Check answers here:
CCNA (200-301) Certification Practice Exam Answers (ENSA v7.0)
Quiz-summary
0 of 142 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
Information
CCNA (200-301) Certification Practice Exam (ENSA v7.0) - Test online
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 142 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
- Answered
- Review
-
Question 1 of 142
1. Question
1 pointsAn instructor is reviewing student answers on a previous term exam to prepare for a lecture on IPv6. What would be a good point for the instructor to make when explaining an IPv6 GUA (global unicast address)?Correct
Incorrect
-
Question 2 of 142
2. Question
1 pointsAn administrator needs to implement a 2.4GHz WLAN that requires multiple APs. Which two are characteristics of the 2.4GHz channels? (Choose two.)Correct
Incorrect
-
Question 3 of 142
3. Question
1 pointsA technician must accommodate at least 500 subnets from address 172.16.0.0/16. What is an appropriate subnet mask and corresponding number of available host IP addresses per subnet to meet the requirement?Correct
Incorrect
-
Question 4 of 142
4. Question
1 pointsRefer to the exhibit. A PC with the MAC address of 0800.069d.3841 attached to port Fa0/8 is sending data to a device that has the MAC address of 6400.6a5a.6821. What will the switch do first to handle the data transfer?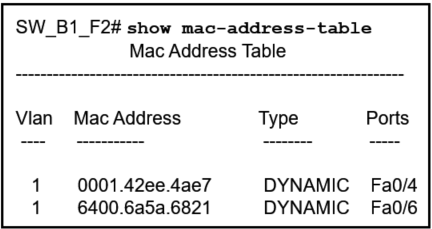 Correct
Correct
Incorrect
-
Question 5 of 142
5. Question
1 pointsA network engineer is giving a tour of the company network operations center to a college class. The engineer is trying to describe how a WAN and connectivity to the internet relate to the network infrastructure. Which statement correctly describes network infrastructure and network communication?Correct
Incorrect
-
Question 6 of 142
6. Question
1 pointsA network engineer is designing a borderless switched network in a hierarchical fashion. Which guideline might cause the engineer to implement a three-tier layer model?Correct
Incorrect
-
Question 7 of 142
7. Question
1 pointsTwo students are discussing routers and one statement that is said between them is accurate. Which statement is that?Correct
Incorrect
-
Question 8 of 142
8. Question
1 pointsWhat are two benefits of using virtualization? (Choose two.)Correct
Incorrect
-
Question 9 of 142
9. Question
1 pointsStudents in a data networking class are reviewing materials in preparation for a quiz. Which statement describes the operation of an access control method for shared network media?Correct
Incorrect
-
Question 10 of 142
10. Question
1 pointsA network administrator is designing an IPv4 addressing scheme and requires these subnets. 1 subnet of 100 hosts 2 subnets of 80 hosts 2 subnets of 30 hosts 4 subnets of 20 hosts Which combination of subnets and masks will provide the best addressing plan for these requirements?Correct
Incorrect
-
Question 11 of 142
11. Question
1 pointsA group of network technicians is discussing IPv6 multicast processes. What is a feature of one type of IPv6 multicast address that should be discussed?Correct
Incorrect
-
Question 12 of 142
12. Question
1 pointsWhich LAN attack allows for identification of connected Cisco devices which are sending unencrypted broadcasts?Correct
Incorrect
-
Question 13 of 142
13. Question
1 pointsWhat is a characteristic of the REST API?Correct
Incorrect
-
Question 14 of 142
14. Question
1 pointsA network administrator is using the Cisco DNA Center to monitor network health and to troubleshoot network issues. Which area should the administrator use to perform these tasks?Correct
Incorrect
-
Question 15 of 142
15. Question
1 pointsWhich term describes the process of managing configuration changes of network devices in an orderly fashion?Correct
Incorrect
-
Question 16 of 142
16. Question
