CyberOps Associate (Version 1.0) – CyberOps Associate (200-201) Certification Practice Exam
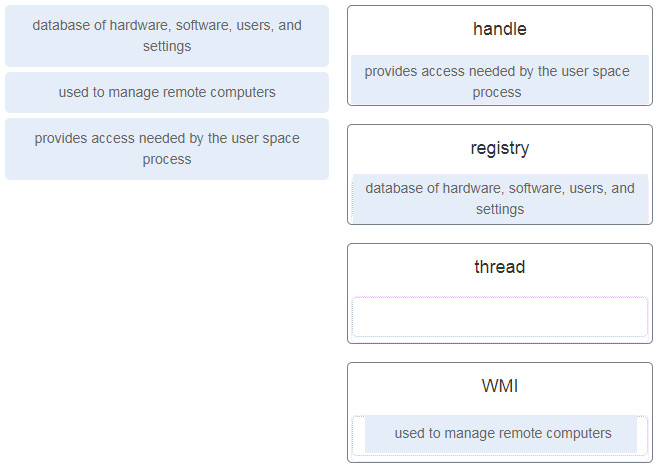
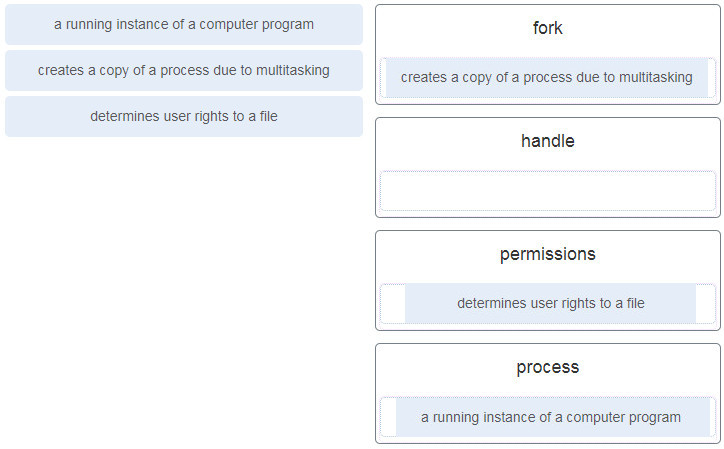
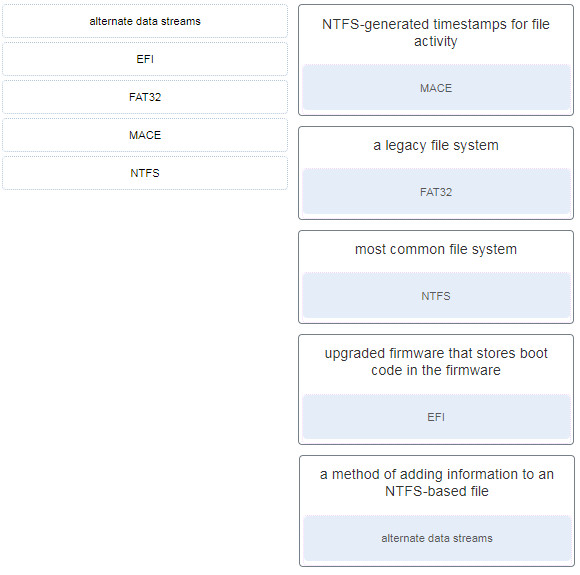
1. Match the definition to the Microsoft Windows term. (Not all options are used.)
Case 2
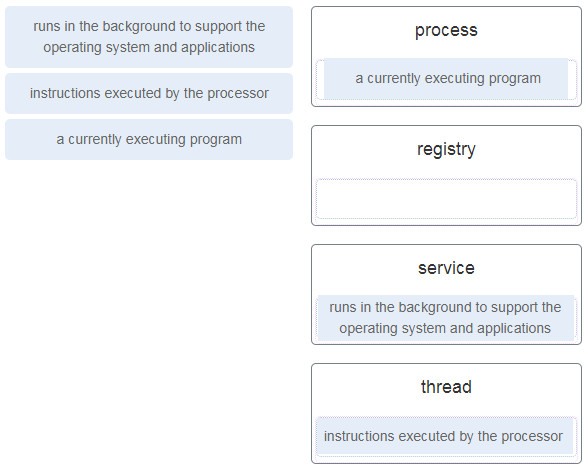
Match the definition to the Microsoft Windows term. (Not all options are used.)
