad:b::2/64 | ||
| Edge Router | G0/0/0 | 10.1.0.2/24 |
| 2001:DB8:ACAD:A::2/64 | ||
| G0/0/1 | 10.3.0.1/24 | |
| 2001:DB8:ACAD:C::1/64 | ||
| WLC-10 | management | 192.168.100.254 |
| WLAN 10 | 192.168.10.254/24 | |
| Server O-S-10 | NIC | 192.168.3.122 |
| 2001:db8:acad:3::122 | ||
| Website NIC | NIC | 203.0.113.25 |
| 2001:db8:acad:cafe:25 | ||
| DNS Server | NIC | 198.51.100.163 |
| 2001:DB8:face::163 | ||
| Management Host | NIC | 192.168.100.23 |
| LT-1 laptop | NIC | DHCP |
| RADIUS server | NIC | 172.16.1.100/24 |
| HQ-1-1 | NIC | 192.168.1.10/24 |
| 2001:db8:acad:1::10/64 | ||
| HQ-1-2 | NIC | 192.168.1.11/24 |
| 2001:db8:acad:1::11/64 | ||
| HQ-2-1 | NIC | 192.168.2.20/24 |
| 2001:db8:acad:2::20/64 | ||
| Host 4 | NIC | 192.168.2.11/24 |
| 2001:db8:acad:2::21/64 | ||
| O-1 | NIC | 192.168.3.30/24 |
| 2001:db8:acad:3::30/64 |
Objectives
In this assessment, you will configure the following:
- Floating static and default routes in IPv4 and IPv6.
- Host routes in IPv4 and IPv6.
- DHCP pools and scopes.
- Switch security including port security.
- Enhanced LAN security with DHCP snooping, dynamic ARP inspection, PortFast, and BPDU guard.
- Wireless LAN Controller-based wireless LAN with enterprise authentication.
You will only configure the R-1-A and R-B-10 routers, the Sw-A switch, and the WLC-10 wireless LAN controller. Access to other devices is not available.
Background / Scenario
Cisco Demo LLC. is reworking their network. You have been asked to prototype the network in Packet Tracer for evaluation by senior network staff.
Instructions
Part 1: Configure Switch Security
In this part of the assessment you will configure switch Sw-A with switch security features. Switch ports FastEthernet0/1 to FastEthernet0/5 are the active switch ports. Port GigabitEthernet0/1 is a dedicated link to router R-1-A. All other ports should be secured.
Step 1: Configure VLANs
- a. Configure VLAN 10 with name users.
- b. Configure VLAN 999 with the name unused.
Sw-A Switch
Sw-A(config)#vlan 10 Sw-A(config-vlan)#name users Sw-A(config-vlan)#vlan 999 Sw-A(config-vlan)#name unused
Step 2: Configure active switch ports.
On the active switch ports configure the following:
a. Configure FastEthernet 0/1 through 0/5 and GigabitEthernet 0/1 as static access ports in VLAN 10.
Sw-A(config)#interface range f0/1-5, g0/1 Sw-A(config-if-range)#switchport mode access Sw-A(config-if-range)#switchport access vlan 10
b. Activate port security on the ports.
- Configure the active ports to accept a maximum of 4 MAC addresses.
- If a violation occurs, configure the ports to drop frames from the unauthorized MAC address, log it, and send an alert.
- MAC addresses should be present in the MAC address table for a maximum of 10 minutes before they are removed.
- Ports should add the learned MAC addresses to the running configuration.
- Configure the MAC address of HQ-1-1 as a static address on port FastEthernet0/1.
Sw-A(config)#interface range f0/1-5 Sw-A(config-if-range)#switchport port-security Sw-A(config-if-range)#switchport port-security maximum 4 Sw-A(config-if-range)#switchport port-security violation restrict Sw-A(config-if-range)#switchport port-security aging time 10 Sw-A(config-if-range)#switchport port-security mac-address sticky Sw-A(config-if-range)#exit Sw-A(config)#interface f0/1 Sw-A(config-if)#switchport port-security mac-address 00D0.D3DC.2825 Sw-A(config-if)#exit
c. Protect against DHCP snooping.
Note: In this simulated network, DHCP snooping may not operate correctly in Packet Tracer. Configure it as you would normally. You will receive full credit for a configuration that meets the requirements below.
- Activate DHCP snooping globally.
- Activate DHCP snooping for the two VLANs that you configured.
- Configure the ports to limit the rate to 5 DHCP packets per second.
- Configure the port that links to the router as trusted.
Sw-A(config)#ip dhcp snooping Sw-A(config)#ip dhcp snooping vlan 10,999 Sw-A(config)#interface range f0/1-5, g0/1 Sw-A(config-if-range)#ip dhcp snooping limit rate 5 Sw-A(config-if-range)#exit Sw-A(config)#interface g0/1 Sw-A(config-if)#ip dhcp snooping trust Sw-A(config-if)#exit
d. Guard against ARP attacks by implementing DAI.
- Activate DAI globally.
- Activate DAI on the two VLANs.
- Configure the port that links to the router as trusted.
Sw-A(config)#ip arp inspection vlan 10,999 Sw-A(config)#interface g0/1 Sw-A(config-if)#ip arp inspection trust Sw-A(config-if)#exit
e. Mitigate STP attacks by configuring BPDUguard and PortFast on the active ports.
Sw-A(config)#interface range f0/1-5 Sw-A(config-if-range)#spanning-tree portfast Sw-A(config-if-range)#spanning-tree bpduguard enable
Step 3: Secure unused switch ports.
a. Move all unused switch ports to VLAN 999.
b. Configure all unused switch ports as static access ports.
c. Deactivate all unused switch ports.
Sw-A(config)#interface range f0/6-24, g0/2 Sw-A(config-if-range)#switchport mode access Sw-A(config-if-range)#switchport access vlan 999 Sw-A(config-if-range)#shutdown
Part 2: Configure Addressing and DHCP
You will configure DHCP and interface addressing on router R-B-10 to prepare for implementing the wireless LAN controller network.
Step 1: Configure and address a subinterface for the WLAN user network.
a. Configure subinterface 10 on the router interface that is connected to the switch S4-1.
b. The router should provide router-on-a-stick routing to VLAN 10.
c. Configure the subinterface with the address from the Addressing Table.
R-B-10 Router
R-B-10(config)#interface g0/0/0.10 R-B-10(config-subif)#description WLAN users R-B-10(config-subif)#encapsulation dot1q 10 R-B-10(config-subif)#ip address 192.168.10.1 255.255.255.0
Step 2: Configure a DHCP pool for WLAN user network.
a. Exclude the router interface address and the management address of the WLC.
R-B-10(config)#ip dhcp excluded-address 192.168.10.1 R-B-10(config)#ip dhcp excluded-address 192.168.10.254
b. Configure a DHCP pool that will be used by hosts that are connecting to the WLAN.
- Name the pool WLAN-hosts.
- Configure the pool to use addresses in the 192.168.10.0/24 network.
- The pool should also provide the default gateway and DNS server addresses.
R-B-10(config)#ip dhcp pool WLAN-hosts R-B-10(dhcp-config)#network 192.168.10.0 255.255.255.0 R-B-10(dhcp-config)#default-router 192.168.10.1 R-B-10(dhcp-config)#dns-server 198.51.100.163
Step 3: Configure an interface as a DHCP client.
On R-B-10, configure the interface that is connected to Edge Router to receive its address over DHCP.
R-B-10(config)#interface g0/0/1 R-B-10(config-if)#ip address dhcp R-B-10(config-if)#exit
Part 3: Configure Static Routes
In this part of the assessment you will configure static, default, floating static, and host routes in both IPv4 and IPv6. You will configure the R-1-A and R-B-10 routers. Cisco Demo LLC. has decided that it wants to use static routing between all its networks. In addition, the company wants to use the Ethernet links between routers for most data traffic and reserve serial link between R-1-A and R-B-10 for backup purposes in case one of the Ethernet links becomes unavailable. You will be configuring floating static and default routes.
Step 1: Configure static routes on R-1-A.
a. Configure IPv4 default routes to the cloud using the Ethernet link as the preferred link and the serial link as the floating backup. Use an administrative distance of 10 for the backup route. These routes should be configured as directly connected routes.
Note: Ethernet interfaces will give a warning when configured without a next-hop address. In this configuration, the interface is point-to-point, so the warning can be ignored.
R-1-A(config)#ip route 0.0.0.0 0.0.0.0 g0/0/2 R-1-A(config)#ip route 0.0.0.0 0.0.0.0 s0/1/0 10
b. Configure IPv4 static routes to the Remote Branch LAN WLAN user network following the same guidelines as above for type of route and administrative distance.
R-1-A(config)#ip route 192.168.10.0 255.255.255.0 g0/0/2 R-1-A(config)#ip route 192.168.10.0 255.255.255.0 s0/1/0 10
c. Configure an IPv4 host route on R-1-A to the Server O-S-10 on the Remote Office LAN. Create a directly connected route.
R-1-A(config)#ip route 192.168.3.122 255.255.255.255 s0/1/1
Note: For the purpose of this assessment, please enter the IPv4 static routes in the following order:
1) IPv4 default route
2) IPv4 floating default route
3) IPv4 host route
4) IPv4 static route to Remote Branch LAN
5) IPv4 floating static route to Remote Branch LAN
d. Ensure that the device is configured to route IPv6.
e. Configure IPv6 default routes to the cloud. Use the Ethernet link as the primary route, and the serial link as the floating backup. Use an administrative distance of 10 for the backup route. These routes should specify the next hop interface address.
R-1-A(config)#ipv6 unicast-routing R-1-A(config)#ipv6 route ::/0 2001:DB8:ACAD:A::2 R-1-A(config)#ipv6 route ::/0 2001:db8:acad:b::2 10
f. Configure an IPv6 host route on R-1-A to the Server O-S-10 on the Remote Office LAN It should be a next-hop route.
R-1-A(config)#ipv6 route 2001:db8:acad:3::122/128 2001:db8:acad:d::2
Note: For the purpose of this assessment, please enter the IPv6 static routes in the following order:
1) IPv6 default route
2) IPv6 floating default route
3) IPv6 host route
Step 2: Configure static routes on R-B-10.
R-B-10 must also be configured with static routes to the other three networks in the Cisco Demo LLC. network. It will require floating static and default routes in IPv4 and IPv6 following the same guidelines as were used for the R-1-A static routes.
- IPv6 routes use next-hop address arguments.
- IPv4 routes use exit interface arguments.
- All routes should prefer the Ethernet links over the serial link.
- Backup floating routes use an administrative distance of 10.
a. Configure IPv4 default routes to the cloud using the Ethernet link as the preferred link and the serial link as the backup.
Note: For the purpose of this assessment, please enter the IPv4 static routes in the following order:
1) IPv4 default route
2) IPv4 floating default route
R-B-10(config)#ip route 0.0.0.0 0.0.0.0 g0/0/1 R-B-10(config)#ip route 0.0.0.0 0.0.0.0 s0/1/0 10
b. Ensure that the device is configured to route IPv6.
c. Configure IPv6 default routes to the cloud. Use the Ethernet link as the primary route, and the serial link as backup. Use an administrative distance of 10 for the backup route. These routes should specify the next hop interface address.
