4.0 Introduction
4.0.1 Why Should I Take this Module?
Linux is an open-source operating system that is fast, powerful, and highly customizable. It is built for network use as either a client or server. Linux is well-loved by a large community of users, including cybersecurity personnel.
Study this module to learn some basic information about the Linux operating system and learn some Linux skills. Linux skills are highly desirable in the cybersecurity operations profession.
4.0.2 What Will I Learn in this Module?
Module Title: Linux Overview
Module Objective: Implement basic Linux security.
| Topic Title | Topic Objective |
| Linux Basics | Explain why Linux skills are essential for network security monitoring and investigation. |
| Working in the Linux Shell | Use the Linux shell to manipulate text files. |
| Linux Servers and Clients | Explain how client-server networks function. |
| Basic Server Administration | Explain how a Linux administrator locates and manipulates security log files.. |
| The Linux File System | Manage the Linux file system and permissions. |
| Working in the Linux GUI | Explain the basic components of the Linux GUI. |
| Working on a Linux Host | Use tools to detect malware on a Linux host. |
4.1 Linux Basics
4.1.1 What is Linux?

Linux is an operating system that was created in 1991. Linux is open source, fast, reliable, and small. It requires very little hardware resources to run and is highly customizable. Unlike other operating systems such as Windows and Mac OS X, Linux was created, and is currently maintained by, a community of programmers. Linux is part of several platforms and can be found on devices anywhere from “wristwatches to supercomputers”.
Another important aspect of Linux is that it is designed to be connected to the network, which makes it much simpler to write and use network-based applications. Because Linux is open source, any person or company can get the kernel’s source code, inspect it, modify it, and re-compile it at will. They are also allowed to redistribute the program with or without charges.
A Linux distribution is the term used to describe packages created by different organizations. Linux distributions (or distros) include the Linux kernel with customized tools and software packages. While some of these organizations may charge for their Linux distribution support (geared towards Linux-based businesses), the majority of them also offer their distribution for free without support. Debian, Red Hat, Ubuntu, CentOS, and SUSE are just a few examples of Linux distributions.
4.1.2 The Value of Linux
Linux is often the operating system of choice in the Security Operations Center (SOC). These are some of the reasons to choose Linux:
- Linux is open source – Any person can acquire Linux at no charge and modify it to fit specific needs. This flexibility allows analysts and administrators to tailor-build an operating system specifically for security analysis.
- The Linux CLI is very powerful – While a GUI makes many tasks easier to perform, it adds complexity and requires more computer resources to run. The Linux Command Line Interface (CLI) is extremely powerful and enables analysts to perform tasks not only directly on a terminal, but also remotely.
- The user has more control over the OS – The administrator user in Linux, known as the root user, or superuser, has absolute power over the computer. Unlike other operating systems, the root user can modify any aspect of the computer with a few keystrokes. This ability is especially valuable when working with low level functions such as the network stack. It allows the root user to have precise control over the way network packets are handled by the operating system.
- It allows for better network communication control – Control is an inherent part of Linux. Because the OS can be adjusted in practically every aspect, it is a great platform for creating network applications. This is the same reason that many great network-based software tools are available for Linux only.
4.1.3 Linux in the SOC
The flexibility provided by Linux is a great feature for the SOC. The entire operating system can be tailored to become the perfect security analysis platform. For example, administrators can add only the necessary packages to the OS, making it lean and efficient. Specific software tools can be installed and configured to work in conjunction, allowing administrators to build a customized computer that fits perfectly in the workflow of a SOC.
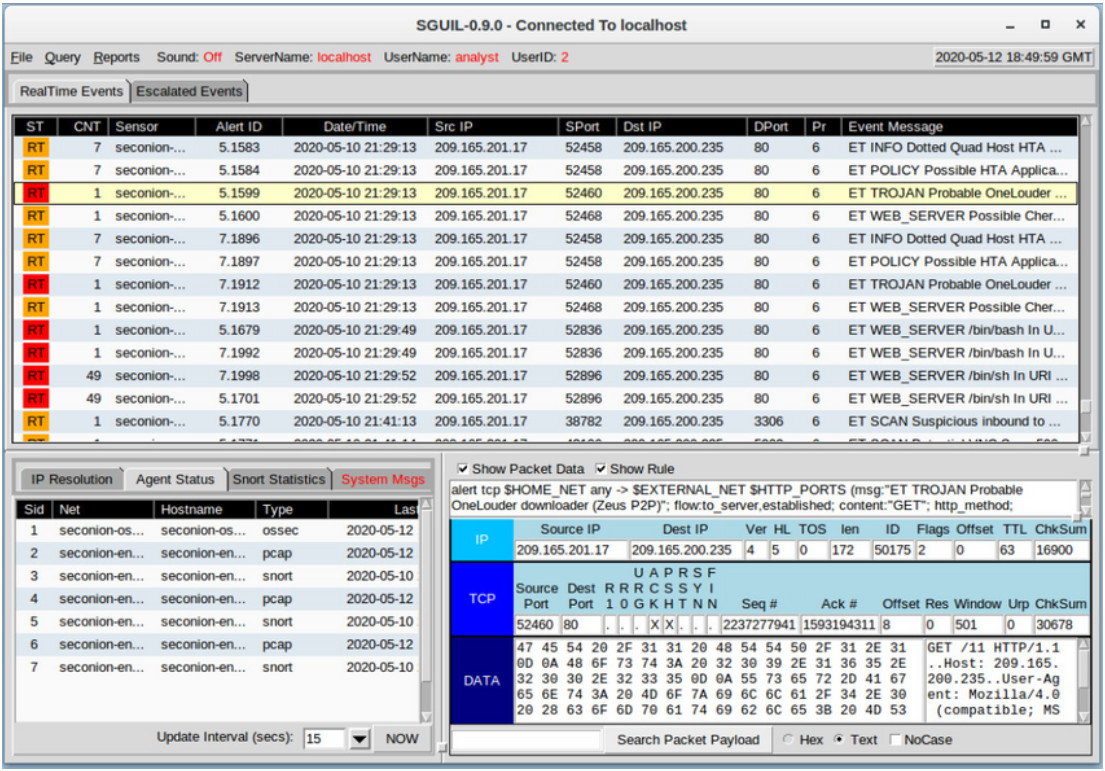
The figure shows Sguil, which is the cybersecurity analyst console in a special version of Linux called Security Onion. Security Onion is an open source suite of tools that work together for network security analysis. We will work with Security Onion later in this course.
The table lists a few tools that are often found in a SOC.
| SOC Tool | Description |
|---|---|
| Network packet capture software |
|
| Malware analysis tools | These tools allow analysts to safely run and observe malware execution without the risk of compromising the underlying system. |
| Intrusion detection systems (IDSs) |
|
| Firewalls | This software is used to specify, based on pre-defined rules, whether traffic is allowed to enter or leave a network or device. |
| Log managers |
|
| Security information and event management (SIEM) | SIEMs provide real-time analysis of alerts and log entries generated by network appliances such as IDSs and firewalls. |
| Ticketing systems | Task ticket assignment, editing, and recording is done through a ticket management system. Security alerts are often assigned to analysts through a ticketing system. |
4.1.4 Linux Tools
In addition to SOC-specific tools, Linux computers that are used in the SOC often contain penetration testing tools. Also known as PenTesting, a penetration test is the process of looking for vulnerabilities in a network or computer by attacking it. Packet generators, port scanners, and proof-of-concept exploits are examples of PenTesting tools.
