Switching, Routing, and Wireless Essentials (Versión 7.00) – SRWE Practice Final Exam Answers
Practice Final Exam – SRWE Answers
1. A network administrator is using the router-on-a-stick method to configure inter-VLAN routing. Switch port Gi1/1 is used to connect to the router. Which command should be entered to prepare this port for the task?
Switch(config)# interface gigabitethernet 1/1
Switch(config-if)# spanning-tree vlan 1
Switch(config)# interface gigabitethernet 1/1
Switch(config-if)# spanning-tree portfast
Switch(config)# interface gigabitethernet 1/1
Switch(config-if)# switchport mode trunk
Switch(config)# interface gigabitethernet 1/1
Switch(config-if)# switchport access vlan 1
2. Refer to the exhibit. The configuration shows commands entered by a network administrator for inter-VLAN routing. However, host H1 cannot communicate with H2. Which part of the inter-VLAN configuration causes the problem?
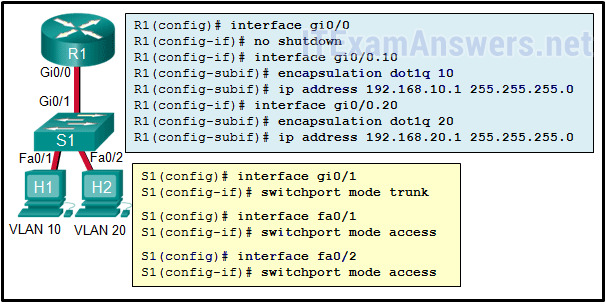
- trunking
- port mode on the two switch FastEthernet ports
- VLAN configuration
- router port configuration
3. Refer to the exhibit. Inter-VLAN communication between VLAN 10, VLAN 20, and VLAN 30 is not successful. What is the problem?
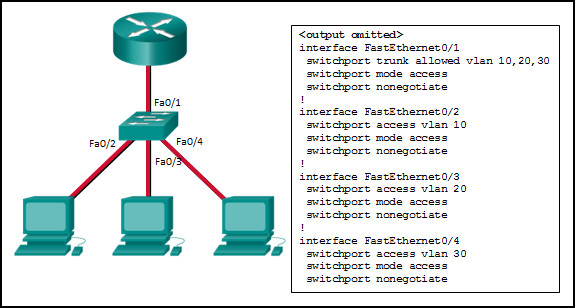
- The access interfaces do not have IP addresses and each should be configured with an IP address.
- The switch interface FastEthernet0/1 is configured as an access interface and should be configured as a trunk interface.
- The switch interface FastEthernet0/1 is configured to not negotiate and should be configured to negotiate.
- The switch interfaces FastEthernet0/2, FastEthernet0/3, and FastEthernet0/4 are configured to not negotiate and should be configured to negotiate.
4. An employee connects wirelessly to the company network using a cell phone. The employee then configures the cell phone to act as a wireless access point that will allow new employees to connect to the company network. Which type of security threat best describes this situation?