1 pointsWhich function of the Cisco intent-based networking system (IBNS) enables network operators to express the expected networking behavior that will best support the business intent?Correct
Incorrect
-
Question 17 of 142
17. Question
1 pointsWhich type of API would be used to allow authorized salespeople of an organization access to internal sales data from their mobile devices?Correct
Incorrect
-
Question 18 of 142
18. Question
1 pointsRefer to the exhibit. In the displayed JSON data representation, which symbol should be used to replace the question mark in lines 2 and 15?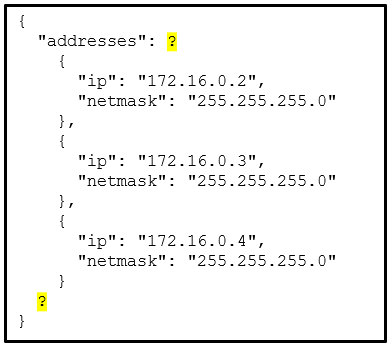 Correct
Correct
Incorrect
-
Question 19 of 142
19. Question
1 pointsWhat action takes place when a frame entering a switch has a multicast destination MAC address?Correct
Incorrect
-
Question 20 of 142
20. Question
1 pointsA network engineer is configuring secure remote access to a Cisco router. Which two commands would be issued in the line configuration mode of the router to implement SSH? (Choose two.)Correct
Incorrect
-
Question 21 of 142
21. Question
1 pointsWhen an end device requests services from a DHCPv4 server it receives a host IPv4 address and a subnet mask. Which two other IPv4 addresses are also typically provided to a DCHPv4 client? (Choose two.)Correct
Incorrect
-
Question 22 of 142
22. Question
1 pointsA network engineer wants to synchronize the time of a router with an NTP server at the IPv4 address 209.165.200.225. The exit interface of the router is configured with an IPv4 address of 192.168.212.11. Which global configuration command should be used to configure the NTP server as the time source for this router?Correct
Incorrect
-
Question 23 of 142
23. Question
1 pointsWhen testing a new web server, a network administrator cannot access the home page when the server name is entered into a web browser on a PC. Pings to both the IPv4 and IPv6 addresses of the server are successful. What could be the problem?Correct
Incorrect
-
Question 24 of 142
24. Question
1 pointsA network engineer is using SNMP manager software to monitor and manage network performance. In addition to polling network devices at regular time intervals, the engineer is configuring the devices to generate messages that inform the SNMP manager of specified events. What message type is configured on those devices that allows them to send unsolicited messages?Correct
Incorrect
-
Question 25 of 142
25. Question
1 pointsA wireless network engineer is implementing updated wireless equipment within the company. Which statement describes a wireless security protocol?Correct
Incorrect
-
Question 26 of 142
26. Question
1 pointsRefer to the exhibit. Which access list configuration on router R1 will prevent traffic from the 192.168.2.0 LAN from reaching the Restricted LAN while permitting traffic from any other LAN?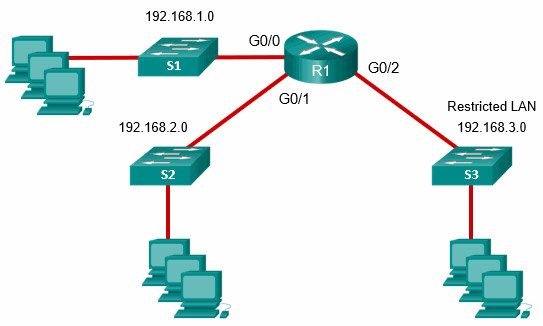 Correct
Correct
Incorrect
-
Question 27 of 142
27. Question
1 pointsAn administrator who is troubleshooting connectivity issues on a switch notices that a switch port configured for port security is in the err-disabled state. After verifying the cause of the violation, how should the administrator re-enable the port without disrupting network operation?Correct
Incorrect
-
Question 28 of 142
28. Question
1 pointsAn IT security specialist enables port security on a switch port of a Cisco switch. What is the default violation mode in use until the switch port is configured to use a different violation mode?Correct
Incorrect
-
Question 29 of 142
29. Question
1 pointsRefer to the exhibit. Which interface on switch S1 should be configured as a DHCP snooping trusted port to help mitigate DHCP spoofing attacks?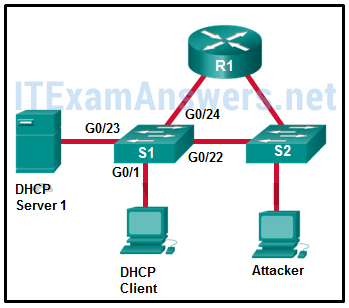 Correct
Correct
Incorrect
-
Question 30 of 142
30. Question
1 pointsWhich statement is an accurate description of a VPN type?Correct