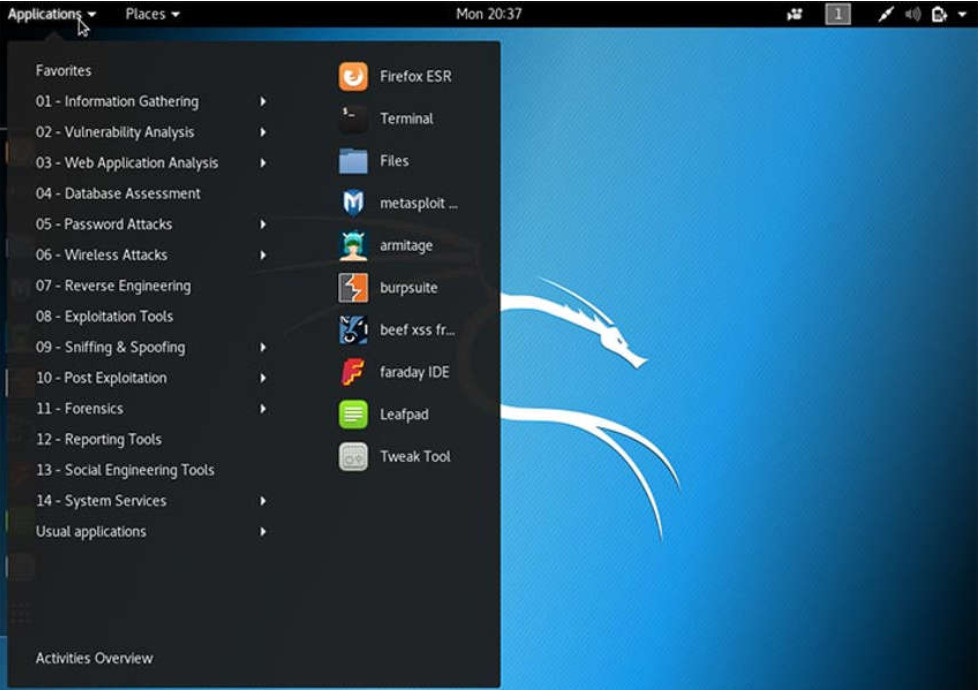
Kali Linux is a Linux distribution groups many penetration tools together in a single Linux distribution. Kali contains a great selection of tools. The figure shows a screenshot of Kali Linux. Notice all the major categories of penetration testing tools.
4.2 Working in the Linux Shell
4.2.1 The Linux Shell
In Linux, the user communicates with the OS by using the CLI or the GUI. Linux often starts in the GUI by default. This hides the CLI from the user. One way to access the CLI from the GUI is through a terminal emulator application. These applications provide user access to the CLI and are often named as some variation of the word “terminal”. In Linux, popular terminal emulators are Terminator, eterm, xterm, konsole, and gnome-terminal.
Fabrice Bellard has created JSLinux which allows an emulated version of Linux to run in a browser. Search for it on the internet. Open a Linux console in JSLinux and type the ls command to list the current directory content. Keep the tab open if you would like to try out some of the other commands discussed in this chapter.
The figure shows gnome-terminal, a popular Linux terminal emulator.
Note: The terms shell, console, console window, CLI terminal, and terminal window are often used interchangeably.
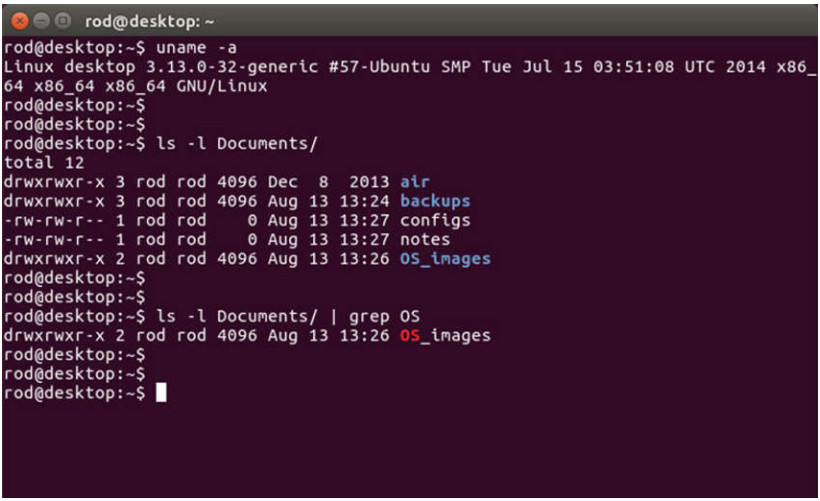
4.2.2 Basic Commands
Linux commands are programs created to perform a specific task. Use the man command (short for manual) to obtain documentation about commands. As an example, man ls provides documentation about the ls command from the user manual.
Because commands are programs stored on the disk, when a user types a command, the shell must find it on the disk before it can be executed. The shell will look for user-typed commands in specific directories and attempt to execute them. The list of directories checked by the shell is called the path. The path contains many directories commonly used to store commands. If a command is not in the path, the user must specify its location, or the shell will not be able to find it. Users can easily add directories to the path, if necessary.
To invoke a command via the shell, simply type its name. The shell will try to find it in the system path and execute it.
The table lists basic Linux commands and their functions.
| Command | Description |
|---|---|
| mv | Moves or renames files and directories |
| chmod | Modifies file permissions |
| chown | Changes the ownership of a file |
| dd | Copies data from an input to an output |
| pwd | Displays the name of the current directory |
| ps | Lists the processes that are currently running in the system |
| su | Simulates a login as another user or to become a superuser |
| sudo | Runs a command as a super user, by default, or another named user |
| grep | Used to search for specific strings of characters within a file or other command outputs. To search through the output of a previous command, grep must be piped at the end of the previous command. |
| ifconfig | Used to display or configure network card related information. If issued without parameters, ifconfig will display the current network card(s) configuration. Note: While still widely in use, this command is deprecated. Use ip address instead. |
| apt-get | Used to install, configure and remove packages on Debian and its derivatives. Note: apt-get is a user-friendly command line front-end for dpkg, Debian’s package manager. The combo dpkg and apt-get is the default package manager system in all Debian Linux derivatives, including Raspbian. |
| iwconfig | Used to display or configure wireless network card related information. Similar to ifconfig, iwconfig will display wireless information when issued without parameters. |
| shutdown | Shuts down the system, shutdown can be instructed to perform a number of shut down related tasks, including restart, halt, put to sleep or kick out all currently connected users. |
| passwd | Used to change the password. If no parameters are provided, passwd changes the password for the current user. |
| cat | Used to list the contents of a file and expects the file name as the parameter. The cat command is usually used on text files. |
| man | Used to display the documentation for a specific command. |
Note: It is assumed that the user has the proper permissions to execute the command. File permissions in Linux are covered later in this chapter.
4.2.3 File and Directory Commands
Many command line tools are included in Linux by default. To adjust the command operation, users can pass parameters and switches along with the command. The table lists a few of the most common commands related to files and directories.
| Command | Description |
|---|---|
| Is | Displays the files inside a directory |
| cd | Changes the current directory |
| mkdir | Creates a directory under the current directory |
| cp | Copies files from source to destination |
| mv | Moves files to a different directory |
| rm | Removes files |
| grep | Searches for specific strings of characters within a file or other commands outputs |
| cat | Lists the contents of a file and expects the file name as the parameter |
4.2.4 Working with Text Files
Linux has many different text editors, with various features and functions. Some text editors include graphical interfaces while others are command-line only tools. Each text editor includes a feature set designed to support a specific type of task. Some text editors focus on the programmer and include features such as syntax highlighting, brackets and parenthesis check, and other programming-focused features.
While graphical text editors are convenient and easy to use, command line-based text editors are very important for Linux users. The main benefit of command-line-based text editors is that they allow for text file editing from a remote computer.
Consider the following scenario: a user must perform administrative tasks on a Linux computer but is not sitting in front of that computer. Using SSH, the user starts a remote shell to the remote computer. Under the text-based remote shell, the graphical interface is not available, which makes it impossible to rely on tools such as graphical text editors. In this type of situation, text-based programs are crucial.
