1. Which three options correctly associate a layer of the hierarchical design model with its function? (Choose three.)
- Core — interface for end devices
- Distribution — traffic control and security policies
- Access — interface for end devices
- Distribution — high-speed backbone
- Core — high-speed backbone
- Access — implementation of security policies
2. With respect to network design, what is convergence?
- implementation of standard equipment sets for LAN design
- implementation of a core-distribution-access design model for all sites in an enterprise
- a point in the network where all traffic “converges” before transmission to the destination, normally the core switch
- combining conventional data with voice and video on a common network
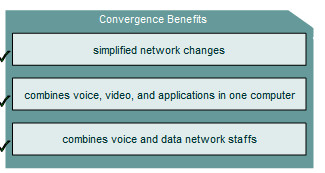
3. Drag the potential benefits of a converged network on the left to the right column.
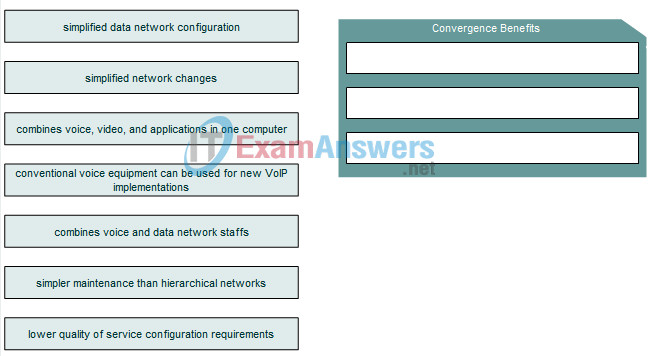
Answer
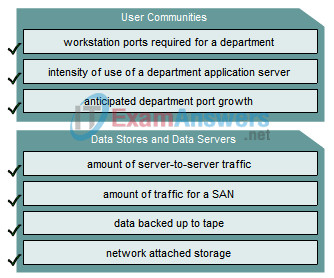
4. Drag the analysis actions on the left to the correct analysis type in the right column.
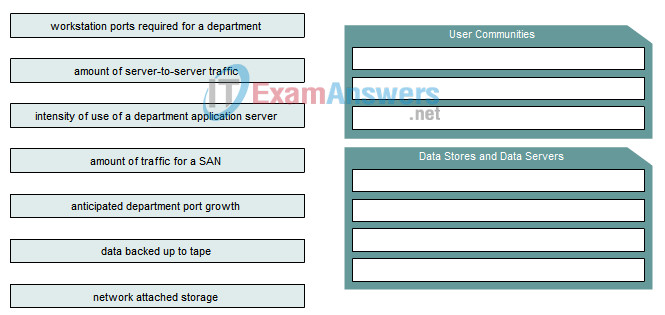
Answer
5. What factor may complicate user communities analysis?
- application changes may radically affect predicted data growth
- server to server traffic may skew user port usage data
- application usage is not always bound by department, or physical location
- different organization applications may share data stores
6. Drag the term on the left to the associated definition on the right.
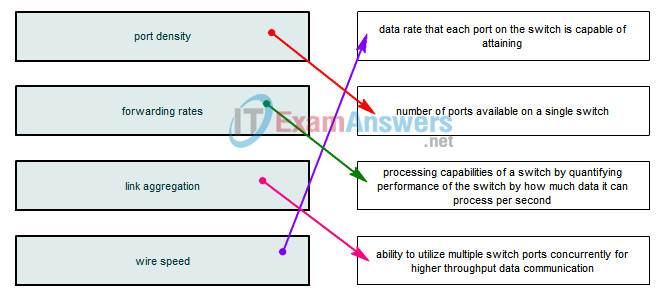
7. What would be the port capacity of a single port on a 48-port Gigabit Ethernet switch?
- 48 Gbps
- 10 Mbps
- 1000 Mbps
- 100 Mbps
8. A switch that uses MAC addresses to forward frames operates at which layer of the OSI model?
- Layer 1
- Layer 2
- Layer 3
- Layer 4
9. What is a feature offered by all stackable switches?
- predetermined number of ports
- fully redundant backplane
- support for Gigabit connectivity
- low bandwidth for inter-switch communications
- PoE capability
10. What function is performed by a Cisco access level switch?
- inter-VLAN support
- routing
- providing PoE
- link aggregation
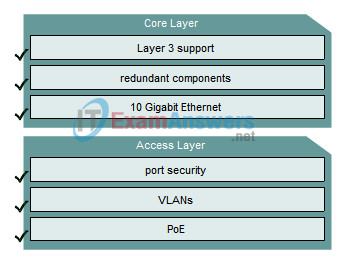
11. Drag the features listed on the left to the Cisco layer to which they are associated.
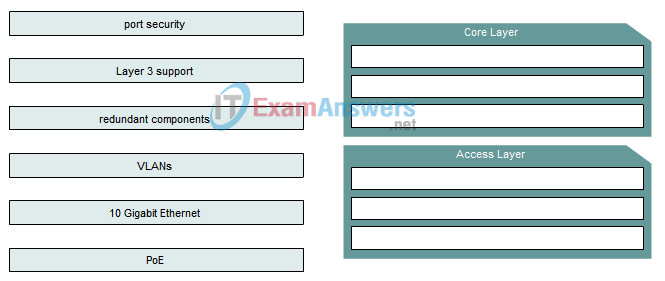
Answer
12. Which two characteristics describe the core layer of the hierarchical network design model? (Choose two.)
- redundant paths
- high-level policy enforcement
- PoE
- controls access of end devices to network
- rapid forwarding of traffic
