Module Group 5: Modules 17 – 20 Group Exam Answers
Networking Essentials (Version 2) – Modules 17 – 20: Introduction to Cisco Networking Group Exam Answers
1. An administrator defined a local user account with a secret password on router R1 for use with SSH. Which three additional steps are required to configure R1 to accept only encrypted SSH connections? (Choose three.)
- Generate the SSH keys.
- Configure DNS on the router.
- Generate two-way pre-shared keys.
- Enable inbound vty Telnet sessions.
- Enable inbound vty SSH sessions.
- Configure the IP domain name on the router.
2. A user experiences access and performance issues with the Internet connection from a home computer. The Internet connection is provided through a DSL line. The user calls the support line of the phone company for help. The support technician asks the user to connect the computer directly to the DSL modem. Which two pieces of information will help the technician to troubleshoot the problem? (Choose two.)
- the model and vendor of the computer
- when the problem started
- the IP address of the computer
- the MAC address of the Ethernet NIC on the computer
- the number of times that the ping command was issued
3. What advantage does SSH offer over Telnet?
- more connection lines
- connection-oriented services
- encryption
- username and password authentication
4. Match the configuration mode with the command that is available in that mode. (Not all options are used.)
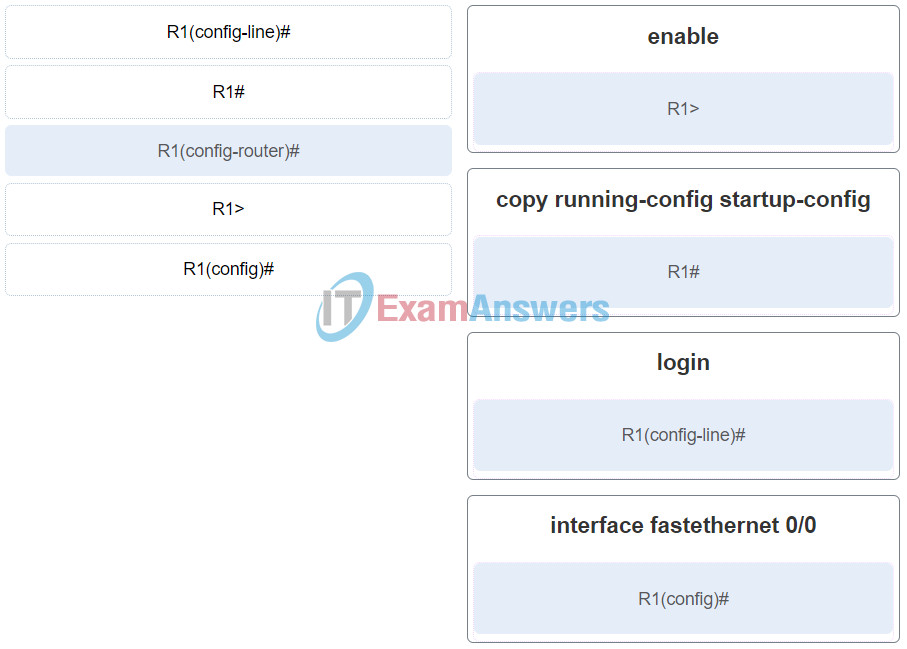
Networking Essentials (Version 2) – Modules 17 – 20: Introduction to Cisco Networking Group ExamQ4
5. What type of cable is used to connect a workstation serial port to a Cisco router console port?
- straight-through
- rollover
- coaxial
- crossover
6. What are two requirements when using out-of-band configuration of a Cisco IOS network device? (Choose two.)
- Telnet or SSH access to the device
- a direct connection to the console or AUX port
- HTTP access to the device
- a terminal emulation client
- a connection to an operational network interface on the device
7. When is an IP address required to be configured on a Cisco LAN switch?
- when the switch is connected to another switch
- when the switch must forward LAN traffic
- when the switch needs to be managed through an in-band connection
- when the switch is configured from a computer connected to the console port
8. When a router is powered on, where will the router first search for a valid IOS image to load by default?
- flash memory
- RAM
- ROM
- NVRAM
9. Following default settings, what two tasks are performed first in the router boot sequence? (Choose two.)
- Load the running-config file from RAM.
- Locate and load the operating system.
- Locate and load the startup-config file from NVRAM.
- Load the bootstrap program from ROM.
- Perform the POST routine.
10. A network administrator is working on a Cisco router. The CLI prompt is Router1(config-if)#. Which operation is the administrator likely to configure next?