R-B-10(config)#ipv6 unicast-routing R-B-10(config)#ipv6 route ::/0 2001:DB8:ACAD:C::1 R-B-10(config)#ipv6 route ::/0 2001:DB8:ACAD:B::1 10
Note: For the purpose of this assessment, please enter the IPv6 static routes in the following order:
1) IPv6 default route
2) IPv6 floating default route
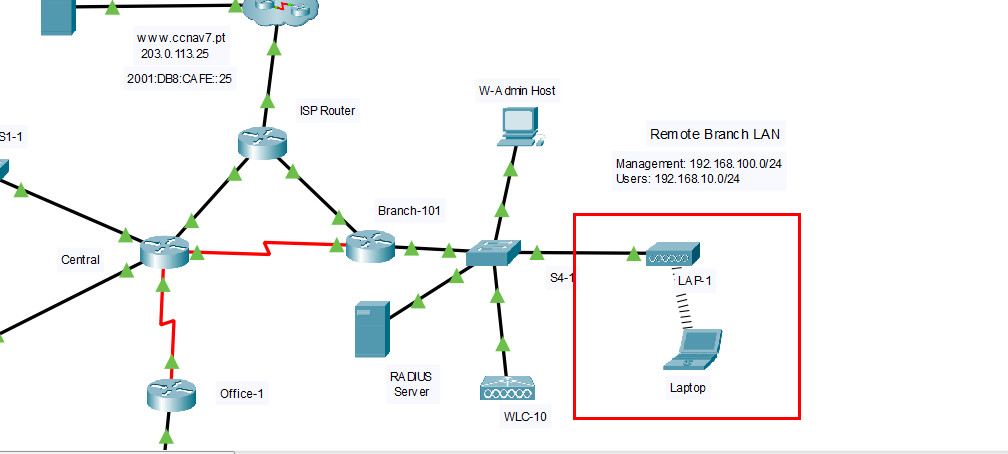
Part 4: Configure a Wireless LAN using a Wireless LAN Controller
In this part of the assessment, you will configure the wireless LAN controller to provide access wireless access to the network. Username and password are the default admin/admin. Connect to the WLC over HTTPS to the management interface.
Open the browser from the desktop of W-Admin Host (or Management Host/Admin). Connect to the IP address of the WLC over HTTPS: https://192.168.100.254

Login with the username admin and password admin
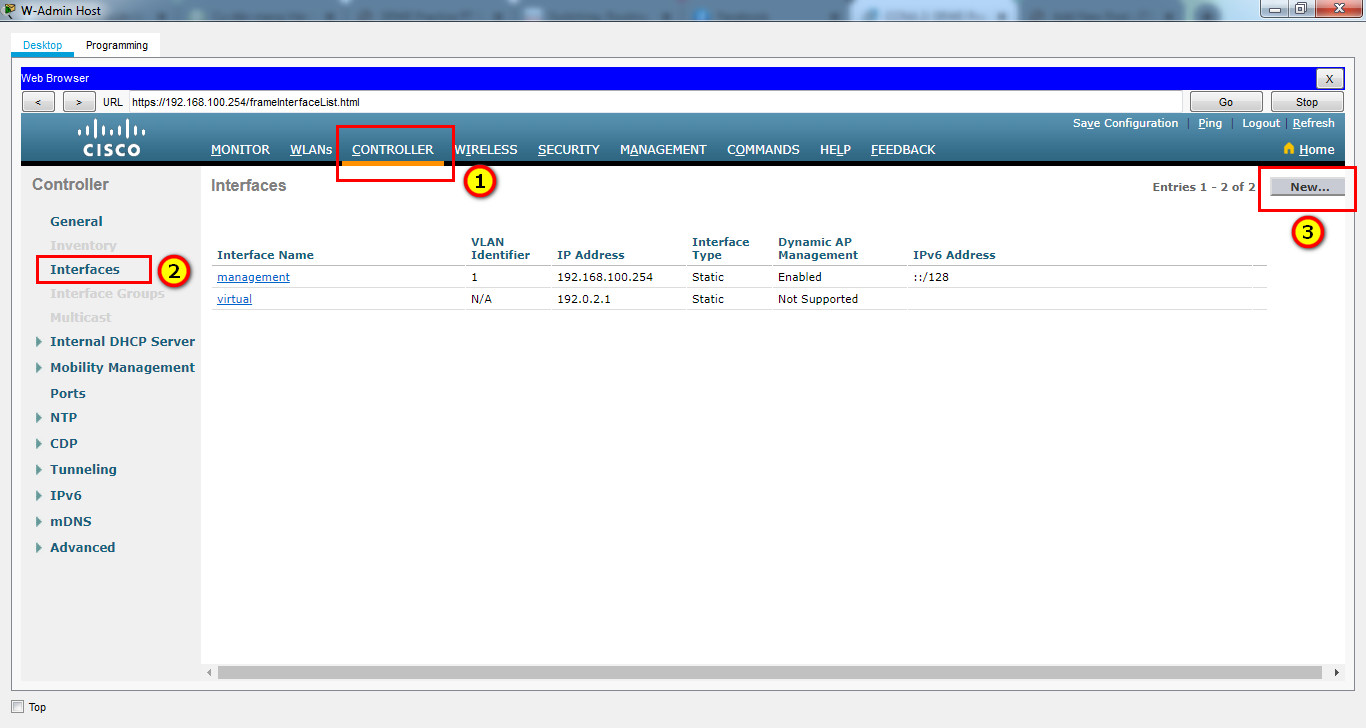
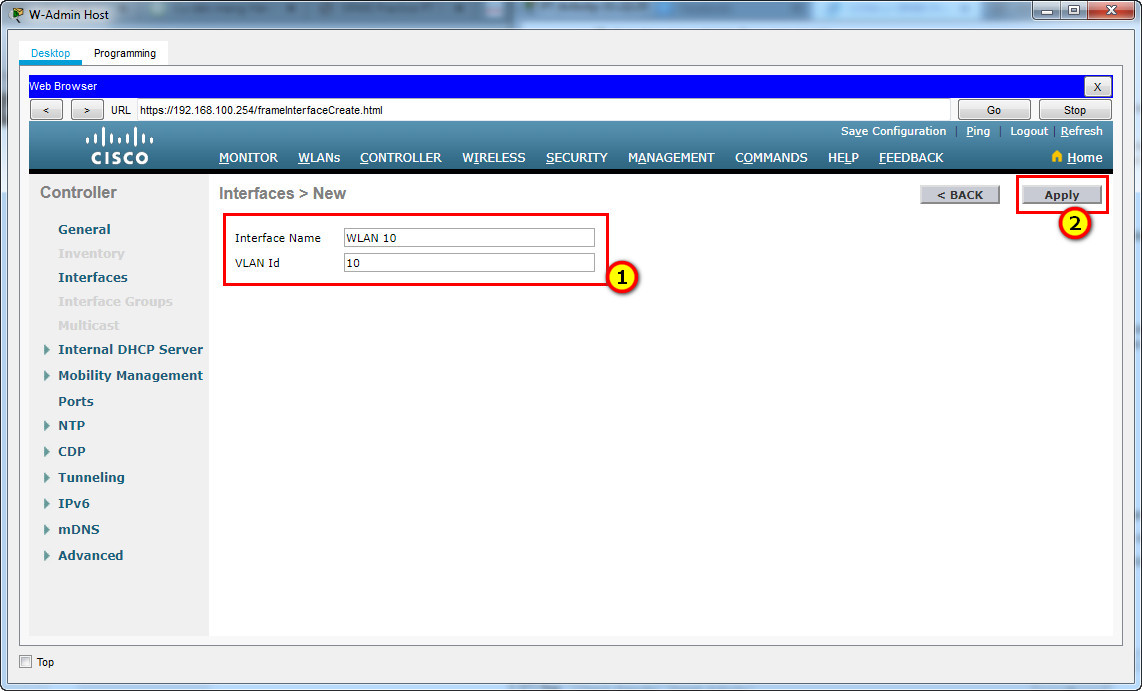
Step 1: Configure a VLAN interface.
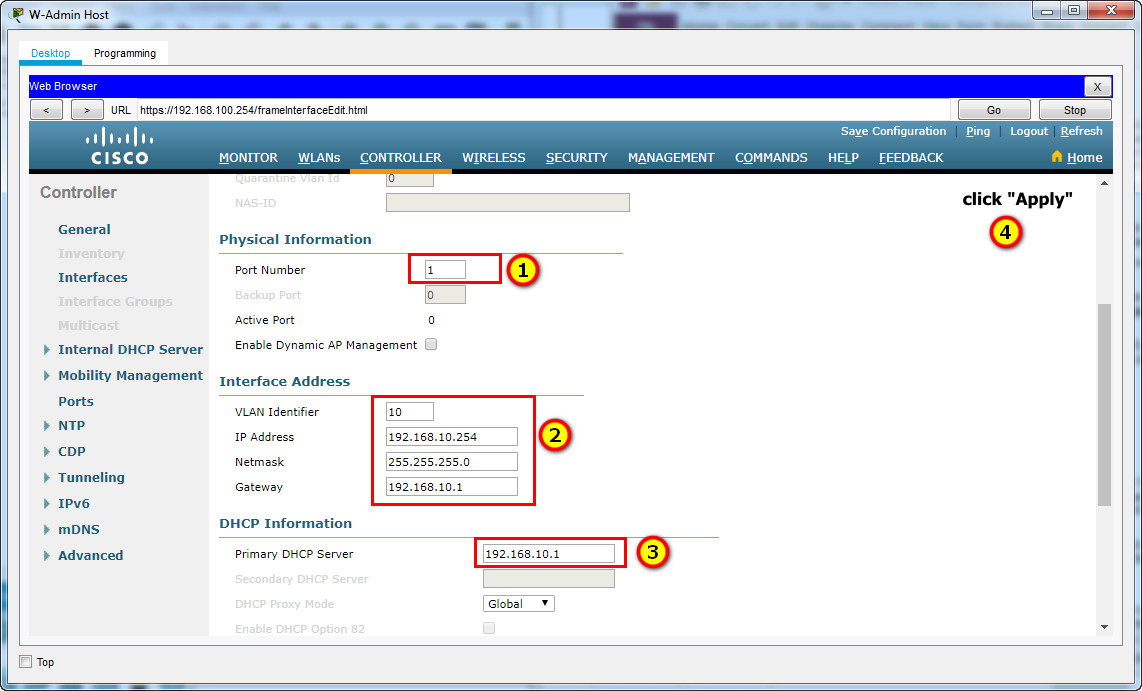
a. Create a new interface and name it WLAN 10. The interface should use VLAN 10 and physical port 1.
b. Use the information in the addressing table to configure the addressing settings for the interface. The interface will be using a DHCP pool that is configured on the subinterface that is assigned to VLAN 10 on router Branch-101 (or RTR-Branch/R-B-10).
