How to find: Press “Ctrl + F” in the browser and fill in whatever wording is in the question to find that question/answer. If the question is not here, find it in Questions Bank.
NOTE: If you have the new question on this test, please comment Question and Multiple-Choice list in form below this article. We will update answers for you in the shortest time. Thank you! We truly value your contribution to the website.
CyberOps Associate (Version 1.0) – Modules 26 – 28: Analyzing Security Data Group Exam
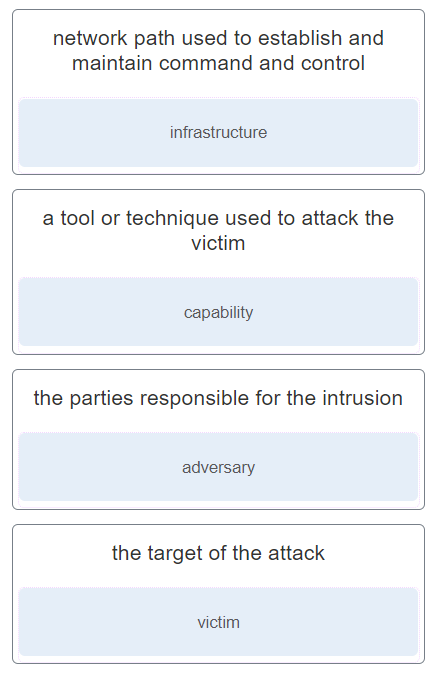
1. Match the intrusion event defined in the Diamond Model of intrusion to the description.
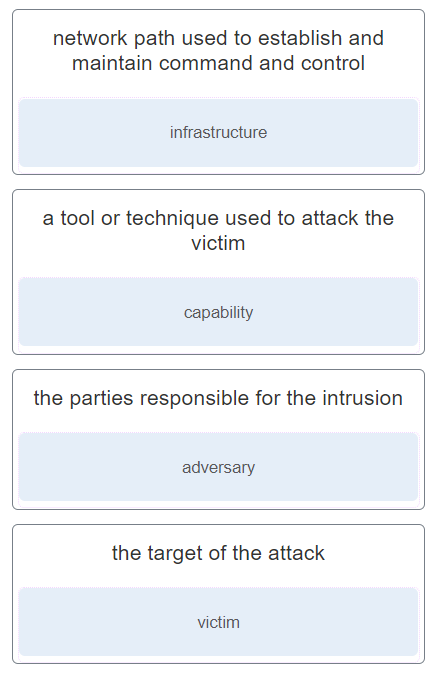
- network path used to establish and maintain command and control : infrastructure
- a tool or technique used to attack the victim : capability
- the parties responsible for the intrusion : adversary
- the target of the attack : victim
2. What two shared sources of information are included within the MITRE ATT&CK framework? (Choose two.)
- collection of digital evidence from most volatile evidence to least volatile
- attacker tactics, techniques, and procedures
- details about the handling of evidence including times, places, and personnel involved
- eyewitness evidence from someone who directly observed criminal behavior
- mapping the steps in an attack to a matrix of generalized tactics
Explanation: The MITRE Framework uses stored information on attacker tactics, techniques, and procedures (TTP) as part of threat defense and attack attribution. This is done by mapping the steps in an attack to a matrix of generalized tactics and describing the techniques that are used in each tactic. These sources of information create models that assist in the ability to attribute a threat.
3. What information is gathered by the CSIRT when determining the scope of a security incident?
- the networks, systems, and applications affected by an incident
- the amount of time and resources needed to handle an incident
- the strategies and procedures used for incident containment
- the processes used to preserve evidence
Explanation: The scoping activity performed by the CSIRT after an incident determines which networks, systems, or applications are affected; who or what originated the incident; and how the incident is occurring.
4. According to NIST standards, which incident response stakeholder is responsible for coordinating an incident response with other stakeholders to minimize the damage of an incident?
- human resources
- legal department
- management
- IT support
Explanation: The management team creates the policies, designs the budget, and is in charge of staffing all departments. Management is also responsible for coordinating the incident response with other stakeholders and minimizing the damage of an incident.
