Check answers here:
Modules 10 – 13: L2 Security and WLANs Exam Answers
Quiz-summary
0 of 82 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
Information
CCNA 2 v7 Modules 10 – 13: L2 Security and WLANs Test Online
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 82 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- Answered
- Review
-
Question 1 of 82
1. Question
1 pointsWhich Layer 2 attack will result in legitimate users not getting valid IP addresses?Correct
Incorrect
-
Question 2 of 82
2. Question
1 pointsWhat mitigation plan is best for thwarting a DoS attack that is creating a MAC address table overflow?Correct
Incorrect
-
Question 3 of 82
3. Question
1 pointsWhich three Cisco products focus on endpoint security solutions? (Choose three.)Correct
Incorrect
-
Question 4 of 82
4. Question
1 pointsTrue or False? In the 802.1X standard, the client attempting to access the network is referred to as the supplicant.Correct
Incorrect
-
Question 5 of 82
5. Question
1 pointsWhich authentication method stores usernames and passwords in the router and is ideal for small networks?Correct
Incorrect
Hint
In a small network with a few network devices, AAA authentication can be implemented with the local database and with usernames and passwords stored on the network devices. Authentication using the TACACS+ or RADIUS protocol will require dedicated ACS servers although this authentication solution scales well in a large network. -
Question 6 of 82
6. Question
1 pointsWhat represents a best practice concerning discovery protocols such as CDP and LLDP on network devices?Correct
Incorrect
Hint
Both discovery protocols can provide hackers with sensitive network information. They should not be enabled on edge devices, and should be disabled globally or on a per-interface basis if not required. CDP is enabled by default. -
Question 7 of 82
7. Question
1 pointsWhich protocol should be used to mitigate the vulnerability of using Telnet to remotely manage network devices?Correct
Incorrect
Hint
Telnet uses plain text to communicate in a network. The username and password can be captured if the data transmission is intercepted. SSH encrypts data communications between two network devices. TFTP and SCP are used for file transfer over the network. SNMP is used in network management solutions. -
Question 8 of 82
8. Question
1 pointsWhich statement describes the behavior of a switch when the MAC address table is full?Correct
Incorrect
Hint
When the MAC address table is full, the switch treats the frame as an unknown unicast and begins to flood all incoming traffic to all ports only within the local VLAN. -
Question 9 of 82
9. Question
1 pointsWhat device is considered a supplicant during the 802.1X authentication process?Correct
Incorrect
Hint
The devices involved in the 802.1X authentication process are as follows:- The supplicant, which is the client that is requesting network access
- The authenticator, which is the switch that the client is connecting to and that is actually controlling physical network access
- The authentication server, which performs the actual authentication
-
Question 10 of 82
10. Question
1 pointsRefer to the exhibit. Port Fa0/2 has already been configured appropriately. The IP phone and PC work properly. Which switch configuration would be most appropriate for port Fa0/2 if the network administrator has the following goals?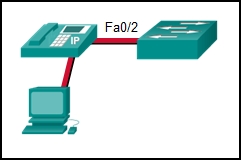 No one is allowed to disconnect the IP phone or the PC and connect some other wired device.
If a different device is connected, port Fa0/2 is shut down.
The switch should automatically detect the MAC address of the IP phone and the PC and add those addresses to the running configuration. Correct
No one is allowed to disconnect the IP phone or the PC and connect some other wired device.
If a different device is connected, port Fa0/2 is shut down.
