Check answers here:
CyberOps Associate (200-201) Certification Practice Exam Answers
Quiz-summary
0 of 95 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
Information
CyberOps Associate (200-201) Certification Practice - Test online
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 95 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- Answered
- Review
-
Question 1 of 95
1. Question
1 pointsMatch the definition to the Microsoft Windows term. (Not all options are used.)Correct
Incorrect
-
Question 2 of 95
2. Question
1 pointsWhat are two motivating factors for nation-state sponsored threat actors? (Choose two.)Correct
Incorrect
-
Question 3 of 95
3. Question
1 pointsMatch the description to the Linux term. (Not all options are used.)Correct
Incorrect
-
Question 4 of 95
4. Question
1 pointsMatch the antimalware approach to the description.Correct
Incorrect
-
Question 5 of 95
5. Question
1 pointsWhich type of data is used by Cisco Cognitive Intelligence to find malicious activity that has bypassed security controls, or entered through unmonitored channels, and is operating inside an enterprise network?Correct
Incorrect
-
Question 6 of 95
6. Question
1 pointsWhich type of evasion technique splits malicious payloads into smaller packets in order to bypass security sensors that do not reassemble the payloads before scanning them?Correct
Incorrect
-
Question 7 of 95
7. Question
1 pointsWhich type of cyber attack is a form of MiTM in which the perpetrator copies IP packets off the network without modifying them?Correct
Incorrect
-
Question 8 of 95
8. Question
1 pointsWhich is an example of social engineering?Correct
Incorrect
-
Question 9 of 95
9. Question
1 pointsWhich component is a pillar of the zero trust security approach that focuses on the secure access of devices, such as servers, printers, and other endpoints, including devices attached to IoT?Correct
Incorrect
-
Question 10 of 95
10. Question
1 pointsA security analyst is reviewing information contained in a Wireshark capture created during an attempted intrusion. The analyst wants to correlate the Wireshark information with the log files from two servers that may have been compromised. What type of information can be used to correlate the events found in these multiple data sets?Correct
Incorrect
-
Question 11 of 95
11. Question
1 pointsA security analyst is investigating a cyber attack that began by compromising one file system through a vulnerability in a custom software application. The attack now appears to be affecting additional file systems under the control of another security authority. Which CVSS v3.0 base exploitability metric score is increased by this attack characteristic?Correct
Incorrect
-
Question 12 of 95
12. Question
1 pointsWhich regular expression would match any string that contains 4 consecutive zeros?Correct
Incorrect
-
Question 13 of 95
13. Question
1 pointsRefer to the exhibit. Which technology generated the event log?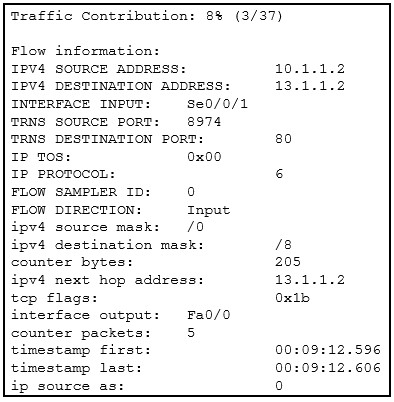 Correct
Correct
Incorrect
-
Question 14 of 95
14. Question
1 pointsRefer to the exhibit. A security specialist is using Wireshark to review a PCAP file generated by tcpdump . When the client initiated a file download request, which source socket pair was used?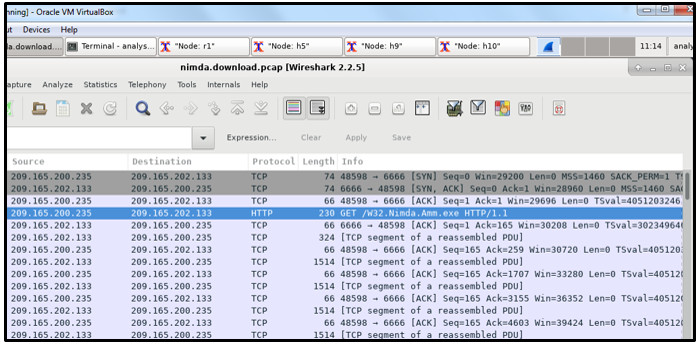 Correct
Correct
Incorrect
-
Question 15 of 95
15. Question
1 pointsMatch the security service with the description.Correct
Incorrect
-
Question 16 of 95
16. Question