Incorrect
-
Question 31 of 142
31. Question
1 pointsA network administrator of a college is configuring WLAN security with WPA2 Enterprise authentication. Which server is required when deploying this type of authentication?Correct
Incorrect
-
Question 32 of 142
32. Question
1 pointsWhen configuring a switch for SSH access, what other command that is associated with the login local command is required to be entered on the switch?Correct
Incorrect
-
Question 33 of 142
33. Question
1 pointsWhat term describes a process where a router simply discards any packet that arrives at the end of a queue that has completely used up its packet-holding resources?Correct
Incorrect
-
Question 34 of 142
34. Question
1 pointsIn an OSPF network when are DR and BDR elections required?Correct
Incorrect
-
Question 35 of 142
35. Question
1 pointsA network engineer has been asked to prepare a router and to ensure that it can route IPv6 packets. Which command should the network engineer ensure has been entered on the router?Correct
Incorrect
-
Question 36 of 142
36. Question
1 pointsRefer to the exhibit. Match the packets with their destination IP address to the exiting interfaces on the router. (Not all targets are used.)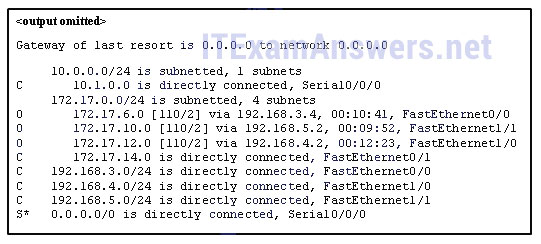 Correct
Correct
Incorrect
-
Question 37 of 142
37. Question
1 pointsConsider the following static route configured on a Cisco router:ipv6 route 2001:db8:acad:4::/64 2001:db8:acad:3::2
What remote network is specified in this route?Correct
Incorrect
-
Question 38 of 142
38. Question
1 pointsA network administrator configures a router with theipv6 route ::/0 Serial2/0command. What is the purpose of this command?Correct
Incorrect
-
Question 39 of 142
39. Question
1 pointsWhat is the purpose of a First Hop Redundancy Protocol?Correct
Incorrect
-
Question 40 of 142
40. Question
1 pointsA network engineer examining the configuration of a Cisco router sees a network entry in a routing table listed with a code O. Which kind of route is this?Correct
Incorrect
-
Question 41 of 142
41. Question
1 pointsWhat defines a host route on a Cisco router?Correct
Incorrect
-
Question 42 of 142
42. Question
1 pointsRefer to the exhibit. Packets destined to which two networks will require the router to perform a recursive lookup? (Choose two.)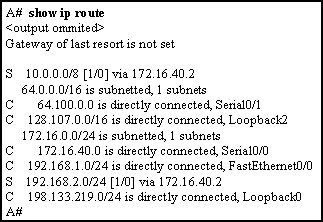 Correct
Correct
Incorrect
-
Question 43 of 142
43. Question
1 pointsThe routing table of a Cisco router has four static routes for network 10.0.0.0. Which route is the best match for a packet entering the router with a destination of 10.16.0.10?Correct
Incorrect
-
Question 44 of 142
44. Question
1 pointsMatch the FHRP protocols to the appropriate description. (Not all options are used.)Correct
Incorrect
-
Question 45 of 142
45. Question
1 pointsOpen the PT Activity. Perform the tasks in the activity instructions and then answer the question.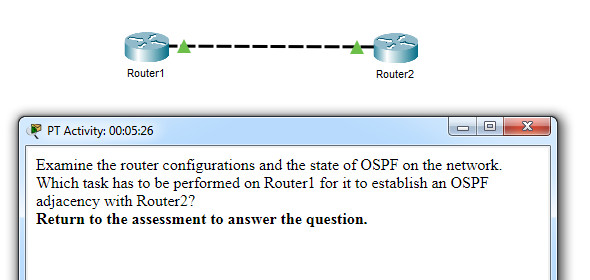 Which task has to be performed on Router 1 for it to establish an OSPF adjacency with Router 2? Correct
Which task has to be performed on Router 1 for it to establish an OSPF adjacency with Router 2? Correct
Incorrect
-
Question 46 of 142
46. Question
1 pointsWhat is the recommended Cisco best practice for configuring an OSPF-enabled router so that each router can be easily identified when troubleshooting routing issues?Correct
Incorrect
-
Question 47 of 142
47. Question
1 pointsIn FHRP terminology, what represents a set of routers that present the illusion of a single router to hosts?Correct
Incorrect
-
Question 48 of 142
48. Question
1 pointsA network administrator is configuring the SNMP function on a Cisco 3500 series WLC. The task is to add an SNMP trap server to which this WLC will forward SNMP log messages. Which tab should the administrator use to add the SNMP trap server information?Correct