The switch should automatically detect the MAC address of the IP phone and the PC and add those addresses to the running configuration. Correct
Incorrect
-
Question 11 of 82
11. Question
1 pointsRefer to the exhibit. Port security has been configured on the Fa 0/12 interface of switch S1. What action will occur when PC1 is attached to switch S1 with the applied configuration?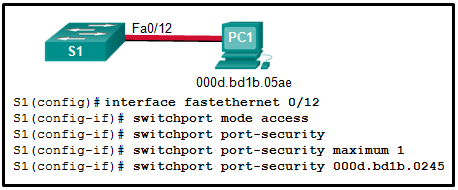 Correct
Correct
Incorrect
Hint
Manual configuration of the single allowed MAC address has been entered for port fa0/12. PC1 has a different MAC address and when attached will cause the port to shut down (the default action), a log message to be automatically created, and the violation counter to increment. The default action of shutdown is recommended because the restrict option might fail if an attack is underway. -
Question 12 of 82
12. Question
1 pointsWhich type of VLAN-hopping attack may be prevented by designating an unused VLAN as the native VLAN?Correct
Incorrect
Hint
Spoofing DTP messages forces a switch into trunking mode as part of a VLAN-hopping attack, but VLAN double tagging works even if trunk ports are disabled. Changing the native VLAN from the default to an unused VLAN reduces the possibility of this type of attack. DHCP spoofing and DHCP starvation exploit vulnerabilities in the DHCP message exchange. -
Question 13 of 82
13. Question
1 pointsA network administrator is configuring DAI on a switch with the command ip arp inspection validate src-mac. What is the purpose of this configuration command?Correct
Incorrect
Hint
DAI can be configured to check for both destination or source MAC and IP addresses:- Destination MAC – Checks the destination MAC address in the Ethernet header against the target MAC address in the ARP body.
- Source MAC – Checks the source MAC address in the Ethernet header against the sender MAC address in the ARP body.
- IP address – Checks the ARP body for invalid and unexpected IP addresses including addresses 0.0.0.0, 255.255.255.255, and all IP multicast addresses.
-
Question 14 of 82
14. Question
1 pointsWhich two commands can be used to enable BPDU guard on a switch? (Choose two.)Correct
Incorrect
Hint
BPDU guard can be enabled on all PortFast-enabled ports by using the spanning-tree portfast bpduguard default global configuration command. Alternatively, BPDU guard can be enabled on a PortFast-enabled port through the use of the spanning-tree bpduguard enable interface configuration command. -
Question 15 of 82
15. Question
1 pointsAs part of the new security policy, all switches on the network are configured to automatically learn MAC addresses for each port. All running configurations are saved at the start and close of every business day. A severe thunderstorm causes an extended power outage several hours after the close of business. When the switches are brought back online, the dynamically learned MAC addresses are retained. Which port security configuration enabled this?Correct
Incorrect
Hint
With sticky secure MAC addressing, the MAC addresses can be either dynamically learned or manually configured and then stored in the address table and added to the running configuration file. In contrast, dynamic secure MAC addressing provides for dynamically learned MAC addressing that is stored only in the address table. -
Question 16 of 82
16. Question
1 pointsWhich type of management frame may regularly be broadcast by an AP?Correct
Incorrect
Hint
Beacons are the only management frame that may regularly be broadcast by an AP. Probing, authentication, and association frames are used only during the association (or reassociation) process. -
Question 17 of 82
17. Question
1 pointsWhat are the two methods that are used by a wireless NIC to discover an AP? (Choose two.)Correct
Incorrect
Hint
Two methods can be used by a wireless device to discover and register with an access point: passive mode and active mode. In passive mode, the AP sends a broadcast beacon frame that contains the SSID and other wireless settings. In active mode, the wireless device must be manually configured for the SSID, and then the device broadcasts a probe request. -
Question 18 of 82
18. Question
1 pointsA technician is configuring the channel on a wireless router to either 1, 6, or 11. What is the purpose of adjusting the channel?Correct
