1. What is an example of a closed-loop control system?
- a manual garage door opener
- a clock
- a traditional dishwasher
- a thermostat
Explanation: Closed-loop control systems use feedback. A thermostat is constantly monitoring environmental temperature and uses the temperature to decide whether to activate a climate control system. The other options are examples of open-loop control systems.
2. True or False?
The purpose of the Cisco IoT System is to create complexity in IoT system implementation and management.
Explanation: The Cisco IoT System reduces the complexities of digitization for industry. IoT implementation and management are two components of the digitization process.
3. What are three components of a control system? (Choose three.)
- sensor
- plant
- thermostat
- wearable device
- controller
Explanation: The basic building blocks of a control system are sensors, controllers, and plants. Controllers monitor environmental conditions using sensors. In response to environmental conditions, the controller can communicate with a plant that can perform a variety of actions.
4. What are two advantages of using fiber optic cables compared with copper cables? (Choose two.)
- They are less expensive.
- They support higher bandwidth.
- They provide connections over longer distances.
- They use electromagnetic signals to transmit data.
- They provide shared media access for a single link.
Explanation: Data can travel longer distances on fiber optic cables, and the cables can support higher bandwidths than can copper cables. Using fiber optic cables, the sending device transmits the binary bits as light pulses using LEDs or lasers. The receiving device uses photodiodes to detect the light pulses and convert them to voltages. Fiber optic links are typical point-to-point links and they are more expensive than copper cables.
5. To answer the question, you do not need to consider the exhibit. Which type of media would use electromagnetic signals to communicate between IoT devices?

- wireless
- single-mode fiber
- copper
- multimode fiber
Explanation: Wireless media are commonly used to connect previously unconnected devices to a network. Wireless connectivity methods include the use of electromagnetic signals, radio and microwave frequencies, and satellite links.
6. Which level of the Internet of Things reference model describes data storage?
- data abstraction
- edge computing
- data accumulation
- physical devices and controllers
Explanation: The data accumulation level (Level 4) of the Internet of Things reference model describes data storage aspects of IoT.
7. What are two benefits of using a layered model for network protocol development? (Choose two.)
- promoting acquisition of networking products
- reducing competition among different manufacturers
- enhancing capabilities of networking products and services
- providing a common language to describe networking functions
- preventing technology changes in one layer from affecting other layers
Explanation: There are many benefits of using a layered model to explain network protocols and operations, including: (1) assisting in protocol design; (2) fostering competition because products from different vendors can work together; (3) preventing technology or capability changes in one layer from affecting other layers; and (4) providing a common language to describe networking functions and capabilities.
8. What are three machine-intelligible message structures that group strings of bits for network transmission? (Choose three.)
- ASCII codes
- frames
- pixels
- packets
- segments
- waveforms
Explanation: Long stings of bits must be transmitted in groups. These machine-intelligible message structures are frames, packets, and segments. ASCII codes are groups of bits that represent characters and text. Pixels are tiny parts of a larger image, and waveforms are depictions of various kinds of signals, including sounds.
9. What are two factors that impact network security in the IoT? (Choose two.)
- the number of devices
- the number of bits used for encryption
- the nontraditional location of devices
- the lack of Internet standards
- the amount of space between sensors
Explanation: Network security is a challenge in the IoT. Some of the factors that impact security are as follows:
- Number of devices
- Nontraditional location of devices, which makes physical security a challenge
- Type and quantity of gathered data
- Lack of device upgradability
10. What are three types of connections in an IoT system? (Choose three.)
- connection to power sources
- application protocols designed for IoT
- exclusive networking for IoT systems
- interconnection among cloud computing systems
- wires and circuitry associated with linking IoT components
- OSI Layer 2 and Layer 3 networking connections
Explanation: There are multiple meanings of the word “connection” when describing IoT systems, including (1) devices that must be connected to some source of power, such as batteries or AC/DC power; (2) the fact that all IoT devices have circuitry interconnecting sensors, actuators, and controllers together; and (3) that IoT devices have networking links at Layer 2 and Layer 3 of the OSI model.
The IoT does not need unique and exclusive network or application connections.
The IoT does not need unique and exclusive network or application connections.