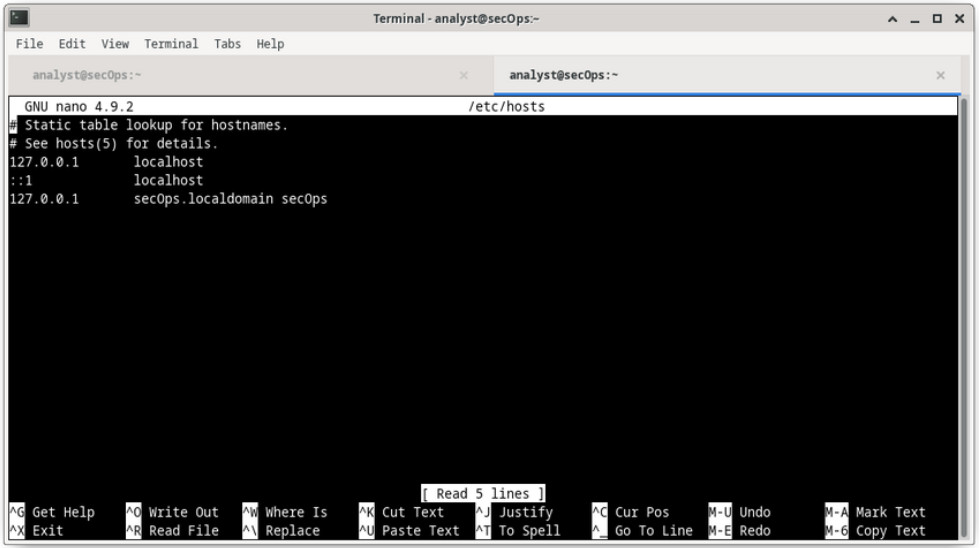
The figure shows nano, a popular command-line text editor. The administrator is editing firewall rules. Text editors are often used for system configuration and maintenance in Linux.
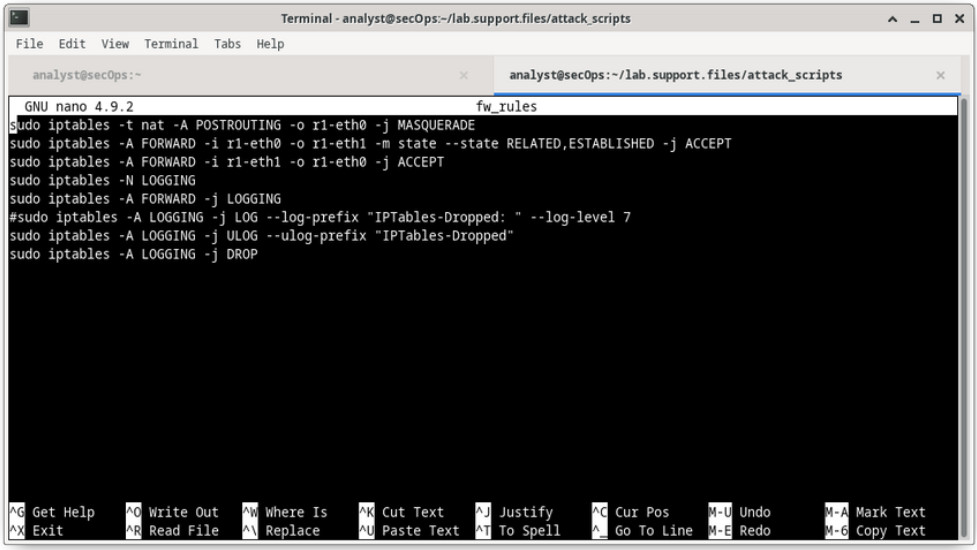
Due to the lack of graphical support, nano (or GNU nano) can only be controlled with the keyboard. For example, CTRL+O saves the current file; CTRL+W opens the search menu. GNU nano uses a two-line shortcut bar at the bottom of the screen, where commands for the current context are listed. Press CTRL+G for the help screen and a complete list of commands.
4.2.5 The Importance of Text Files in Linux
In Linux, everything is treated as a file. This includes the memory, the disks, the monitor, and the directories. For example, from the operating system standpoint, showing information on the display means to write to the file that represents the display device. It should be no surprise that the computer itself is configured through files. Known as configuration files, they are usually text files used to store adjustments and settings for specific applications or services. Practically everything in Linux relies on configuration files to work. Some services have not one, but several configuration files.
Users with proper permission levels can use text editors to change the contents of configuration files. After the changes are made, the file is saved and can be used by the related service or application. Users are able to specify exactly how they want any given application or service to behave. When launched, services and applications check the contents of specific configuration files to adjust their behavior accordingly.
In the figure, the administrator opened the host configuration file in nano for editing. The host file contains static mappings of host IP addresses to names. The names serve as shortcuts that allow connecting to other devices by using a name instead of an IP address. Only the superuser can change the host file.
Note: The administrator used the command sudo nano /etc/hosts to open the file. The command sudo (short for “superuser do”) invokes the superuser privilege to use the nano text editor to open the host file.
4.2.6 Lab – Working with Text Files in the CLI
In this lab, you will get familiar with Linux command-line text editors and configuration files.
4.2.6 Lab – Working with Text Files in the CLI
4.2.7 Lab – Getting Familiar with the Linux Shell
In this lab, you will use the Linux command line to manage files and folders and perform some basic administrative tasks.
4.2.7 Lab – Getting Familiar with the Linux Shell
4.3 Linux Servers and Clients
4.3.1 An Introduction to Client-Server Communications
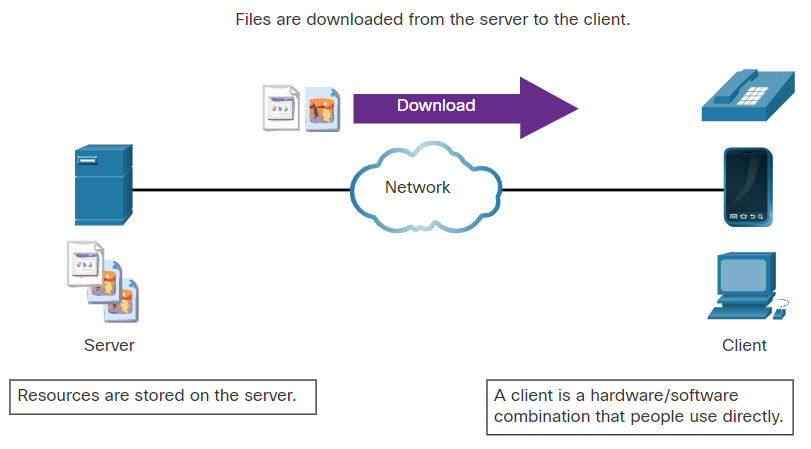
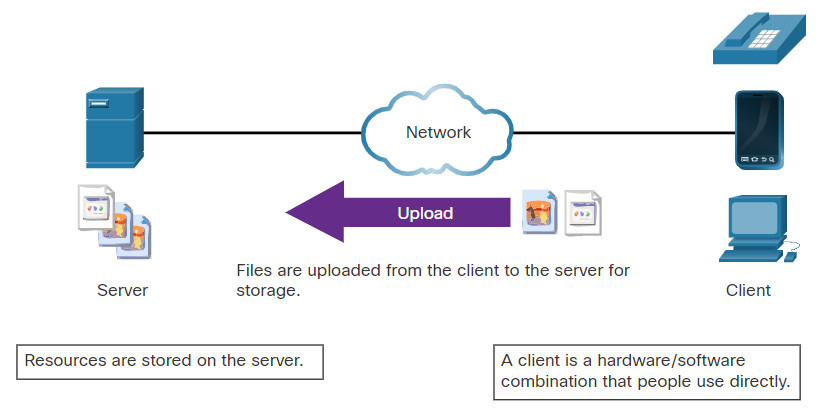
Servers are computers with software installed that enables them to provide services to clients across the network. There are many types of services. Some provide external resources such as files, email messages, or web pages to clients upon request. Other services run maintenance tasks such as log management, memory management, disk scanning, and more. Each service requires separate server software. For example, the server in the figure uses file server software to provide clients with the ability to retrieve and submit files.
Client-server communications is discussed in more detail later in the course.
4.3.2 Servers, Services, and Their Ports
In order that a computer can be the server for multiple services, ports are used. A port is a reserved network resource used by a service. A server is said to be “listening” on a port when it has associated itself to that port.
