Check answers here:
CyberOps Associate 1.0 Practice Final Exam (Answers)
Quiz-summary
0 of 70 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
Information
CyberOps Associate 1.0 Practice Final - Test online
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 70 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- Answered
- Review
-
Question 1 of 70
1. Question
1 pointsWhat are two problems that can be caused by a large number of ARP request and reply messages? (Choose two.)Correct
Incorrect
-
Question 2 of 70
2. Question
1 pointsRefer to the exhibit. Which field in the Sguil application window indicates the priority of an event or set of correlated events?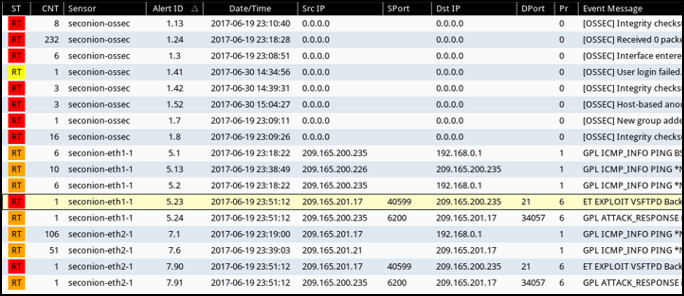 Correct
Correct
Incorrect
-
Question 3 of 70
3. Question
1 pointsMatch the job titles to SOC personnel positions. (Not all options are used.)Correct
Incorrect
-
Question 4 of 70
4. Question
1 pointsIf the default gateway is configured incorrectly on the host, what is the impact on communications?Correct
Incorrect
-
Question 5 of 70
5. Question
1 pointsWhen a connectionless protocol is in use at a lower layer of the OSI model, how is missing data detected and retransmitted if necessary?Correct
Incorrect
-
Question 6 of 70
6. Question
1 pointsWhat is the prefix length notation for the subnet mask 255.255.255.224?Correct
Incorrect
-
Question 7 of 70
7. Question
1 pointsWhich network monitoring tool saves captured network frames in PCAP files?Correct
Incorrect
-
Question 8 of 70
8. Question
1 pointsWhat is the TCP mechanism used in congestion avoidance?Correct
Incorrect
-
Question 9 of 70
9. Question
1 pointsWhat is the Internet?Correct
Incorrect
-
Question 10 of 70
10. Question
1 pointsWhich protocol is used by the traceroute command to send and receive echo-requests and echo-replies?Correct
Incorrect
-
Question 11 of 70
11. Question
1 pointsWhat are two ICMPv6 messages that are not present in ICMP for IPv4? (Choose two.)Correct
Incorrect
-
Question 12 of 70
12. Question
1 pointsMatch the network security testing technique with how it is used to test network security. (Not all options are used.)Correct
Incorrect
-
Question 13 of 70
13. Question
1 pointsWhat are two monitoring tools that capture network traffic and forward it to network monitoring devices? (Choose two.)Correct
Incorrect
-
Question 14 of 70
14. Question
1 pointsWhich network monitoring tool is in the category of network protocol analyzers?Correct
Incorrect
-
Question 15 of 70
15. Question
1 pointsBased on the command output shown, which file permission or permissions have been assigned to the other user group for the data.txt file?ls –l data.txt -rwxrw-r-- sales staff 1028 May 28 15:50 data.txt
Correct
Incorrect
-
Question 16 of 70
16. Question
1 pointsWhat are three benefits of using symbolic links over hard links in Linux? (Choose three.)Correct
Incorrect
-
Question 17 of 70
17. Question
1 pointsA network security specialist is tasked to implement a security measure that monitors the status of critical files in the data center and sends an immediate alert if any file is modified. Which aspect of secure communications is addressed by this security measure?Correct
Incorrect
-
Question 18 of 70
18. Question
1 pointsA network administrator is configuring an AAA server to manage TACACS+ authentication. What are two attributes of TACACS+ authentication? (Choose two.)Correct
Incorrect
-
Question 19 of 70
19. Question
1 pointsIn an attempt to prevent network attacks, cyber analysts share unique identifiable attributes of known attacks with colleagues. What three types of attributes or indicators of compromise are helpful to share? (Choose three.)Correct
Incorrect
-
Question 20 of 70
20. Question
1 pointsWhich two types of messages are used in place of ARP for address resolution in IPv6? (Choose two.)Correct
Incorrect
-
Question 21 of 70
21. Question
1 pointsWhat is indicated by a true negative security alert classification?Correct
Incorrect
-
Question 22 of 70
22. Question
1 pointsWhich statement describes the anomaly-based intrusion detection approach?Correct
Incorrect
-