Incorrect
Hint
Channels 1, 6, and 11 are selected because they are 5 channels apart. thus minimizing the interference with adjacent channels. A channel frequency can interfere with channels on either side of the main frequency. All wireless devices need to be used on nonadjacent channels. -
Question 19 of 82
19. Question
1 pointsWhile attending a conference, participants are using laptops for network connectivity. When a guest speaker attempts to connect to the network, the laptop fails to display any available wireless networks. The access point must be operating in which mode?Correct
Incorrect
Hint
Active is a mode used to configure an access point so that clients must know the SSID to connect to the access point. APs and wireless routers can operate in a mixed mode meaning that that multiple wireless standards are supported. Open is an authentication mode for an access point that has no impact on the listing of available wireless networks for a client. When an access point is configured in passive mode, the SSID is broadcast so that the name of wireless network will appear in the listing of available networks for clients. -
Question 20 of 82
20. Question
1 pointsA network administrator is required to upgrade wireless access to end users in a building. To provide data rates up to 1.3 Gb/s and still be backward compatible with older devices, which wireless standard should be implemented?Correct
Incorrect
Hint
802.11ac provides data rates up to 1.3 Gb/s and is still backward compatible with 802.11a/b/g/n devices. 802.11g and 802.11n are older standards that cannot reach speeds over 1Gb/s. 802.11ad is a newer standard that can offer theoretical speeds of up to 7 Gb/s. -
Question 21 of 82
21. Question
1 pointsA technician is about to install and configure a wireless network at a small branch office. What is the first security measure the technician should apply immediately upon powering up the wireless router?Correct
Incorrect
Hint
The first action a technician should do to secure a new wireless network is to change the default user-name and password of the wireless router. The next action would usually be to configure encryption. Then once the initial group of wireless hosts have connected to the network, MAC address filtering would be enabled and SSID broadcast disabled. This will prevent new unauthorized hosts from finding and connecting to the wireless network. -
Question 22 of 82
22. Question
1 pointsOn a Cisco 3504 WLC dashboard, which option provides access to the full menu of features?Correct
Incorrect
Hint
The Cisco 3504 WLC dashboard displays when a user logs into the WLC. It provides some basic settings and menus that users can quickly access to implement a variety of common configurations. By clicking the Advanced button, the user will access the advanced Summary page and access all the features of the WLC. -
Question 23 of 82
23. Question
1 pointsWhich step is required before creating a new WLAN on a Cisco 3500 series WLC?Correct
Incorrect
Hint
Each new WLAN configured on a Cisco 3500 series WLC needs its own VLAN interface. Thus it is required that a new VLAN interface to be created first before a new WLAN can be created. -
Question 24 of 82
24. Question
1 pointsA network engineer is troubleshooting a newly deployed wireless network that is using the latest 802.11 standards. When users access high bandwidth services such as streaming video, the wireless network performance is poor. To improve performance the network engineer decides to configure a 5 Ghz frequency band SSID and train users to use that SSID for streaming media services. Why might this solution improve the wireless network performance for that type of service?Correct
Incorrect
Hint
Wireless range is determined by the access point antenna and output power, not the frequency band that is used. In this scenario it is stated that all users have wireless NICs that comply with the latest standard, and so all can access the 5 GHz band. Although some users may find it inconvenient to switch to the 5 Ghz band to access streaming services, it is the greater number of channels, not just fewer users, that will improve network performance. -
Question 25 of 82
25. Question
1 pointsA network administrator is configuring a RADIUS server connection on a Cisco 3500 series WLC. The configuration requires a shared secret password. What is the purpose for the shared secret password?Correct