2. What are two motivating factors for nation-state sponsored threat actors? (Choose two.)
- industrial espionage
- showing off their hacking skill
- disruption of trade or infrastructure
- social or personal causes
- financial gain
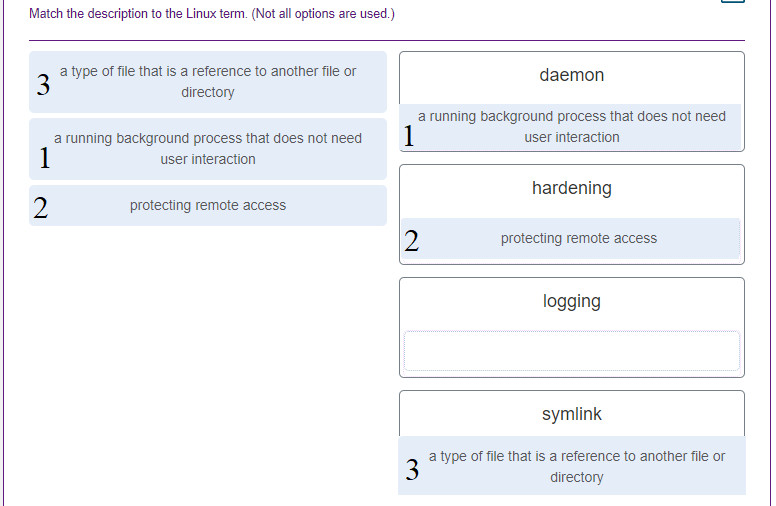
3. Match the description to the Linux term. (Not all options are used.)
Other case
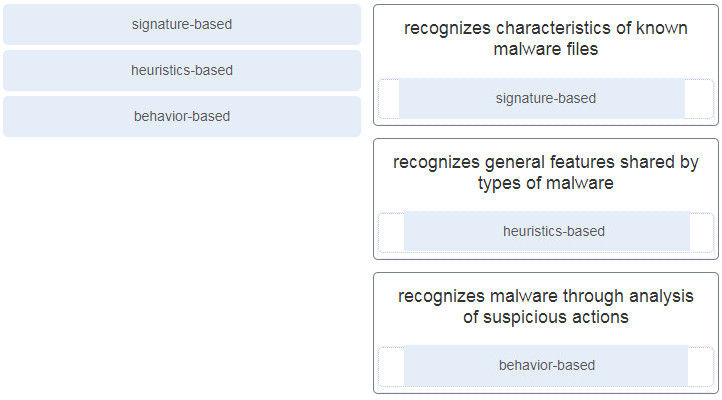
4. Match the antimalware approach to the description.
5. Which type of data is used by Cisco Cognitive Intelligence to find malicious activity that has bypassed security controls, or entered through unmonitored channels, and is operating inside an enterprise network?
- statistical
- session
- alert
- transaction
6. Which type of evasion technique splits malicious payloads into smaller packets in order to bypass security sensors that do not reassemble the payloads before scanning them?
- pivoting
- traffic fragmentation
- protocol-level misinterpretation
- traffic insertion
7. Which type of cyber attack is a form of MiTM in which the perpetrator copies IP packets off the network without modifying them?
- compromised key
- eavesdropping
- denial-of-service
- IP spoofing
8. Which is an example of social engineering?
- an anonymous programmer directing a DDoS attack on a data center
- an unidentified person claiming to be a technician collecting user information from employees
- a computer displaying unauthorized pop-ups and adware
- the infection of a computer by a virus carried by a Trojan
9. Which component is a pillar of the zero trust security approach that focuses on the secure access of devices, such as servers, printers, and other endpoints, including devices attached to IoT?
- workflows
- workloads
- workplace
- workforce
10. A security analyst is reviewing information contained in a Wireshark capture created during an attempted intrusion. The analyst wants to correlate the Wireshark information with the log files from two servers that may have been compromised. What type of information can be used to correlate the events found in these multiple data sets?
- ISP geolocation data
- IP five-tuples
- logged-in user account
- ownership metadata
11. A security analyst is investigating a cyber attack that began by compromising one file system through a vulnerability in a custom software application. The attack now appears to be affecting additional file systems under the control of another security authority. Which CVSS v3.0 base exploitability metric score is increased by this attack characteristic?
- privileges required
- scope
- attack complexity
- user interaction
12. Which regular expression would match any string that contains 4 consecutive zeros?
- {0-4}
- [0-4]
- 0{4}
- ^0000
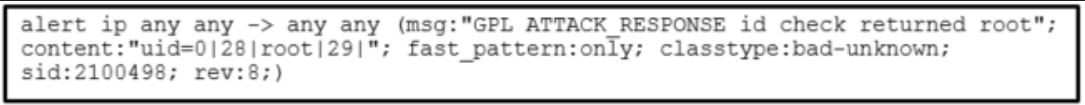
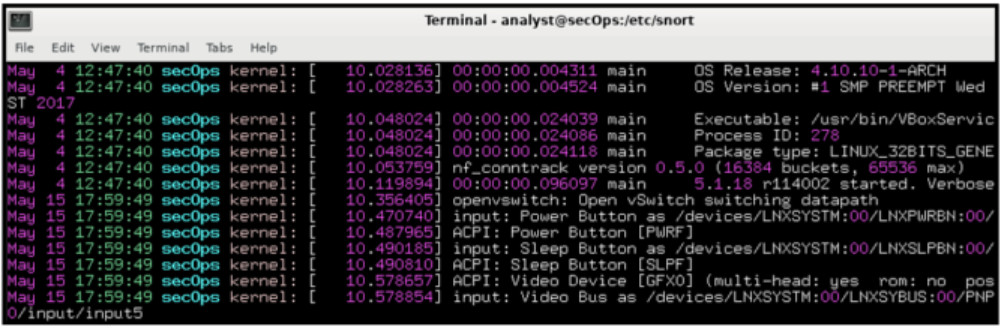
13. Refer to the exhibit. Which technology generated the event log?
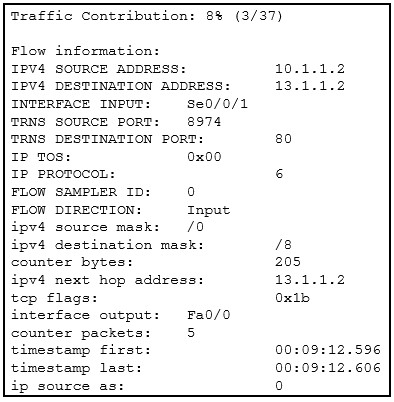
- Wireshark
- Netflow
- web proxy
- syslog
14. Refer to the exhibit. A security specialist is using Wireshark to review a PCAP file generated by tcpdump . When the client initiated a file download request, which source socket pair was used?