Question 23 of 70
23. Question
1 pointsMatch the description to the antimalware approach. (Not all options are used.)Correct
Incorrect
-
Question 24 of 70
24. Question
1 pointsWhich two protocols are associated with the transport layer? (Choose two.)Correct
Incorrect
-
Question 25 of 70
25. Question
1 pointsA network administrator is creating a network profile to generate a network baseline. What is included in the critical asset address space element?Correct
Incorrect
-
Question 26 of 70
26. Question
1 pointsWhat are the three impact metrics contained in the CVSS 3.0 Base Metric Group? (Choose three.)Correct
Incorrect
-
Question 27 of 70
27. Question
1 pointsWhat is a characteristic of DNS?Correct
Incorrect
-
Question 28 of 70
28. Question
1 pointsWhat are two differences between HTTP and HTTP/2? (Choose two.)Correct
Incorrect
-
Question 29 of 70
29. Question
1 pointsMatch the steps with the actions that are involved when an internal host with IP address 192.168.10.10 attempts to send a packet to an external server at the IP address 209.165.200.254 across a router R1 that is running dynamic NAT. (Not all options are used.)Correct
Incorrect
-
Question 30 of 70
30. Question
1 pointsA router has received a packet destined for a network that is in the routing table. What steps does the router perform to send this packet on its way? Match the step to the task performed by the router.Correct
Incorrect
-
Question 31 of 70
31. Question
1 pointsWhat are two shared characteristics of the IDS and the IPS? (Choose two.)Correct
Incorrect
-
Question 32 of 70
32. Question
1 pointsWhich statement describes a typical security policy for a DMZ firewall configuration?Correct
Incorrect
-
Question 33 of 70
33. Question
1 pointsAfter complaints from users, a technician identifies that the college web server is running very slowly. A check of the server reveals that there are an unusually large number of TCP requests coming from multiple locations on the Internet. What is the source of the problem?Correct
Incorrect
-
Question 34 of 70
34. Question
1 pointsWhich two statements describe access attacks? (Choose two.)Correct
Incorrect
-
Question 35 of 70
35. Question
1 pointsWhich two actions can be taken when configuring Windows Firewall? (Choose two.)Correct
Incorrect
-
Question 36 of 70
36. Question
1 pointsWhich statement describes the state of the administrator and guest accounts after a user installs Windows desktop version to a new computer?Correct
Incorrect
-
Question 37 of 70
37. Question
1 pointsWhat is a purpose of entering the nslookup cisco.com command on a Windows PC?Correct
Incorrect
-
Question 38 of 70
38. Question
1 pointsHow is the event ID assigned in Sguil?Correct
Incorrect
-
Question 39 of 70
39. Question
1 pointsWhich two types of network traffic are from protocols that generate a lot of routine traffic? (Choose two.)Correct
Incorrect
-
Question 40 of 70
40. Question
1 pointsWhat are two elements that form the PRI value in a syslog message? (Choose two.)Correct
Incorrect
-
Question 41 of 70
41. Question
1 pointsWhich three pieces of information are found in session data? (Choose three.)Correct
Incorrect
-
Question 42 of 70
42. Question
1 pointsWhat kind of ICMP message can be used by threat actors to perform network reconnaissance and scanning attacks?Correct
Incorrect
-
Question 43 of 70
43. Question
1 pointsA flood of packets with invalid source IP addresses requests a connection on the network. The server busily tries to respond, resulting in valid requests being ignored. What type of attack has occurred?Correct
Incorrect
-
Question 44 of 70
44. Question
1 pointsAn attacker is redirecting traffic to a false default gateway in an attempt to intercept the data traffic of a switched network. What type of attack could achieve this?Correct
Incorrect
-
Question 45 of 70
45. Question
1 pointsWhat is the most common goal of search engine optimization (SEO) poisoning?Correct
Incorrect
-
Question 46 of 70
46. Question