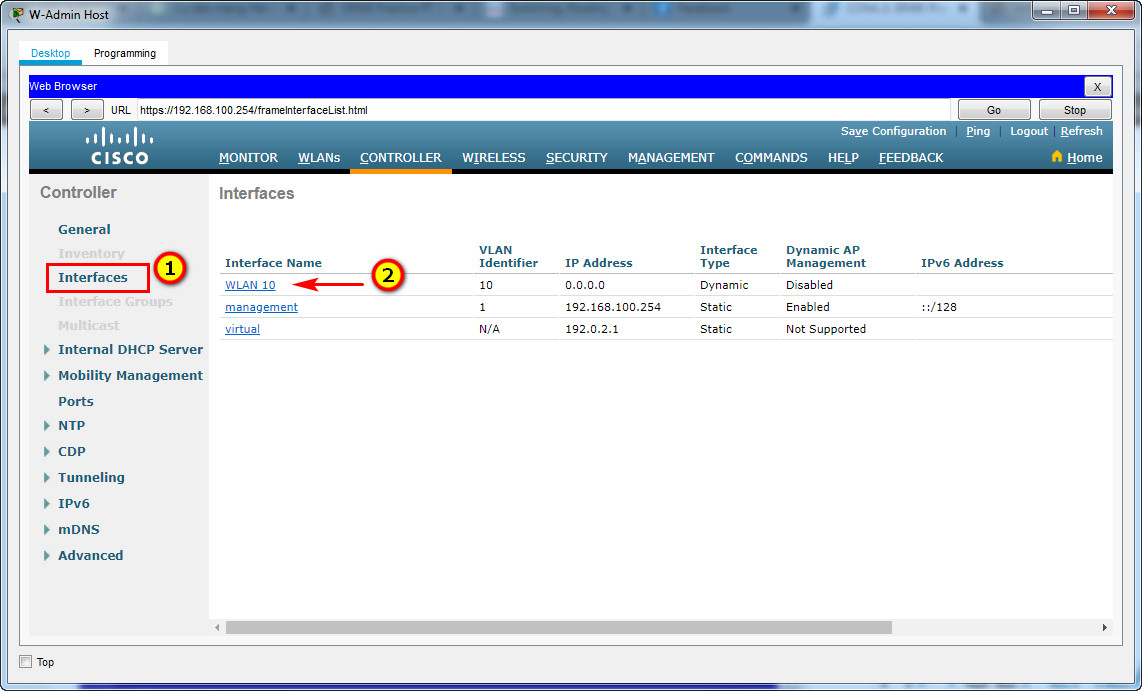
Port Number: 1
VLAN Identifier: 10
IP Address: 192.168.10.254
Netmask: 255.255.255.0
Gateway: 192.168.10.1
Primary DHCP Server: 192.168.10.1
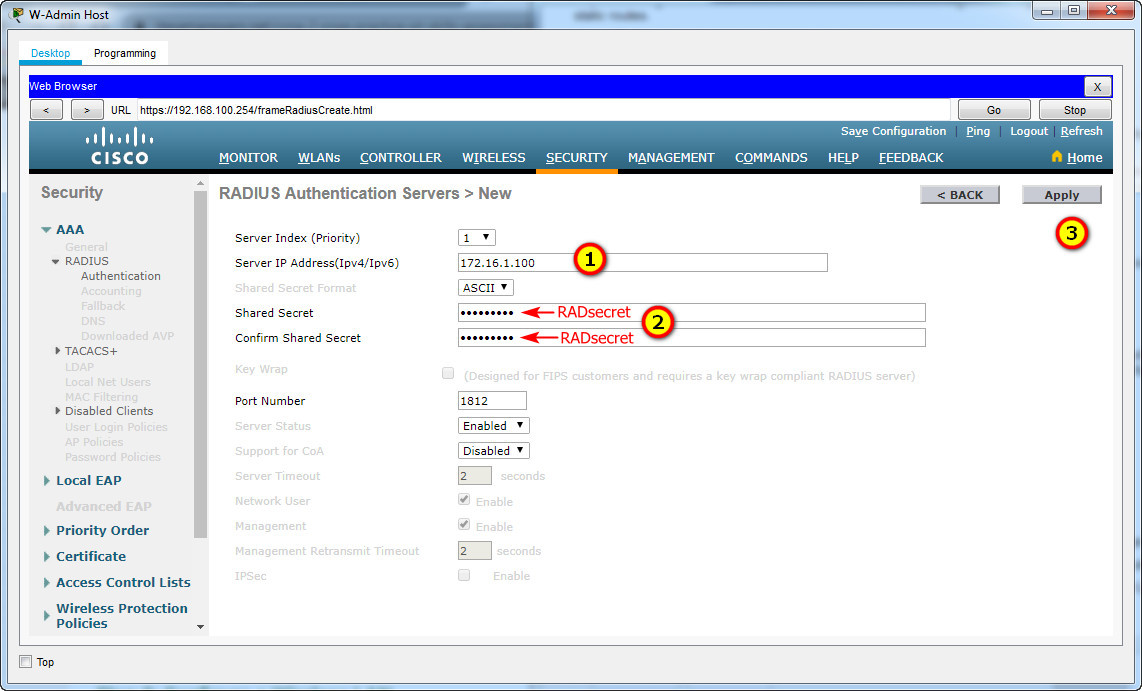
Step 2: Configure a RADIUS server.
a. Configure the WLC with the RADIUS server IPv4 address.
b. Use a shared secret of RADsecret.
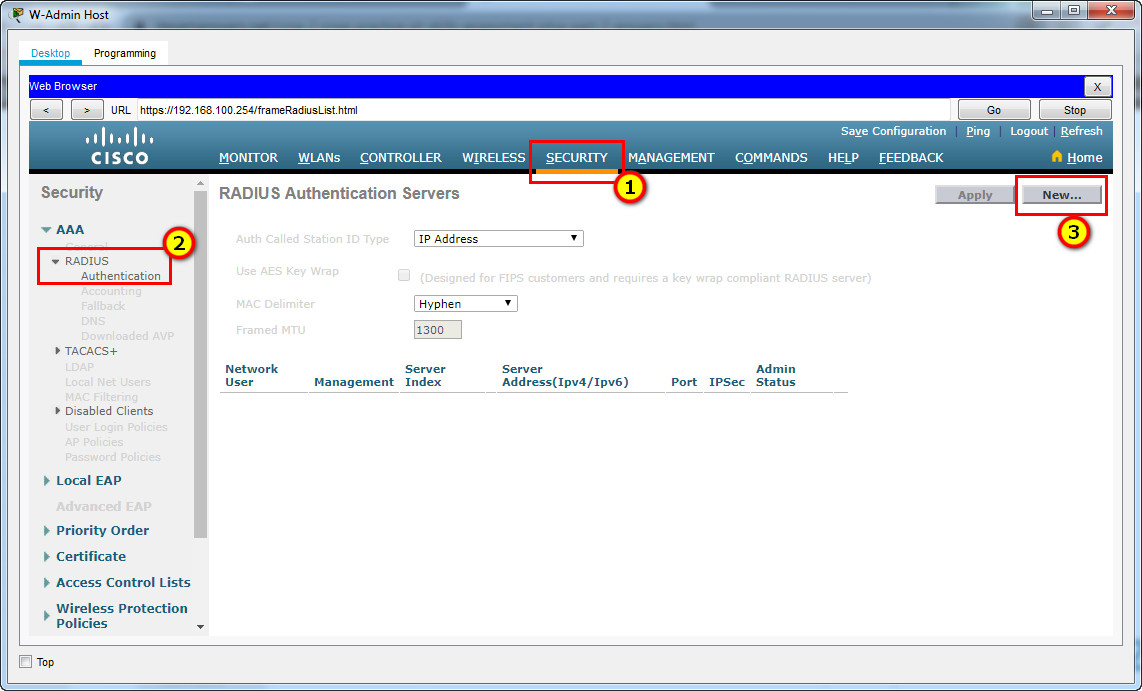
RADIUS Server:
Server IP Address: 172.16.1.100
Shared Secret: RADsecret
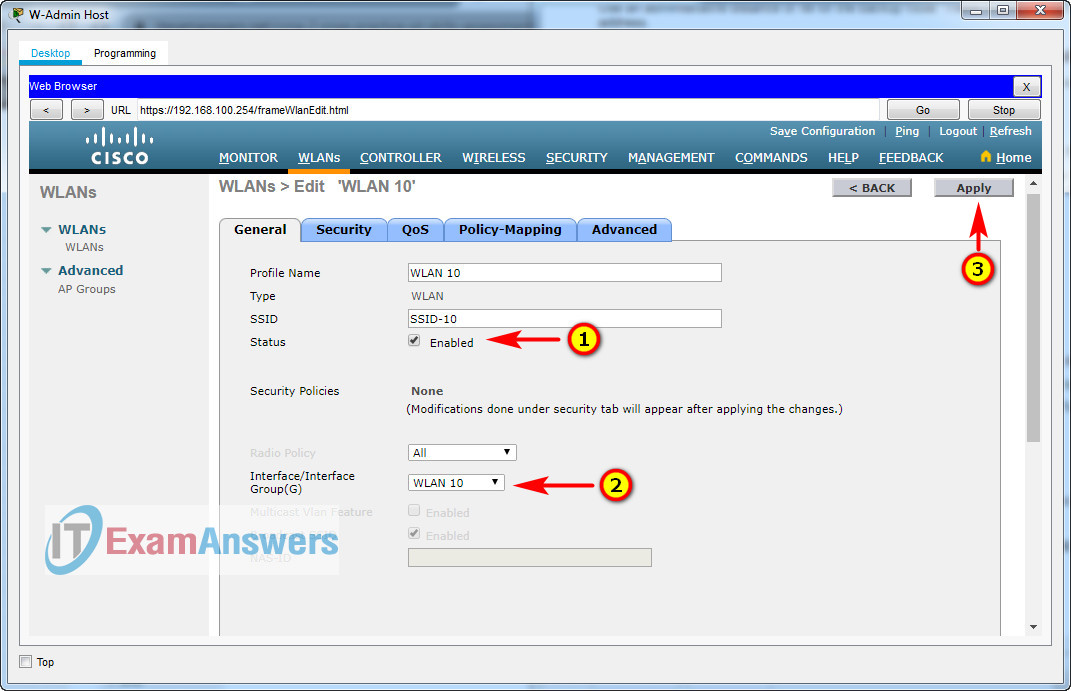
Step 3: Configure a Wireless LAN.