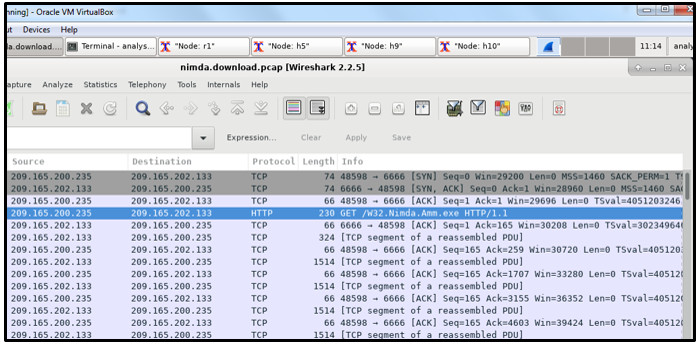
- 209.165.202.133:48598
- 209.165.202.133:6666
- 209.165.200.235:6666
- 209.165.200.235:48598
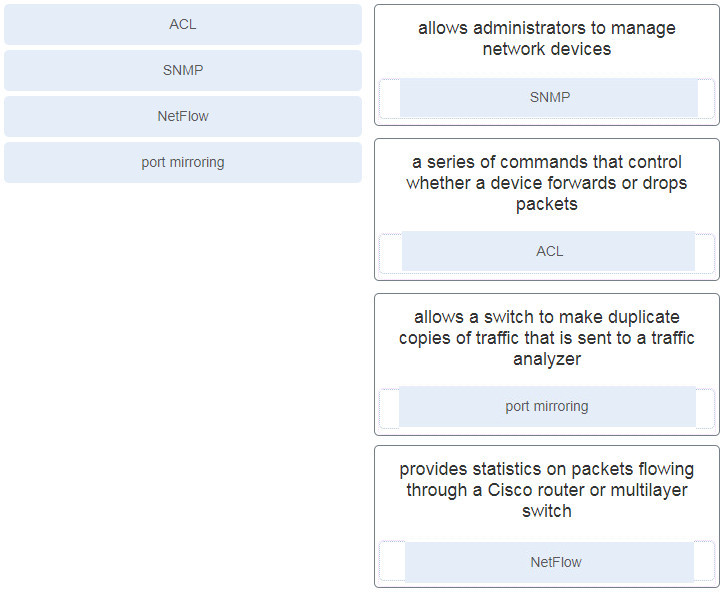
15. Match the security service with the description.
16. Using Tcpdump and Wireshark, a security analyst extracts a downloaded file from a pcap file. The analyst suspects that the file is a virus and wants to know the file type for further examination. Which Linux command can be used to determine the file type?
- file
- tail
- nano
- ls -l
17. Match the IPS alarm with the description.
CyberOps Associate (Version 1.0) – CyberOps Associate (200-201) Certification Practice Exam
18. What is a feature of an IPS?
- It can stop malicious packets.
- It is deployed in offline mode.
- It has no impact on latency.
- It is primarily focused on identifying possible incidents.
19. Which three fields are found in both the TCP and UDP headers? (Choose three.)
- window
- checksum
- options
- sequence number
- destination port
- source port
20. What will match the regular expression ^83?
- any string that includes 83
- any string that begins with 83
- any string with values greater than 83
- any string that ends with 83
21. What is a key difference between the data captured by NetFlow and data captured by Wireshark?
- NetFlow provides transaction data whereas Wireshark provides session data.
- NetFlow data is analyzed by tcpdump whereas Wireshark data is analyzed by nfdump.
- NetFlow collects metadata from a network flow whereas Wireshark captures full data packets.
- NetFlow data shows network flow contents whereas Wireshark data shows network flow statistics.