While the administrator can decide which port to use with any given service, many clients are configured to use a specific port by default. It is common practice to leave the service running in its default port. The table lists a few commonly used ports and their services. These are also called “well-known ports”.
| Port | Description |
|---|---|
| 20/21 | File Transfer Protocol (FTP) |
| 22 | Secure Shell (SSH) |
| 23 | Telnet remote login service |
| 25 | Simple Mail Transfer Protocol (SMTP) |
| 53 | Domain Name System (DNS) |
| 67/68 | Dynamic Host Configuration Protocol (DHCP) |
| 69 | Trivial File Transfer Protocol (TFTP) |
| 80 | Hypertext Transfer Protocol (HTTP) |
| 110 | Post Office Protocol version 3 (POP3) |
| 123 | Network Time Protocol (NTP) |
| 143 | Internet Message Access Protocol (IMAP) |
| 161/162 | Simple Network Management Protocol (SNMP) |
| 443 | HTTP Secure (HTTPS) |
Ports and their uses in network communications are discussed in more detail later in the course.
4.3.3 Clients
Clients are programs or applications designed to communicate with a specific type of server. Also known as client applications, clients use a well-defined protocol to communicate with the server. Web browsers are web clients that are used to communicate with web servers through the Hyper Text Transfer Protocol (HTTP) on port 80. The File Transfer Protocol (FTP) client is software used to communicate with an FTP server. The figure shows a client uploading files to a server.
4.3.4 Lab – Linux Servers
In this lab, you will use the Linux command line to identify servers that are running on a computer.
4.4 Basic Server Administration
4.4.1 Service Configuration Files
In Linux, services are managed using configuration files. Common options in configuration files are port number, location of the hosted resources, and client authorization details. When the service starts, it looks for its configuration files, loads them into memory, and adjusts itself according to the settings in the files. Configuration file modifications often require restarting the service before the changes take effect.
Because services often require superuser privileges to run, service configuration files often require superuser privileges to edit.
The command output shows a portion of the configuration file for Nginx, which is a lightweight web server for Linux.
[analyst@secOps ~]$ cat /etc/nginx/nginx.conf
#user html;
worker_processes 1;
#error_log logs/error.log;
#error_log logs/error.log notice;
#error_log logs/error.log info;
#pid logs/nginx.pid;
events {
worker_connections 1024;
}
http {
include mime.types;
default_type application/octet-stream;
#log_format main '$remote_addr - $remote_user [$time_local] "$request" '
# '$status $body_bytes_sent "$http_referer" '
# '"$http_user_agent" "$http_x_forwarded_for"';
#access_log logs/access.log main;
The next command output shows the configuration file for the network time protocol (NTP).
[analyst@secOps ~]$ cat /etc/ntp.conf # Please consider joining the pool: # # http://www.pool.ntp.org/join.html # # For additional information see: # - https://wiki.archlinux.org/index.php/Network_Time_Protocol_daemon # - http://support.ntp.org/bin/view/Support/GettingStarted # - the ntp.conf man page # Associate to Arch's NTP pool server 0.arch.pool.ntp.org server 1.arch.pool.ntp.org server 2.arch.pool.ntp.org server 3.arch.pool.ntp.org # By default, the server allows: # - all queries from the local host # - only time queries from remote hosts, protected by rate limiting and kod restrict default kod limited nomodify nopeer noquery notrap restrict 127.0.0.1 restrict ::1 # Location of drift file [analyst@secOps ~]$
The last command output shows the configuration file for Snort, a Linux-based intrusion detection system (IDS).
[analyst@secOps ~]$ cat /etc/snort/snort.conf #-------------------------------------------------- # VRT Rule Packages Snort.conf # # For more information visit us at: # http://www.snort.org Snort Website # http://vrt-blog.snort.org/ Sourcefire VRT Blog # # Mailing list Contact: [email protected] # False Positive reports: [email protected] # Snort bugs: [email protected] # # Compatible with Snort Versions: # VERSIONS : 2.9.9.0 # # Snort build options: # OPTIONS : --enable-gre --enable-mpls --enable-targetbased --enable-ppm --enable-perfprofiling --enable-zlib --enable-active-response --enable-normalizer --enable-reload --enable-react --enable-flexresp3
There is no rule for a configuration file format; it is the choice of the service’s developer. However, the option = value format is often used. For example, in the last command output, the variable ipvar is configured with several options. The first option, HOME_NET, has the value 209.165.200.224/27. The hash character (#) is used to indicate comments.
4.4.2 Hardening Devices
Device hardening involves implementing proven methods of securing the device and protecting its administrative access. Some of these methods involve maintaining passwords, configuring enhanced remote login features, and implementing secure login with SSH. Defining administrative roles in terms of access is another important aspect of securing infrastructure devices because not all information technology personnel should have the same level of access to the infrastructure devices.
Depending on the Linux distribution, many services are enabled by default. Some of these features are enabled for historical reasons but are no longer required. Stopping such services and ensuring they do not automatically start at boot time is another device hardening technique.
OS updates are also extremely important to maintaining a hardened device. New vulnerabilities are discovered every day. OS developers create and issue fixes and patches regularly. An up-to-date computer is less likely to be compromised.
The following are basic best practices for device hardening.
- Ensure physical security
- Minimize installed packages
- Disable unused services
- Use SSH and disable the root account login over SSH
- Keep the system updated
- Disable USB auto-detection
- Enforce strong passwords
- Force periodic password changes
- Keep users from re-using old passwords
Many other steps exist and are often service or application-dependent.
4.4.3 Monitoring Service Logs
Log files are the records that a computer stores to keep track of important events. Kernel, services, and application events are all recorded in log files. It is very important for an administrator to periodically review the logs of a computer to keep it healthy. By monitoring Linux log files, an administrator gains a clear picture of the computer’s performance, security status, and any underlying issues. Log file analysis allows an administrator to guard against upcoming issues before they occur.
In Linux, log files can be categorized as:
- Application logs
- Event logs
- Service logs
- System logs
Some logs contain information about daemons that are running in the Linux system. A daemon is a background process that runs without the need for user interaction. For example, the System Security Services Daemon (SSSD) manages remote access and authentication for single sign-on capabilities.
The table lists a few popular Linux log files and their functions
| Linux Log File | Description |
|---|---|
| /var/log/messages |
|
| /var/log/auth.log |
|
| /var/log/secure |
|
| /var/log/boot.log |
|
| /var/log/dmesg |
|
| /var/log/kern.log |
|
| /var/log/cron |
|
| /var/log/mysqld.log or /var/log/mysql.log |
|
The command output shows a portion of /var/log/messages log file. Each line represents a logged event. The timestamps at the beginning of the lines mark the moment the event took place.