Incorrect
-
Question 49 of 142
49. Question
1 pointsMatch the STP port state with the appropriate description. (Not all options are used.)Correct
Incorrect
-
Question 50 of 142
50. Question
1 pointsRefer to the exhibit. All the displayed switches are Cisco 2960 switches with the same default priority and operating at the same bandwidth. Which three ports will be STP designated ports? (Choose three.)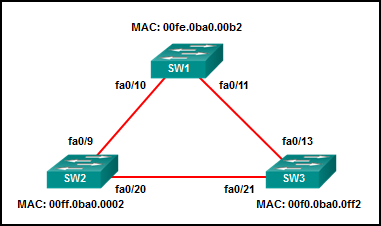 Correct
Correct
Incorrect
-
Question 51 of 142
51. Question
1 pointsRefer to the exhibit. A network technician issues the command show vlan to verify the VLAN configuration. Based on the output, which port should be assigned with native VLAN?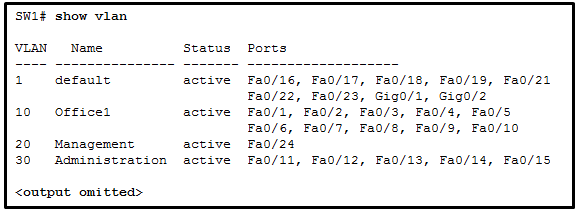 Correct
Correct
Incorrect
-
Question 52 of 142
52. Question
1 pointsWhat is the purpose of setting the native VLAN separate from data VLANs?Correct
Incorrect
-
Question 53 of 142
53. Question
1 pointsWhich is a characteristic of EtherChannel?Correct
Incorrect
-
Question 54 of 142
54. Question
1 pointsWhat characteristic describes how data or voice VLANs are configured on a network?Correct
Incorrect
-
Question 55 of 142
55. Question
1 pointsWhat are two load-balancing methods in the EtherChannel technology? (Choose two.)Correct
Incorrect
-
Question 56 of 142
56. Question
1 pointsA network administrator is configuring a WLAN with WPA2 Enterprise on a Cisco 3500 series WLC. Client authentications will be handled by a RADIUS server. Which tab should the administrator use to add the RADIUS server information?Correct
Incorrect
-
Question 57 of 142
57. Question
1 pointsAn administrator issues the show vlan brief command on a Cisco switch and the output shows that all ports are currently assigned to the default VLAN. What conclusion can be drawn?Correct
Incorrect
-
Question 58 of 142
58. Question
1 pointsIf no bridge priority is configured in PVST, which criteria is considered when electing the root bridge?Correct
Incorrect
-
Question 59 of 142
59. Question
1 pointsRefer to the exhibit. A network administrator issues the show lldp neighbors command to display information about neighboring devices. What can be determined based on the information?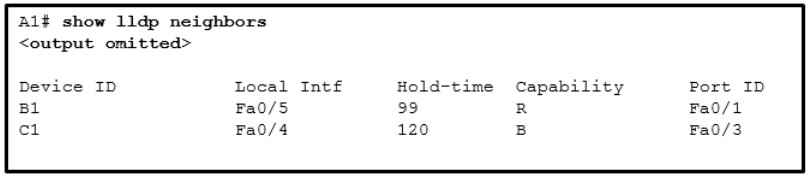 Correct
Correct
Incorrect
-
Question 60 of 142
60. Question
1 pointsWhat characteristic completes the following statement? When an IPv6 static route is configured, it is possible that the same IPv6 link-local address is used for ……Correct
Incorrect
-
Question 61 of 142
61. Question
1 pointsWhich two protocols provide gateway redundancy at Layer 3? (Choose two.)Correct
Incorrect
-
Question 62 of 142
62. Question
1 pointsWhich security solution identifies incoming threats and blocks them from entering the corporate network?Correct
Incorrect
-
Question 63 of 142
63. Question
1 pointsRefer to the exhibit. What does the hyphen symbol (-) indicate in the YAML data structure?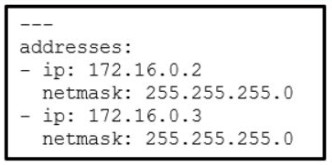 Correct
Correct
Incorrect
-
Question 64 of 142
64. Question
1 pointsIn an Intent-Based Networking architecture, which two items are considered parts of an overlay fabric? (Choose two.)Correct
Incorrect
-
Question 65 of 142
65. Question
1 pointsWhat is an architectural constraint to which a true RESTful API web service must adhere?Correct
Incorrect
-
Question 66 of 142
66. Question
1 pointsA programmer is using Ansible as the configuration management tool. Which term is used to describe a set of instructions for execution?Correct
Incorrect
-
Question 67 of 142
67. Question
1 pointsWhat action takes place when the source MAC address of a frame entering a switch is not in the MAC address table?Correct
Incorrect
-
Question 68 of 142
68. Question