22. Which three IPv4 header fields have no equivalent in an IPv6 header? (Choose three.)
- flag
- identification
- TTL
- fragment offset
- version
- protocol
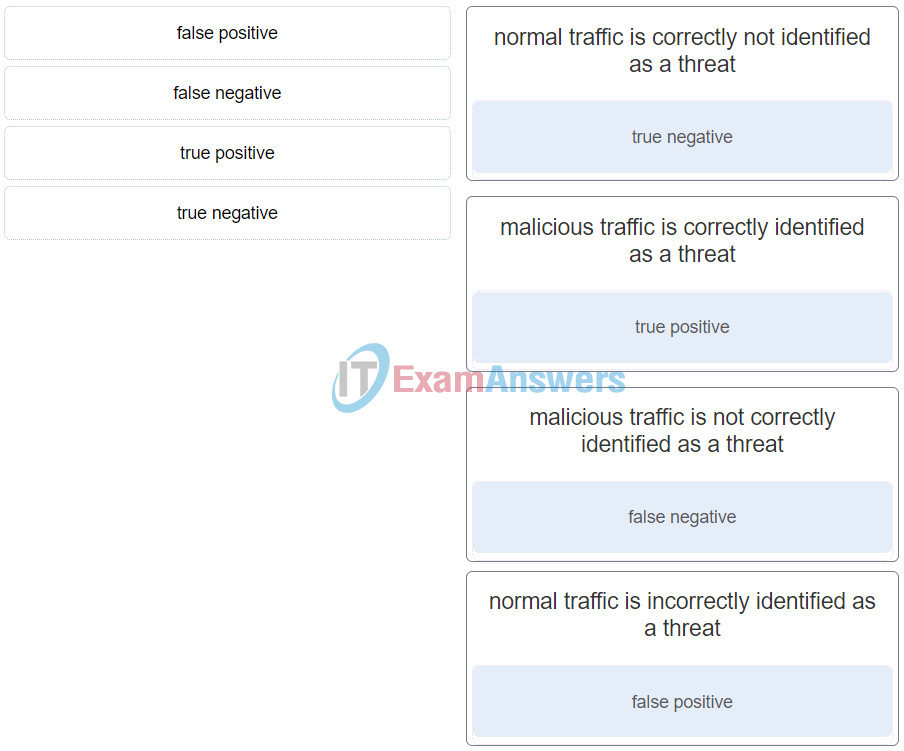
23. What classification is used for an alert that correctly identifies that an exploit has occurred?
- false negative
- false positive
- true positive
- true negative
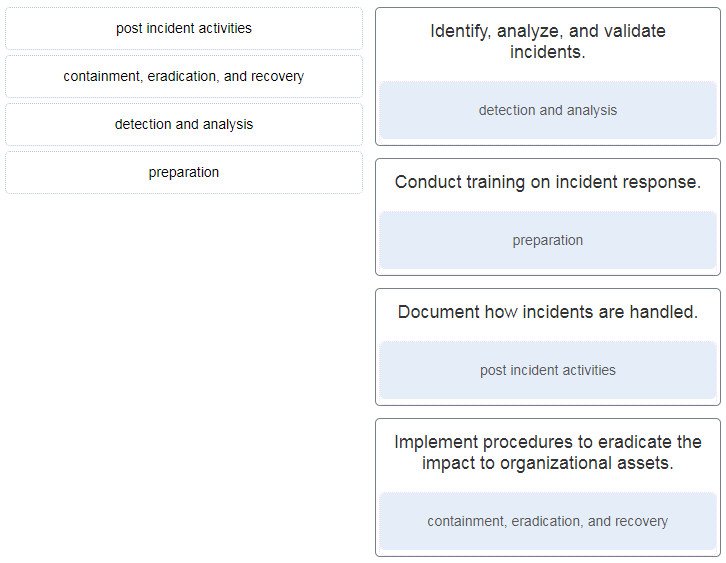
24. Match the NIST incident response life cycle phase with the description.
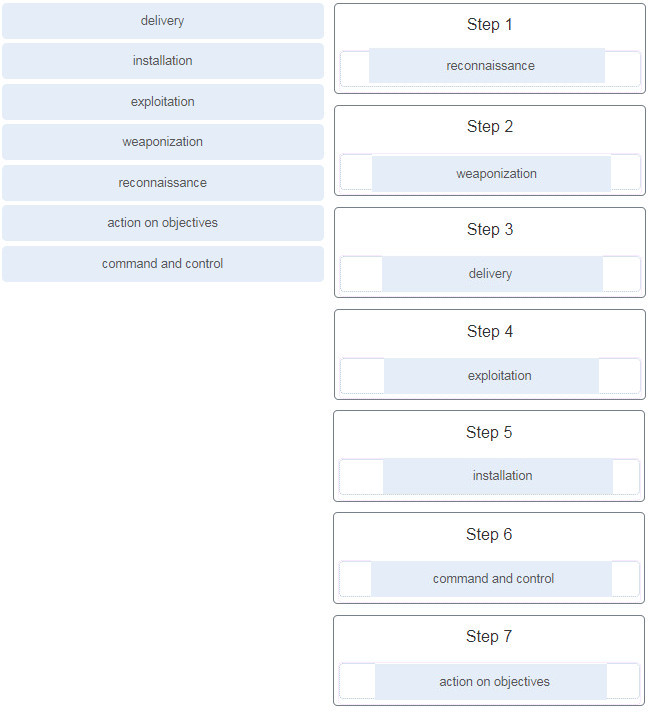
25. Place the seven steps defined in the Cyber Kill Chain in the correct order.
26. During the detection and analysis phase of the NIST incident response process life cycle, which sign category is used to describe that an incident might occur in the future?
- attrition
- impersonation
- precursor
- indicator
27. According to the Cyber Kill Chain model, after a weapon is delivered to a targeted system, what is the next step that a threat actor would take?
- action on objectives
- exploitation
- weaponization
- installation
28. A company is applying the NIST.SP800-61 r2 incident handling process to security events. What are two examples of incidents that are in the category of precursor? (Choose two.)
- multiple failed logins from an unknown source
- log entries that show a response to a port scan
- an IDS alert message being sent
- a newly-discovered vulnerability in Apache web servers
- a host that has been verified as infected with malware
29. A network administrator is creating a network profile to generate a network baseline. What is included in the critical asset address space element?