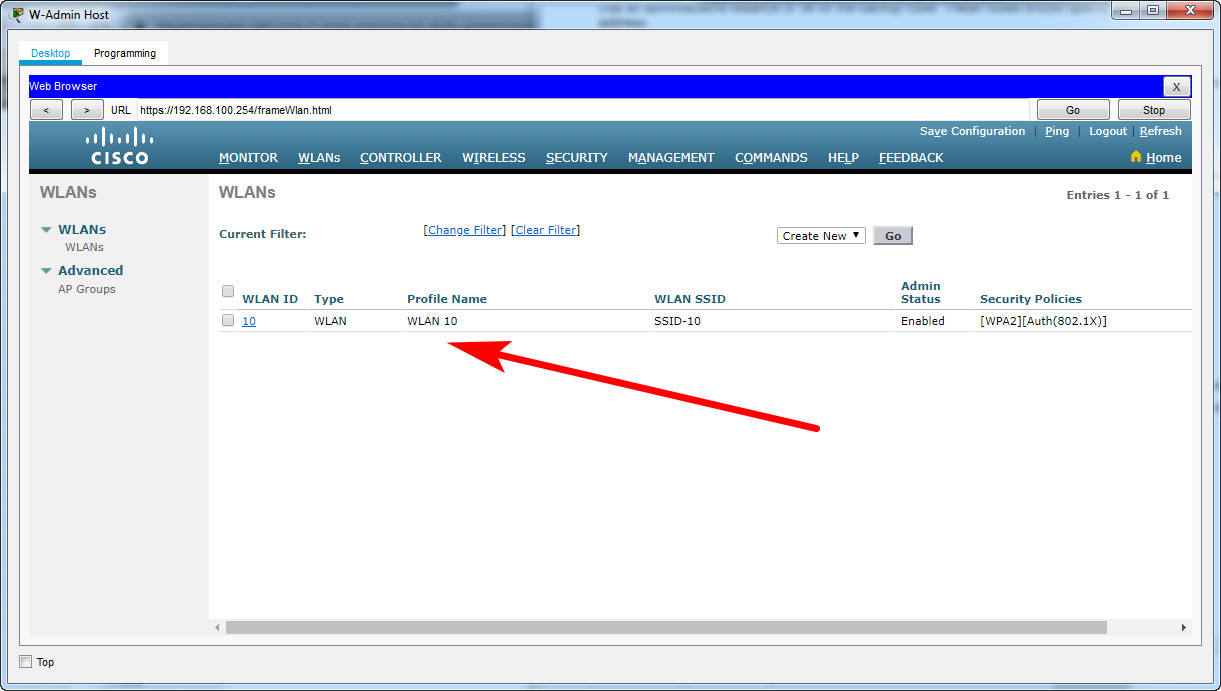
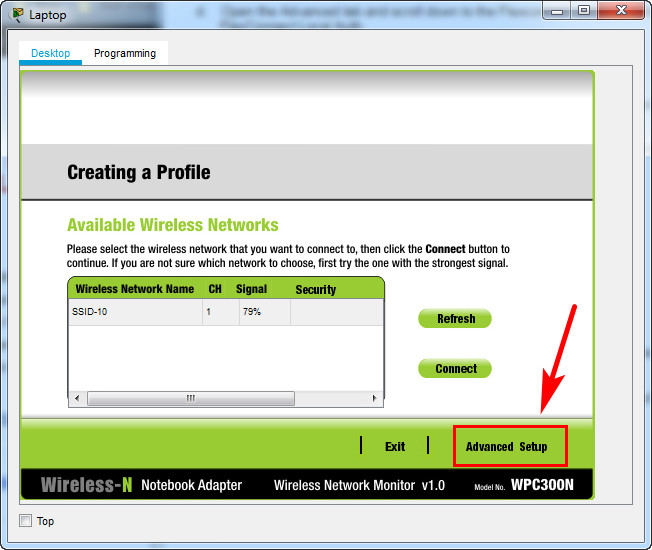
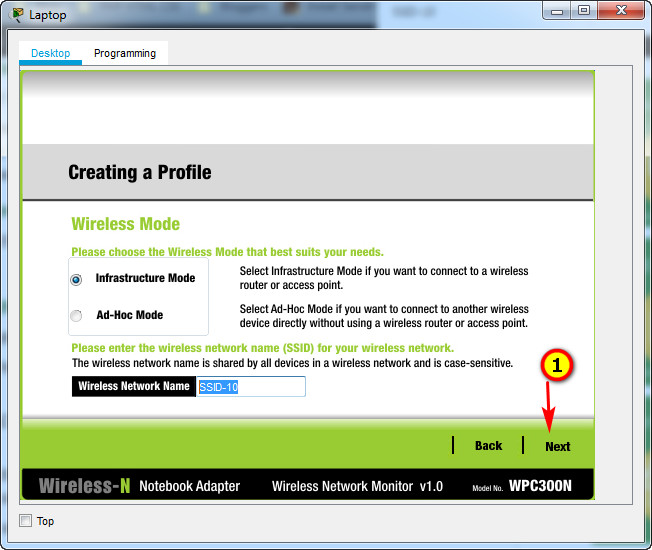
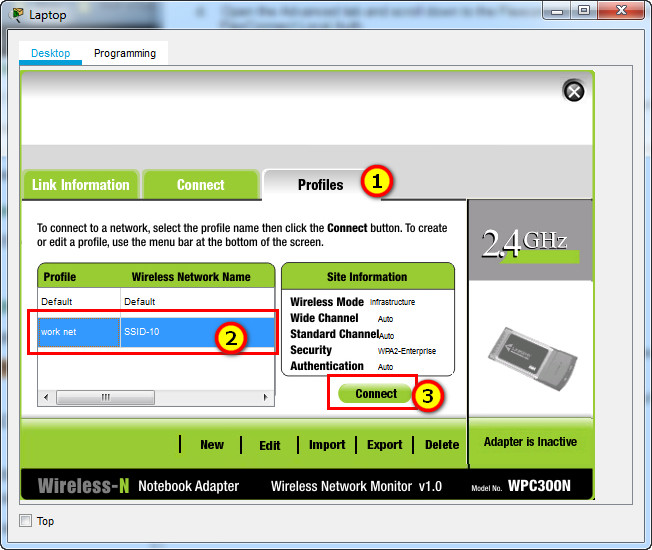
a. Create a new WLAN. Name it WLAN 10 and configure the SSID as SSID-10.
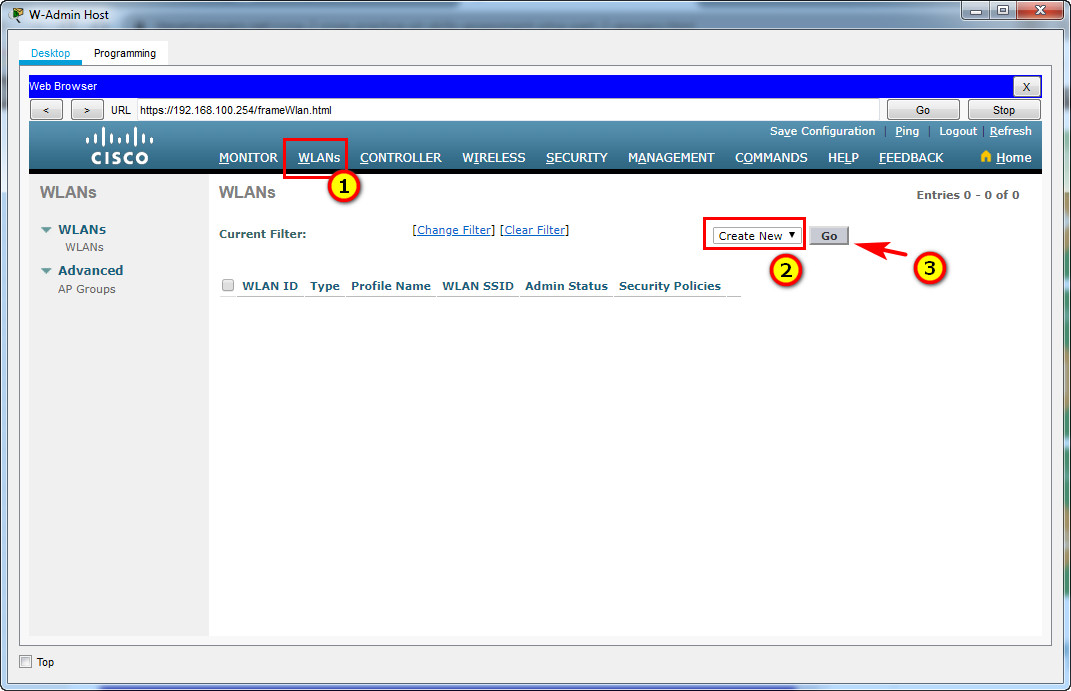
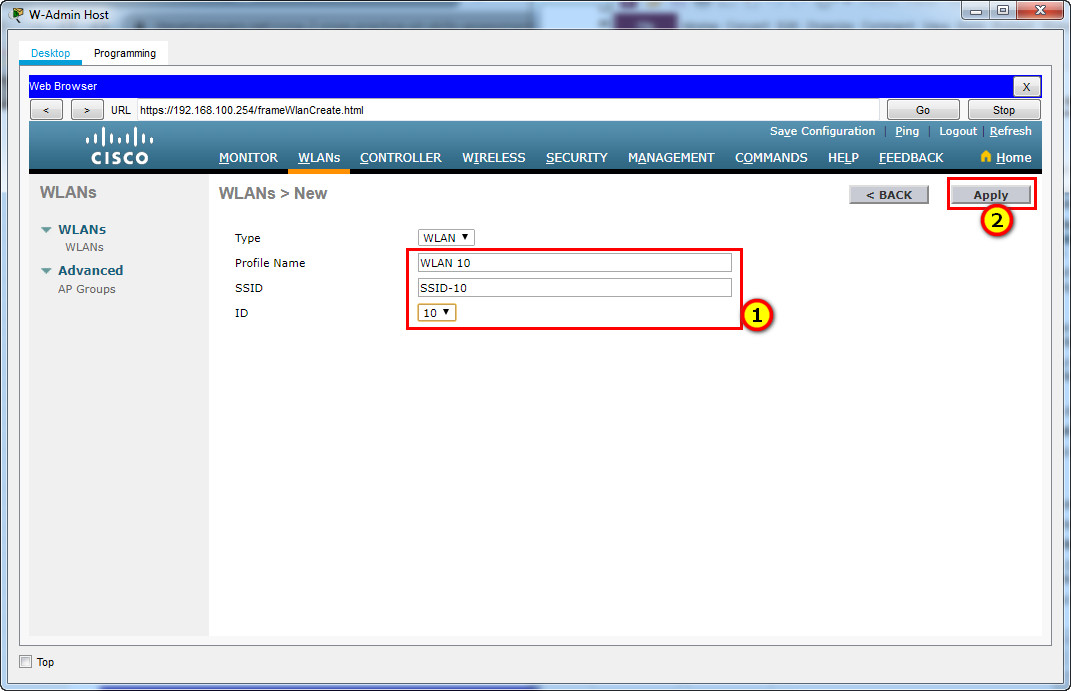
b. The wireless LAN should use the VLAN interface that was previously configured.
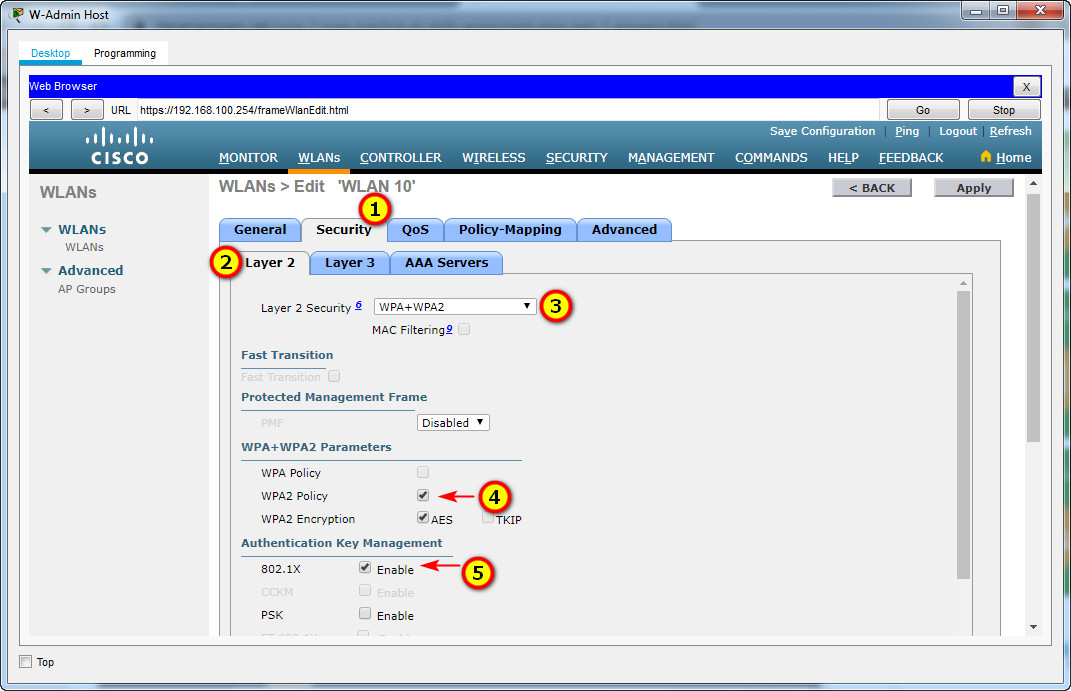
c. Configure the WLAN to use the WPA2 security policy and dot1x Authentication Key Management.