- cracking
- denial of service
- rogue access point
- spoofing
5. Which combination of WLAN authentication and encryption is recommended as a best practice for home users?
- WPA2 and AES
- WEP and RC4
- WPA and PSK
- EAP and AES
- WEP and TKIP
6. What are the two methods that a wireless NIC can use to discover an AP? (Choose two.)
- transmitting a probe request
- sending an ARP request broadcast
- receiving a broadcast beacon frame
- initiating a three-way handshake
- sending a multicast frame
7. What address and prefix length is used when configuring an IPv6 default static route?
- ::/0
- ::1/128
- 0.0.0.0/0
- FF02::1/8
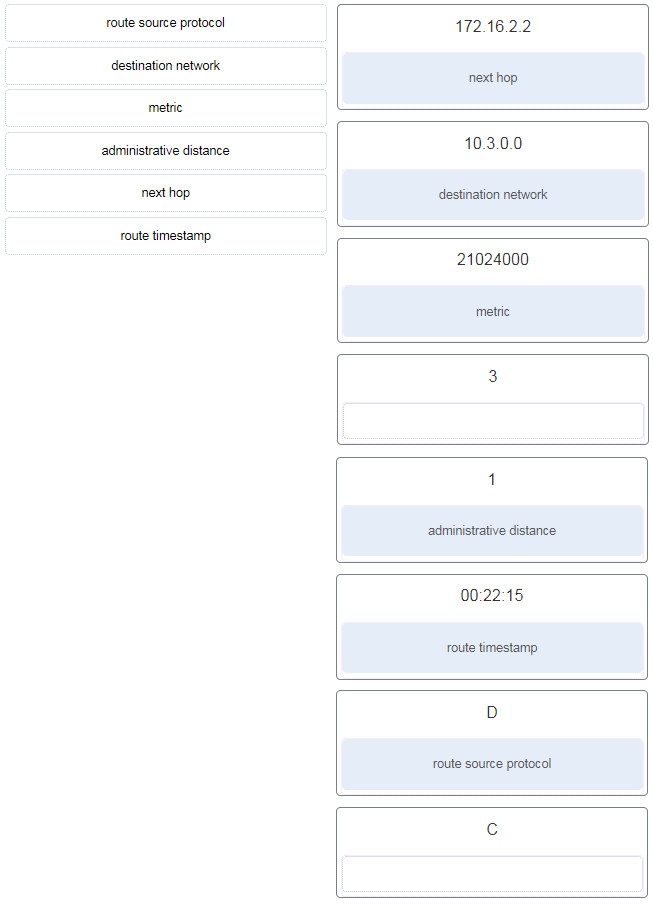
8. Refer to the exhibit. Match the description with the routing table entries. (Not all options are used.)
Graphic contains output of show ip route as follows:
R3# show ip route 172.16.0.0/24 is subnetted, 3 subnets C 172.16.0.0 is directly connected, Serial0/1/0 D 172.16.1.0 [90/21024000] via 172.16.0.1, 00:22:15, Serial0/1/0 C 172.16.2.0 is directly connected, Serial0/1/0 10.0.0.0/24 is subnetted, 1 subnets S 10.2.0.0/24 [1/0] via 172.16.2.2 C 10.3.0.0 is directly connected, FastEthernet0/0
9. Refer to the exhibit. Which interface will be the exit interface to forward a data packet that has the destination IP address 172.18.109.152?
Gateway of last resort is not set. 172.18.109.0/26 is variously subnetted, 7 subnets, 3 masks O 172.18.109.0/26 [110/10] via 172.18.32.1, 00:00:24, Serial0/0/0 O 172.18.109.64/26 [110/20] via 172.18.32.6, 00:00:56, Serial 0/0/1 O 172.18.109.128/26 [110/10] via 172.18.32.1, 00:00:24, Serial 0/0/0 C 172.18.109.192/27 is directly connected, GigabitEthernet0/0 L 172.18.109.193/27 is directly connected, GigabitEthernet0/0 C 172.18.109.224/27 is directly connected, GigabitEthernet0/1 L 172.18.109.225/27 is directly connected, GigabitEthernet0/1 172.18.32.0/24 is variably subnetted, 4 subnets, 2 masks C 172.18.32.0/30 is directly connected, Serial0/0/0 L 172.18.32.2/32 is directly connected, Serial0/0/0 C 172.18.32.4/30 is directly connected, Serial0/0/1 L 172.18.32.5/32 is directly connected, Serial0/0/1 S 172.18.33.0/26 [1/0] via 172.18.32.1, 00:00:24, Serial0/0/0 R1#
- GigabitEthernet0/0
- GigabitEthernet0/1
- Serial0/0/0
- None, the packet will be dropped.
10. Match the dynamic routing protocol component to the characteristic. (Not all options are used.)
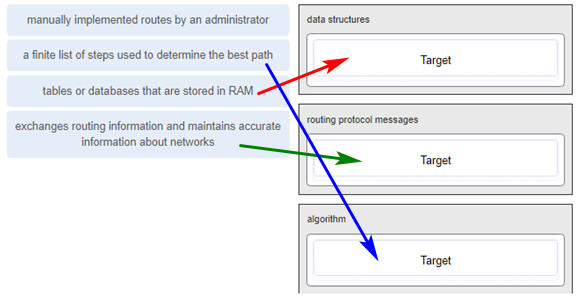
data structures
tables or databases that are stored in RAM
routing protocol messages
exchanges routing information and maintains accurate information about networks
algorithm
a finite list of steps used to determine the best path
11. Which statement describes the behavior of a switch when the MAC address table is full?
- It treats frames as unknown unicast and floods all incoming frames to all ports on the switch.
- It treats frames as unknown unicast and floods all incoming frames to all ports across multiple switches.
- It treats frames as unknown unicast and floods all incoming frames to all ports within the local VLAN.
- It treats frames as unknown unicast and floods all incoming frames to all ports within the collision domain.