1 pointsUsing Tcpdump and Wireshark, a security analyst extracts a downloaded file from a pcap file. The analyst suspects that the file is a virus and wants to know the file type for further examination. Which Linux command can be used to determine the file type?Correct
Incorrect
-
Question 17 of 95
17. Question
1 pointsMatch the IPS alarm with the description.Correct
Incorrect
-
Question 18 of 95
18. Question
1 pointsWhat is a feature of an IPS?Correct
Incorrect
-
Question 19 of 95
19. Question
1 pointsWhich three fields are found in both the TCP and UDP headers? (Choose three.)Correct
Incorrect
-
Question 20 of 95
20. Question
1 pointsWhat will match the regular expression ^83?Correct
Incorrect
-
Question 21 of 95
21. Question
1 pointsWhat is a key difference between the data captured by NetFlow and data captured by Wireshark?Correct
Incorrect
-
Question 22 of 95
22. Question
1 pointsWhich three IPv4 header fields have no equivalent in an IPv6 header? (Choose three.)Correct
Incorrect
-
Question 23 of 95
23. Question
1 pointsWhat classification is used for an alert that correctly identifies that an exploit has occurred?Correct
Incorrect
-
Question 24 of 95
24. Question
1 pointsMatch the NIST incident response life cycle phase with the description.Correct
Incorrect
-
Question 25 of 95
25. Question
1 pointsPlace the seven steps defined in the Cyber Kill Chain in the correct order.Correct
Incorrect
-
Question 26 of 95
26. Question
1 pointsDuring the detection and analysis phase of the NIST incident response process life cycle, which sign category is used to describe that an incident might occur in the future?Correct
Incorrect
-
Question 27 of 95
27. Question
1 pointsAccording to the Cyber Kill Chain model, after a weapon is delivered to a targeted system, what is the next step that a threat actor would take?Correct
Incorrect
-
Question 28 of 95
28. Question
1 pointsA company is applying the NIST.SP800-61 r2 incident handling process to security events. What are two examples of incidents that are in the category of precursor? (Choose two.)Correct
Incorrect
-
Question 29 of 95
29. Question
1 pointsA network administrator is creating a network profile to generate a network baseline. What is included in the critical asset address space element?Correct
Incorrect
-
Question 30 of 95
30. Question
1 pointsWhich NIST-defined incident response stakeholder is responsible for coordinating incident response with other stakeholders and minimizing the damage of an incident?Correct
Incorrect
-
Question 31 of 95
31. Question
1 pointsWhat is defined in the policy element of the NIST incident response plan?Correct
Incorrect
-
Question 32 of 95
32. Question
1 pointsWhat is the responsibility of the human resources department when handing a security incident as defined by NIST?Correct
Incorrect
-
Question 33 of 95
33. Question
1 pointsWhat is the benefit of a defense-in-depth approach?Correct
Incorrect
-
Question 34 of 95
34. Question
1 pointsWhich type of analysis relies on predefined conditions and can analyze applications that only use well-known fixed ports?Correct
Incorrect
-
Question 35 of 95
35. Question
1 pointsWhich type of analysis relies on different methods to establish the likelihood that a security event has happened or will happen?Correct
Incorrect
-
Question 36 of 95
36. Question
1 pointsWhich access control model allows users to control access to data as an owner of that data?Correct
Incorrect
-
Question 37 of 95
37. Question
1 pointsWhat are the three impact metrics contained in the CVSS 3.0 Base Metric Group? (Choose three.)Correct
Incorrect
-
Question 38 of 95
38. Question
