Enterprise Networking, Security, and Automation ( Version 7.00) – Modules 13 – 14: Emerging Network Technologies Exam
1. A company uses a cloud-based payroll system. Which cloud computing technology is this company using?
- browser as a service (BaaS)
- infrastructure as a service (IaaS)
- software as a service (SaaS)
- wireless as a service (WaaS)
2. For a data center, what is the difference in the server virtualization data traffic compared with the traditional client-server model?
- Data traffic from clients will be routed to multiple virtual servers.
- There are significant data exchanges between virtual servers.
- There is more data traffic flowing from virtual servers to clients.
- More network control traffic is generated between virtual servers and clients.
3. Which component in a traditional infrastructure device provides Layer 2 and Layer 3 functions to create data paths within a network?
- data plane
- control plane
- adjacency table
- forwarding information base
4. Which network traffic management technology is a basic element in SDN implementations?
- OpenFlow
- OpenStack
- IEEE 802.1aq
- Interface to the Routing System
5. Which type of hypervisor would most likely be used in a data center?
- Type 2
- Type 1
- Nexus
- Hadoop
6. Which is a characteristic of a Type 1 hypervisor?
- installed directly on a server
- best suited for consumers and not for an enterprise environment
- does not require management console software
- installed on an existing operating system
7. Which two layers of the OSI model are associated with SDN network control plane functions that make forwarding decisions? (Choose two.)
- Layer 1
- Layer 2
- Layer 3
- Layer 4
- Layer 5
8. What pre-populates the FIB on Cisco devices that use CEF to process packets?
- the routing table
- the adjacency table
- the ARP table
- the DSP
9. What is a function of the data plane of a network device?
- sending information to the CPU for processing
- building the routing table
- resolving MAC addresses
- forwarding traffic flows
10. Which statement describes the concept of cloud computing?
- separation of application from hardware
- separation of management plane from control plane
- separation of operating system from hardware
- separation of control plane from data plane
11. Which cloud model provides services for a specific organization or entity?
- a public cloud
- a hybrid cloud
- a private cloud
- a community cloud
12. What two benefits are gained when an organization adopts cloud computing and virtualization? (Choose two.)
- provides a “pay-as-you-go” model, allowing organizations to treat computing and storage expenses as a utility
- enables rapid responses to increasing data volume requirements
- distributed processing of large data sets in the size of terabytes
- elimination of vulnerabilities to cyber attacks
- increases the dependance on onsite IT resources
13. Which type of Hypervisor is implemented when a user with a laptop running the Mac OS installs a Windows virtual OS instance?
- type 2
- virtual machine
- type 1
- bare metal
14. A small company is considering moving many of its data center functions to the cloud. What are three advantages of this plan? (Choose three.)
- The company only needs to pay for the amount of processing and storage capacity that it uses.
- Cloud services are billed at a fixed fee no matter how much processing and storage are used by the company.
- The company does not need to be concerned about how to handle increasing data storage and processing demands with in-house data center equipment.
- The company can increase processing and storage capacity as needed and then decrease capacity when it is no longer needed.
- Single-tenant data centers can easily grow to accommodate increasing data storage requirements.
- Cloud services enable the company to own and administer its own servers and storage devices.
15. How does virtualization help with disaster recovery within a data center?
- support of live migration
- guarantee of power
- improvement of business practices
- supply of consistent air flow
16. What technology allows users to access data anywhere and at any time?
- Cloud computing
- virtualization
- micromarketing
- data analytics
17. Which action takes place in the assurance element of the IBN model?
- verification and corrective action
- configuring systems
- translation of policies
- integrity checks
18. Refer to the exhibit. Which data format is used to represent the data for network automation applications?
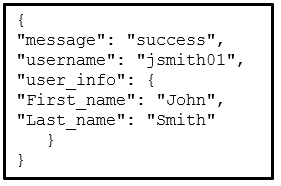
- XML
- YAML
- HTML
- JSON
19. What is the function of the key contained in most RESTful APIs?
- It is the top-level object of the API query.
- It is used to authenticate the requesting source.
- It represents the main query components in the API request.
- It is used in the encryption of the message by an API request.
20. Which two configuration management tools are developed using Ruby? (Choose two.)
- Puppet
- Ansible
- SaltStack
- Chef
- RESTCONF
21. Which term is used to describe a set of instructions for execution by the configuration management tool Puppet?
- Playbook
- Cookbook
- Manifest
- Pillar
22. Which term is used to describe a set of instructions for execution by the configuration management tool SaltStack?
- Cookbook
- Manifest
- Pillar
- Playbook
23. Which scenario describes the use of a public API?
- It requires a license.
- It can be used with no restrictions.
- It is used between a company and its business partners.
- It is used only within an organization.
24. What is YAML?
- It is a scripting language.
- It is a data format and superset of JSON.
- It is a compiled programming language.