12. Which term describes the role of a Cisco switch in the 802.1X port-based access control?
- agent
- supplicant
- authenticator
- authentication server
13. What is a result of connecting two or more switches together?
- The number of broadcast domains is increased.
- The size of the broadcast domain is increased.
- The number of collision domains is reduced.
- The size of the collision domain is increased.
14. A small publishing company has a network design such that when a broadcast is sent on the LAN, 200 devices receive the transmitted broadcast. How can the network administrator reduce the number of devices that receive broadcast traffic?
- Add more switches so that fewer devices are on a particular switch.
- Replace the switches with switches that have more ports per switch. This will allow more devices on a particular switch.
- Segment the LAN into smaller LANs and route between them.
- Replace at least half of the switches with hubs to reduce the size of the broadcast domain.
15.Refer to the exhibit. How is a frame sent from PCA forwarded to PCC if the MAC address table on switch SW1 is empty?
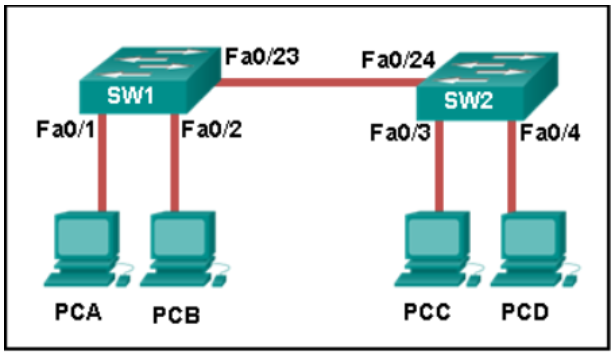
- SW1 forwards the frame directly to SW2. SW2 floods the frame to all ports connected to SW2, excluding the port through which the frame entered the switch.
- SW1 floods the frame on all ports on the switch, excluding the interconnected port to switch SW2 and the port through which the frame entered the switch.
- SW1 floods the frame on all ports on SW1, excluding the port through which the frame entered the switch.
- SW1 drops the frame because it does not know the destination MAC address.
16. What are two switch characteristics that could help alleviate network congestion? (Choose two.)
- fast internal switching
- large frame buffers
- store-and-forward switching
- low port density
- frame check sequence (FCS) check
17. A network engineer is configuring a LAN with a redundant first hop to make better use of the available network resources. Which protocol should the engineer implement?
- FHRP
- GLBP
- HSRP
- VRRP
18. Match the FHRP protocols to the appropriate description. (Not all options are used.)
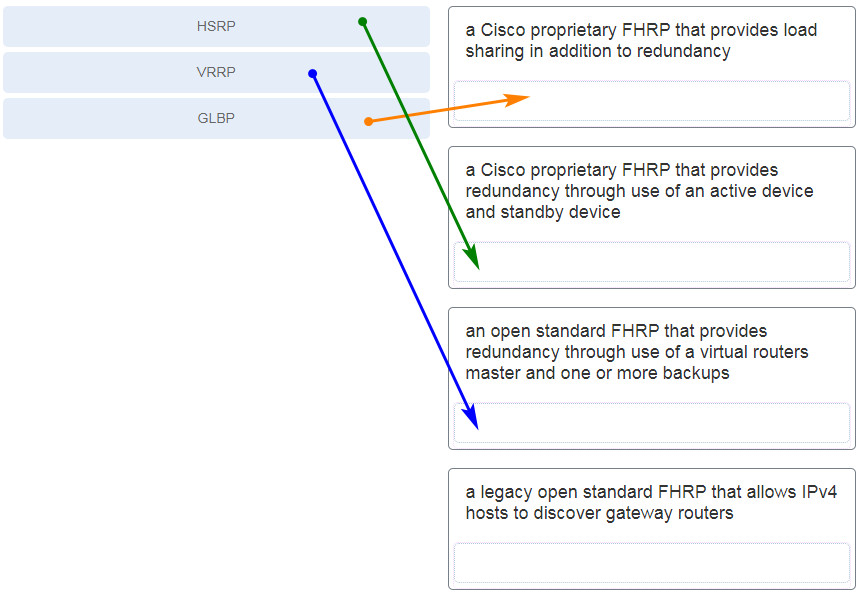
19. After sticky learning of MAC addresses is enabled, what action is needed to prevent dynamically learned MAC addresses from being lost in the event that an associated interface goes down?
- Reboot the switch.
- Copy the running configuration to the startup configuration.
- Shut down the interface then enable it again with the no shutdown command.
- Configure port security for violation protect mode.