5. According to NIST, which step in the digital forensics process involves drawing conclusions from data?
- reporting
- collection
- examination
- analysis
Explanation: NIST describes the digital forensics process as involving the following four steps:
Collection – the identification of potential sources of forensic data and acquisition, handling, and storage of that data.
Examination – assessing and extracting relevant information from the collected data. This may involve decompression or decryption of the data.
Analysis – drawing conclusions from the data. Salient features, such as people, places, times, events, and so on should be documented.
Reporting – preparing and presenting information that resulted from the analysis. Reporting should be impartial and alternative explanations should be offered if appropriate.
6. A cybersecurity analyst has been called to a crime scene that contains several technology items including a computer. Which technique will be used so that the information found on the computer can be used in court?
- Tor
- rootkit
- unaltered disk image
- log collection
Explanation: A normal file copy does not recover all data on a storage device so an unaltered disk image is commonly made. An unaltered disk image preserves the original evidence, thus preventing inadvertent alteration during the discovery phase. It also allows recreation of the original evidence.
7. In which phase of the NIST incident response life cycle is evidence gathered that can assist subsequent investigations by authorities?
- postincident activities
- detection and analysis
- preparation
- containment, eradication, and recovery
Explanation: NIST defines four phases in the incident response process life cycle. It is in the containment, eradication, and recovery phase that evidence is gathered to resolve an incident and to help with subsequent investigations.
8. When dealing with security threats and using the Cyber Kill Chain model, which two approaches can an organization use to block a potential back door creation? (Choose two.)
- Audit endpoints to discover abnormal file creations.
- Establish an incident response playbook.
- Consolidate the number of Internet points of presence.
- Conduct damage assessment.
- Use HIPS to alert or place a block on common installation paths.
Explanation: In the installation phase of the Cyber Kill Chain, the threat actor establishes a back door into the system to allow for continued access to the target. Among other measures, using HIPS to alert or block on common installation paths and auditing endpoints to discover abnormal file creations can help block a potential back door creation.
9. What is defined in the SOP of a computer security incident response capability (CSIRC)?
- the details on how an incident is handled
- the procedures that are followed during an incident response
- the metrics for measuring incident response capabilities
- the roadmap for increasing incident response capabilities
Explanation: A CSIRC will include standard operating procedures (SOPs) that are followed during an incident response. Procedures include following technical processes, filling out forms, and following checklists.
10. How does an application program interact with the operating system?
- sending files
- accessing BIOS or UEFI
- making API calls
- using processes
Explanation: Application programs interact with an operating system through system calls to the OS application programming interface (API). These system calls allow access to many aspects of system operation such as software process control, file management, device management, and network access.
11. Which tool included in the Security Onion provides a visual interface to NSM data?
- Curator
- Beats
- Squert
- OSSEC
Explanation: Dashboards provide a combination of data and visualizations designed to improve the access of individuals to large amounts of information. Kibana includes the capability of designing custom dashboards. In addition, other tools that are included in Security Onion, such as Squert, provide a visual interface to NSM data.
12. Which tool included in the Security Onion includes the capability of designing custom dashboards?
- Sguil
- Kibana
- Squert
- OSSEC
Explanation: Dashboards are usually interactive and provide a combination of data and visualizations designed to improve the access of individuals to large amounts of information. Kibana includes the capability of designing custom dashboards.
13. How is the hash value of files useful in network security investigations?
- It is used to decode files.
- It helps identify malware signatures.
- It verifies confidentiality of files.
- It is used as a key for encryption.
Explanation: When ELSA is used to investigate downloaded files, the hash value of each file is created and stored with other information about the file. If a cybersecurity analyst is suspicious of the file, the hash value can be submitted to an online malware repository site to determine if the file is known malware.
14. Which technology is a major standard consisting of a pattern of symbols that describe data to be matched in a query?
Explanation: A regular expression (regex) is a pattern of symbols that describe data to be matched in a query or other operation. Regular expressions are constructed similarly to arithmetic expressions, by using various operators to combine smaller expressions. There are two major standards of regular expression, POSIX and Perl.