[analyst@secOps ~]$ sudo cat /var/log/messages Mar 20 15:28:45 secOps kernel: Linux version 4.15.10-1-ARCH (builduser@heftig-18961) (gcc version 7.3.1 20180312 (GCC)) #1 SMP PREEMPT Thu Mar 15 12:24:34 UTC 2018 Mar 20 15:28:45 secOps kernel: Command line: BOOT_IMAGE=/boot/vmlinuz-linux root=UUID=07c6b457-3f39-4ddf-bfd8-c169e8a877b2 rw quiet Mar 20 15:28:45 secOps kernel: KERNEL supported cpus: Mar 20 15:28:45 secOps kernel: Intel GenuineIntel Mar 20 15:28:45 secOps kernel: AMD AuthenticAMD Mar 20 15:28:45 secOps kernel: Centaur CentaurHauls Mar 20 15:28:45 secOps kernel: x86/fpu: Supporting XSAVE feature 0x001: 'x87 floating point registers' Mar 20 15:28:45 secOps kernel: x86/fpu: Supporting XSAVE feature 0x002: 'SSE registers' Mar 20 15:28:45 secOps kernel: x86/fpu: Supporting XSAVE feature 0x004: 'AVX registers' Mar 20 15:28:45 secOps kernel: x86/fpu: xstate_offset[2]: 576, xstate_sizes[2]: 256 Mar 20 15:28:45 secOps kernel: x86/fpu: Enabled xstate features 0x7, context size is 832 bytes, using 'standard' format. Mar 20 15:28:45 secOps kernel: e820: BIOS-provided physical RAM map: Mar 20 15:28:45 secOps kernel: BIOS-e820: [mem 0x0000000000000000-0x000000000009fbff] usable Mar 20 15:28:45 secOps kernel: BIOS-e820: [mem 0x000000000009fc00-0x000000000009ffff] reserved Mar 20 15:28:45 secOps kernel: BIOS-e820: [mem 0x00000000000f0000-0x00000000000fffff] reserved Mar 20 15:28:45 secOps kernel: BIOS-e820: [mem 0x0000000000100000-0x000000003ffeffff] usable Mar 20 15:28:45 secOps kernel: BIOS-e820: [mem 0x000000003fff0000-0x000000003fffffff] ACPI data Mar 20 15:28:45 secOps kernel: BIOS-e820: [mem 0x00000000fec00000-0x00000000fec00fff] reserved Mar 20 15:28:45 secOps kernel: BIOS-e820: [mem 0x00000000fee00000-0x00000000fee00fff] reserved Mar 20 15:28:45 secOps kernel: BIOS-e820: [mem 0x00000000fffc0000-0x00000000ffffffff] reserved Mar 20 15:28:45 secOps kernel: NX (Execute Disable) protection: active Mar 20 15:28:45 secOps kernel: random: fast init done Mar 20 15:28:45 secOps kernel: SMBIOS 2.5 present. Mar 20 15:28:45 secOps kernel: DMI: innotek GmbH VirtualBox/VirtualBox, BIOS VirtualBox 12/01/2006 Mar 20 15:28:45 secOps kernel: Hypervisor detected: KVM Mar 20 15:28:45 secOps kernel: e820: last_pfn = 0x3fff0 max_arch_pfn = 0x400000000 Mar 20 15:28:45 secOps kernel: MTRR: Disabled Mar 20 15:28:45 secOps kernel: x86/PAT: MTRRs disabled, skipping PAT initialization too. Mar 20 15:28:45 secOps kernel: CPU MTRRs all blank - virtualized system.
4.4.4 Lab – Locating Log Files
In this lab, you will get familiar with locating and manipulating Linux log files.
4.4.4 Lab – Locating Log Files
4.5 The Linux File System
4.5.1 The File System Types in Linux
There are many different kinds of file systems, varying in properties of speed, flexibility, security, size, structure, logic and more. It is up to the administrator to decide which file system type best suits the operating system and the files it will store.
The table lists a few file system types commonly found and supported by Linux.
| Linux File System | Description |
|---|---|
| ext2 (second extended file system) |
|
| ext3 (third extended file system) |
|
| ext4 (fourth extended file system) |
|
| NFS (Network File System) |
|
| CDFS (Compact Disc File System) | CDFS was created specifically for optical disk media. |
| Swap File System |
|
| HFS Plus or HFS+ (Hierarchical File System Plus) |
|
| APFS (Apple File System) | An updated file system that is used by Apple devices. It provides strong encryption and is optimized for flash and solid-state drives. |
| Master Boot Record (MBR) |
|
Mounting is the term used for the process of assigning a directory to a partition. After a successful mount operation, the file system contained on the partition is accessible through the specified directory. In this context, the directory is called the mounting point for that file system. Windows users may be familiar with a similar concept; the drive letter.
The command output shows the output of the mount command issued in the Cisco CyberOPS VM.
[analyst@secOps ~]$ mount proc on /proc type proc (rw,nosuid,nodev,noexec,relatime) sys on /sys type sysfs (rw,nosuid,nodev,noexec,relatime) dev on /dev type devtmpfs (rw,nosuid,relatime,size=494944k,nr_inodes=123736,mode=755) run on /run type tmpfs (rw,nosuid,nodev,relatime,mode=755) /dev/sda1 on / type ext4 (rw,relatime) securityfs on /sys/kernel/security type securityfs (rw,nosuid,nodev,noexec,relatime) tmpfs on /dev/shm type tmpfs (rw,nosuid,nodev) devpts on /dev/pts type devpts (rw,nosuid,noexec,relatime,gid=5,mode=620,ptmxmode=000) tmpfs on /sys/fs/cgroup type tmpfs (ro,nosuid,nodev,noexec,mode=755) cgroup2 on /sys/fs/cgroup/unified type cgroup2 (rw,nosuid,nodev,noexec,relatime,nsdelegate) cgroup on /sys/fs/cgroup/systemd type cgroup (rw,nosuid,nodev,noexec,relatime,xattr,name=systemd) pstore on /sys/fs/pstore type pstore (rw,nosuid,nodev,noexec,relatime) none on /sys/fs/bpf type bpf (rw,nosuid,nodev,noexec,relatime,mode=700) cgroup on /sys/fs/cgroup/rdma type cgroup (rw,nosuid,nodev,noexec,relatime,rdma) cgroup on /sys/fs/cgroup/cpu,cpuacct type cgroup (rw,nosuid,nodev,noexec,relatime,cpu,cpuacct) cgroup on /sys/fs/cgroup/blkio type cgroup (rw,nosuid,nodev,noexec,relatime,blkio) cgroup on /sys/fs/cgroup/hugetlb type cgroup (rw,nosuid,nodev,noexec,relatime,hugetlb) cgroup on /sys/fs/cgroup/cpuset type cgroup (rw,nosuid,nodev,noexec,relatime,cpuset) cgroup on /sys/fs/cgroup/devices type cgroup (rw,nosuid,nodev,noexec,relatime,devices) cgroup on /sys/fs/cgroup/pids type cgroup (rw,nosuid,nodev,noexec,relatime,pids) cgroup on /sys/fs/cgroup/memory type cgroup (rw,nosuid,nodev,noexec,relatime,memory) cgroup on /sys/fs/cgroup/net_cls,net_prio type cgroup (rw,nosuid,nodev,noexec,relatime,net_cls,net_prio) cgroup on /sys/fs/cgroup/perf_event type cgroup (rw,nosuid,nodev,noexec,relatime,perf_event) cgroup on /sys/fs/cgroup/freezer type cgroup (rw,nosuid,nodev,noexec,relatime,freezer) systemd-1 on /proc/sys/fs/binfmt_misc type autofs (rw,relatime,fd=29,pgrp=1,timeout=0,minproto=5,maxproto=5,direct,pipe_ino=11792) debugfs on /sys/kernel/debug type debugfs (rw,nosuid,nodev,noexec,relatime) tracefs on /sys/kernel/tracing type tracefs (rw,nosuid,nodev,noexec,relatime) hugetlbfs on /dev/hugepages type hugetlbfs (rw,relatime,pagesize=2M) mqueue on /dev/mqueue type mqueue (rw,nosuid,nodev,noexec,relatime) tmpfs on /tmp type tmpfs (rw,nosuid,nodev)
When issued with no options, mount returns the list of file systems currently mounted in a Linux computer. While many of the file systems shown are out of the scope of this course, notice the root file system (highlighted). The root file system is represented by the “/” symbol and holds all files in the computer by default. It is also shown in the output that the root file system was formatted as ext4 and occupies the first partition of the first drive (/dev/sda1).
4.5.2 Linux Roles and File Permissions
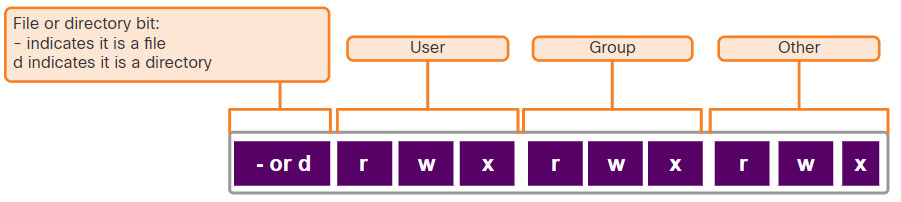
In Linux, most system entities are treated as files. In order to organize the system and enforce boundaries within the computer, Linux uses file permissions. File permissions are built into the file system structure and provide a mechanism to define permissions on every file. Every file in Linux carries its file permissions, which define the actions that the owner, the group, and others can perform with the file. The possible permission rights are Read, Write and Execute. The ls command with the -l parameter lists additional information about the file.
Consider the output of the ls -l command in the command output.