- It is a web application.
25. Which RESTFul operation corresponds to the HTTP GET method?
- post
- patch
- update
- read
26. Which technology virtualizes the network control plane and moves it to a centralized controller?
- SDN
- fog computing
- cloud computing
- IaaS
27. What are two functions of hypervisors? (Choose two.)
- to partition the hard drive to run virtual machines
- to manage virtual machines
- to protect the host from malware infection from the virtual machines
- to share the antivirus software across the virtual machines
- to allocate physical system resources to virtual machines
28. What is a difference between the functions of Cloud computing and virtualization?
- Cloud computing requires hypervisor technology whereas virtualization is a fault tolerance technology.
- Cloud computing separates the application from the hardware whereas virtualization separates the OS from the underlying hardware.
- Cloud computing provides services on web-based access whereas virtualization provides services on data access through virtualized Internet connections.
- Cloud computing utilizes data center technology whereas virtualization is not used in data centers.
29. How is the YAML data format structure different from JSON?
- It uses indentations.
- It uses end tags.
- It uses hierarchical levels of nesting.
- It uses brackets and commas.
30. What is the most widely used API for web services?
- XML-RPC
- SOAP
- JSON-RPC
- REST
31. What is REST?
- It is a way to store and interchange data in a structured format.
- It is an architecture style for designing web service applications.
- It is a human readable data structure that is used by applications for storing, transforming, and reading data.
- It is a protocol that allows administrators to manage nodes on an IP network.
32. What is a difference between the XML and HTML data formats?
- XML does not use predefined tags whereas HTML does use predefined tags.
- XML encloses data within a pair of tags whereas HTML uses a pair of quotation makes to enclose data.
- XML formats data in binary whereas HTML formats data in plain text.
- XML does not require indentation for each key/value pair but HTML does require indentation.
33. To avoid purchasing new hardware, a company wants to take advantage of idle system resources and consolidate the number of servers while allowing for multiple operating systems on a single hardware platform. What service or technology would support this requirement?
- dedicated servers
- Cisco ACI
- virtualization
- software defined networking
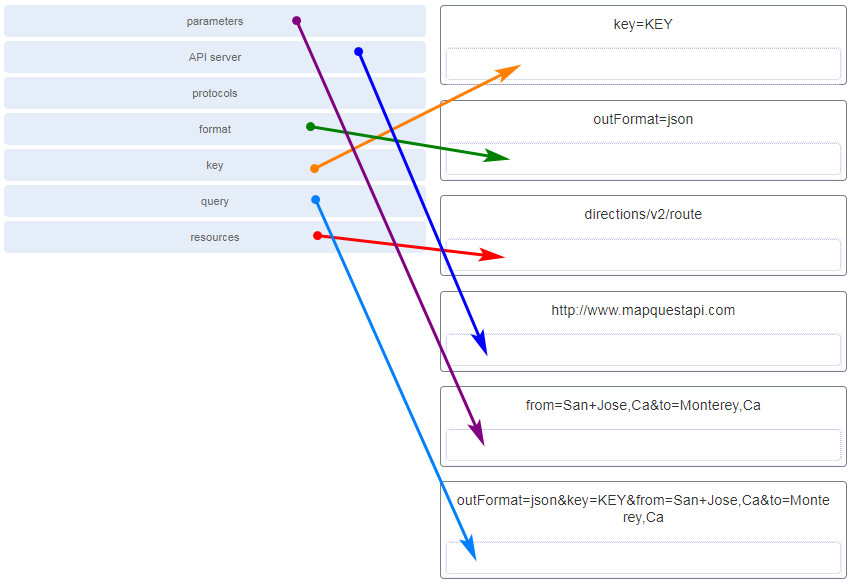
34. Match the term to the RESTful API request http://www.mapquestapi.com/directions/v2/route?outFormat=json&key=KEY&from=San+Jose,Ca&to=Monterey,Ca component. (Not all options are used.)
35. Which cloud computing opportunity would provide the use of network hardware such as routers and switches for a particular company?
- software as a service (SaaS)
- wireless as a service (WaaS)
- infrastructure as a service (IaaS)
- browser as a service (BaaS)
36. What component is considered the brains of the ACI architecture and translates application policies?
- the Application Network Profile endpoints
- the Nexus 9000 switch
- the hypervisor
- the Application Policy Infrastructure Controller
37. Which statement describes the concept of cloud computing?
- separation of management plane from control plane
- separation of control plane from data plane
- separation of application from hardware
- separation of operating system from hardware
38. In which situation would a partner API be appropriate?
- an internet search engine allowing developers to integrate the search engine into their own software applications
- company sales staff accessing internal sales data from their mobile devices
- someone creating an account on an external app or website by using his or her social media credentials
- a vacation service site interacting with hotel databases to display information from all the hotels on its web site
39. Because of enormous growth in web traffic, a company has planned to purchase additional servers to help handle the web traffic. What service or technology would support this requirement?