15. Which tool is a Security Onion integrated host-based intrusion detection system?
Explanation: OSSEC is a host-based intrusion detection system (HIDS) that is integrated into Security Onion and actively monitors host system operation.
16. Which term is used to describe the process of converting log entries into a common format?
- classification
- systemization
- normalization
- standardization
Explanation: For processing log entries, data normalization can organize and convert data values in datasets from difference sources into common format. The normalization makes it easy for further data analysis and reporting.
17. What is the purpose for data normalization?
- to simplify searching for correlated events
- to reduce the amount of alert data
- to enhance the secure transmission of alert data
- to make the alert data transmission fast
Explanation: With data normalization various sources of data are combined into a common display format, which simplifies the searching for similar or relevant events.
18. Which personnel in a SOC is assigned the task of verifying whether an alert triggered by monitoring software represents a true security incident?
- SOC Manager
- Tier 3 personnel
- Tier 2 personnel
- Tier 1 personnel
Explanation: In a SOC, the job of a Tier 1 Alert Analyst includes monitoring incoming alerts and verifying that a true security incident has occurred.
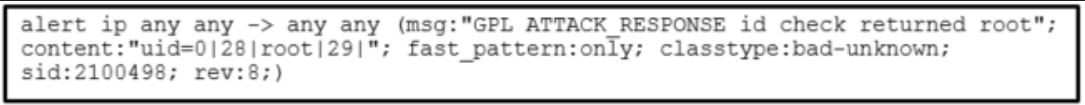
19. Refer to the exhibit. A security analyst is reviewing an alert message generated by Snort. What does the number 2100498 in the message indicate?
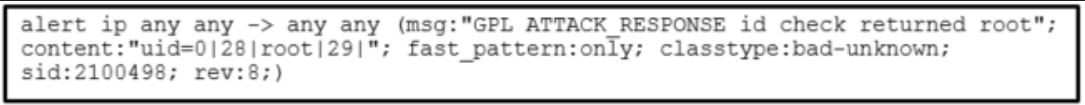
- the id of the user that triggers the alert
- the message length in bits
- the Snort rule that is triggered
- the session number of the message
Explanation: The sid field in a Snort alert message indicates the Snort security rule that is triggered.
20. What are security event logs commonly based on when sourced by traditional firewalls?
- static filtering
- application analysis
- signatures
- 5-tuples
Explanation: Traditional firewalls commonly provide security event logs based on the 5-tuples of source IP address and port number, destination IP address and port number, and the protocol in use.
21. A threat actor has successfully breached the network firewall without being detected by the IDS system. What condition describes the lack of alert?
- false negative
- true negative
- true positive
- false positive
Explanation: A false negative is where no alert exists and exploits are not being detected by the security systems that are in place.
22. What information is contained in the options section of a Snort rule?
- direction of traffic flow
- text describing the event
- action to be taken
- source and destination address
Explanation: Snort rules consist of two sections, the rules header and the rule options. The rule options section of a snort rule consists of the messages text displayed to describe an alert as well as metadata about the alert.
23. A network administrator is trying to download a valid file from an internal server. However, the process triggers an alert on a NMS tool. What condition describes this alert?
- false negative
- false positive
- true negative
- true positive
Explanation: Alerts can be classified as follows:
True Positive: The alert has been verified to be an actual security incident.
False Positive: The alert does not indicate an actual security incident. Benign activity that results in a false positive is sometimes referred to as a benign trigger.
An alternative situation is that an alert was not generated. The absence of an alert can be classified as:
True Negative: No security incident has occurred. The activity is benign.
False Negative: An undetected incident has occurred.
24. What is indicated by a Snort signature ID that is below 3464?
- The SID was created by Sourcefire and distributed under a GPL agreement.
- This is a custom signature developed by the organization to address locally observed rules.
- The SID was created by the Snort community and is maintained in Community Rules.
- The SID was created by members of EmergingThreats.
Explanation: Snort is an open source network intrusion prevention system (NIPS) and network intrusion detection system (NIDS) developed by Sourcefire. It has the ability to perform real time traffic analysis and packet logging on Internet Protocol (IP) networks and can also be used to detect probes or attacks.
25. After a security monitoring tool identifies a malware attachment entering the network, what is the benefit of performing a retrospective analysis?