20. A small coffee shop is offering free Wi-Fi to customers. The network includes a wireless router and a DSL modem that is connected to the local phone company. What method is typically used to configure the connection to the phone company?
- Set the WAN connection in the wireless router as a DHCP client.
- Set the connection between the wireless router and the DSL modem as a private IP network.
- Set the DSL modem as a DHCP client to get a public IP address from the wireless router.
- Set the DSL modem as a DHCP client to the phone company and a DHCP server for the internal connection.
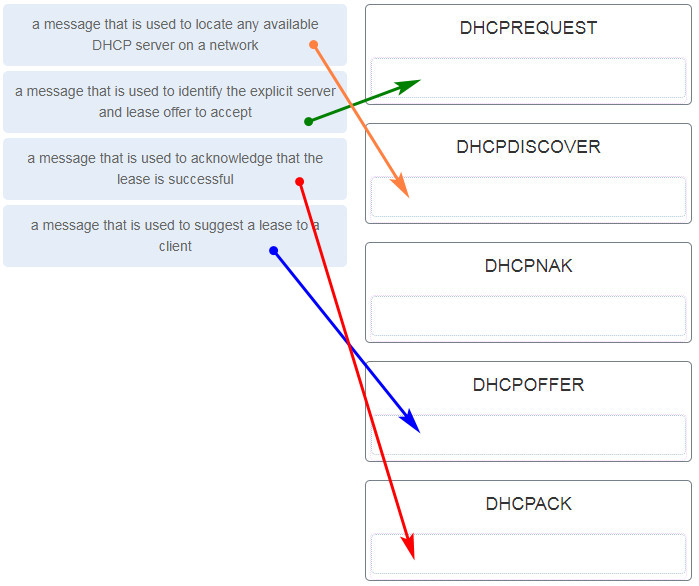
21. Match the purpose with its DHCP message type. (Not all options are used.)
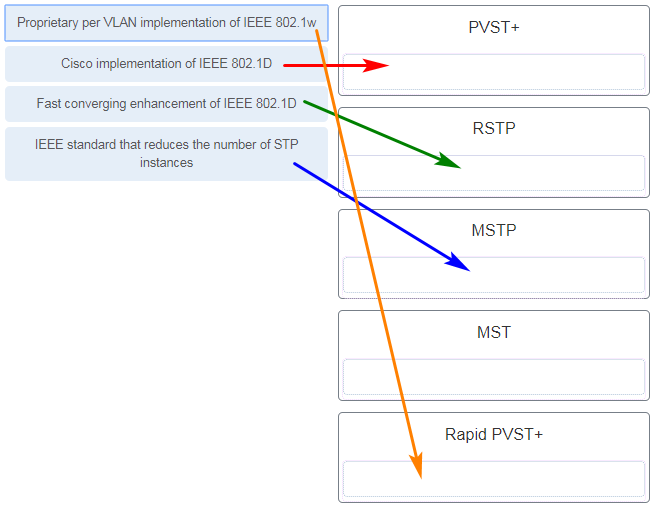
22. Match the spanning-tree feature with the protocol type. (Not all options are used.)
23. Which three components are combined to form a bridge ID?
- MAC address
- extended system ID
- IP address
- cost
- bridge priority
- port ID
24. What is an advantage of PVST+?
- PVST+ requires fewer CPU cycles for all the switches in the network.
- PVST+ reduces bandwidth consumption compared to traditional implementations of STP that use CST.
- PVST+ optimizes performance on the network through autoselection of the root bridge.
- PVST+ optimizes performance on the network through load sharing.
25. Which problem is evident if the show ip interface command shows that the interface is down and the line protocol is down?
- An encapsulation mismatch has occurred.
- A cable has not been attached to the port.
- The no shutdown command has not been issued on the interface.
- There is an IP address conflict with the configured address on the interface.
26. A technician is configuring a new Cisco 2960 switch. What is the effect of issuing the BranchSw(config)#interface VLAN88 command?
- It updates the MAC address table for the associated port.
- It applies an IPv4 address to the virtual interface.
- It permits an IPv6 address to be configured on a switch physical interface.
- It applies an IPv6 address to the virtual interface.
- It enters configuration mode for a switch virtual interface.