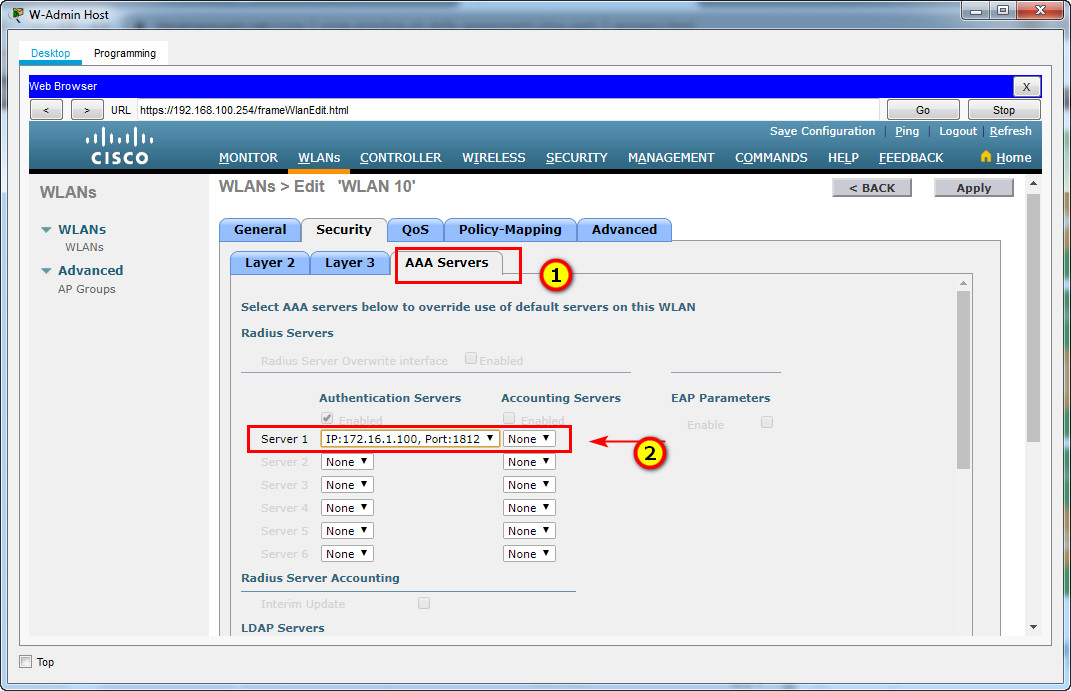
d. Configure the WLAN to use the RADIUS server that was previously configured to authenticate wireless users.
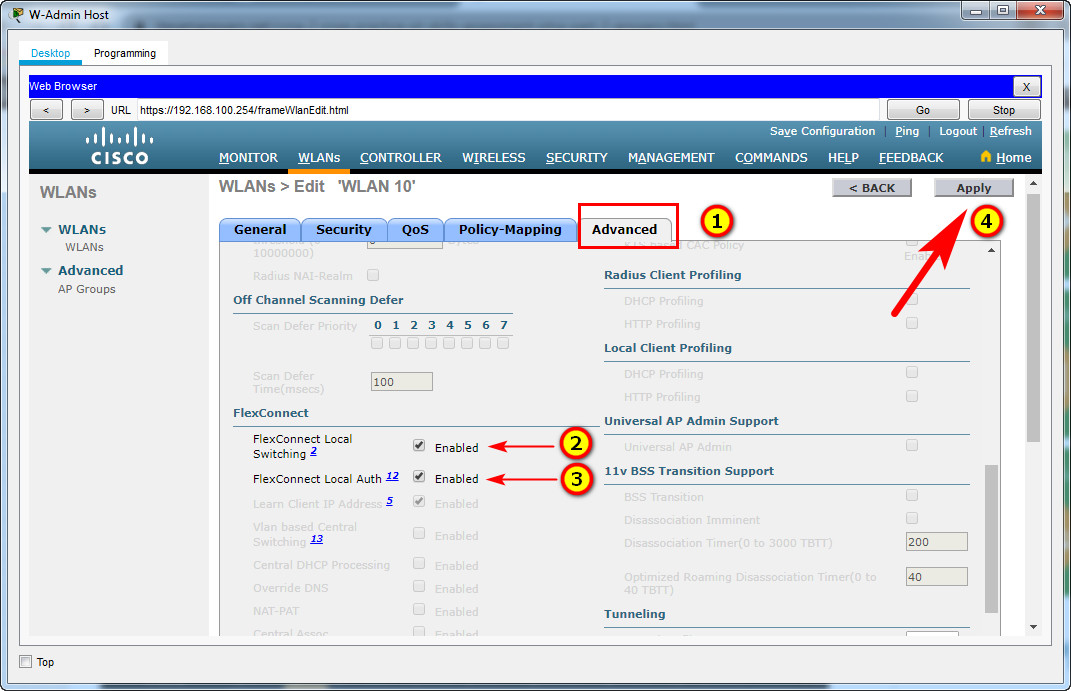
e. Open the Advanced tab and scroll down to the Flexconnect sections. Activate FlexConnect Local Switching and FlexConnect Local Auth.
f. Verify that the WLAN is configured and operational.
Step 4: Configure a DHCP scope for the management network.
Configure a new DHCP scope to be used by the LAPs and other management devices on the network.
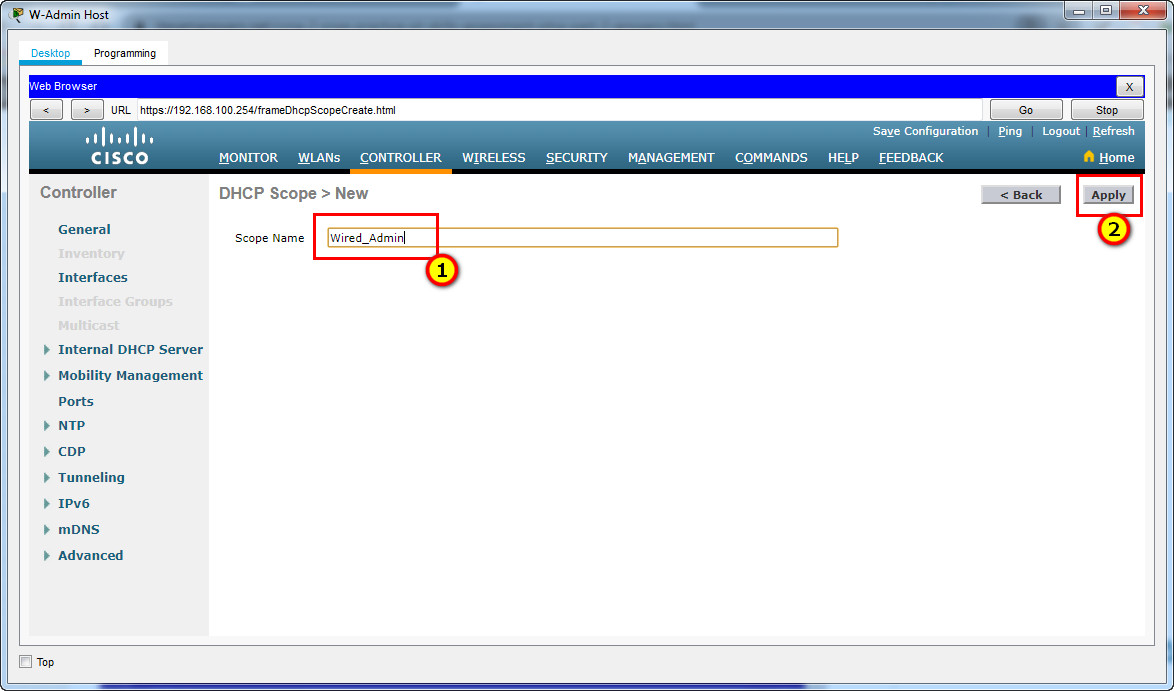
a. Name the DHCP scope Wired_Admin.
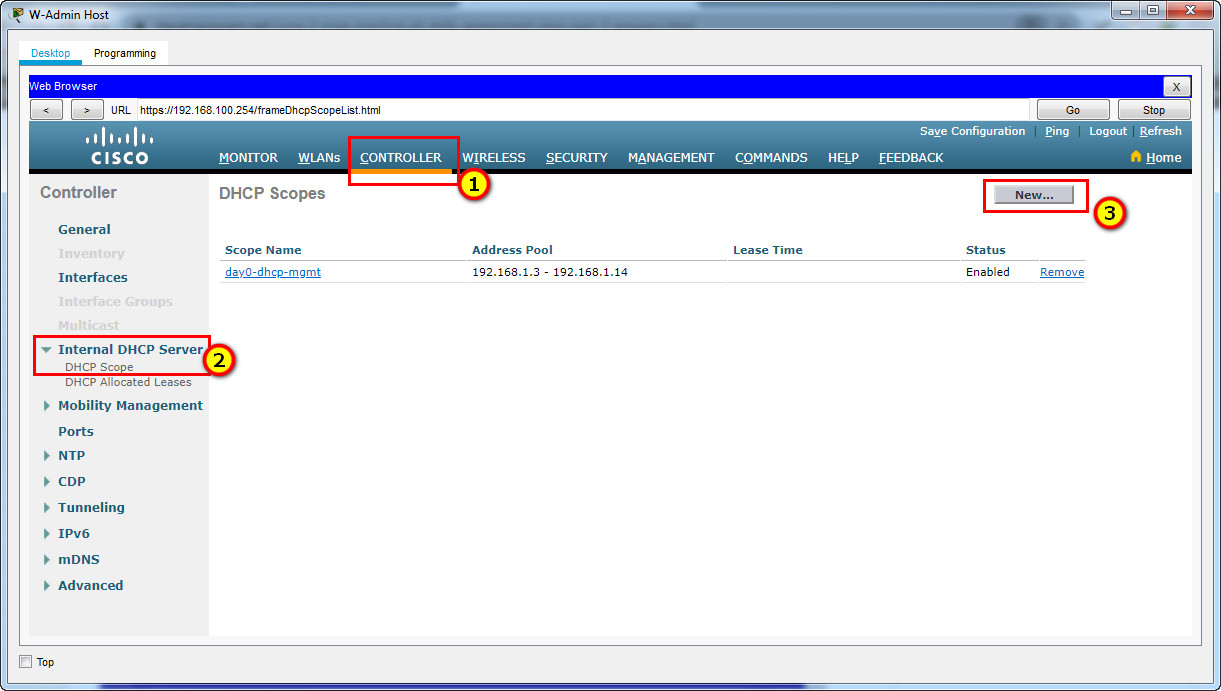
b. Start the scope at address 192.168.100.240. End the scope at address 192.168.100.249.