Incorrect
Hint
The RADIUS protocol uses security features to protect communications between the RADIUS server and clients. A shared secret is the password used between the WLC and the RADIUS server. It is not for end users. -
Question 26 of 82
26. Question
1 pointsWhich three parameters would need to be changed if best practices are being implemented for a home wireless AP? (Choose three.)Correct
Incorrect
Hint
As soon as an AP is taken out of a box, the default device password, SSID, and security parameters (wireless network password) should be set. The frequency of a wireless antenna can be adjusted, but doing so is not required. The beacon time is not normally configured. The wireless client operating system password is not affected by the configuration of a home wireless network. -
Question 27 of 82
27. Question
1 pointsWhich access control component, implementation, or protocol is based upon usernames and passwords?Correct
Incorrect
-
Question 28 of 82
28. Question
1 pointsWhich type of wireless network is based on the 802.11 standard and a 2.4-GHz or 5-GHz radio frequency?Correct
Incorrect
-
Question 29 of 82
29. Question
1 pointsWhich two Cisco solutions help prevent DHCP starvation attacks? (Choose two.)Correct
Incorrect
Hint
Cisco provides solutions to help mitigate Layer 2 attacks including these:- IP Source Guard (IPSG) – prevents MAC and IP address spoofing attacks
- Dynamic ARP Inspection (DAI) – prevents ARP spoofing and ARP poisoning attacks
- DHCP Snooping – prevents DHCP starvation and SHCP spoofing attacks
- Port Security – prevents many types of attacks including MAC table overflow attacks and DHCP starvation attacks
-
Question 30 of 82
30. Question
1 pointsWhat are three techniques for mitigating VLAN attacks? (Choose three.)Correct
Incorrect
Hint
Mitigating a VLAN attack can be done by disabling Dynamic Trunking Protocol (DTP), manually setting ports to trunking mode, and by setting the native VLAN of trunk links to VLANs not in use. -
Question 31 of 82
31. Question
1 pointsRefer to the exhibit. What can be determined about port security from the information that is shown?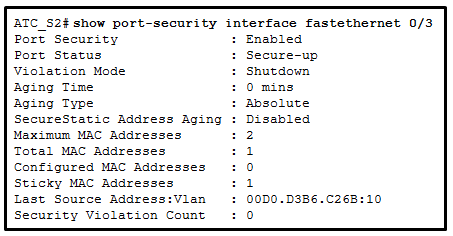 Correct
Correct
Incorrect
Hint
The Port Security line simply shows a state of Enabled if the switchport port-security command (with no options) has been entered for a particular switch port. If a port security violation had occurred, a different error message appears such as Secure-shutdown. The maximum number of MAC addresses supported is 50. The Maximum MAC Addresses line is used to show how many MAC addresses can be learned (2 in this case). The Sticky MAC Addresses line shows that only one device has been attached and learned automatically by the switch. This configuration could be used when a port is shared by two cubicle-sharing personnel who bring in separate laptops. -
Question 32 of 82
32. Question
1 pointsA network administrator of a college is configuring the WLAN user authentication process. Wireless users are required to enter username and password credentials that will be verified by a server. Which server would provide such service?Correct
Incorrect
Hint
Remote Authentication Dial-In User Service (RADIUS) is a protocol and server software that provides user-based authentication for an organization. When a WLAN is configured to use a RADIUS server, users will enter username and password credentials that are verified by the RADIUS server before allowing to the WLAN. -
Question 33 of 82
33. Question
1 pointsA technician is troubleshooting a slow WLAN that consists of 802.11b and 802.11g devices . A new 802.11n/ac dual-band router has been deployed on the network to replace the old 802.11g router. What can the technician do to address the slow wireless speed?Correct
Incorrect
Hint
Splitting the wireless traffic between the 802.11n 2.4 GHz band and the 5 GHz band will allow for the 802.11n to use the two bands as two separate wireless networks to help manage the traffic, thus improving wireless performance. -
Question 34 of 82
34. Question
1 pointsThe company handbook states that employees cannot have microwave ovens in their offices. Instead, all employees must use the microwave ovens located in the employee cafeteria. What wireless security risk is the company trying to avoid?Correct