- the time between the establishment of a data flow and its termination
- the TCP and UDP daemons and ports that are allowed to be open on the server
- the IP addresses or the logical location of essential systems or data
- the list of TCP or UDP processes that are available to accept data
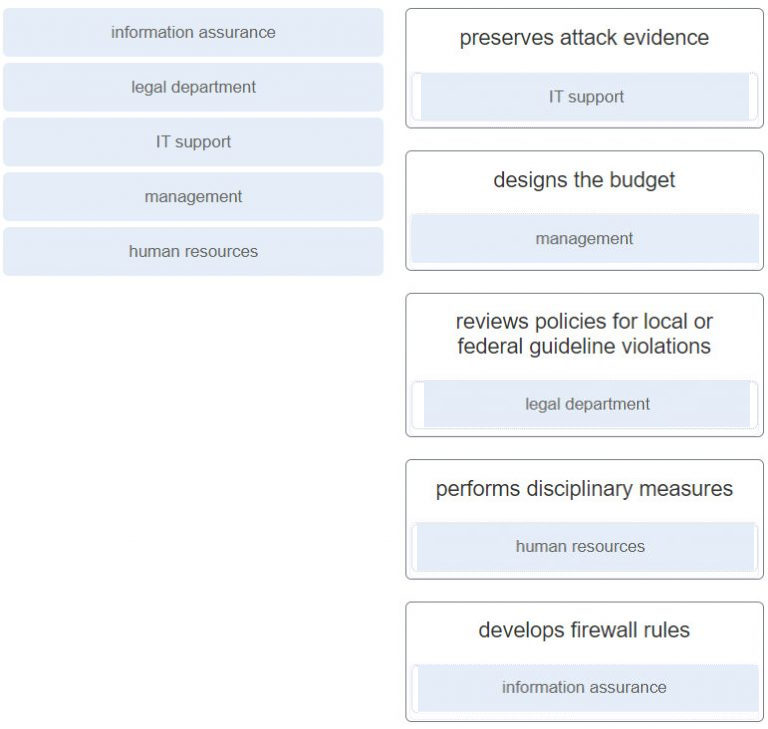
30. Which NIST-defined incident response stakeholder is responsible for coordinating incident response with other stakeholders and minimizing the damage of an incident?
- human resources
- IT support
- the legal department
- management
31. What is defined in the policy element of the NIST incident response plan?
- how to handle incidents based on the mission and functions of an organization
- a roadmap for updating the incident response capability
- the metrics used for measuring incident response capability in an organization
- how the incident response team of an organization will communicate with organization stakeholders
32. What is the responsibility of the human resources department when handing a security incident as defined by NIST?
- Review the incident policies, plans, and procedures for local or federal guideline violations.
- Perform disciplinary actions if an incident is caused by an employee.
- Coordinate the incident response with other stakeholders and minimize the damage of an incident.
- Perform actions to minimize the effectiveness of the attack and preserve evidence.
33. What is the benefit of a defense-in-depth approach?
- All network vulnerabilities are mitigated.
- The need for firewalls is eliminated.
- Only a single layer of security at the network core is required.
- The effectiveness of other security measures is not impacted when a security mechanism fails.
34. Which type of analysis relies on predefined conditions and can analyze applications that only use well-known fixed ports?
- statistical
- deterministic
- log
- probabilistic
35. Which type of analysis relies on different methods to establish the likelihood that a security event has happened or will happen?
- deterministic
- statistical
- log
- probabilistic
36. Which access control model allows users to control access to data as an owner of that data?
- mandatory access control
- nondiscretionary access control
- discretionary access control
- attribute-based access control
37. What are the three impact metrics contained in the CVSS 3.0 Base Metric Group? (Choose three.)
- confidentiality
- remediation level
- integrity
- attack vector
- exploit
- availability
38. Which access control model applies the strictest access control and is often used in military and mission critical applications?