[analyst@secOps ~]$ ls -l space.txt -rwxrw-r-- 1 analyst staff 253 May 20 12:49 space.txt (1)(2)(3)(4)(5)(6)(7) [analyst@secOps ~]$
The output provides a lot of information about the file space.txt.
The first field of the output displays the permissions that are associated with space.txt (-rwxrw-r–). File permissions are always displayed in the User, Group, and Other order.
The file space.txt in has the following permissions:
- The dash (-) means that this is a file. For directories, the first dash would be a “d”.
- The first set of characters is for user permission (rwx). The user, analyst, who owns the file can Read, Write and eXecute the file.
- The second set of characters is for group permissions (rw-). The group, staff, who owns the file can Read and Write to the file.
- The third set of characters is for any other user or group permissions (r–). Any other user or group on the computer can only Read the file.
The second field defines the number of hard links to the file (the number 1 after the permissions). A hard link creates another file with a different name linked to the same place in the file system (called an inode). This is in contrast to a symbolic link, which is discussed on the next page.
The third and fourth field display the user (analyst) and group (staff) who own the file, respectively.
The fifth field displays the file size in bytes. The space.txt file has 253 bytes.
The sixth field displays the date and time of the last modification.
The seventh field displays the file name.
The figure shows a breakdown of file permissions in Linux.
Use octal values to define permissions.
| Binary | Octal | Permission | Description |
|---|---|---|---|
| 000 | 0 | — | No access |
| 001 | 1 | –x | Execute only |
| 010 | 2 | -w- | Write only |
| 011 | 3 | -wx | Write and Execute |
| 100 | 4 | r– | Read only |
| 101 | 5 | r-x | Read and Execute |
| 110 | 6 | rw- | Read and Write |
| 111 | 7 | rwx | Read, Write and Execute |
File permissions are a fundamental part of Linux and cannot be broken. A user has only the rights to a file that the file permissions allow. The only user that can override file permission on a Linux computer is the root user. Because the root user has the power to override file permissions, the root user can write to any file. Because everything is treated as a file, the root user has full control over a Linux computer. Root access is often required before performing maintenance and administrative tasks. Because of the power of the root user, root credentials should use strong passwords and not be shared with anyone other than system administrators and other high-level users.
4.5.3 Hard Links and Symbolic Links
A hard link is another file that points to the same location as the original file. Use the command ln to create a hard link. The first argument is the existing file and the second argument is the new file. As shown in the command output, the file space.txt is linked to space.hard.txt and the link field now shows 2.
[analyst@secOps ~]$ ln space.txt space.hard.txt [analyst@secOps ~]$ [analyst@secOps ~]$ ls -l space* -rw-r--r-- 2 analyst analyst 239 May 7 18:18 space.hard.txt -rw-r--r-- 2 analyst analyst 239 May 7 18:18 space.txt [analyst@secOps ~]$ [analyst@secOps ~]$ echo "Testing hard link" >> space.txt [analyst@secOps ~]$ [analyst@secOps ~]$ ls -l space* -rw-r--r-- 2 analyst analyst 257 May 7 18:19 space.hard.txt -rw-r--r-- 2 analyst analyst 257 May 7 18:19 space.txt [analyst@secOps ~]$ [analyst@secOps ~]$ rm space.hard.txt [analyst@secOps ~]$ [analyst@secOps ~]$ more space.txt Space... The final frontier… These are the voyages of the Starship Enterprise. Its continuing mission: - To explore strange new worlds… - To seek out new life; new civilizations… - To boldly go where no one has gone before! Testing hard link [analyst@secOps ~]$
Both files point to the same location in the file system. If you change one file, the other is changed, as well. The echo command is used to add some text to space.txt. Notice that the file size for both space.txt and space.hard.txt increased to 257 bytes. If you delete the space.hard.txt with the rm command (remove), the space.txt file still exists, as verified with the more space.txt command.
A symbolic link, also called a symlink or soft link, is similar to a hard link in that applying changes to the symbolic link will also change the original file. As shown in the command output below, use the ln command option -s to create a symbolic link.
[analyst@secOps ~]$ echo "Hello World!" > test.txt [analyst@secOps ~]$ [analyst@secOps ~]$ ln -s test.txt mytest.txt [analyst@secOps ~]$ [analyst@secOps ~]$ echo "It's a lovely day!" >> mytest.txt [analyst@secOps ~]$ [analyst@secOps ~]$ more test.txt Hello World! It's a lovely day! [analyst@secOps ~]$ [analyst@secOps ~]$ rm test.txt [analyst@secOps ~]$ [analyst@secOps ~]$ more mytest.txt more: stat of mytest.txt failed: No such file or directory [analyst@secOps ~]$ [analyst@secOps ~]$ ls -l mytest.txt lrwxrwxrwx 1 analyst analyst 8 May 7 20:17 mytest.txt -> test.txt [analyst@secOps ~]$
Notice that adding a line of text to test.txt also adds the line to mytest.txt. However, unlike a hard link, deleting the original text.txt file means that mytext.txt is now linked to a file that no longer exists, as shown with the more mytest.txt and ls -l mytest.txt commands.
Although symbolic links have a single point of failure (the underlying file), symbolic links have several benefits over hard links:
- Locating hard links is more difficult. Symbolic links show the location of the original file in the ls -l command, as shown in the last line of output in the previous command output (mytest.txt -> test.txt).
- Hard links are limited to the file system in which they are created. Symbolic links can link to a file in another file system.
- Hard links cannot link to a directory because the system itself uses hard links to define the hierarchy of the directory structure. However, symbolic links can link to directories.
4.5.4 Lab – Navigating the Linux Filesystem and Permission Settings
In this lab, you will familiarize yourself with Linux filesystems.
4.5.4 Lab – Navigating the Linux Filesystem and Permission Settings
4.6 Working with the Linux GUI
4.6.1 X Window System
The graphical interface present in most Linux computers is based on the X Window System. Also known as X or X11, X Window is a windowing system designed to provide the basic framework for a GUI. X includes functions for drawing and moving windows on the display device and interacting with a mouse and keyboard.
X works as a server which allows a remote user to use the network to connect, start a graphical application, and have the graphical window open on the remote terminal. While the application itself runs on the server, the graphical aspect of it is sent by X over the network and displayed on the remote computer.
Notice that X does not specify the user interface, leaving it to other programs, such as window managers, to define all the graphical components. This abstraction allows for great flexibility and customization as graphical components such as buttons, fonts, icons, window borders, and color schemes are all defined by the user application. Because of this separation, the Linux GUI varies greatly from distribution to distribution. Examples of window managers are Gnome and KDE. While the look and feel of window managers vary, the main components are still present.
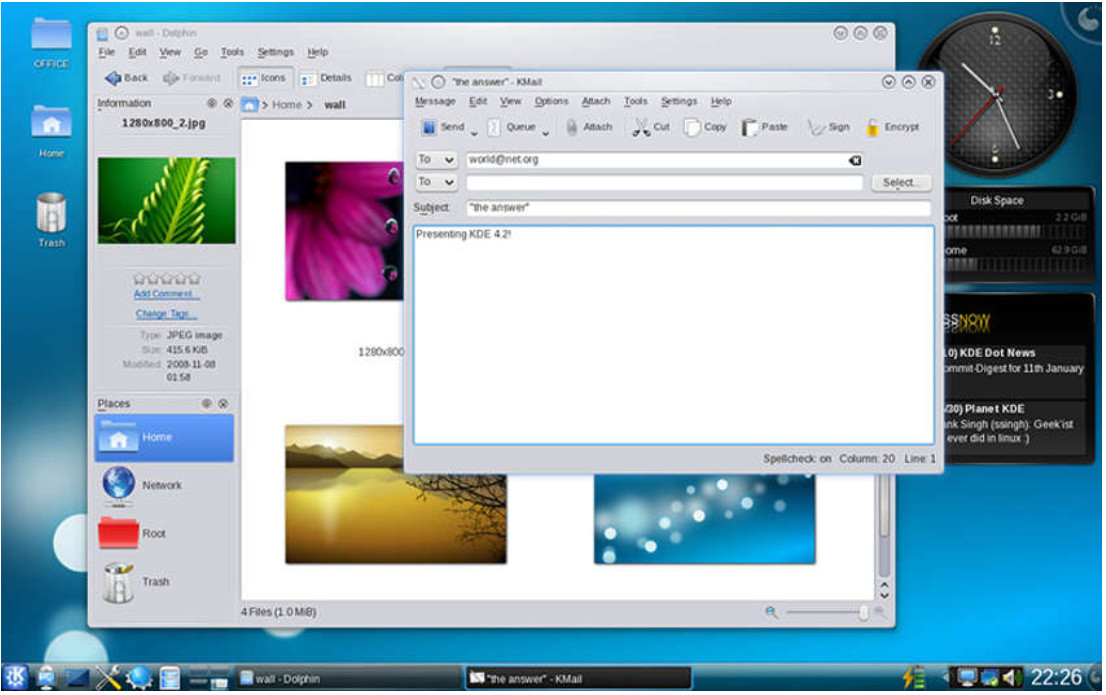
The figure displays the Gnome Window Manager.