1 pointsIn a controller-based wireless network, a Cisco WLC device has four ports connected to a switch to form a bundle. This bundle will provide load balancing and redundancy. Which two configurations must be performed on the four switch ports that connect to the WLC? (Choose two.)Correct
Incorrect
-
Question 69 of 142
69. Question
1 pointsWhen configuring a wireless LAN, to which category does a home wireless router belong?Correct
Incorrect
-
Question 70 of 142
70. Question
1 pointsWhich feature or function does an AP provide in a wireless LAN?Correct
Incorrect
-
Question 71 of 142
71. Question
1 pointsA network engineer is designing a borderless switched network in a hierarchical fashion. Why might the engineer consider using a two-tier layer model?Correct
Incorrect
-
Question 72 of 142
72. Question
1 pointsA technician is troubleshooting a network device and suspects there might be a duplex mismatch. What could cause a duplex mismatch?Correct
Incorrect
-
Question 73 of 142
73. Question
1 pointsA pharmaceutical company wants to contract the services of a cloud provider to store employee data and company-specific applications with strict access security. Which type of cloud would be the most appropriate for this scenario?Correct
Incorrect
-
Question 74 of 142
74. Question
1 pointsWhich LAN attack involves the sending of a double-tagged 802.1Q frame to the switch?Correct
Incorrect
-
Question 75 of 142
75. Question
1 pointsSNMP has been implemented on a network to monitor and manage devices. Which SNMP authentication process is preferred when SNMP managers communicate with SNMP agents?Correct
Incorrect
-
Question 76 of 142
76. Question
1 pointsWhat characteristic completes the following statement? When an IPv6 static route is configured, the use of a link-local address as a next-hop address requires entering ……Correct
Incorrect
-
Question 77 of 142
77. Question
1 pointsA network engineer is examining the routing table of a Cisco router. Consider the following routing table entry:S 10.2.2.0/30 [1/0] via 10.1.1.2, 00:00:13, Serial0/0/0
What is the significance of the Serial0/0/0?Correct
Incorrect
-
Question 78 of 142
78. Question
1 pointsWhen creating an IPv6 static route, when must a next-hop IPv6 address and an exit interface both be specified?Correct
Incorrect
-
Question 79 of 142
79. Question
1 pointsWhat characterizes a floating static route?Correct
Incorrect
-
Question 80 of 142
80. Question
1 pointsWhich feature on a Cisco router permits the forwarding of traffic for which there is no specific route?Correct
Incorrect
-
Question 81 of 142
81. Question
1 pointsWhich ACE would permit traffic from hosts only on the 192.168.8.0/22 subnet?Correct
Incorrect
-
Question 82 of 142
82. Question
1 pointsRefer to the exhibit. A network administrator needs to add an ACE to the TRAFFIC-CONTROL ACL that will deny IP traffic from the subnet 172.23.16.0/20. Which ACE will meet this requirement? Correct
Correct
Incorrect
-
Question 83 of 142
83. Question
1 pointsWhat are two syntax rules for writing a JSON array? (Choose two.)Correct
Incorrect
-
Question 84 of 142
84. Question
1 pointsWhat is the most likely cause when the output of the show interface command shows that a switch interface is up but the line protocol is down?Correct
Incorrect
-
Question 85 of 142
85. Question
1 pointsRefer to the exhibit. A network administrator is reviewing the configuration of switch S1. Which protocol has been implemented to group multiple physical ports into one logical link?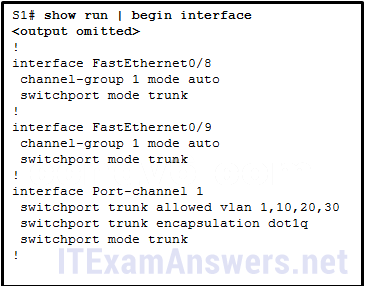 Correct
Correct
Incorrect
-
Question 86 of 142
86. Question
1 pointsA network administrator is considering whether PoE features are required in a specific network installation. Which option provides valid information about PoE?Correct
Incorrect
-
Question 87 of 142
87. Question
1 pointsHow are network data transmissions calculated?Correct
Incorrect
-
Question 88 of 142
88. Question