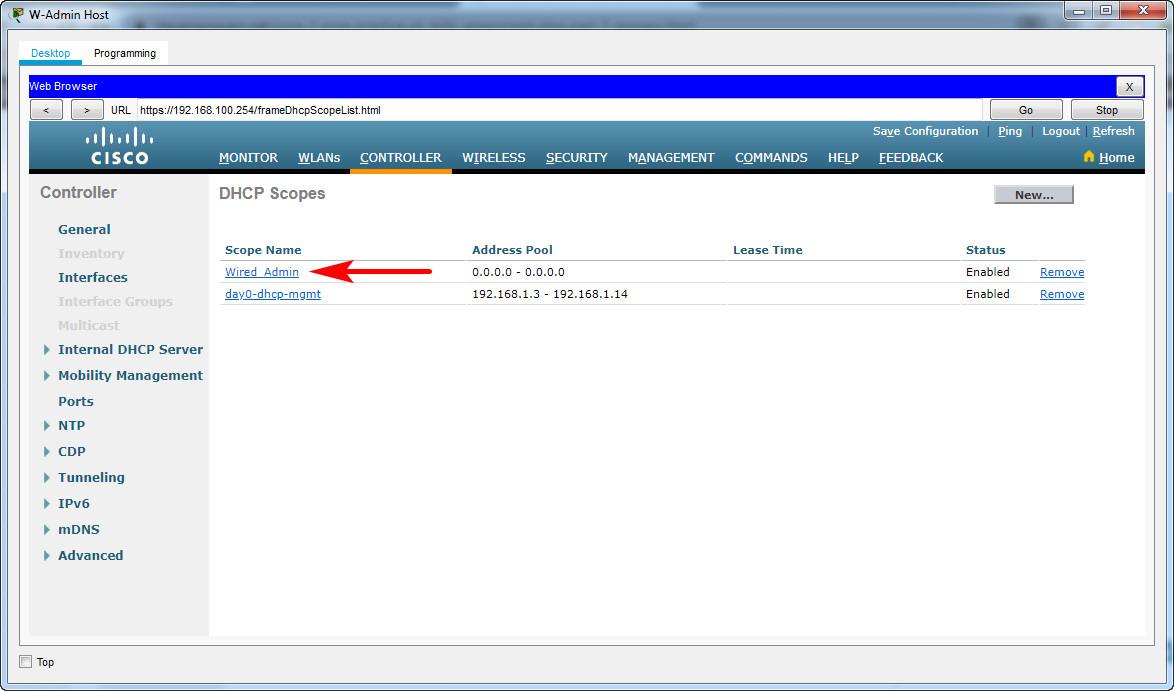
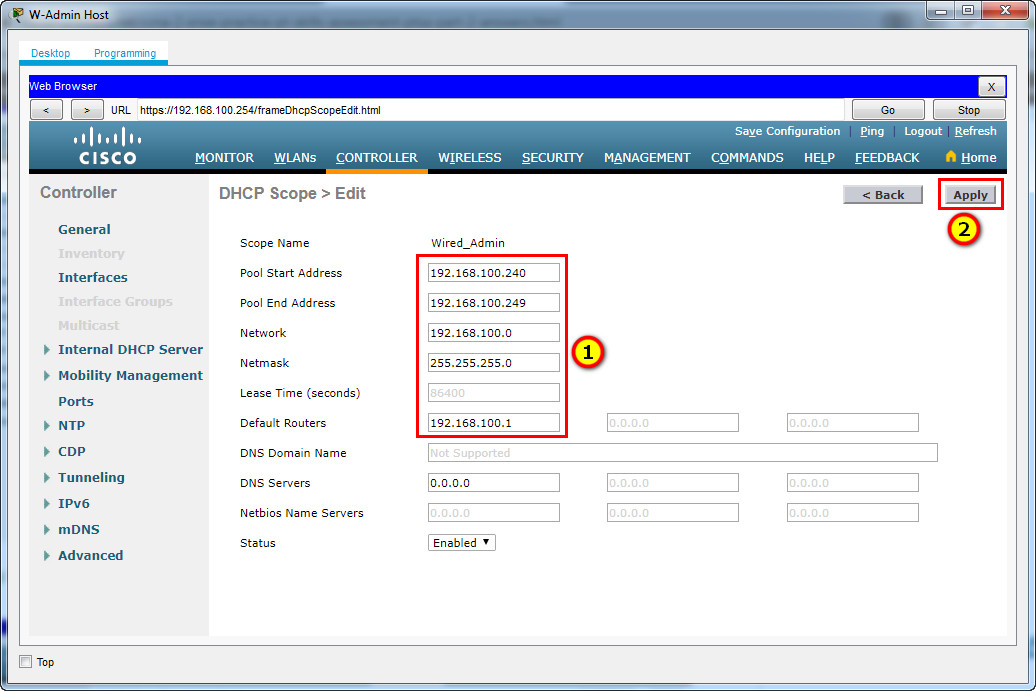
Pool Start Address: 192.168.100.240
Pool End Address: 192.168.100.249
Network: 192.168.100.0
Netmask: 255.255.255.0
Default Routers: 192.168.100.1
c. Other information that is required can be found in the Addressing Table.
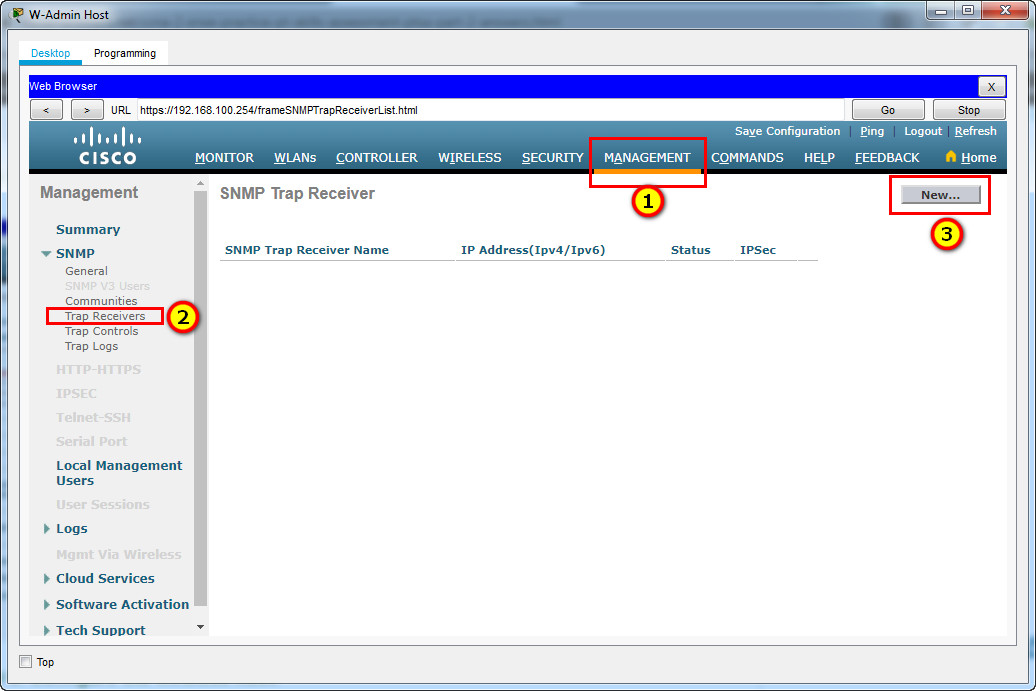
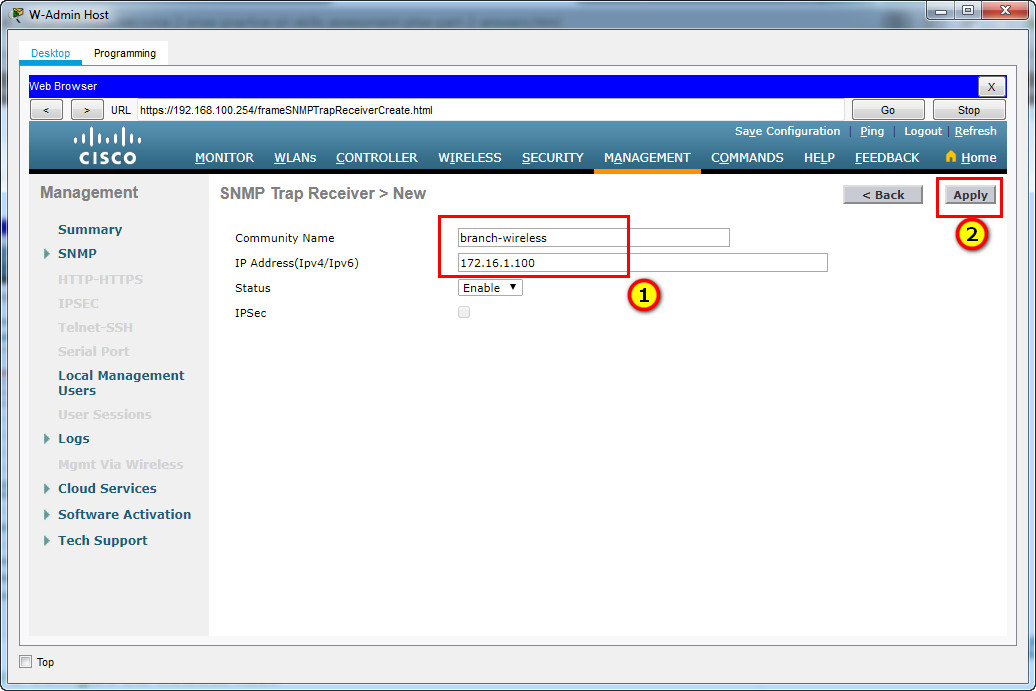
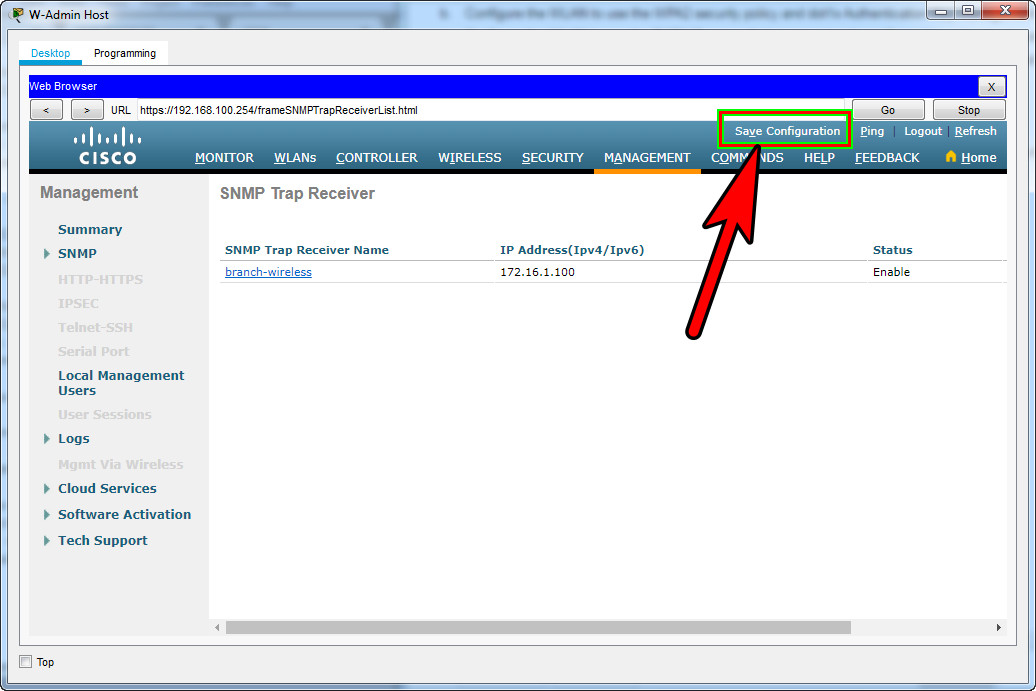
Step 5: Configure an SNMP server.
Configure an SNMP server to receive traps from the WLC.
a. Use the community name branch-wireless.
b. Use 172.16.1.100 as the server address.
Step 6: Configure the wireless host.
Configure the Laptop (or Wireless Host/LT-1 laptop) to connect to the WLAN.
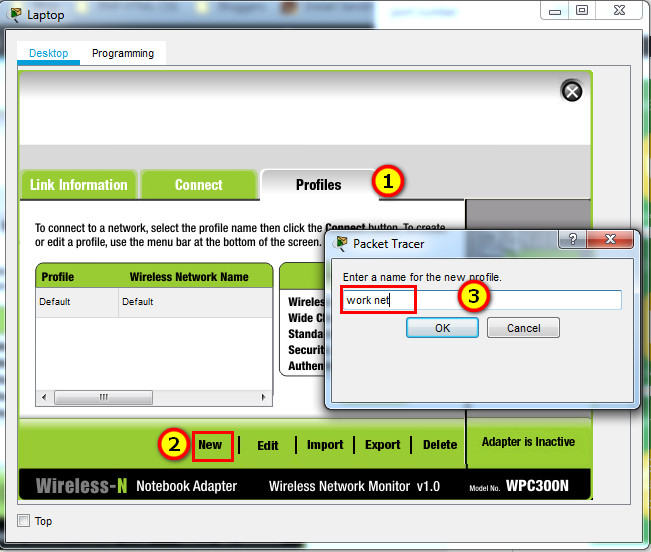
a. Create a new wireless profile on the host. Use the name work net for the profile.