27. In what situation would a Layer 2 switch have an IP address configured?
- when the Layer 2 switch is using a routed port
- when the Layer 2 switch needs to be remotely managed
- when the Layer 2 switch is the default gateway of user traffic
- when the Layer 2 switch needs to forward user traffic to another device
28. Which command would create a valid IPv6 default route?
- ipv6 route ::/0 2001:db8:acad:2::a
- ipv6 route ::/0 fe80::1
- ipv6 route ::/128 2001:db8:acad:1::1
- ipv6 route 2001:db8:acad:1::/64 ::1
29. Refer to the exhibit. The routing table for R2 is as follows:
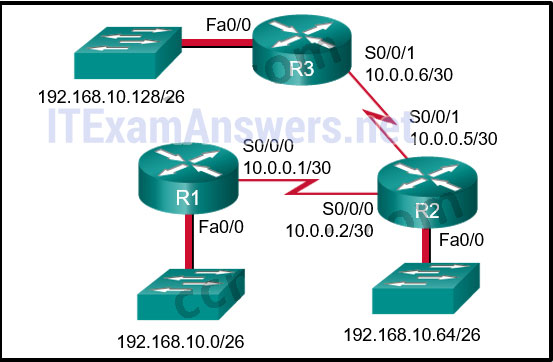
Gateway of last resort is not set 10.0.0.0/30 is subnetted, 2 subnets C 10.0.0.0 is directly connected, Serial0/0/0 C 10.0.0.4 is directly connected, Serial0/0/1 192.168.10.0/26 is subnetted, 3 subnets S 192.168.10.0 is directly connected, Serial0/0/0 C 192.168.10.64 is directly connected, FastEthernet0/0 S 192.168.10.128 [1/0] via 10.0.0.6
What will router R2 do with a packet destined for 192.168.10.129?
- drop the packet
- send the packet out interface Serial0/0/0
- send the packet out interface Serial0/0/1
- send the packet out interface FastEthernet0/0
30. Refer to the exhibit. Router R1 has an OSPF neighbor relationship with the ISP router over the 192.168.0.32 network. The 192.168.0.36 network link should serve as a backup when the OSPF link goes down. The floating static route command ip route 0.0.0.0 0.0.0.0 S0/0/1 100 was issued on R1 and now traffic is using the backup link even when the OSPF link is up and functioning. Which change should be made to the static route command so that traffic will only use the OSPF link when it is up?
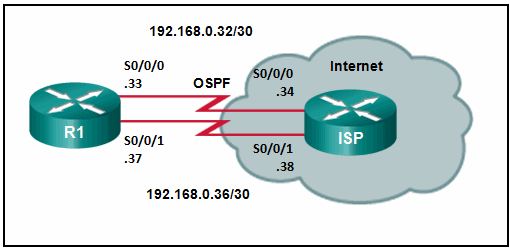
- Add the next hop neighbor address of 192.168.0.36.
- Change the administrative distance to 1.
- Change the destination network to 192.168.0.34.
- Change the administrative distance to 120.
31. A junior technician was adding a route to a LAN router. A traceroute to a device on the new network revealed a wrong path and unreachable status. What should be done or checked?
- Create a floating static route to that network.
- Check the configuration on the floating static route and adjust the AD.
- Check the configuration of the exit interface on the new static route.
- Verify that the static route to the server is present in the routing table.
32. Refer to the exhibit. When a packet arrives on interface Serial0/0/0 on R1, with a destination IP address of PC1, which two events occur? (Choose two)
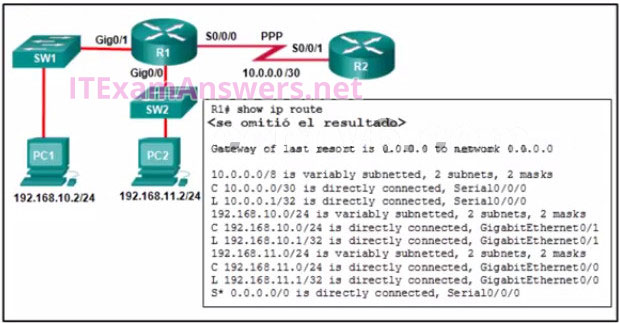
- Router R1 will de-encapsulate the packet and encapsulate it in a PPP frame.
- Router R1 will forward the packet out Gig0/1.
- Router R1 will forward the packet out Gig0/0.
- Router R1 will de-encapsulate the packet and encapsulate it in an Ethernet frame.
- Router R1 will forward the packet out S0/0/0.