- discretionary
- mandatory
- nondiscretionary
- attribute-based
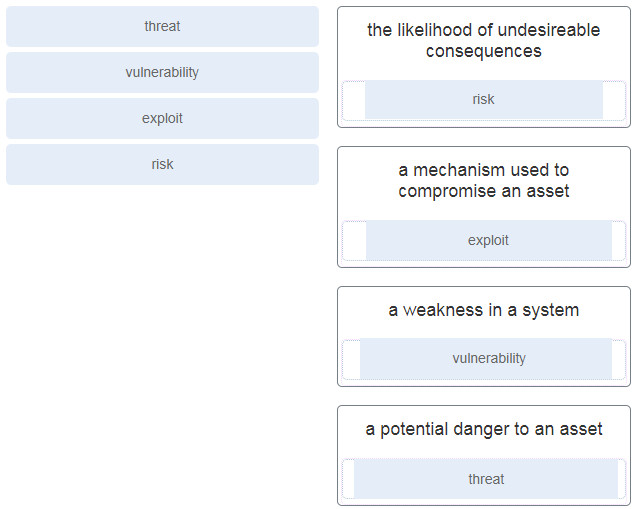
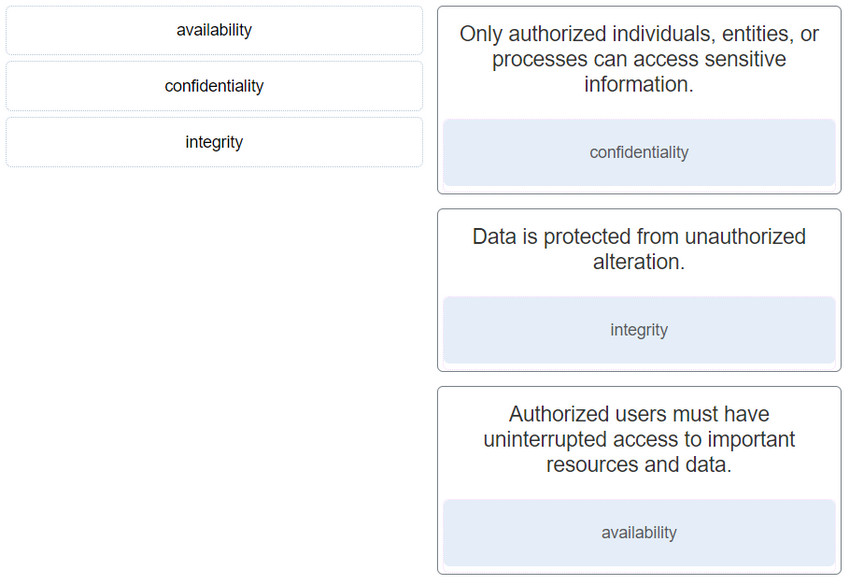
39. Match the security concept to the description.
40. What is the principle behind the nondiscretionary access control model?
- It applies the strictest access control possible.
- It allows access decisions to be based on roles and responsibilities of a user within the organization.
- It allows users to control access to their data as owners of that data.
- It allows access based on attributes of the object be to accessed.
41. Match the information security component with the description.
42. Which attack is integrated with the lowest levels of the operating system of a host and attempts to completely hide the activities of the threat actor on the local system?
- rootkit
- traffic insertion
- traffic substitution
- encryption and tunneling
43. Which tool captures full data packets with a command-line interface only?
- nfdump
- NBAR2
- tcpdump
- Wireshark
44. To which category of security attacks does man-in-the-middle belong?
- DoS
- access
- reconnaissance
- social engineering
45. What is an example of a local exploit?
- Port scanning is used to determine if the Telnet service is running on a remote server.
- A threat actor performs a brute force attack on an enterprise edge router to gain illegal access.
- A buffer overflow attack is launched against an online shopping website and causes the server crash.
- A threat actor tries to gain the user password of a remote host by using a keyboard capture software installed on it by a Trojan.
46. Which Cisco appliance can be used to filter network traffic contents to report and deny traffic based on the web server reputation?
- WSA
- AVC
- ASA
- ESA
47. Which evasion method describes the situation that after gaining access to the administrator password on a compromised host, a threat actor is attempting to login to another host using the same credentials?
- pivoting
- traffic substitution
- resource exhaustion
- protocol-level misinterpretation
48. What are two examples of DoS attacks? (Choose two.)
- port scanning
- SQL injection
- ping of death
- phishing
- buffer overflow
49. Which type of attack is carried out by threat actors against a network to determine which IP addresses, protocols, and ports are allowed by ACLs?
- social engineering
- denial of service
- phishing
- reconnaissance
50. Refer to the exhibit. A security analyst is reviewing an alert message generated by Snort. What does the number 2100498 in the message indicate?
- the id of the user that triggers the alert
- the message length in bits
- the Snort rule that is triggered
- the session number of the message
51. Which two attacks target web servers through exploiting possible vulnerabilities of input functions used by an application? (Choose two.)
- SQL injection
- port scanning
- port redirection
- trust exploitation
- cross-site scripting
52. Which security function is provided by encryption algorithms?
- key management
- authorization
- integrity
- confidentiality
53. Match the Windows term to the description.
54. Which security endpoint setting would be used by a security analyst to determine if a computer has been configured to prevent a particular application from running?
- services
- block listing
- baselining
- Allow listing
55. Refer to the exhibit. Which technology would contain information similar to the data shown for infrastructure devices within a company?
- Apache server
- firewall
- HIDS
- syslog server
56. At the request of investors, a company is proceeding with cyber attribution with a particular attack that was conducted from an external source. Which security term is used to describe the person or device responsible for the attack?
- threat actor
- fragmenter
- tunneler
- skeleton
57. Which Windows application is commonly used by a cybersecurity analyst to view Microsoft IIS access logs?
- Event Viewer
- Notepad
- SIEM
- Word
58. Which two algorithms use a hashing function to ensure message integrity? (Choose two.)
- SEAL
- AES
- 3DES
- MD5
- SHA
59. Which type of evidence cannot prove an IT security fact on its own?
- best
- corroborative
- indirect
- hearsay
60. Refer to the exhibit. Approximately what percentage of the physical memory is still available on this Windows system?
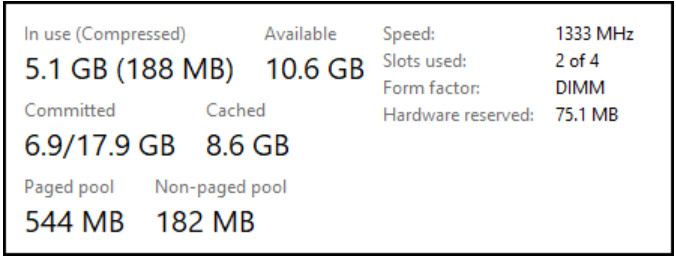
- 32%
- 53%
- 68%
- 90%
61. Which Windows tool can be used by a cybersecurity administrator to secure stand-alone computers that are not part of an active directory domain?