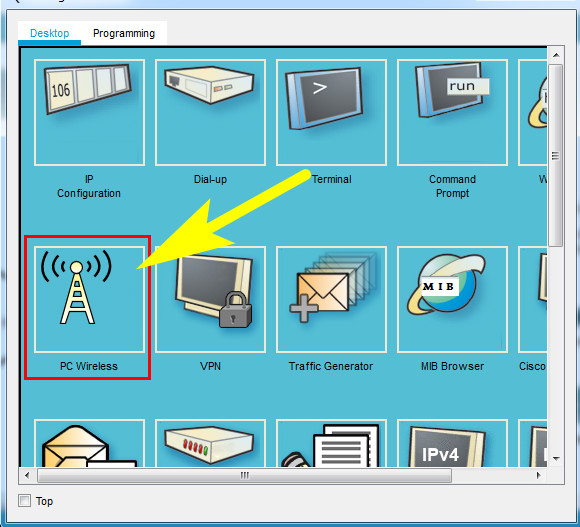
Click Wireless Host Laptop and open the PC Wireless app
b. Configure the profile for the SSID of the WLAN.
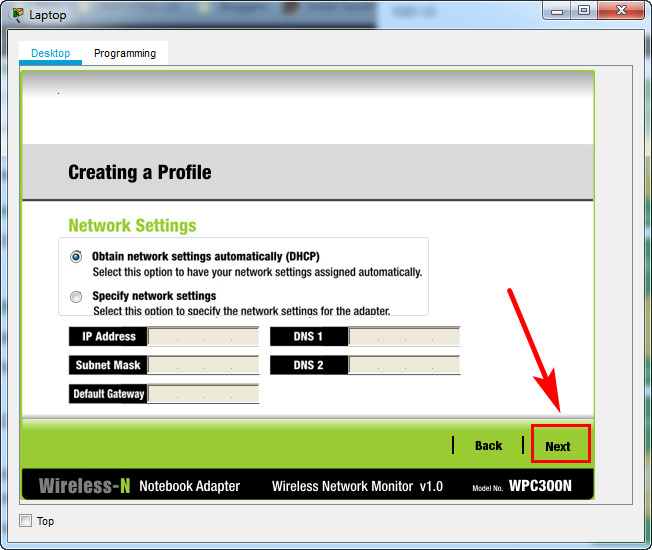
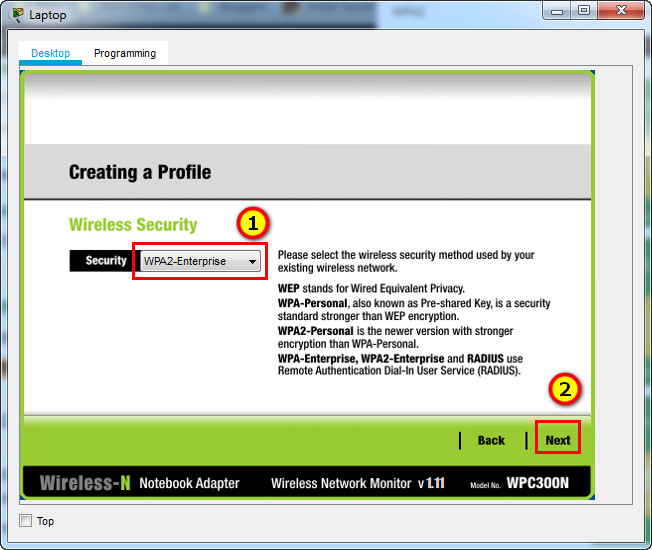
c. Use enterprise authentication with a username of user1 and password of user1Pass.
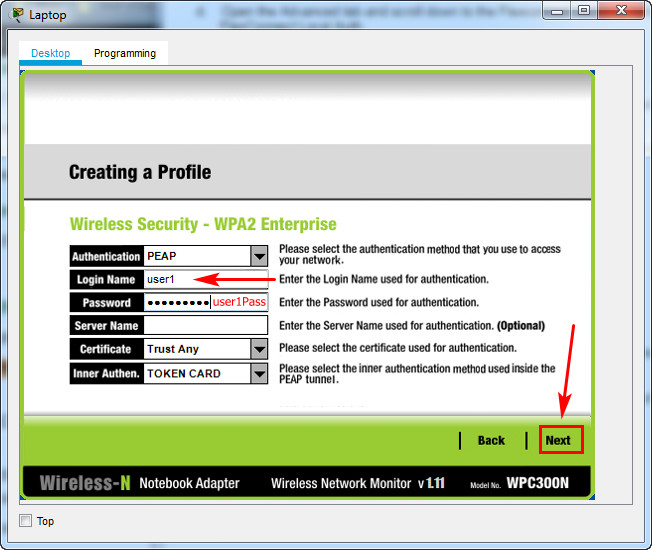
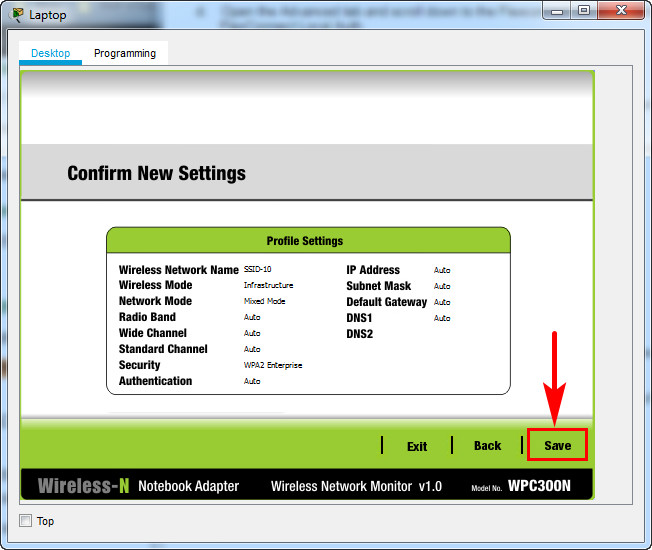
d. When you are finished, click Connect to Network. It will take time for the connection to be established.
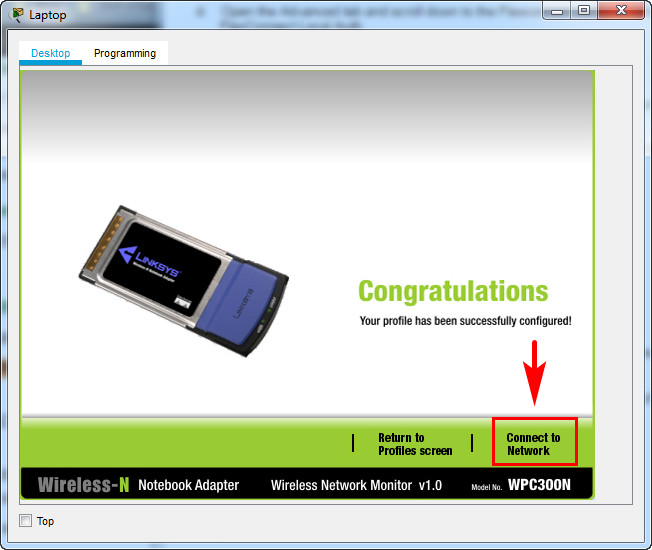
Result
You can click the Fast Forward Time button speed up the process.
Fast script – Answers
Part 1 + 2 + 3
S1-1 Switch (or SW-1/Sw-A)
en config t vlan 10 name users vlan 999 name unused exit interface range f0/1-5, g0/1 switchport mode access switchport access vlan 10 interface range f0/1-5 switchport port-security switchport port-security maximum 4 switchport port-security violation restrict switchport port-security aging time 10 switchport port-security mac-address sticky exit interface f0/1 switchport port-security mac-address 00D0.D3DC.2825 exit ip dhcp snooping ip dhcp snooping vlan 10,999 interface range f0/1-5, g0/1 ip dhcp snooping limit rate 5 exit interface g0/1 ip dhcp snooping trust exit ip arp inspection vlan 10,999 interface g0/1 ip arp inspection trust exit interface range f0/1-5 spanning-tree portfast spanning-tree bpduguard enable interface range f0/6-24, g0/2 switchport mode access switchport access vlan 999 shutdown
Branch-101 Router (or RTR-Branch/R-B-10)
en config t interface g0/0/0.10 description WLAN users encapsulation dot1q 10 ip address 192.168.10.1 255.255.255.0 exit ip dhcp excluded-address 192.168.10.1 ip dhcp excluded-address 192.168.10.254 ip dhcp pool WLAN-hosts network 192.168.10.0 255.255.255.0 default-router 192.168.10.1 dns-server 198.51.100.163 exit interface g0/0/1 ip address dhcp end exit
Central Router (or RTR-HQ/R-1-A)
enable conf t ip route 0.0.0.0 0.0.0.0 g0/0/2 ip route 0.0.0.0 0.0.0.0 s0/1/0 10 ip route 192.168.10.0 255.255.255.0 g0/0/2 ip route 192.168.10.0 255.255.255.0 s0/1/0 10 ip route 192.168.3.122 255.255.255.255 s0/1/1 ipv6 unicast-routing ipv6 route ::/0 2001:DB8:ACAD:A::2 ipv6 route ::/0 2001:db8:acad:b::2 10 ipv6 route 2001:db8:acad:3::122/128 2001:db8:acad:d::2
Branch-101 Router (or RTR-Branch/R-B-10)
enable configure terminal ip route 0.0.0.0 0.0.0.0 g0/0/1 ip route 0.0.0.0 0.0.0.0 s0/1/0 10 ipv6 unicast-routing ipv6 route ::/0 2001:DB8:ACAD:C::1 ipv6 route ::/0 2001:DB8:ACAD:B::1 10

I can’t enter realtime mode, so it’s impossible to configure the WLC
hi , stil valid??
There is an error in the packet tracer that did not allow Laptop to reach RADIUS Server and authenticate. The RADIUS server is connected to f0/1 on S4-1 but it should be connected to f0/10. Once I connected the RADIUS server to f0/10 the laptop was able to connect to LAP-1.
same problem can u help me ?
Error fixed, redownload the pka file here.
Completed on Dec. 20, 2023 – scored 98.0%. Not sure what I missed.
Did you fix the mistake they make on ip dhcp excluded-addresses? (they put 192.168.10.254 instead of 192.168.100.254 for the management IP of WLC)
ID 2 Complete but I’ve got 91%. The wireless was configured and worked following all instructions. November 2023.
I could not connect to wireless – got 84
valid 100%
what if I entered the url but the ouput is request timeout
add s in http like this https
Excuse me. Do i need just to write everything thats in Part 1+2+3 or i need to do every single step to complete it 100%?
I asking this because i got around 50% on id 0
Part 1+2+3 then u scroll up to part 4 and follow the instructions since there
Thanks for the help I did this on 28/2/2023 with the ID 0 and got a 100%
2022/12/17 answers are still valid..
27/11/2022 i got ID 0 i passed with 95%
Network:WLC-10:DHCP Server List:DHCP Server:Pools:Wired_Admin:Max Users :Incorrect
why Server Reset Connection,, any one can help me?
use https
I followed these instructions exactly and got an 86% to anyone wondering.
Just so you guys know, for ID 1, I wasn’t able to get the laptop to connect. Everything was configured properly, but the laptop would not connect. So, I submitted the assignment as-is, and got 100%
Me pasó igual, repetí el paso 6 para el wireless y no se conectó. aún así aprobé con 100%. Gracias. 24/12/2023.
i got a “none” profiency for IPv6 Static Routing.
anybody know what went wrong?
I switched the ID (tab on top of the topology) to the one that corresponded to me, and I got a passing grade. Be sure you pick the right ID, fellas
They are totall the same.
Excellent I followed all the steps and got 100%.
I followed and got 100
What’s the difference between ID 1 an ID 2?