- A retrospective analysis can help in tracking the behavior of the malware from the identification point forward.
- It can identify how the malware originally entered the network.
- It can calculate the probability of a future incident.
- It can determine which network host was first affected.
Explanation: General security monitoring can identify when a malware attachment enters a network and which host is first infected. Retrospective analysis takes the next step and is the tracking of the behavior of the malware from that point forward.
26. A threat actor collects information from web servers of an organization and searches for employee contact information. The information collected is further used to search personal information on the Internet. To which attack phase do these activities belong according to the Cyber Kill Chain model?
- action on objectives
- exploitation
- reconnaissance
- weaponization
Explanation: According to the Cyber Kill Chain model, in the reconnaissance phase the threat actor performs research, gathers intelligence, and selects targets.
27. Which HIDS is integrated into the Security Onion and uses rules to detect changes in host-based operating parameters caused by malware through system calls?
Explanation: OSSEC is a HIDS integrated into the Security Onion and uses rules to detect changes in host-based parameters like the execution of software processes, changes in user privileges, registry modifications, among many others. OSSEC rules will trigger events that occurred on the host, including indicators that malware may have interacted with the OS kernel. Bro, Snort, and Suricata are examples of NIDS systems.
28. Which type of events should be assigned to categories in Sguil?
- false positive
- true positive
- false negative
- true negative
Explanation: Sguil includes seven pre-built categories that can be assigned to events that have been identified as true positives.
29. A cybersecurity analyst is going to verify security alerts using the Security Onion. Which tool should the analyst visit first?
Explanation: The primary duty of a cybersecurity analyst is the verification of security alerts. In the Security Onion, the first place that a cybersecurity analyst will go to verify alerts is Sguil because it provides a high-level console for investigating security alerts from a wide variety of sources.
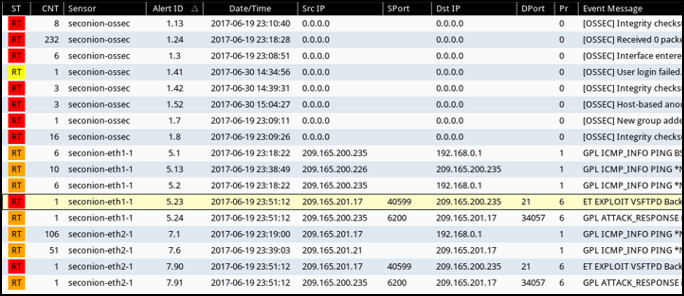
30. Refer to the exhibit. Which field in the Sguil application window indicates the priority of an event or set of correlated events?
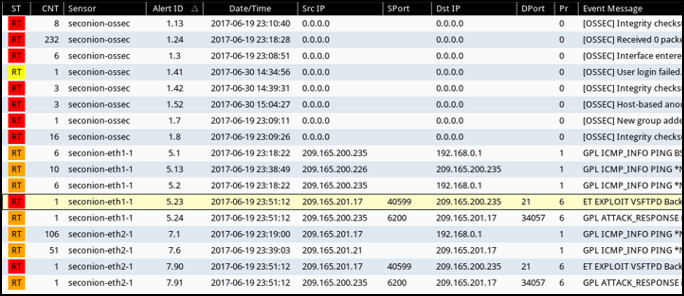
Explanation: The Sguil application window has several fields available that give information about an event. The ST field gives the status of an event that includes a color-coded priority from light yellow to red to indicate four levels of priority.
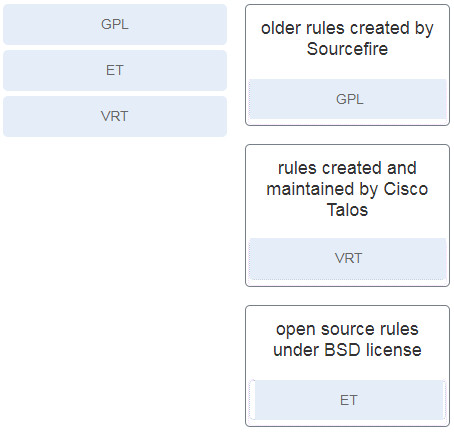
31. Match the Snort rule source to the description.
32. What is the purpose for data reduction as it relates to NSM?
- to make the alert data transmission fast
- to remove recurring data streams
- to enhance the secure transmission of alert data
- to diminish the quantity of NSM data to be handled
Explanation: The amount of network traffic that is collected by packet captures and the number of log file entries and alerts that are generated by network and security devices can be enormous. For this reason, it is important to identify the NSM-related data that should be gathered. This process is called data reduction.