1 pointsUsers report that a database file on the main server cannot be accessed. A database administrator verifies the issue and notices that the database file is now encrypted. The organization receives a threatening email demanding payment for the decryption of the database file. What type of attack has the organization experienced?Correct
Incorrect
-
Question 47 of 70
47. Question
1 pointsWhat two kinds of personal information can be sold on the dark web by cybercriminals? (Choose two.)Correct
Incorrect
-
Question 48 of 70
48. Question
1 pointsWhat three services are offered by FireEye? (Choose three.)Correct
Incorrect
-
Question 49 of 70
49. Question
1 pointsAfter containment, what is the first step of eradicating an attack?Correct
Incorrect
-
Question 50 of 70
50. Question
1 pointsWhich activity is typically performed by a threat actor in the installation phase of the Cyber Kill Chain?Correct
Incorrect
-
Question 51 of 70
51. Question
1 pointsWhen dealing with a security threat and using the Cyber Kill Chain model, which two approaches can an organization use to help block potential exploitations on a system? (Choose two.)Correct
Incorrect
-
Question 52 of 70
52. Question
1 pointsHow might corporate IT professionals deal with DNS-based cyber threats?Correct
Incorrect
-
Question 53 of 70
53. Question
1 pointsHow does using HTTPS complicate network security monitoring?Correct
Incorrect
-
Question 54 of 70
54. Question
1 pointsMatch the security concept to the description.Correct
Incorrect
-
Question 55 of 70
55. Question
1 pointsWhat are the two important components of a public key infrastructure (PKI) used in network security? (Choose two.)Correct
Incorrect
-
Question 56 of 70
56. Question
1 pointsWhich three algorithms are designed to generate and verify digital signatures? (Choose three.)Correct
Incorrect
-
Question 57 of 70
57. Question
1 pointsWhich section of a security policy is used to specify that only authorized individuals should have access to enterprise data?Correct
Incorrect
-
Question 58 of 70
58. Question
1 pointsRefer to the exhibit. A cybersecurity analyst is viewing captured packets forwarded on switch S1. Which device has the MAC address d8:cb:8a:5c:d5:8a?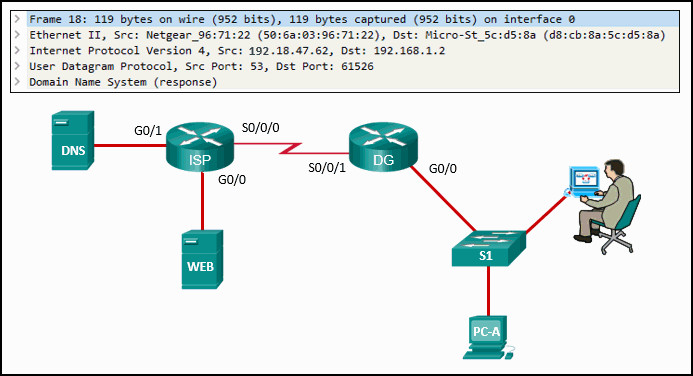 Correct
Correct
Incorrect
-
Question 59 of 70
59. Question
1 pointsWhat kind of message is sent by a DHCPv4 client requesting an IP address?Correct
Incorrect
-
Question 60 of 70
60. Question
1 pointsPlace the evidence collection priority from most volatile to least volatile as defined by the IETF guidelines.Correct
Incorrect
-
Question 61 of 70
61. Question
1 pointsWhat is the responsibility of the human resources department when handling a security incident?Correct
Incorrect
-
Question 62 of 70
62. Question
1 pointsHow does a security information and event management system (SIEM) in a SOC help the personnel fight against security threats?Correct
Incorrect
-
Question 63 of 70
63. Question
1 pointsAt which OSI layer is a source IP address added to a PDU during the encapsulation process?Correct
Incorrect
-
Question 64 of 70
64. Question
1 pointsWhat is the purpose of CSMA/CA?Correct
Incorrect
-
Question 65 of 70
65. Question
1 pointsWhy is DHCP preferred for use on large networks?Correct
Incorrect
-
Question 66 of 70
66. Question
1 pointsWhich NIST incident response life cycle phase includes continuous monitoring by the CSIRT to quickly identify and validate an incident?Correct
Incorrect
-
Question 67 of 70
67. Question
1 pointsWhat will a threat actor do to create a back door on a compromised target according to the Cyber Kill Chain model?Correct
Incorrect
-
Question 68 of 70
68. Question
1 pointsWhich type of evidence supports an assertion based on previously obtained evidence?Correct
Incorrect
-
Question 69 of 70
69. Question
1 pointsA technician is configuring email on a mobile device. The user wants to be able to keep the original email on the server, organize it into folders, and synchronize the folders between the mobile device and the server. Which email protocol should the technician use?Correct
Incorrect
-
Question 70 of 70
70. Question
1 pointsWhat is the goal of an attack in the installation phase of the Cyber Kill Chain?Correct
Incorrect