1 pointsWhich access control model applies the strictest access control and is often used in military and mission critical applications?Correct
Incorrect
-
Question 39 of 95
39. Question
1 pointsMatch the security concept to the description.Correct
Incorrect
-
Question 40 of 95
40. Question
1 pointsWhat is the principle behind the nondiscretionary access control model?Correct
Incorrect
-
Question 41 of 95
41. Question
1 pointsMatch the information security component with the description.Correct
Incorrect
-
Question 42 of 95
42. Question
1 pointsWhich attack is integrated with the lowest levels of the operating system of a host and attempts to completely hide the activities of the threat actor on the local system?Correct
Incorrect
-
Question 43 of 95
43. Question
1 pointsWhich tool captures full data packets with a command-line interface only?Correct
Incorrect
-
Question 44 of 95
44. Question
1 pointsTo which category of security attacks does man-in-the-middle belong?Correct
Incorrect
-
Question 45 of 95
45. Question
1 pointsWhat is an example of a local exploit?Correct
Incorrect
-
Question 46 of 95
46. Question
1 pointsWhich Cisco appliance can be used to filter network traffic contents to report and deny traffic based on the web server reputation?Correct
Incorrect
-
Question 47 of 95
47. Question
1 pointsWhich evasion method describes the situation that after gaining access to the administrator password on a compromised host, a threat actor is attempting to login to another host using the same credentials?Correct
Incorrect
-
Question 48 of 95
48. Question
1 pointsWhat are two examples of DoS attacks? (Choose two.)Correct
Incorrect
-
Question 49 of 95
49. Question
1 pointsWhich type of attack is carried out by threat actors against a network to determine which IP addresses, protocols, and ports are allowed by ACLs?Correct
Incorrect
-
Question 50 of 95
50. Question
1 pointsRefer to the exhibit. A security analyst is reviewing an alert message generated by Snort. What does the number 2100498 in the message indicate?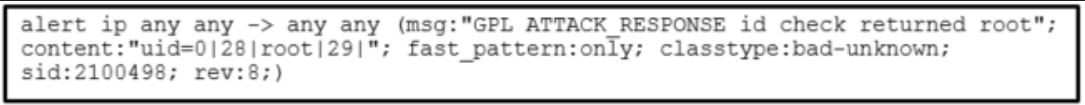 Correct
Correct
Incorrect
-
Question 51 of 95
51. Question
1 pointsWhich two attacks target web servers through exploiting possible vulnerabilities of input functions used by an application? (Choose two.)Correct
Incorrect
-
Question 52 of 95
52. Question
1 pointsWhich security function is provided by encryption algorithms?Correct
Incorrect
-
Question 53 of 95
53. Question
1 pointsMatch the Windows term to the description.Correct
Incorrect
-
Question 54 of 95
54. Question
1 pointsWhich security endpoint setting would be used by a security analyst to determine if a computer has been configured to prevent a particular application from running?Correct
Incorrect
-
Question 55 of 95
55. Question
1 pointsRefer to the exhibit. Which technology would contain information similar to the data shown for infrastructure devices within a company?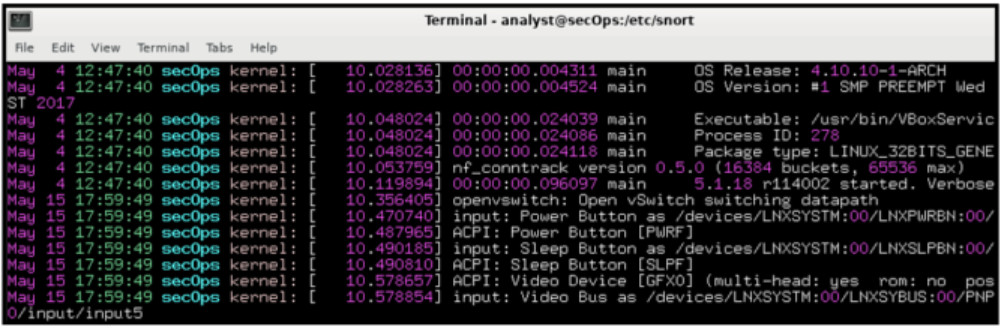 Correct
Correct
Incorrect
-
Question 56 of 95
56. Question
1 pointsAt the request of investors, a company is proceeding with cyber attribution with a particular attack that was conducted from an external source. Which security term is used to describe the person or device responsible for the attack?Correct
Incorrect
-
Question 57 of 95
57. Question
1 pointsWhich Windows application is commonly used by a cybersecurity analyst to view Microsoft IIS access logs?Correct
Incorrect
-
Question 58 of 95
58. Question
1 pointsWhich two algorithms use a hashing function to ensure message integrity? (Choose two.)Correct
Incorrect
-
Question 59 of 95
59. Question