33. Why would threat actors prefer to use a zero-day attack in the Cyber Kill Chain weaponization phase?
- to avoid detection by the target
- to launch a DoS attack toward the target
- to get a free malware package
- to gain faster delivery of the attack on the target
Explanation: When a threat actor prepares a weapon for an attack, the threat actor chooses an automated tool (weaponizer) that can be deployed through discovered vulnerabilities. Malware that will carry desired attacks is then built into the tool as the payload. The weapon (tool plus malware payload) will be delivered to the target system. By using a zero-day weaponizer, the threat actor hopes that the weapon will not be detected because it is unknown to security professionals and detection methods are not yet developed.
34. What is the objective the threat actor in establishing a two-way communication channel between the target system and a CnC infrastructure?
- to allow the threat actor to issue commands to the software that is installed on the target
- to send user data stored on the target to the threat actor
- to steal network bandwidth from the network where the target is located
- to launch a buffer overflow attack
Explanation: In the command and control phase of the Cyber Kill Chain, the threat actor establishes command and control (CnC) with the target system. With the two-way communication channel, the threat actor is able to issue commands to the malware software installed on the target.
35. Which meta-feature element in the Diamond Model describes information gained by the adversary?
- methodology
- resources
- results
- direction
Explanation: The meta-feature element results are used to delineate what the adversary gained from the intrusion event.
36. In which step of the NIST incident response process does the CSIRT perform an analysis to determine which networks, systems, or applications are affected; who or what originated the incident; and how the incident is occurring?
- incident notification
- attacker identification
- scoping
- detection
Explanation: In the detection and analysis phase of the NIST incident response process life cycle, the CSIRT should immediately perform an initial analysis to determine the scope of the incident, such as which networks, systems, or applications are affected; who or what originated the incident; and how the incident is occurring.
37. Which classification indicates that an alert is verified as an actual security incident?
- false negative
- true positive
- false positive
- true negative
Explanation:
Alerts can be classified as follows:
True Positive: The alert has been verified to be an actual security incident.
False Positive: The alert does not indicate an actual security incident. Benign activity that results in a false positive is sometimes referred to as a benign trigger.
An alternative situation is that an alert was not generated. The absence of an alert can be classified as follows:
True Negative: No security incident has occurred. The activity is benign.
False Negative: An undetected incident has occurred.
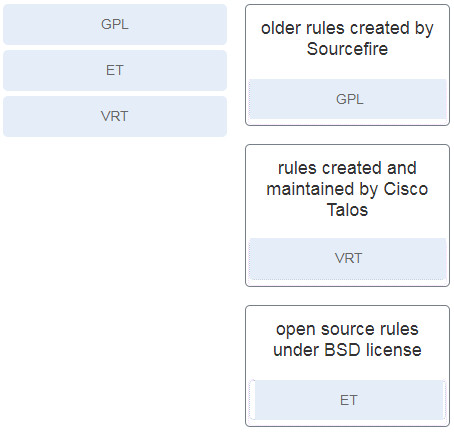

Match the Snort rule source to the description.
older rules created by Sourcefire: GPLrules created and maintained by Cisco Talos: VRTopen source rules under BSD license: ET
Which type of events should be assigned to categories in Sguil?
Thanks!!
A threat actor collects information from web servers of an organization and searches for employee contact information. The information collected is further used to search personal information on the Internet. To which attack phase do these activities belong according to the Cyber Kill Chain model?
action on objectives
exploitation
reconnaissance
weaponization
added! Many thank
Which HIDS is integrated into the Security Onion and uses rules to detect changes in host-based operating parameters caused by malware through system calls?