33. Refer to the exhibit. How was the host route 2001:DB8:CAFE:4::1/128 installed in the routing table?
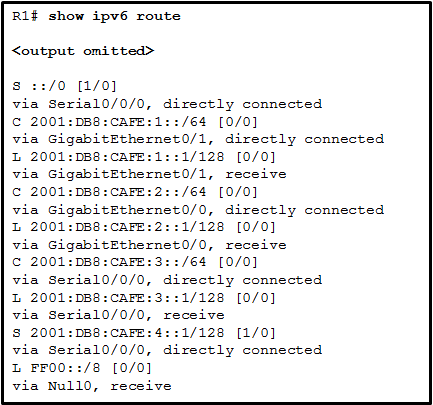
- The route was dynamically created by router R1.
- The route was dynamically learned from another router.
- The route was manually entered by an administrator.
- The route was automatically installed when an IP address was configured on an active interface.
34. Which command will start the process to bundle two physical interfaces to create an EtherChannel group via LACP?
- channel-group 2 mode auto
- interface port-channel 2
- channel-group 1 mode desirable
- interface range GigabitEthernet 0/4 – 5
35. Refer to the exhibit. Based on the command output shown, what is the status of the EtherChannel?
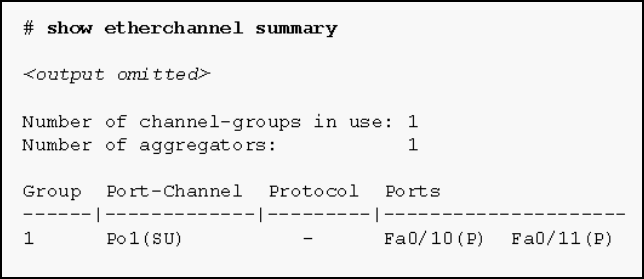
- The EtherChannel is dynamic and is using ports Fa0/10 and Fa0/11 as passive ports.
- The EtherChannel is down as evidenced by the protocol field being empty.
- The EtherChannel is partially functional as indicated by the P flags for the FastEthernet ports.
- The EtherChannel is in use and functional as indicated by the SU and P flags in the command output.
36. Refer to the exhibit. DLS1 is connected to another switch, DLS2, via a trunk link. A host that is connected to DLS1 is not able to communicate to a host that is connected to DLS2, even though they are both in VLAN 99. Which command should be added to Fa0/1 on DLS1 to correct the problem?
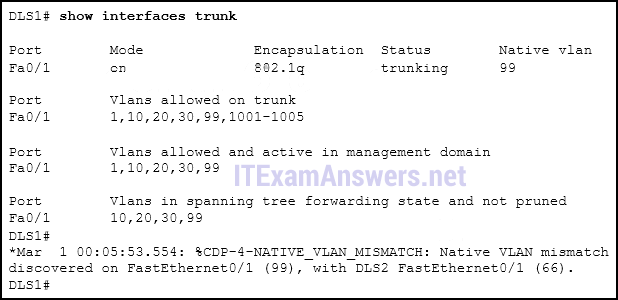
- switchport nonegotiate
- switchport mode dynamic auto
- switchport trunk native vlan 66
- switchport trunk allowed vlan add 99
37. Which type of traffic is designed for a native VLAN?
- management
- user-generated
- tagged
- untagged
38. Refer to the exhibit. PC-A and PC-B are both in VLAN 60. PC-A is unable to communicate with PC-B. What is the problem?
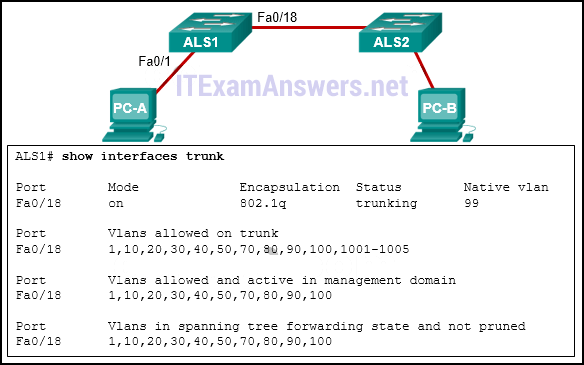
- The native VLAN should be VLAN 60.
- The native VLAN is being pruned from the link.
- The trunk has been configured with the switchport nonegotiate command.
- The VLAN that is used by PC-A is not in the list of allowed VLANs on the trunk.