Incorrect
Hint
Denial of service attacks can be the result of improperly configured devices which can disable the WLAN. Accidental interference from devices such as microwave ovens and cordless phones can impact both the security and performance of a WLAN. Man-in-the-middle attacks can allow an attacker to intercept data. Rogue access points can allow unauthorized users to access the wireless network. -
Question 35 of 82
35. Question
1 pointsWhat is the function provided by CAPWAP protocol in a corporate wireless network?Correct
Incorrect
Hint
CAPWAP is an IEEE standard protocol that enables a WLC to manage multiple APs and WLANs. CAPWAP is also responsible for the encapsulation and forwarding of WLAN client traffic between an AP and a WLC. -
Question 36 of 82
36. Question
1 pointsOpen the PT Activity. Perform the tasks in the activity instructions and then answer the question.Which event will take place if there is a port security violation on switch S1 interface Fa0/1?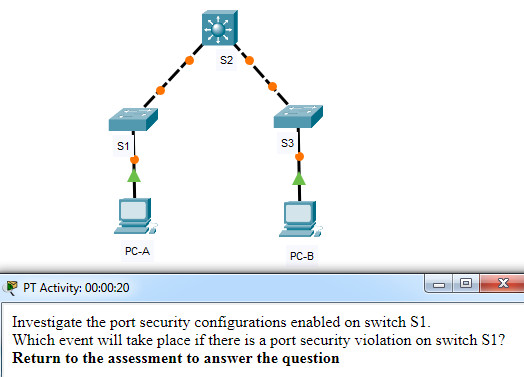
Modules 10 – 13: L2 Security and WLANs Exam Answers
Correct
Incorrect
Hint
The violation mode can be viewed by issuing the show port-security interface <int>command. Interface FastEthernet 0/1 is configured with the violation mode of protect. If there is a violation, interface FastEthernet 0/1 will drop packets with unknown MAC addresses. -
Question 37 of 82
37. Question
1 pointsMatch each functional component of AAA with its description. (Not all options are used.)Sort elements
- proves that users are who they say they are
- determines what resources users can access or the operations they are allowed to perform
- records what users do and what they access
- calculates how much a user must pay for remote access to a device
-
authentication
-
authorization
-
accounting
Correct
Incorrect
-
Question 38 of 82
38. Question
1 pointsWhat are two protocols that are used by AAA to authenticate users against a central database of usernames and password? (Choose two.)Correct
Incorrect
Hint
By using TACACS+ or RADIUS, AAA can authenticate users from a database of usernames and passwords stored centrally on a server such as a Cisco ACS server. -
Question 39 of 82
39. Question
1 pointsWhat is the result of a DHCP starvation attack?Correct
Incorrect
Hint
DCHP starvation attacks are launched by an attacker with the intent to create a DoS for DHCP clients. To accomplish this goal, the attacker uses a tool that sends many DHCPDISCOVER messages to lease the entire pool of available IP addresses, thus denying them to legitimate hosts. -
Question 40 of 82
40. Question
1 pointsWhich feature or configuration on a switch makes it vulnerable to VLAN double-tagging attacks?Correct
Incorrect
Hint
A double-tagging (or double-encapsulated) VLAN hopping attack takes advantage of the way that hardware on most switches operates. Most switches perform only one level of 802.1Q de-encapsulation, which allows an attacker to embed a hidden 802.1Q tag inside the frame. This tag allows the frame to be forwarded to a VLAN that the original 802.1Q tag did not specify. An important characteristic of the double-encapsulated VLAN hopping attack is that it works even if trunk ports are disabled, because a host typically sends a frame on a segment that is not a trunk link. This type of attack is unidirectional and works only when the attacker is connected to a port residing in the same VLAN as the native VLAN of the trunk port. -
Question 41 of 82
41. Question
1 pointsWhich component of AAA allows an administrator to track individuals who access network resources and any changes that are made to those resources?Correct
Incorrect
Hint
One of the components in AAA is accounting. After a user is authenticated through AAA, AAA servers keep a detailed log of exactly what actions the authenticated user takes on the device. -
Question 42 of 82
42. Question
1 pointsRefer to the exhibit. PC1 and PC2 should be able to obtain IP address assignments from the DHCP server. How many ports among switches should be assigned as trusted ports as part of the DHCP snooping configuration?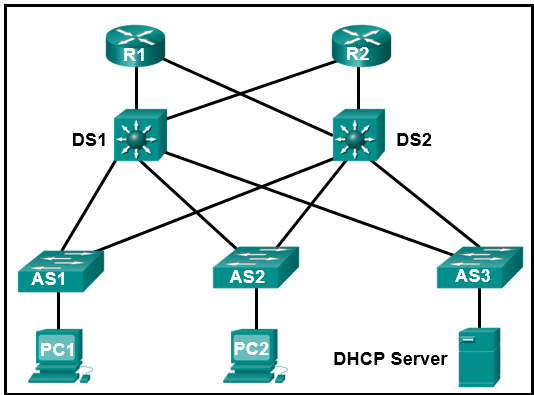 Correct
Correct
Incorrect
Hint