1 pointsRefer to the exhibit. A corporate network is using NTP to synchronize the time across devices. What can be determined from the displayed output?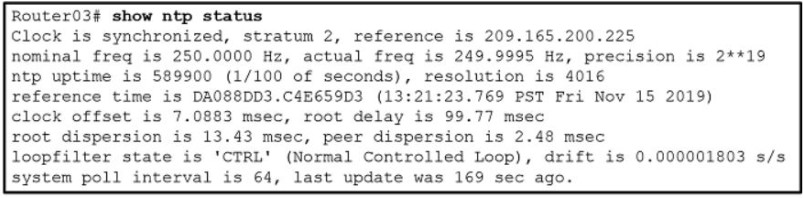 Correct
Correct
Incorrect
-
Question 89 of 142
89. Question
1 pointsRefer to the exhibit. Which source address is being used by router R1 for packets being forwarded to the Internet?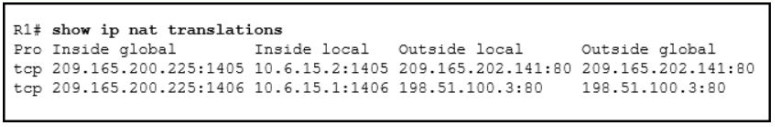 Correct
Correct
Incorrect
-
Question 90 of 142
90. Question
1 pointsA user is reading a book from the website https://www.books-info.com/author50/book1.html#page150 . Which term is used to describe the component http://www.books-info.com/author50/book1.html ?Correct
Incorrect
-
Question 91 of 142
91. Question
1 pointsWhat are three components used in the query portion of a typical RESTful API request? (Choose three.)Correct
Incorrect
-
Question 92 of 142
92. Question
1 pointsWhich two configuration management tools are developed using Python? (Choose two.)Correct
Incorrect
-
Question 93 of 142
93. Question
1 pointsWhat characteristic completes the following statement? When an IPv6 static route is configured, and traffic is to be directed to one specific server, the static route requires …Correct
Incorrect
-
Question 94 of 142
94. Question
1 pointsWhen two or more routes to the same destination are learned from different routing protocols, what does a router use to choose between the routes?Correct
Incorrect
-
Question 95 of 142
95. Question
1 pointsWhich LAN attack enables traffic from one VLAN to be seen by another VLAN without the aid of a router?Correct
Incorrect
-
Question 96 of 142
96. Question
1 pointsWhat are the three categories of tools that can be used in IP networks to implement QoS? (Choose three.)Correct
Incorrect
-
Question 97 of 142
97. Question
1 pointsWhich is a QoS model that a network engineer would implement to ensure a source to destination quality of service standard for a specified data flow?Correct
Incorrect
-
Question 98 of 142
98. Question
1 pointsA network engineer is configuring a Cisco switch when this message is displayed.%LINK-3-UPDOWN: Interface Port-channel1, changed state to up
What is the Syslog severity level of this message?Correct
Incorrect
-
Question 99 of 142
99. Question
1 pointsIn a controller-based wireless network, the WLC device may have multiple ports connected to a switch to form a bundle that provides load-balancing and redundancy. Which protocol supports the port bundle between a Cisco WLC and a Cisco switch?Correct
Incorrect
-
Question 100 of 142
100. Question
1 pointsIn a controller-based wireless network, a Cisco WLC device has four ports connected to a switch to form a bundle. This bundle will provide load-balancing and redundancy. Which two configurations must be performed on the four switch ports that connect to the WLC? (Choose two.)Correct
Incorrect
-
Question 101 of 142
101. Question
1 pointsWhat is a benefit of PortFast configured on a Cisco switch port?Correct
Incorrect
-
Question 102 of 142
102. Question
1 pointsA network administrator is configuring security for new WLANs on a Cisco 3500 series WLC. What is the default protocol used for authentication key management?Correct
Incorrect
-
Question 103 of 142
103. Question
1 pointsWhich two statements describe an Internet-based connectivity option? (Choose two.)Correct
Incorrect
-
Question 104 of 142
104. Question
1 pointsWhat is a difference between autonomous APs and controller-based APs in wireless LANs?Correct
Incorrect
-
Question 105 of 142
105. Question
1 pointsTwo recent networking graduates from a local college have just been hired by a communication company to work on various network cabling projects throughout the state. Why would the company consider using fiber-optic cabling in long-haul networks?Correct
Incorrect
-
Question 106 of 142
106. Question