- PowerShell
- Windows Defender
- Local Security Policy
- Windows Firewall
62. What are three benefits of using symbolic links over hard links in Linux? (Choose three.)
- They can show the location of the original file.
- Symbolic links can be exported.
- They can be compressed.
- They can be encrypted.
- They can link to a directory.
- They can link to a file in a different file system.
63. When attempting to improve system performance for Linux computers with a limited amount of memory, why is increasing the size of the swap file system not considered the best solution?
- A swap file system uses hard disk space to store inactive RAM content.
- A swap file system cannot be mounted on an MBR partition.
- A swap file system only supports the ex2 file system.
- A swap file system does not have a specific file system.
64. Refer to the exhibit. A security analyst is reviewing the logs of an Apache web server. Which action should the analyst take based on the output shown?
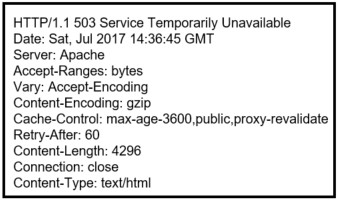
- Notify the appropriate security administration for the country.
- Restart the server.
- Notify the server administrator.
- Ignore the message.
65. A security professional is making recommendations to a company for enhancing endpoint security. Which security endpoint technology would be recommended as an agent-based system to protect hosts against malware?
- IPS
- HIDS
- baselining
- blacklisting
66. Which technique could be used by security personnel to analyze a suspicious file in a safe environment?
- whitelisting
- baselining
- sandboxing
- blacklisting
67. A cybersecurity analyst has been called to a crime scene that contains several technology items including a computer. Which technique will be used so that the information found on the computer can be used in court?
- rootkit
- log collection
- Tor
- unaltered disk image
68. Which SOC technology automates security responses by using predefined playbooks which require a minimum amount of human intervention?
- SOAR
- Wireshark
- NetFlow
- SIEM
- syslog
69. What is the first line of defense when an organization is using a defense-in-depth approach to network security?
- proxy server
- firewall
- IPS
- edge router
70. Which access control model assigns security privileges based on the position, responsibilities, or job classification of an individual or group within an organization?
- rule-based
- role-based
- discretionary
- mandatory
71. Which metric in the CVSS Base Metric Group is used with an attack vector?
- the presence or absence of the requirement for user interaction in order for an exploit to be successful
- the number of components, software, hardware, or networks, that are beyond the control of the attacker and that must be present in order for a vulnerability to be successfully exploited
- the determination whether the initial authority changes to a second authority during the exploit
- the proximity of the threat actor to the vulnerability
72. Which field in the IPv6 header points to optional network layer information that is carried in the IPv6 packet?
- traffic class
- flow label
- next header
- version
73. Which data security component is provided by hashing algorithms?
- integrity
- confidentiality
- key exchange
- authentication
74. Which attack surface, defined by the SANS Institute, is delivered through the exploitation of vulnerabilities in web, cloud, or host-based applications?
- human
- network
- host
- software
75. What is the main goal of using different evasion techniques by threat actors?
- to launch DDoS attacks on targets
- to identify vulnerabilities of target systems
- to prevent detection by network and host defenses
- to gain the trust of a corporate employee in an effort to obtain credentials
76. How can NAT/PAT complicate network security monitoring if NetFlow is being used?
- It disguises the application initiated by a user by manipulating port numbers.
- It changes the source and destination MAC addresses.
- It conceals the contents of a packet by encrypting the data payload.
- It hides internal IP addresses by allowing them to share one or a few outside IP addresses.
77. Which statement describes the function provided by the Tor network?
- It conceals packet contents by establishing end-to-end tunnels.
- It distributes user packets through load balancing.
- It allows users to browse the Internet anonymously.
- It manipulates packets by mapping IP addresses between two networks.
78. When establishing a server profile for an organization, which element describes the type of service that an application is allowed to run on the server?
- user account
- listening port
- service account
- software environment
79. What will a threat actor do to create a back door on a compromised target according to the Cyber Kill Chain model?
- Add services and autorun keys.
- Collect and exfiltrate data.
- Open a two-way communications channel to the CnC infrastructure.
- Obtain an automated tool to deliver the malware payload.
80. Which three things will a threat actor do to prepare a DDoS attack against a target system on the Internet? (Choose three.)
- Install a black door on the target system.
- Obtain an automated tool to deliver the malware payload.
- Establish two-way communications channels to the CnC infrastructure with zombies.
- Collect and exfiltrate data.
- Compromise many hosts on the Internet.
- Install attack software on zombies.
81. What is specified in the plan element of the NIST incident response plan?
- organizational structure and the definition of roles, responsibilities, and levels of authority
- metrics for measuring the incident response capability and effectiveness
- priority and severity ratings of incidents
- incident handling based on the mission of the organization
82. What is the responsibility of the IT support group when handing an incident as defined by NIST?
- coordinates the incident response with other stakeholders and minimizes the damage of an incident
- performs disciplinary measures if an incident is caused by an employee
- performs actions to minimize the effectiveness of the attack and preserve evidence
- reviews the incident policies, plans, and procedures for local or federal guideline violations
83. What is an example of privilege escalation attack?
- A DDoS attack is launched against a government server and causes the server to crash.
- A port scanning attack finds that the FTP service is running on a server that allows anonymous access.
- A threat actor performs an access attack and gains the administrator password.
- A threat actor sends an email to an IT manager to request the root access.