OSSEC
Bro
Snort
Suricata
Which type of events should be assigned to categories in Sguil?
false positive
true positive
false negative
true negative
A cybersecurity analyst is going to verify security alerts using the Security Onion. Which tool should the analyst visit first?
Bro
Sguil
CapME
ELK
25- Match the intrusion event defined in the Diamond Model of intrusion to the description.
+ infrastructure
+ capability
+ adversary
+ victim
24- What two shared sources of information are included within the MITRE ATT&CK framework? (Choose two.)
collection of digital evidence from most volatile evidence to least volatile
attacker tactics, techniques, and procedures
details about the handling of evidence including times, places, and personnel involved
eyewitness evidence from someone who directly observed criminal behavior
mapping the steps in an attack to a matrix of generalized tactics
The MITRE Framework uses stored information on attacker tactics, techniques, and procedures (TTP) as part of threat defense and attack attribution. This is done by mapping the steps in an attack to a matrix of generalized tactics and describing the techniques that are used in each tactic. These sources of information create models that assist in the ability to attribute a threat.
This item references content from the following areas:
CyberOps Associate
23- What information is gathered by the CSIRT when determining the scope of a security incident?
the networks, systems, and applications affected by an incident
the amount of time and resources needed to handle an incident
the strategies and procedures used for incident containment
the processes used to preserve evidence
22- According to NIST standards, which incident response stakeholder is responsible for coordinating an incident response with other stakeholders to minimize the damage of an incident?
human resources
legal department
management
IT support
21- According to NIST, which step in the digital forensics process involves drawing conclusions from data?
20- A cybersecurity analyst has been called to a crime scene that contains several technology items including a computer. Which technique will be used so that the information found on the computer can be used in court?
19- In which phase of the NIST incident response life cycle is evidence gathered that can assist subsequent investigations by authorities?
18- When dealing with security threats and using the Cyber Kill Chain model, which two approaches can an organization use to block a potential back door creation? (Choose two.)
17- What is defined in the SOP of a computer security incident response capability (CSIRC)?
16- How does an application program interact with the operating system?
15- Which tool included in the Security Onion provides a visual interface to NSM data?
14- Which tool included in the Security Onion includes the capability of designing custom dashboards?
Sguil
Kibana
Squert
OSSEC
Dashboards are usually interactive and provide a combination of data and visualizations designed to improve the access of individuals to large amounts of information. Kibana includes the capability of designing custom dashboards.
This item references content from the following areas:
CyberOps Associate
13- How is the hash value of files useful in network security investigations?
12- Which technology is a major standard consisting of a pattern of symbols that describe data to be matched in a query?
11- Which tool is a Security Onion integrated host-based intrusion detection system?
10- Which term is used to describe the process of converting log entries into a common format?
9- What is the purpose for data normalization?
8- Which personnel in a SOC is assigned the task of verifying whether an alert triggered by monitoring software represents a true security incident?
7- Refer to the exhibit. A security analyst is reviewing an alert message generated by Snort. What does the number 2100498 in the message indicate?
the exhibit
The exhibit
6- What are security event logs commonly based on when sourced by traditional firewalls?
5- A threat actor has successfully breached the network firewall without being detected by the IDS system. What condition describes the lack of alert?
4- What information is contained in the options section of a Snort rule?
3- A network administrator is trying to download a valid file from an internal server. However, the process triggers an alert on a NMS tool. What condition describes this alert?
Alerts can be classified as follows:
An alternative situation is that an alert was not generated. The absence of an alert can be classified as:
This item references content from the following areas:
CyberOps Associate
2- What is indicated by a Snort signature ID that is below 3464?
The SID was created by Sourcefire and distributed under a GPL agreement.
This is a custom signature developed by the organization to address locally observed rules.
The SID was created by the Snort community and is maintained in Community Rules.
The SID was created by members of EmergingThreats.
1- After a security monitoring tool identifies a malware attachment entering the network, what is the benefit of performing a retrospective analysis?
A retrospective analysis can help in tracking the behavior of the malware from the identification point forward.
It can identify how the malware originally entered the network.
It can calculate the probability of a future incident.
It can determine which network host was first affected.