- a LAN interface
- the password that is required to access the privileged EXEC mode
- the console port
- the vty lines
11. To save time, IOS commands may be partially entered and then completed by typing which key or key combination?
- Tab
- Up Arrow
- Ctrl-P
- Down Arrow
- Ctrl-N
- Right Arrow
12. A network administrator issues the Switch# show running-config command on a Cisco switch. Which term is used to describe the part ” running-config” in the command?
- command
- argument
- keyword
- hot key
13. Refer to the exhibit. Which element of IOS syntax is the expression MainOffice?
- an argument
- a subcommand
- a command
- a keyword
14. A network administrator is troubleshooting inter-connection issues between routers. Which show command can be used to check the bandwidth and MTU settings of an interface?
- show protocols
- show ip route
- show interfaces
- show arp
15. What is the purpose of assigning an IP address to the VLAN1 interface on a Cisco Layer 2 switch?
- to permit IP packets to be forwarded by the switch
- to create a new IP local network on the switch
- to enable remote access to the switch to manage it
- to enable the switch to route packets between networks
16. Match the type of password on a Cisco device to the function.
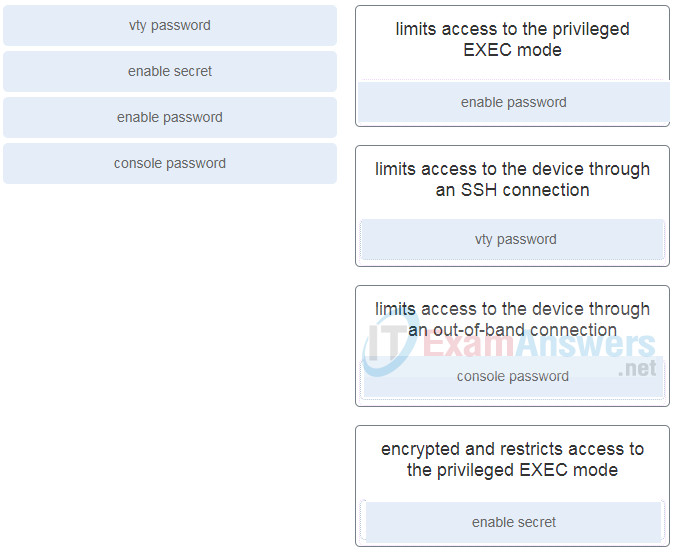
- enable password: limits access to the privileged EXEC mode
- vty password: limits access to the device through an SSH connection
- console password: limits access to the device through an out-of-band connection
- enable secret: encrypted and restricts access to the privileged EXEC mode
17. Which statement regarding the service password-encryption command is true?
- It is configured in privileged EXEC mode.
- To see the passwords encrypted by the service password-encryption command in plain text, issue the no service password-encryption command.
- As soon as the service password-encryption command is entered, all currently set passwords formerly displayed in plain text are encrypted.
- It encrypts only line mode passwords.
18. Passwords can be used to restrict access to all or parts of the Cisco IOS. Select the modes and interfaces that can be protected with passwords. (Choose three.)
- privileged EXEC mode
- boot IOS mode
- console interface
- VTY interface
- router configuration mode
- Ethernet interface
19. A user can print to a printer that is on the same network, but the traffic of the user cannot reach the Internet. What is a possible cause of the problem?
- The PC has an incorrect IP address.
- The network cable connected to the user PC is faulty.
- The NIC on the PC is faulty.
- The PC default gateway address is missing or incorrect.
20. For the second time in a week, workstations on a LAN are not able to log into a specific server. The technician fixed the problem the first time, but cannot remember the steps taken to solve it. What aspect of the troubleshooting process has the technician neglected?
- documenting the troubleshooting process
- identifying the problem
- asking questions of end users
- using structured techniques to solve a problem
21. Which utility can be used to view a list of open TCP connections on Linux or Windows systems?
- Ping
- Netstat
- Ipconfig
- Tracert
22. Which three pieces of information are revealed by the ipconfig command (without the /all switch)? (Choose three.)
- subnet mask
- MAC address
- default gateway
- IP address
- DHCP server
- DNS server
23. Which command can be used to verify connectivity between two host devices?
- nslookup
- ipconfig
- netstat
- ping
24. How does an activity LED on wireless routers indicate that traffic is moving through a port?
- by flashing
- by staying a solid amber color
- by staying a solid green color
- by staying turned off