- virtualization
- data center
- cloud services
- dedicated servers
40. ABCTech is investigating the use of automation for some of its products. In order to control and test these products, the programmers require Windows, Linux, and MAC OS on their computers. What service or technology would support this requirement?
- dedicated servers
- software defined networking
- virtualization
- Cisco ACI
41. What are three components used in the query portion of a typical RESTful API request? (Choose three.)
- API server
- format
- parameters
- key
- protocol
- resources
42. A company has recently become multinational. Employees are working remotely, in different time zones, and they need access to company services from any place at any time. What service or technology would support this requirement?
- dedicated servers
- cloud services
- Cisco ACI
- virtualization
43. Following a multicontinent advertising campaign for a new product, a company finds its client database and volume of orders are overloading its on-site computer systems but the company does not have any room to expand. What service or technology would support this requirement?
- cloud services
- dedicated servers
- data center
- virtualization
44. A network administrator has been tasked with creating a disaster recovery plan. As part of this plan, the administrator is looking for a backup site for all of the data on the company servers. What service or technology would support this requirement?
- virtualization
- software defined networking
- data center
- dedicated servers
45. Which is a requirement of a site-to-site VPN?
- It requires hosts to use VPN client software to encapsulate traffic.
- It requires a VPN gateway at each end of the tunnel to encrypt and decrypt traffic.
- It requires the placement of a VPN server at the edge of the company network.
- It requires a client/server architecture.
46. Which statement describes an important characteristic of a site-to-site VPN?
- It must be statically set up.
- After the initial connection is established, it can dynamically change connection information.
- It requires using a VPN client on the host PC.
- It is commonly implemented over dialup and cable modem networks.
- It is ideally suited for use by mobile workers.
47. Which protocol is attacked when a cybercriminal provides an invalid gateway in order to create a man-in-the-middle attack?
- DHCP
- ICMP
- DNS
- HTTP or HTTPS
48. In which TCP attack is the cybercriminal attempting to overwhelm a target host with half-open TCP connections?
- reset attack
- session hijacking attack
- SYN flood attack
- port scan attack
49. Which statement describes a VPN?
- VPNs use logical connections to create public networks through the Internet.
- VPNs use open source virtualization software to create the tunnel through the Internet.
- VPNs use dedicated physical connections to transfer data between remote users.
- VPNs use virtual connections to create a private network through a public network.

Still valid 10/10/2023
Which is a requirement of a site-to-site VPN?
Which statement describes an important characteristic of a site-to-site VPN?
Which protocol is attacked when a cybercriminal provides an invalid gateway in order to create a man-in-the-middle attack?
In which TCP attack is the cybercriminal attempting to overwhelm a target host with half-open TCP connections?
Which statement describes a VPN?
Item 10 and 37 is duplicate
Which statement describes an important characteristic of a site-to-site VPN?
True answer: It must be statically set up
What technology allows users to access data anywhere and at any time?
Following a multicontinent advertising campaign for a new product, a company finds its client database and volume of orders are overloading its on-site computer systems but the company does not have any room to expand. What service or technology would support this requirement?
– cloud services <—-
– dedicated servers
– data center
– virtualization
A network administrator has been tasked with creating a disaster recovery plan. As part of this plan, the administrator is looking for a backup site for all of the data on the company servers. What service or technology would support this requirement?
Following a multicontinent advertising campaign for a new product, a company finds its client database and volume of orders are overloading its on-site computer systems but the company does not have any room to expand. What service or technology would support this requirement?
ABCTech is investigating the use of automation for some of its products. In order to control and test these products, the programmers require Windows, Linux, and MAC OS on their computers. What service or technology would support this requirement?
dedicated servers
data center
virtualization
software defined networking
A company has recently become multinational. Employees are working remotely, in different time zones, and they need access to company services from any place at any time. What service or technology would support this requirement?
dedicated servers
cloud services
Cisco ACI
virtualization
cloud services
What are three components used in the query portion of a typical RESTful API request? (Choose three.)
-API server
-format
-parameters
-key
-protocol
-resources
is there ENSA packet tracer answer?
ABCTech is investigating the use of automation for some of its products. In order to control and test these products, the programmers require Windows, Linux, and MAC OS on their computers. What service or technology would support this requirement?
dedicated servers
software defined networking
-> virtualization
Cisco ACI
How is the YAML data format structure different from JSON?
(X) It uses indentations.
It uses hierarchical levels of nesting.
It uses brackets and commas.
It uses end tags.
A company has recently become multinational. Employees are working remotely, in different time zones, and they need access to company services from any place at any time. What service or technology would support this requirement?
is this the final exam for the ccca 3 v7?
HI HOPE YOU ARE GOOD !!!! I’am kindly asking the final exam for the new ccna , enterprise networking,security, and automation