This figure displays the KDE Windows Manager.
4.6.2 The Linux GUI
Although an operating system does not require a GUI to function, GUIs are considered more user-friendly than the CLI. The Linux GUI as a whole can be easily replaced by the user. As a result of the large number of Linux distributions, this chapter focuses on Ubuntu when covering Linux because it is a very popular and user-friendly distribution.
Ubuntu Linux uses Gnome 3 as its default GUI. The goal of Gnome 3 is to make Ubuntu even more user-friendly. The table lists the main UI components of Unity.
The figure shows the location of some of the features of the Ubuntu Gnome 3 Desktop.
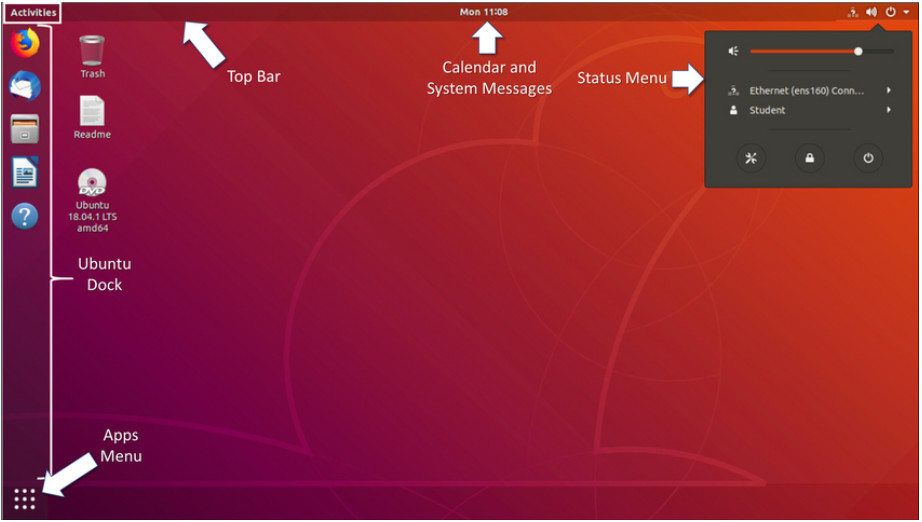
| UI Component | Description |
|---|---|
| Apps Menu |
|
| Ubuntu Dock |
|
| Top Bar |
|
| Calendar and System Message Tray |
|
| Activities |
|
| Status Menu |
|
4.7 Working on a Linux Host
4.7.1 Installing and Running Applications on a Linux Host
Many end-user applications are complex programs written in compiled languages. To aid in the installation process, Linux often includes programs called package managers. A package is the term used to refer to a program and all its supporting files. By using a package manager to install a package, all the necessary files are placed in the correct file system location.
Package managers vary depending on Linux distributions. For example, pacman is used by Arch Linux while dpkg (Debian package) and apt (Advanced Packaging Tool) are used in Debian and Ubuntu Linux distributions. For this course, we will use the pacman package manager.
The command output shows the output of a few apt-get commands used in Debian distributions.
analyst@cuckoo:~$ sudo apt-get update [sudo] password for analyst: Hit:l http://us.archive.ubuntu.com/ubuntu xenial InRelease Get:2 http://us.archive.ubuntu.com/ubuntu xenial-updates InRelease [102 kB] Get:3 http://security.ubuntu.com/ubuntu xenial-security InRelease [102 kB] Get:4 http://us.archive.ubuntu.com/ubuntu xenial-backports InRelease [102 kB] Get:5 http://us.archive.ubuntu.com/ubuntu xenial-updates/main amd64 Packages [534 kB]
The apt-get update command is used to get the package list from the package repository and update the local package database. The apt-get upgrade command is used to update all currently installed packages to their latest versions.
4.7.2 Keeping the System Up to Date
Also known as patches, OS updates are released periodically by OS companies to address any known vulnerabilities in their operating systems. While companies have update schedules, the release of unscheduled OS updates can happen when a major vulnerability is found in the OS code. Modern operating systems will alert the user when updates are available for download and installation, but the user can check for updates at any time.
The following table compares Arch Linux and Debian / Ubuntu Linux distribution commands to perform package system basic operations.
| Task | Arch | Debian / Ubuntu |
|---|---|---|
| Install a package by name | pacman -S | apt install |
| Remove a package by name | pacman -Rs | apt remove |
| Update a local package | pacman -Syy | apt-get update |
| Upgrade all currently installed packages | pacman -Syu | apt-get upgrade |
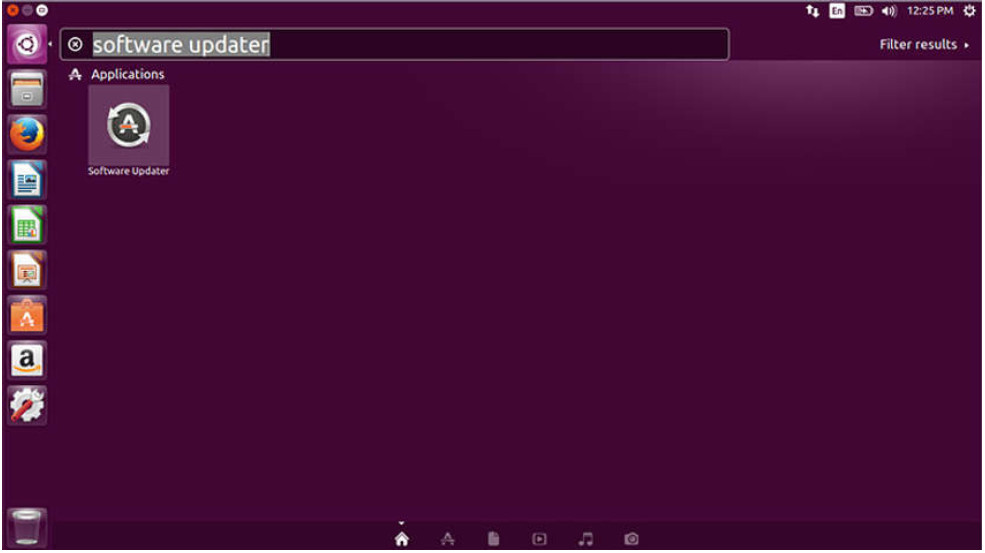
A Linux GUI can also be used to manually check and install updates. In Ubuntu for example, to install updates you would click Dash Search Box, type software updater, and then click the Software Updater icon, as shown in the figure.
4.7.3 Processes and Forks
A process is a running instance of a computer program. Multitasking operating systems can execute many processes at the same time.
Forking is a method that the kernel uses to allow a process to create a copy of itself. Processes need a way to create new processes in multitasking operating systems. The fork operation is the only way of doing so in Linux.
Forking is important for many reasons. One of them relates to process scalability. Apache, a popular web server, is a good example. By forking itself, Apache is able to serve a large number of requests with fewer system resources than a single-process-based server.
When a process calls a fork, the caller process becomes the parent process, with the newly created process referred to as its child. After the fork, the processes are, to some extent, independent processes; they have different process IDs but run the same program code.
The table lists three commands that are used to manage processes.
| Command | Description |
|---|---|
| ps |
|
| top |
|
| kill |
|
The command output shows the output of the top command on a Linux computer.