The DHCP snooping configuration includes building the DHCP Snooping Binding Database and assigning necessary trusted ports on switches. A trusted port points to the legitimate DHCP servers. In this network design, because the DHCP server is attached to AS3, seven switch ports should be assigned as trusted ports, one on AS3 toward the DHCP server, one on DS1 toward AS3, one on DS2 toward AS3, and two connections on both AS1 and AS2 (toward DS1 and DS2), for a total of seven. -
Question 43 of 82
43. Question
1 pointsAn IT security specialist enables port security on a switch port of a Cisco switch. What is the default violation mode in use until the switch port is configured to use a different violation mode?Correct
Incorrect
Hint
If no violation mode is specified when port security is enabled on a switch port, then the security violation mode defaults to shutdown. -
Question 44 of 82
44. Question
1 pointsA laptop cannot connect to a wireless access point. Which two troubleshooting steps should be taken first? (Choose two.)Correct
Incorrect
-
Question 45 of 82
45. Question
1 pointsWhat is an advantage of SSID cloaking?Correct
Incorrect
Hint
SSID cloaking is a weak security feature that is performed by APs and some wireless routers by allowing the SSID beacon frame to be disabled. Although clients have to manually identify the SSID to be connected to the network, the SSID can be easily discovered. The best way to secure a wireless network is to use authentication and encryption systems. SSID cloaking does not provide free Internet access in public locations, but an open system authentication could be used in that situation. -
Question 46 of 82
46. Question
1 pointsWhat is a wireless security mode that requires a RADIUS server to authenticate wireless users? personalCorrect
Incorrect
Hint
WPA and WPA2 come in two types: personal and enterprise. Personal is used in home and small office networks. Shared key allows three different authentication techniques: (1) WEP, (2) WPA, and (3) 802.11i/WPA2. WEP is an encryption method. -
Question 47 of 82
47. Question
1 pointsA company has recently implemented an 802.11n wireless network. Some users are complaining that the wireless network is too slow. Which solution is the best method to enhance the performance of the wireless network?Correct
Incorrect
Hint
Because some users are complaining about the network being too slow, the correct option would be to split the traffic so that there are two networks using different frequencies at the same time. Replacing the wireless NICs will not necessarily correct the network being slow and it could be expensive for the company. DHCP versus static addressing should have no impact of the network being slow and it would be a huge task to have all users assigned static addressing for their wireless connection. Upgrading the firmware on the wireless access point is always a good idea. However, if some of the users are experiencing a slow network connection, it is likely that this would not substantially improve network performance. -
Question 48 of 82
48. Question
1 pointsWhich protocol can be used to monitor the network?Correct
Incorrect
Hint
Simple Network Management Protocol (SNMP) is used to monitor the network. -
Question 49 of 82
49. Question
1 pointsA network administrator deploys a wireless router in a small law firm. Employee laptops join the WLAN and receive IP addresses in the 10.0.10.0/24 network. Which service is used on the wireless router to allow the employee laptops to access the internet?Correct
Incorrect
Hint
Any address with the 10 in the first octet is a private IPv4 address and cannot be routed on the internet. The wireless router will use a service called Network Address Translation (NAT) to convert private IPv4 addresses to internet-routable IPv4 addresses for wireless devices to gain access to the internet. -
Question 50 of 82
50. Question
1 pointsWhich service can be used on a wireless router to prioritize network traffic among different types of applications so that voice and video data are prioritized over email and web data?Correct
Incorrect
Hint
Many wireless routers have an option for configuring quality of service (QoS). By configuring QoS, certain time-sensitive traffic types, such as voice and video, are prioritized over traffic that is not as time-sensitive, such as email and web browsing. -
Question 51 of 82
51. Question