Alm
R-B-10(config)#ipv6 route ::/0 2001:db8:acad:c::2
% Not allowed to point static routes through yourself
Percentage: 100%
sh running
S1-1#sh ru
Building configuration…
Current configuration : 4838 bytes
!
version 12.2
no service timestamps log datetime msec
no service timestamps debug datetime msec
no service password-encryption
!
hostname S1-1
!
ip arp inspection vlan 10,999
!
ip dhcp snooping vlan 10,999
ip dhcp snooping
!
spanning-tree mode pvst
spanning-tree extend system-id
!
interface FastEthernet0/1
description “A PC-A”
switchport access vlan 10
ip dhcp snooping limit rate 5
switchport mode access
switchport port-security
switchport port-security maximum 4
switchport port-security mac-address sticky
switchport port-security violation restrict
switchport port-security mac-address 00D0.D3DC.2825
switchport port-security aging time 10
spanning-tree portfast
spanning-tree bpduguard enable
!
interface FastEthernet0/2
description “A PC-B”
switchport access vlan 10
ip dhcp snooping limit rate 5
switchport mode access
switchport port-security
switchport port-security maximum 4
switchport port-security mac-address sticky
switchport port-security violation restrict
switchport port-security aging time 10
spanning-tree portfast
spanning-tree bpduguard enable
!
interface FastEthernet0/3
description ACCESO VLAN 10
switchport access vlan 10
ip dhcp snooping limit rate 5
switchport mode access
switchport port-security
switchport port-security maximum 4
switchport port-security mac-address sticky
switchport port-security violation restrict
switchport port-security aging time 10
spanning-tree portfast
spanning-tree bpduguard enable
!
interface FastEthernet0/4
description ACCESO VLAN 10
switchport access vlan 10
ip dhcp snooping limit rate 5
switchport mode access
switchport port-security
switchport port-security maximum 4
switchport port-security mac-address sticky
switchport port-security violation restrict
switchport port-security aging time 10
spanning-tree portfast
spanning-tree bpduguard enable
!
interface FastEthernet0/5
description ACCESO VLAN 10
switchport access vlan 10
ip dhcp snooping limit rate 5
switchport mode access
switchport port-security
switchport port-security maximum 4
switchport port-security mac-address sticky
switchport port-security violation restrict
switchport port-security aging time 10
spanning-tree portfast
spanning-tree bpduguard enable
!
interface FastEthernet0/6
description “ADM DOWN”
switchport access vlan 999
switchport mode access
shutdown
!
interface FastEthernet0/7
description “ADM DOWN”
switchport access vlan 999
switchport mode access
shutdown
!
interface FastEthernet0/8
description “ADM DOWN”
switchport access vlan 999
switchport mode access
shutdown
!
interface FastEthernet0/9
description “ADM DOWN”
switchport access vlan 999
switchport mode access
shutdown
!
interface FastEthernet0/10
description “ADM DOWN”
switchport access vlan 999
switchport mode access
shutdown
!
interface FastEthernet0/11
description “ADM DOWN”
switchport access vlan 999
switchport mode access
shutdown
!
interface FastEthernet0/12
description “ADM DOWN”
switchport access vlan 999
switchport mode access
shutdown
!
interface FastEthernet0/13
description “ADM DOWN”
switchport access vlan 999
switchport mode access
shutdown
!
interface FastEthernet0/14
description “ADM DOWN”
switchport access vlan 999
switchport mode access
shutdown
!
interface FastEthernet0/15
description “ADM DOWN”
switchport access vlan 999
switchport mode access
shutdown
!
interface FastEthernet0/16
description “ADM DOWN”
switchport access vlan 999
switchport mode access
shutdown
!
interface FastEthernet0/17
description “ADM DOWN”
switchport access vlan 999
switchport mode access
shutdown
!
interface FastEthernet0/18
description “ADM DOWN”
switchport access vlan 999
switchport mode access
shutdown
!
interface FastEthernet0/19
description “ADM DOWN”
switchport access vlan 999
switchport mode access
shutdown
!
interface FastEthernet0/20
description “ADM DOWN”
switchport access vlan 999
switchport mode access
shutdown
!
interface FastEthernet0/21
description “ADM DOWN”
switchport access vlan 999
switchport mode access
shutdown
!
interface FastEthernet0/22
description “ADM DOWN”
switchport access vlan 999
switchport mode access
shutdown
!
interface FastEthernet0/23
description “ADM DOWN”
switchport access vlan 999
switchport mode access
shutdown
!
interface FastEthernet0/24
description “ADM DOWN”
switchport access vlan 999
switchport mode access
shutdown
!
interface GigabitEthernet0/1
description A Central
switchport access vlan 10
ip arp inspection trust
ip dhcp snooping trust
switchport mode access
!
interface GigabitEthernet0/2
description “ADM DOWN”
switchport access vlan 999
switchport mode access
shutdown
!
interface Vlan1
no ip address
shutdown
!
line con 0
!
line vty 0 4
login
line vty 5 15
login
!
end
————————————————————
RTR-Cloud#sh ru
Building configuration…
Current configuration : 2083 bytes
!
version 15.4
no service timestamps log datetime msec
no service timestamps debug datetime msec
no service password-encryption
!
hostname RTR-Cloud
!
ip dhcp excluded-address 10.3.0.1
!
ip dhcp pool Branch-Ether
network 10.3.0.0 255.255.255.252
!
!
!
ip cef
ipv6 unicast-routing
!
no ipv6 cef
!
spanning-tree mode pvst
!
interface GigabitEthernet0/0/0
description A Central
ip address 10.1.0.2 255.255.255.252
duplex auto
speed auto
ipv6 address 2001:DB8:ACAD:A::2/64
!
interface GigabitEthernet0/0/1
description A Branch-101
ip address 10.3.0.1 255.255.255.252
duplex auto
speed auto
ipv6 address FE80::3 link-local
ipv6 address 2001:DB8:ACAD:C::1/64
!
interface GigabitEthernet0/0/2
description A Nube
media-type sfp
no ip address
duplex auto
speed auto
!
interface GigabitEthernet0/0/2.10
encapsulation dot1Q 10
ip address 203.0.113.1 255.255.255.0
ipv6 address FE80::4 link-local
ipv6 address 2001:DB8:CAFE::1/64
!
interface GigabitEthernet0/0/2.198
encapsulation dot1Q 198
ip address 198.51.100.1 255.255.255.0
ipv6 address FE80::4 link-local
ipv6 address 2001:DB8:FACE::1/64
!
interface Vlan1
no ip address
shutdown
!
ip classless
ip route 192.168.1.0 255.255.255.0 GigabitEthernet0/0/0
ip route 192.168.2.0 255.255.255.0 GigabitEthernet0/0/0
ip route 192.168.2.0 255.255.255.0 GigabitEthernet0/0/1 10
ip route 192.168.1.0 255.255.255.0 GigabitEthernet0/0/1 10
ip route 192.168.100.0 255.255.255.0 GigabitEthernet0/0/1
ip route 192.168.10.0 255.255.255.0 GigabitEthernet0/0/1
ip route 192.168.3.0 255.255.255.0 GigabitEthernet0/0/0
ip route 192.168.3.0 255.255.255.0 GigabitEthernet0/0/1 10
!
ip flow-export version 9
!
ipv6 route 2001:DB8:ACAD:3::/64 2001:DB8:ACAD:A::1
ipv6 route 2001:DB8:ACAD:3::/64 2001:DB8:ACAD:C::2 10
ipv6 route 2001:DB8:ACAD:1::/64 2001:DB8:ACAD:A::1
ipv6 route 2001:DB8:ACAD:1::/64 2001:DB8:ACAD:C::2 10
ipv6 route 2001:DB8:ACAD:2::/64 2001:DB8:ACAD:A::1
ipv6 route 2001:DB8:ACAD:2::/64 2001:DB8:ACAD:C::2 10
!
line con 0
!
line aux 0
!
line vty 0 4
login
!
!
!
end
———————————————————————-
Branch-101#sh ru
Building configuration…
Current configuration : 1675 bytes
!
version 15.4
no service timestamps log datetime msec
no service timestamps debug datetime msec
no service password-encryption
!
hostname Branch-101
!
ip dhcp excluded-address 192.168.10.1
ip dhcp excluded-address 192.168.10.254
!
ip dhcp pool WLAN-hosts
network 192.168.10.0 255.255.255.0
default-router 192.168.10.1
dns-server 198.51.100.163
!
no ip cef
ipv6 unicast-routing
!
no ipv6 cef
!
spanning-tree mode pvst
!
interface GigabitEthernet0/0/0
description A S4-1
no ip address
duplex auto
speed auto
!
interface GigabitEthernet0/0/0.10
description WLAN users
encapsulation dot1Q 10
ip address 192.168.10.1 255.255.255.0
!
interface GigabitEthernet0/0/0.100
encapsulation dot1Q 1 native
ip address 192.168.100.1 255.255.255.0
!
interface GigabitEthernet0/0/0.172
encapsulation dot1Q 172
ip address 172.16.1.1 255.255.255.0
!
interface GigabitEthernet0/0/1
description A ISP Router
ip address dhcp
duplex auto
speed auto
ipv6 address FE80::3 link-local
ipv6 address 2001:DB8:ACAD:C::2/64
!
interface GigabitEthernet0/0/2
media-type sfp
no ip address
duplex auto
speed auto
!
interface Serial0/1/0
description BKP A Central
ip address 10.2.0.2 255.255.255.252
ipv6 address 2001:DB8:ACAD:B::2/64
clock rate 2000000
!
interface Serial0/1/1
no ip address
clock rate 2000000
shutdown
!
interface Vlan1
no ip address
shutdown
!
ip classless
ip route 0.0.0.0 0.0.0.0 GigabitEthernet0/0/1
ip route 0.0.0.0 0.0.0.0 Serial0/1/0 10
!
ip flow-export version 9
!
ipv6 route ::/0 2001:DB8:ACAD:C::1
ipv6 route ::/0 2001:DB8:ACAD:B::1 10
!
line con 0
!
line aux 0
!
line vty 0 4
login
!
end
Hola, alguno pudo bajar el archivo de packet tracer?
new one
Hello!
A little help here.
I couldn’t connect to the SSID-10 from the laptop. No errors, just nothing happens when choosing connect.
Show I check anything?
There are a few cases where the packet tracer has crashed, so please repeat/review step 6 and reconnect the laptop again.
I have followed your step 6 carefully but nothing happened. What’s wrong?
Please check/redo the previous steps again.
also deal with this issue , check the cap wap tunnel connectivity and verify the trunk interfaces between router , wlc , ap .
How do you do that?
Can you upload the newest version of The Skills Assessment?
Hi, I have new skill practice. How i can send us?
[part 2] HI can we know where it went wrong? thank you
ipv6 unicast-routing
HI can we know where it went wrong? thank you
recheck your wlan configuration
There some little details that need to be corrected… But overall is good enough
I’ve got 92.7%
But I did some changes on my own… I believe that following this page the score will be around 88%
Step 5: Configure an SNMP server.
The screenshot is pointing to “Communities”, but before you can use that, you have to first click on “Trap Receivers” on the left-side pane
You can see in the screenshot that the screen that you are on is: “SNMP Trap Receiver => New”
Regarding the SSID – the screenshot is a bit confusing. The SSID should be: SSID-10
Performing this lab as given here will give a score of 97/100 with 88.2 % percentile…
i make 69% :(
There’s a mistake at the very beginning of the configuration:
en
config t
vlan 10
name users
vlan 999
ununsed <<<<—– should be name unused
exit
Can i open this pka file with any packet tracer version or which version is required >???
Download packet tracer: https://itexamanswers.net/cisco-packet-tracer-latest-for-windows-linux-macos.html
missing a few things here
Hello Team,
Is there .pka file for the topology ?
thanks !
added file
are the answers available for SRWE Practice PT Skills Assessment (PTSA) – Part 2
Is there a way to configure it?