1 pointsAn employee is logging into a company account and another employee stands in such a way to see the account ID and password. Which kind of threat is this?Correct
Incorrect
-
Question 107 of 142
107. Question
1 pointsWhat is the purpose of the overload keyword in the ip nat inside source list 1 pool NAT_POOL overload command?Correct
Incorrect
-
Question 108 of 142
108. Question
1 pointsWhat two types of always-on internet connections are commonly used by teleworkers to communicate with a company? (Choose two.)Correct
Incorrect
-
Question 109 of 142
109. Question
1 pointsA technician needs to add a new wireless device to a small WLAN. The WLAN is a mixture of old and newer 802.11b and 802.11g devices. What choice for the new device would provide the most interoperability for present and future growth?Correct
Incorrect
-
Question 110 of 142
110. Question
1 pointsWhat action takes place when a frame entering a switch has a unicast destination MAC address appearing in the MAC address table?Correct
Incorrect
-
Question 111 of 142
111. Question
1 pointsA technician is reviewing a report of slowness during peak traffic periods and is looking at performance on a particular switch. What should the technician be aware of about memory buffering on a switch?Correct
Incorrect
-
Question 112 of 142
112. Question
1 pointsA company deploys FlexConnect APs in the remote office and uses CAPWAP to allow a WLC in their corporate headquarters office to manage WLANs in the remote office. One day the network administrator in the remote office notices that the FlexConnect APs are operating in the standalone mode. Which two functions can these APs perform in this mode? (Choose two.)Correct
Incorrect
-
Question 113 of 142
113. Question
1 pointsWhat term describes a default queuing method where packets are sent out of an interface in the order in which they arrive?Correct
Incorrect
-
Question 114 of 142
114. Question
1 pointsAn employee who travels constantly for work needs to access the company network remotely. Which security mechanism offers a secure connection?Correct
Incorrect
-
Question 115 of 142
115. Question
1 pointsWhich protocol defines port-based authentication to restrict unauthorized hosts from connecting to the LAN through publicly accessible switch ports?Correct
Incorrect
-
Question 116 of 142
116. Question
1 pointsWhat is a spyware threat?Correct
Incorrect
-
Question 117 of 142
117. Question
1 pointsWhat characteristic completes the following statement? When an IPv6 static route is configured, a fully-specified configuration should be used with …Correct
Incorrect
-
Question 118 of 142
118. Question
1 pointsWhich LAN attack spoofs the root bridge to change the topology of a network?Correct
Incorrect
-
Question 119 of 142
119. Question
1 pointsRefer to the exhibit. A network administrator is reviewing port and VLAN assignments on switch S2 and notices that interfaces Gi0/1 and Gi0/2 are not included in the output. Why would the interfaces be missing from the output? Correct
Correct
Incorrect
-
Question 120 of 142
120. Question
1 pointsData is being sent from a source PC to a destination server. Which three statements correctly describe the function of TCP or UDP in this situation? (Choose three.)Correct
Incorrect
-
Question 121 of 142
121. Question
1 pointsWhich two 802.11 WLAN standards operate in both the 2.4 GHz and in the 5 GHz frequency bands? (Choose two.)Correct
Incorrect
-
Question 122 of 142
122. Question
1 pointsWhich two protocols are used to provide server-based AAA authentication? (Choose two.)Correct
Incorrect
-
Question 123 of 142
123. Question
1 pointsA network engineer is examining Cisco router configurations across an internetwork. Consider the following routing table entryO 10.0.4.0/24 [110/50] via 10.0.3.2, 00:24:22, Serial0/1/1
What is the administrative distance of this route?Correct
Incorrect