1 pointsWhich access control component, implementation, or protocol is based on device roles of supplicant, authenticator, and authentication server?Correct
Incorrect
-
Question 52 of 82
52. Question
1 pointsWhich type of wireless network is suitable for national and global communications?Correct
Incorrect
-
Question 53 of 82
53. Question
1 pointsWhich feature on a switch makes it vulnerable to VLAN hopping attacks?Correct
Incorrect
Hint
A VLAN hopping attack enables traffic from one VLAN to be seen by another VLAN without routing. In a basic VLAN hopping attack, the attacker takes advantage of the automatic trunking port feature enabled by default on most switch ports. -
Question 54 of 82
54. Question
1 pointsWhich component of AAA is used to determine which resources a user can access and which operations the user is allowed to perform?Correct
Incorrect
Hint
One of the components in AAA is authorization. After a user is authenticated through AAA, authorization services determine which resources the user can access and which operations the user is allowed to perform. -
Question 55 of 82
55. Question
1 pointsRefer to the exhibit. The Fa0/2 interface on switch S1 has been configured with the switchport port-security mac-address 0023.189d.6456 command and a workstation has been connected. What could be the reason that the Fa0/2 interface is shutdown?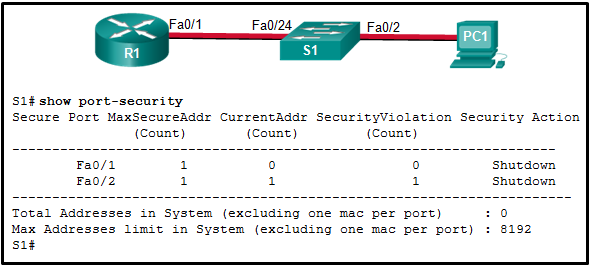 Correct
Correct
Incorrect
Hint
The security violation counter for Fa0/2 has been incremented (evidenced by the 1 in the SecurityViolation column). The most secure addresses allowed on port Fa0/2 is 1 and that address was manually entered. Therefore, PC1 must have a different MAC address than the one configured for port Fa0/2. Connections between end devices and the switch, as well as connections between a router and a switch, are made with a straight-through cable. -
Question 56 of 82
56. Question
1 pointsA network administrator enters the following commands on the switch SW1.SW1(config)# interface range fa0/5 - 10 SW1(config-if)# ip dhcp snooping limit rate 6
What is the effect after these commands are entered?Correct
Incorrect
Hint
When DHCP snooping is being configured, the number of DHCP discovery messages that untrusted ports can receive per second should be rate-limited by using the ip dhcp snooping limit rate interface configuration command. When a port receives more messages than the rate allows, the extra messages will be dropped. -
Question 57 of 82
57. Question
1 pointsA network administrator is configuring port security on a Cisco switch. The company security policy specifies that when a violation occurs, packets with unknown source addresses should be dropped and no notification should be sent. Which violation mode should be configured on the interfaces?Correct
Incorrect
Hint
On a Cisco switch, an interface can be configured for one of three violation modes, specifying the action to be taken if a violation occurs:Protect – Packets with unknown source addresses are dropped until a sufficient number of secure MAC addresses are removed, or the number of maximum allowable addresses is increased. There is no notification that a security violation has occurred. Restrict – Packets with unknown source addresses are dropped until a sufficient number of secure MAC addresses are removed, or the number of maximum allowable addresses is increased. In this mode, there is a notification that a security violation has occurred. Shutdown – The interface immediately becomes error-disabled and the port LED is turned off. -
Question 58 of 82
58. Question
1 pointsA network administrator is working to improve WLAN performance on a dual-band wireless router. What is a simple way to achieve a split-the-traffic result?Correct
Incorrect
Hint
By default, dual-band routers and APs use the same network name on both the 2.4 GHz band and the 5 GHz band. The simplest way to segment traffic is to rename one of the wireless networks. -
Question 59 of 82
59. Question
1 pointsWhich access control component, implementation, or protocol controls what users can do on the network?Correct
Incorrect
-
Question 60 of 82
60. Question
1 pointsWhich type of wireless network is suitable for providing wireless access to a city or district?Correct
Incorrect
-
Question 61 of 82
61. Question