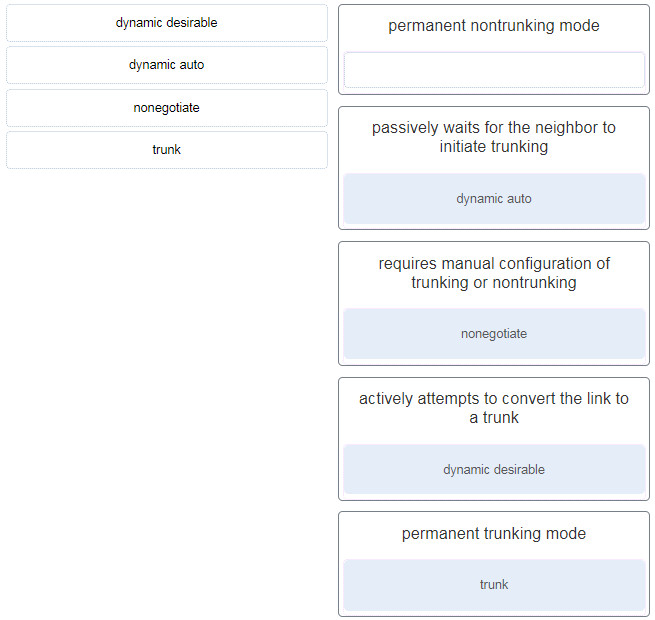
39. Question as presented: Match the DTP mode with its function. (Not all options are used.)
40. What type of VLAN is configured specifically for network traffic such as SSH, Telnet, HTTPS, HTTP, and SNMP?
- management VLAN
- security VLAN
- trunk VLAN
- voice VLAN
41. Refer to the exhibit. The users on the LAN network of R1 cannot receive an IPv6 address from the configured stateful DHCPv6 server. What is missing from the stateful DHCPv6 configuration on router R1?
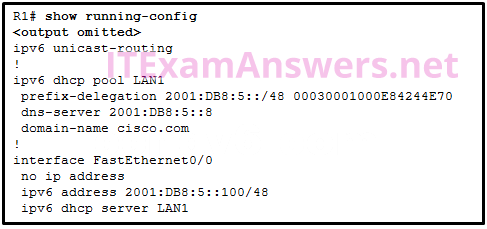
- The FA0/0 interface is missing the command that informs the clients to use stateful DHCPv6.
- IPv6 has not been enabled globally on router R1.
- The DHCPv6 pool has not been bound to the LAN interface.
- The DHCPv6 pool does not match the IPv6 address configured on interface FA0/0.
42. A network administrator is implementing DHCPv6 for the company. The administrator configures a router to send RA messages with M flag as 1 by using the interface command ipv6 nd managed-config-flag . What effect will this configuration have on the operation of the clients?
- Clients must use the information that is contained in RA messages.
- Clients must use all configuration information that is provided by a DHCPv6 server.
- Clients must use the prefix and prefix length that are provided by a DHCPv6 server and generate a random interface ID.
- Clients must use the prefix and prefix length that are provided by RA messages and obtain additional information from a DHCPv6 server.
43. Refer to the exhibit. A network administrator is troubleshooting a problem with EtherChannel. What command was used to produce the exhibited output?
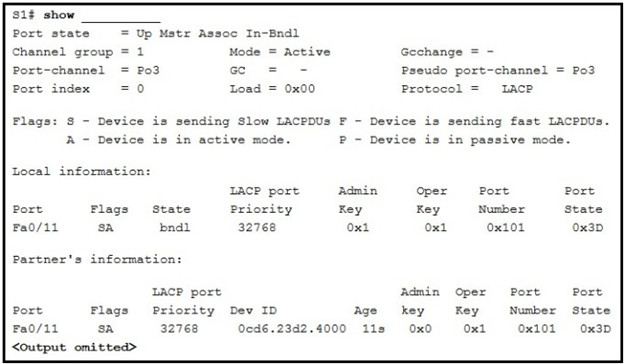
- show etherchannel Port-channel
- show interfaces Port-channel11
- show interfaces fastethernet 0/11 etherchannel
- show etherchannel summary
44. Refer to the exhibit. The administrator wants to enable port security on an interface on switch S1, but the command was rejected. Which conclusion can be drawn?
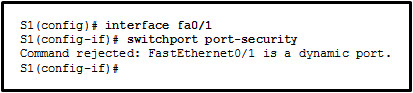
- The interface must be initially configured with the switchport mode trunk command.
- The interface needs to be configured initially with an IP address.
- The interface needs to be previously configured with the no shutdown command.
- The interface must be initially configured with the switchport mode access command.
45. On which port should Dynamic ARP Inspection (DAI) be configured on a switch?
- access ports only
- any untrusted port
- an uplink port to another switch
- on any port where DHCP snooping is disabled
46. Refer to the exhibit. A network administrator is configuring DAI on switch SW1. What is the result of entering the exhibited commands?