-
Question 124 of 142
124. Question
1 pointsWhat term describes allowing delay-sensitive packets such as voice to be sent before packets in other queues based on strict priority queuing?Correct
Incorrect
-
Question 125 of 142
125. Question
1 pointsWhich two 802.11 WLAN standards operate in both the 2.4 Ghz and in the 5Ghz frequency bands?(Choose two)Correct
Incorrect
-
Question 126 of 142
126. Question
1 pointsA network engineer is configuring a Cisco router as a DHCP relay. When issuing the ip helper-address command in the interface configuration mode which IPv4 address is added to the command?Correct
Incorrect
-
Question 127 of 142
127. Question
1 pointsOpen the PT Activity. Perform the tasks in the activity instructions and then answer the question. Which task has to be performed on Router 1 for it to establish an OSPF adjacency with Router 2?Correct
Incorrect
-
Question 128 of 142
128. Question
1 pointsWhat action takes place when the source MAC address of a frame entering a switch appears in the MAC address table associated with a different port?Correct
Incorrect
-
Question 129 of 142
129. Question
1 pointsRefer to the exhibit. Static NAT is being configured to allow PC 1 access to the web server on the internal network. What two addresses are needed in place of A and B to complete the static NAT configuration? (Choose two.) Correct
Correct
Incorrect
-
Question 130 of 142
130. Question
1 pointsIn computer network communications which data transfer process does the application layer protocol FTP use?Correct
Incorrect
-
Question 131 of 142
131. Question
1 pointsWhat action takes place when a frame entering a switch has a broadcast destination MAC address?Correct
Incorrect
-
Question 132 of 142
132. Question
1 pointsWhich LAN attack involves sending unsolicited ARP replies, with the MAC Address of the threat actor and the IP address of the default gateway, to other hosts on a subnet?Correct
Incorrect
-
Question 133 of 142
133. Question
1 pointsA network engineer is examining the configuration of a router and notices that interface Gi0/0 has been configured with the ip address dhcp command. Which statement describes the IP address condition of this interface?Correct
Incorrect
-
Question 134 of 142
134. Question
1 pointsWhat term describes holding packets in memory until resources become available to transmit them?Correct
Incorrect
-
Question 135 of 142
135. Question
1 pointsWhat defines a two-tier spine-leaf topology?Correct
Incorrect
-
Question 136 of 142
136. Question
1 pointsWhat characteristic completes the following statement? When an IPv6 static route is configured, as a default route, the destination network is …Correct
Incorrect
-
Question 137 of 142
137. Question
1 pointsWhich LAN attack involves a rogue server connected to the network providing false IP configuration parameters to legitimate clients?Correct
Incorrect
-
Question 138 of 142
138. Question
1 pointsWhat term describes a process where a router simply discards any packet that arrives at the end of a queue that has completely used up its packet-holding resources?Correct
Incorrect
-
Question 139 of 142
139. Question
1 pointsWhat term describes adding a value to the packet header, as close to the source as possible, so that the packet matches a defined policy?Correct
Incorrect
-
Question 140 of 142
140. Question
1 pointsWhat action takes place when the source MAC address of a frame entering a switch is in the MAC address table?Correct
Incorrect
-
Question 141 of 142
141. Question
1 pointsWhat action takes place when a frame entering a switch has a unicast destination MAC address that is not in the MAC address table?Correct
Incorrect
-
Question 142 of 142
142. Question
1 pointsWhich LAN attack prevents hosts from obtaining dynamically assigned IP addresses?Correct
Incorrect

Where are the questions from?