84. A threat hunter is concerned about a significant increase in TCP traffic sourced from port 53. It is suspected that malicious file transfer traffic is being tunneled out using the TCP DNS port. Which deep packet inspection tool can detect the type of application originating the suspicious traffic?
- syslog analyzer
- NBAR2
- NetFlow
- IDS/IPS
- Wireshark
85. Which type of evaluation includes the assessment of the likelihood of an attack, the type of threat actor likely to perpetrate such an attack, and what the consequences could be to the organization if the exploit is successful?
- penetration testing
- risk analysis
- vulnerability identification
- server profiling
86. When establishing a network profile for an organization, which element describes the time between the establishment of a data flow and its termination?
- session duration
- total throughput
- routing protocol convergence
- bandwidth of the Internet connection
87. Which term describes a threat actor who has advanced skills and pursues a social agenda?
- organized crime
- script kiddie
- corporate/industrial spies
- hacktivist
88. Refer to the exhibit. A security specialist is checking if files in the directory contain ADS data. Which switch should be used to show that a file has ADS attached?
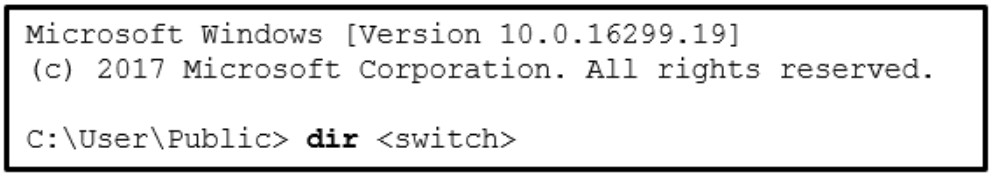
- /a
- /r
- /d
- /s
89. The SOC manager is reviewing the metrics for the previous calendar quarter and discovers that the MTTD for a breach of password security perpetrated through the Internet was forty days. What does the MTTD metric represent within the SOC?
- window of time required to stop the spread of malware in the network
- the average time that it takes to identify valid security incidents that have occurred
- the time required to stop the incident from causing further damage to systems or data
- the average time that it takes to stop and remediate a security incident
90. A cybersecurity analyst is performing a CVSS assessment on an attack where a web link was sent to several employees. Once clicked, an internal attack was launched. Which CVSS Base Metric Group Exploitability metric is used to document that the user had to click on the link in order for the attack to occur?
- scope
- integrity requirement
- availability requirement
- user interaction
91. When a server profile for an organization is being established, which element describes the TCP and UDP daemons and ports that are allowed to be open on the server?
- critical asset address space
- service accounts
- software environment
- listening ports
92. Which two actions should be taken during the preparation phase of the incident response life cycle defined by NIST? (Choose two.)
- Fully analyze the incident.
- Meet with all involved parties to discuss the incident that took place.
- Detect all the incidents that occurred.
- Acquire and deploy the tools that are needed to investigate incidents.
- Create and train the CSIRT
93. Match the NIST incident response stakeholder with the role.
94. Match the file system term used in Linux to the function.
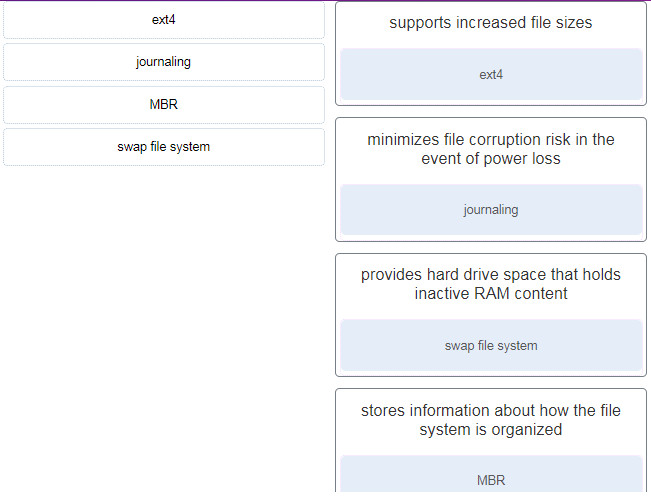
- supports increased file sizes –> ext4
- minimizes file corruption risk in the event of power loss –> journaling
- provides hard drive space that holds inactive RAM content –> swap file system
- stores information about how the file system is organized –> MBR
95. Which information security component is compromised in a DDoS attack?
- accountability
- confidentiality
- integrity
- availability

None of this questions has come in my exams. None. The exam questions are more practical based.
i think 50% of the question listed here did not came out during the exam
thanks
Which information security component is compromised in a DDoS attack?
availability
Match the description to the Linux term. (Not all options are used.)
Added, thanks for your sharing!!
it’s good enough to pass. Make yourself aware of NMAP commands, wireshark filters and cuckoo sandbox!
Example: submit a local binary to be run on virtual machine cuckoo1:
is there a dump for the certification exam
Is this a valid dump for 200-201 exam?
By any chance, could you please confirm?
Refer to the exhibit. A security specialist is using Wireshark to review a PCAP file generated by tcpdump . When the client initiated a file download request, which source socket pair was used?
Thanks for sharing!
Match the file system term used in Linux to the function.
OBS: I dont know if my anwer is 100% correct
It is. It’s deadly obvious.
Hi Admin! Q84 correct answer is NBAR2, see explanation! Sorry;)