11. Match the layers of the TCP/IP model to their function. (Not all options are used.)
- application
– represents data to the user and provides encoding and dialog control
- transport
– supports communication between various devices across diverse networks
- internet
– determines the best path through the networks to send data
- network access
– controls hardware devices and media that make up the network
12. Match the functions with the IoT device.
- adds intelligence to things
– controller
- monitors physical properties of the environment
– sensor
- improves IoT network performance
– none of these
- performs an action
– actuator
13. What type of IoT device is the Raspberry Pi?
- router
- sensor
- actuator
- controller
Explanation: The Raspberry Pi is a powerful controller. It can collect and process a large amount of data. It can also connect to the network to send information to network connected devices.
14. What is embedded within a digital object, such as a photograph or email?
- sensor
- microcontroller
- feedback
- metadata
Explanation: Metadata is data about data. A picture can contain GPS location and timestamp data embedded within it. An email can include a point of origin and all SMTP servers along the delivery pathway.
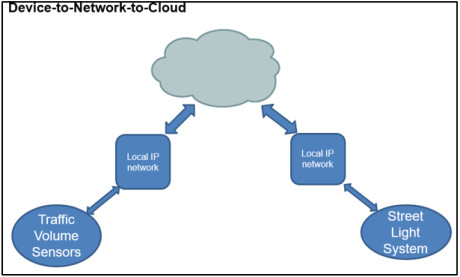
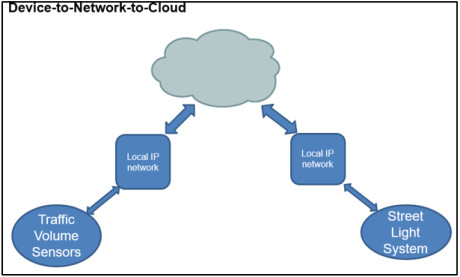
15. To answer the question, you do not need to consider the exhibit. Which type of IoT device operates in the device-to-network-to-cloud communication model?
- Bluetooth heart-rate sensor
- IP camera
- smart watch
- Zigbee gas sensor
Explanation: Some smart devices, such as watches or fitness trackers, are not IP-enabled and cannot connect directly to the fog or cloud. These devices use application software operating on a local gateway device as an intermediary between the device and the cloud service.
16. What is the term for the extension of the existing Internet structure to billions of connected devices?
- SCADA
- digitization
- IoT
- M2M
Explanation: The Internet of Things (IoT) refers to the interconnection of billions of things, or “smart dust.” SCADA refers to a type of IoT system applied to the industrial Internet. Digitization has several meanings. It can refer to the process of converting analog to digital, or it can refer to the process by which an organization modernizes by planning and ultimately building, a sophisticated and forward-thinking IT network ecosystem that will allow for greater connectivity, productivity, and security. Finally, M2M refers to communication from machine to machine.
17. What are three alternative methods of powering IoT systems deployed in remote locations? (Choose three.)
- solar
- PoE
- vibration
- temperature differences
- AC line power
Explanation: As IoT devices are deployed in areas without a direct connection to a power grid, alternative methods of powering them may be used. These alternative methods of providing power for IoT devices havest energy from the sun, temperatature difference, and vibration.
18. Which action is the result of negative feedback?
- A flashlight is used at night by a camper.
- A strong feedback noise is heard in an auditorium during a rehearsal.
- An unexpected chemical reaction in a chemical plant causes an explosion.
- A thermostat shuts down an air conditioning unit when the temperature reaches the set temperature.
Explanation: Negative feedback tends to move a system toward stabilization and equilibrium. A thermostat monitors and maintains room temperature in the summer by activating and deactivating an air conditioning unit. Chemical reactions that lead to explosions or unpleasant noises that are caused by audio signal feedback are examples of positive feedback. A flashlight used by a camper does not involve system feedback.
19. Fill in the blank.
In process control theory, a _____ uses inputs to execute the required actions in order to achieve the desired output.
Correct Answer:
process
or
controlled process
Explanation: A process uses inputs to execute the required actions to achieve the desired output. The output of a system is the status or state of a system. The input contains instructions for actions in order to achieve the desired output.


yes boss this was really helpful
thanks dude this help ed me an dthe person below
Very helpful!!! Thank You so much!