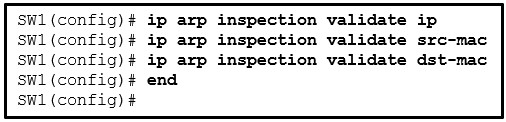
- DAI will validate both source and destination MAC addresses as well as the IP addresses in the order specified. If all parameters are valid then the ARP packet is allowed to pass.
- DAI will validate both source and destination MAC addresses as well as the IP addresses in the order specified. When one set of parameters are valid, the ARP packet is allowed to pass.
- DAI will validate only the destination MAC addresses.
- DAI will validate only the IP addresses.
47. Which Cisco solution helps prevent ARP spoofing and ARP poisoning attacks?
- Dynamic ARP Inspection
- IP Source Guard
- DHCP Snooping
- Port Security
48. What is the reason for disabling SSID broadcasting and changing the default SSID on a wireless access point?
- Wireless clients must then have the SSID manually configured to connect to the wireless network.
- Disabling SSID broadcasting frees up radio frequency bandwidth and increases the data throughput of the access point.
- Anyone with the default SSID can gain access to the access point and change the configuration.
- The access point stops broadcasting its own MAC address, thus preventing unauthorized wireless clients from connecting to the network.
49. What are two characteristics of Cisco Express Forwarding (CEF)? (Choose two.)
- When a packet arrives on a router interface, it is forwarded to the control plane where the CPU searches for a match in the fast-switching cache.
- This is the fastest forwarding mechanism on Cisco routers and multilayer switches.
- With this switching method, flow information for a packet is stored in the fast-switching cache to forward future packets to the same destination without CPU intervention.
- When a packet arrives on a router interface, it is forwarded to the control plane where the CPU matches the destination address with a matching routing table entry.
- Packets are forwarded based on information in the FIB and an adjacency table.
50. A network administrator of a college is configuring WLAN security with WPA2 Enterprise authentication. Which server is required when deploying this type of authentication?
- AAA
- RADIUS
- DHCP
- SNMP
51. What is a potential issue when using the WLC to upgrade and deploy the latest firmware image to all APs?
- Usernames and passwords must be manually entered into the AP so that WLAN authentication continues during the upgrade.
- Only one of the two bands would work at a time.
- Users will not be able to use the WLAN.
- Old 802.11 standards may not be supported anymore.
52. A network administrator is configuring a WLC to provide WLAN access to users in an office building. When testing the newly created WLAN, the administrator does not see the SSID from a wireless device. What is a possible cause?
- The WLAN security setting is incorrect.
- The APs have not been configured for the new WLAN.
- The new WLAN needs to be enabled.
- The RADUIS server is not operational.
53. What is the best way to prevent a VLAN hopping attack?
- Disable trunk negotiation for trunk ports and statically set nontrunk ports as access ports.
- Disable STP on all nontrunk ports.
- Use VLAN 1 as the native VLAN on trunk ports.
- Use ISL encapsulation on all trunk links.
54. An administrator has configured a DHCPv4 relay router and issued these commands:
Router(config)# interface g0/0 Router(config-if)# ip address 10.0.1.1 255.255.255.0 Router(config-if)# no shutdown Router(config-if)# exit Router(config)# ip dhcp pool RELAY Router(dhcp-config)# end
The clients are not receiving IP parameters from the DHCPv4 server. What is a possible cause?
- The IP address is incorrect for the subnet mask that is used.
- The pool cannot be named ‘RELAY’.
- The ip helper-address command is missing.
- The router is configured as a DHCPv4 client.
55. Consider the following command:
ip route 192.168.10.0 255.255.255.0 10.10.10.2 5
What does the 5 at the end of the command signify?
- exit interface
- maximum number of hops to the 192.168.10.0/24 network
- metric
- administrative distance

What type of VLAN is configured specifically for network traffic such as SSH, Telnet, HTTPS, HTTP, and SNMP?
Management VLAN
Management vLAN
hello,please this dump is valid?
Hello Tom! We don’t have question for this exam. You can find answers to each question on this site or google yourself. I hope you can share the questions after this exam is over. Thanks you!
Hi, I have the question list, can you send me an email.
My email: [email protected]
Thanks you so much!
hey i need the answers for ccna 2 v7 practice final. can you please send me?
[email protected]
can u send them 2 me pleas [email protected]
send me please :
[email protected]
send me please :
[email protected]