1 pointsOn a Cisco 3504 WLC Summary page ( Advanced > Summary ), which tab allows a network administrator to access and configure a WLAN for a specific security option such as WPA2?Correct
Incorrect
-
Question 62 of 82
62. Question
1 pointsWhat type of wireless antenna is best suited for providing coverage in large open spaces, such as hallways or large conference rooms?Correct
Incorrect
-
Question 63 of 82
63. Question
1 pointsWhat two IEEE 802.11 wireless standards operate only in the 5 GHz range? (Choose two.)Correct
Incorrect
-
Question 64 of 82
64. Question
1 pointsWhat security benefit is gained from enabling BPDU guard on PortFast enabled interfaces?Correct
Incorrect
Hint
BPDU guard immediately error-disables a port that receives a BPDU. This prevents rogue switches from being added to the network. BPDU guard should only be applied to all end-user ports. -
Question 65 of 82
65. Question
1 pointsWhich access control component, implementation, or protocol logs EXEC and configuration commands configured by a user?Correct
Incorrect
-
Question 66 of 82
66. Question
1 pointsWhich type of wireless network uses transmitters to provide coverage over an extensive geographic area?Correct
Incorrect
-
Question 67 of 82
67. Question
1 pointsWhich access control component, implementation, or protocol controls who is permitted to access a network?Correct
Incorrect
-
Question 68 of 82
68. Question
1 pointsWhat two IEEE 802.11 wireless standards operate only in the 5 GHz range? (Choose two.)Correct
Incorrect
-
Question 69 of 82
69. Question
1 pointsWhich type of wireless network uses low powered transmitters for a short-range network, usually 20 to 30 ft. (6 to 9 meters)?Correct
Incorrect
-
Question 70 of 82
70. Question
1 pointsWhich wireless network topology would be used by network engineers to provide a wireless network for an entire college building?Correct
Incorrect
-
Question 71 of 82
71. Question
1 pointsWhich type of wireless network uses transmitters to provide wireless service over a large urban region?Correct
Incorrect
-
Question 72 of 82
72. Question
1 pointsWhich type of wireless network is suitable for use in a home or office?Correct
Incorrect
-
Question 73 of 82
73. Question
1 pointsWhich access control component, implementation, or protocol indicates success or failure of a client-requested service with a PASS or FAIL message?Correct
Incorrect
-
Question 74 of 82
74. Question
1 pointsWhich type of wireless network often makes use of devices mounted on buildings?Correct
Incorrect
-
Question 75 of 82
75. Question
1 pointsA network administrator is configuring DAI on a switch with the command ip arp inspection validate src-mac. What is the purpose of this configuration command?Correct
Incorrect
-
Question 76 of 82
76. Question
1 pointsWhich access control component, implementation, or protocol collects and reports usage data?Correct
Incorrect
-
Question 77 of 82
77. Question
1 pointsWhich type of wireless network uses transmitters to cover a medium-sized network, usually up to 300 feet (91.4 meters)?Correct
Incorrect
-
Question 78 of 82
78. Question
1 pointsWhich access control component, implementation, or protocol audits what users actions are performed on the network?Correct
Incorrect
-
Question 79 of 82
79. Question
1 pointsWhich type of wireless network commonly uses Bluetooth or ZigBee devices?Correct
Incorrect
-
Question 80 of 82
80. Question
1 pointsWhich access control component, implementation, or protocol is implemented either locally or as a server-based solution?Correct
Incorrect
-
Question 81 of 82
81. Question
1 pointsA technician is troubleshooting a slow WLAN and decides to use the split-the-traffic approach. Which two parameters would have to be configured to do this? (Choose two.)Correct
Incorrect
-
Question 82 of 82
82. Question
1 pointsWhich access control component, implementation, or protocol restricts LAN access through publicly accessible switch ports?Correct
Incorrect

Did the test, there was a new question I didnt see here:
Which wireless network topology would be used by network engineers to provide a wireless netowrk for an entire college building?
infastructure (answer)
ad hoc
mixed mode
hotspot
i think wuestion 65, 67 and 68 have wrong answers recorded. same qustions above have diferent answer recorded …..please
Fixed, thanks for report!