1 pointsWhich type of evidence cannot prove an IT security fact on its own?Correct
Incorrect
-
Question 60 of 95
60. Question
1 pointsRefer to the exhibit. Approximately what percentage of the physical memory is still available on this Windows system?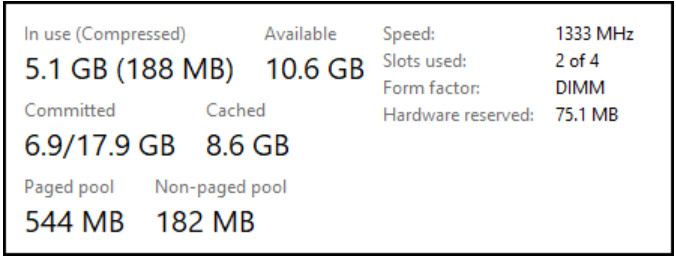 Correct
Correct
Incorrect
-
Question 61 of 95
61. Question
1 pointsWhich Windows tool can be used by a cybersecurity administrator to secure stand-alone computers that are not part of an active directory domain?Correct
Incorrect
-
Question 62 of 95
62. Question
1 pointsWhat are three benefits of using symbolic links over hard links in Linux? (Choose three.)Correct
Incorrect
-
Question 63 of 95
63. Question
1 pointsWhen attempting to improve system performance for Linux computers with a limited amount of memory, why is increasing the size of the swap file system not considered the best solution?Correct
Incorrect
-
Question 64 of 95
64. Question
1 pointsRefer to the exhibit. A security analyst is reviewing the logs of an Apache web server. Which action should the analyst take based on the output shown?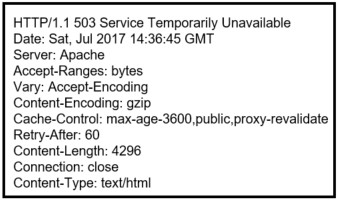 Correct
Correct
Incorrect
-
Question 65 of 95
65. Question
1 pointsA security professional is making recommendations to a company for enhancing endpoint security. Which security endpoint technology would be recommended as an agent-based system to protect hosts against malware?Correct
Incorrect
-
Question 66 of 95
66. Question
1 pointsWhich technique could be used by security personnel to analyze a suspicious file in a safe environment?Correct
Incorrect
-
Question 67 of 95
67. Question
1 pointsA cybersecurity analyst has been called to a crime scene that contains several technology items including a computer. Which technique will be used so that the information found on the computer can be used in court?Correct
Incorrect
-
Question 68 of 95
68. Question
1 pointsWhich SOC technology automates security responses by using predefined playbooks which require a minimum amount of human intervention?Correct
Incorrect
-
Question 69 of 95
69. Question
1 pointsWhat is the first line of defense when an organization is using a defense-in-depth approach to network security?Correct
Incorrect
-
Question 70 of 95
70. Question
1 pointsWhich access control model assigns security privileges based on the position, responsibilities, or job classification of an individual or group within an organization?Correct
Incorrect
-
Question 71 of 95
71. Question
1 pointsWhich metric in the CVSS Base Metric Group is used with an attack vector?Correct
Incorrect
-
Question 72 of 95
72. Question
1 pointsWhich field in the IPv6 header points to optional network layer information that is carried in the IPv6 packet?Correct
Incorrect
-
Question 73 of 95
73. Question
1 pointsWhich data security component is provided by hashing algorithms?Correct
Incorrect
-
Question 74 of 95
74. Question
1 pointsWhich attack surface, defined by the SANS Institute, is delivered through the exploitation of vulnerabilities in web, cloud, or host-based applications?Correct
Incorrect
-
Question 75 of 95
75. Question
1 pointsWhat is the main goal of using different evasion techniques by threat actors?Correct
Incorrect
-
Question 76 of 95
76. Question
1 pointsHow can NAT/PAT complicate network security monitoring if NetFlow is being used?Correct
Incorrect
-
Question 77 of 95
77. Question
1 pointsWhich statement describes the function provided by the Tor network?Correct
Incorrect
-
Question 78 of 95
78. Question
1 pointsWhen establishing a server profile for an organization, which element describes the type of service that an application is allowed to run on the server?Correct
Incorrect
-
Question 79 of 95
79. Question
1 pointsWhat will a threat actor do to create a back door on a compromised target according to the Cyber Kill Chain model?Correct
Incorrect
-
Question 80 of 95
80. Question
1 pointsWhich three things will a threat actor do to prepare a DDoS attack against a target system on the Internet? (Choose three.)Correct
Incorrect
-
Question 81 of 95
81. Question
1 pointsWhat is specified in the plan element of the NIST incident response plan?Correct
Incorrect
-
Question 82 of 95
82. Question
1 pointsWhat is the responsibility of the IT support group when handing an incident as defined by NIST?Correct
Incorrect
-
Question 83 of 95
83. Question
1 pointsWhat is an example of privilege escalation attack?Correct
Incorrect
-
Question 84 of 95
84. Question
1 pointsA threat hunter is concerned about a significant increase in TCP traffic sourced from port 53. It is suspected that malicious file transfer traffic is being tunneled out using the TCP DNS port. Which deep packet inspection tool can detect the type of application originating the suspicious traffic?Correct
Incorrect
-
Question 85 of 95
85. Question
1 pointsWhich type of evaluation includes the assessment of the likelihood of an attack, the type of threat actor likely to perpetrate such an attack, and what the consequences could be to the organization if the exploit is successful?Correct
Incorrect
-
Question 86 of 95
86. Question
1 pointsWhen establishing a network profile for an organization, which element describes the time between the establishment of a data flow and its termination?Correct
Incorrect
-
Question 87 of 95
87. Question
1 pointsWhich term describes a threat actor who has advanced skills and pursues a social agenda?Correct
Incorrect
-
Question 88 of 95
88. Question
1 pointsRefer to the exhibit. A security specialist is checking if files in the directory contain ADS data. Which switch should be used to show that a file has ADS attached?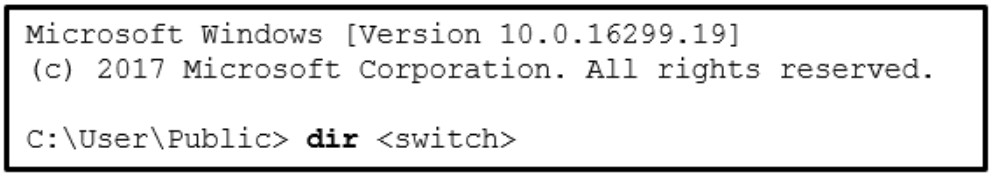 Correct
Correct
Incorrect
-
Question 89 of 95
89. Question
1 pointsThe SOC manager is reviewing the metrics for the previous calendar quarter and discovers that the MTTD for a breach of password security perpetrated through the Internet was forty days. What does the MTTD metric represent within the SOC?Correct
Incorrect
-
Question 90 of 95
90. Question
1 pointsA cybersecurity analyst is performing a CVSS assessment on an attack where a web link was sent to several employees. Once clicked, an internal attack was launched. Which CVSS Base Metric Group Exploitability metric is used to document that the user had to click on the link in order for the attack to occur?Correct
Incorrect
-
Question 91 of 95
91. Question
1 pointsWhen a server profile for an organization is being established, which element describes the TCP and UDP daemons and ports that are allowed to be open on the server?Correct
Incorrect
-
Question 92 of 95
92. Question
1 pointsWhich two actions should be taken during the preparation phase of the incident response life cycle defined by NIST? (Choose two.)Correct
Incorrect
-
Question 93 of 95
93. Question
1 pointsMatch the NIST incident response stakeholder with the role.Correct
Incorrect
-
Question 94 of 95
94. Question
1 pointsMatch the file system term used in Linux to the function.Correct
Incorrect
-
Question 95 of 95
95. Question
1 pointsWhich information security component is compromised in a DDoS attack?Correct
Incorrect