[analyst@secOps ~]$ top top - 11:29:16 up 0 min, 1 user, load average: 1.09, 0.31, 0.11 Tasks: 119 total, 1 running, 118 sleeping, 0 stopped, 0 zombie %Cpu(s): 5.4 us, 2.0 sy, 0.0 ni, 87.4 id, 2.7 wa, 1.4 hi, 1.0 si, 0.0 st MiB Mem : 982.8 total, 67.9 free, 765.8 used, 149.1 buff/cache MiB Swap: 0.0 total, 0.0 free, 0.0 used. 39.3 avail Mem PID USER PR NI VIRT RES SHR S %CPU %MEM TIME+ COMMAND 729 analyst 20 0 2652376 284472 61076 S 2.7 28.3 0:06.75 Web Con+ 570 analyst 20 0 2691388 215728 62404 S 2.0 21.4 0:06.99 firefox 357 root 20 0 267972 91960 18468 S 1.3 9.1 0:01.63 Xorg 461 analyst 20 0 322208 21000 7480 S 1.3 2.1 0:00.67 xfce4-p+ 121 root 20 0 0 0 0 S 0.7 0.0 0:00.43 kswapd0 1 root 20 0 174376 4196 1688 S 0.3 0.4 0:00.66 systemd 294 root 20 0 245036 11876 868 S 0.3 1.2 0:00.34 python2+ 539 analyst 20 0 150824 660 0 S 0.3 0.1 0:00.02 VBoxCli+ 800 analyst 20 0 477768 18968 9800 S 0.3 1.9 0:00.30 xfce4-t+ 2 root 20 0 0 0 0 S 0.0 0.0 0:00.00 kthreadd 3 root 0 -20 0 0 0 I 0.0 0.0 0:00.00 rcu_gp 4 root 0 -20 0 0 0 I 0.0 0.0 0:00.00 rcu_par+ 5 root 20 0 0 0 0 I 0.0 0.0 0:00.00 kworker+ 6 root 0 -20 0 0 0 I 0.0 0.0 0:00.00 kworker+ 7 root 20 0 0 0 0 I 0.0 0.0 0:00.00 kworker+ 8 root 0 -20 0 0 0 I 0.0 0.0 0:00.00 mm_perc+ 9 root 20 0 0 0 0 S 0.0 0.0 0:00.02 ksoftir+ [analyst@secOps ~]$
4.7.4 Malware on a Linux Host
Linux malware includes viruses, Trojan horses, worms, and other types of malware that can affect the operating system. Due to a number of design components such as file system structure, file permissions, and user account restrictions, Linux operating systems are generally regarded as better protected against malware.
While arguably better protected, Linux is not immune to malware. Many vulnerabilities have been found and exploited in Linux. These range from server software to kernel vulnerabilities. Attackers are able to exploit these vulnerabilities and compromise the target. Because Linux is open source, fixes and patches are often made available within hours of the discovery of such problems.
If a malicious program is executed, it will cause damage, regardless of the platform. A common Linux attack vector is its services and processes. Vulnerabilities are frequently found in server and process code running on computers connected to the network. An outdated version of the Apache web server could contain an unpatched vulnerability which can be exploited by an attacker, for example. Attackers often probe open ports to assess the version and nature of the server running on that port. With that knowledge, attackers can research if there are any known issues with that particular version of that particular server to support the attack. As with most vulnerabilities, keeping the computer updated and closing any unused services and ports is a good way to reduce the opportunities for attack in a Linux computer.
The command output shows an attacker using the Telnet command to probe the nature and version of a web server (port 80).
analyst@secOps ~]$ telnet 209.165.200.224 80 Trying 209.165.200.224... Connected to 209.165.200.224. Escape character is ‘^]’. <type anything to force an HTTP error response> HTTP/1.1 400 Bad Request Server: nginx/1.12.0 Date: Wed, 17 May 2017 14:27:30 GMT Content-Type: text/html Content-Length: 173 Connection: close <html> <head><title>400 Bad Request</title></head> <body bgcolor="white"> <center><h1>400 Bad Request</h1></center> <hr><center>nginx/1.12.0</center> </body> </html > Connection closed by foreign host. analyst@secOps ~]$
The attacker has learned that the server in question is running nginx version 1.12.0. The next step would be to research known vulnerabilities in the nginx 1.12.0 code.
Note: You will learn more about this attack later in the course.
4.7.5 Rootkit Check
A rootkit is a type of malware that is designed to increase an unauthorized user’s privileges or grant access to portions of the software that should not normally be allowed. Rootkits are also often used to secure a backdoor to a compromised computer.
The installation of a rootkit can be automated (done as part of an infection) or an attacker can manually install it after compromising a computer. A rootkit is destructive because it changes kernel code and its modules, changing the most fundamental operations of the OS itself. With such a deep level of compromise, rootkits can hide the intrusion, remove any installation tracks, and even tamper with troubleshooting and diagnostic tools so that their output now hides the presence of the rootkit. While a few Linux vulnerabilities through history have allowed rootkit installation via regular user accounts, the vast majority of rootkit compromises require root or administrator access.
Because the very nature of the computer is compromised, rootkit detection can be very difficult. Typical detection methods often include booting the computer from trusted media such as a diagnostics operating system live CD. The compromised drive is mounted and, from the trusted system toolset, trusted diagnostic tools can be launched to inspect the compromised file system. Inspection methods include behavioral-based methods, signature scanning, difference scanning, and memory dump analysis.
Rootkit removal can be complicated and often impossible, especially in cases where the rootkit resides in the kernel; re-installation of the operating system is usually the only real solution to the problem. Firmware rootkits usually require hardware replacement.
chkrootkit is a popular Linux-based program designed to check the computer for known rootkits. It is a shell script that uses common Linux tools such as strings and grep to compare the signatures of core programs. It also looks for discrepancies as it traverses the /proc file system comparing the signatures found there with the output of ps.
While helpful, keep in mind that programs to check for rootkits are not 100% reliable.
The command output shows the output of chkrootkit on an Ubuntu Linux.
analyst@cuckoo:~$ sudo ./chkrootkit [sudo] password for analyst: ROOTDIR is ‘/’ Checking 'amd’... not found Checking 'basename’... not infected Checking 'biff’... not found Checking 'chfn’... not infected Checking 'chsh'... not infected Checking 'cron'... not infected Checking 'crontab’... not infected Checking 'date'... not infected Checking 'du'... not infected Checking 'dirname'... not infected Checking 'echo'... not infected Checking 'egrep’... not infected Checking 'env'— not infected Checking 'find'... not infected Checking 'fingerd'... not found Checking 'gpm'... not found Checking 'grep'... not infected Checking 'hdparm’... not infected Checking 'su'... not infected Checking 'ifconfig'... not infected Checking 'inetd’... not tested Checking 'inetdconf’... not found
4.7.6 Piping Commands
Although command line tools are usually designed to perform a specific, well-defined task, many commands can be combined to perform more complex tasks by a technique known as piping. Named after its defining character, the pipe (|), piping consists of chaining commands together, feeding the output of one command into the input of another.
For example, the ls command is used to display all the files and directories of a given directory. The grep command compares searches through a file or text looking for the specified string. If found, grep displays the entire contents of the folder where the string was found.
The two commands, ls and grep, can be piped together to filter out the output of ls. This is shown in the output of the ls -l | grep host command and the ls -l | grep file command.
[analyst@secOps ~]$ ls -l total 40 drwxr-xr-x 2 analyst analyst 4096 Mar 22 2018 Desktop drwxr-xr-x 3 analyst analyst 4096 April 2 14:44 Downloads -rw-r--r-- 1 analyst analyst 9 May 20 10:51 hostfile1.txt -rw-r--r-- 1 analyst analyst 9 May 20 10:51 hostfile2.txt -rw-r--r-- 1 analyst analyst 9 May 20 10:52 hostfile3.txt drwxr-xr-x 9 analyst analyst 4096 Jul 19 2018 lab.support.files -rw-r--r-- 1 analyst analyst 19 May 20 10:53 mytest.com -rw-r--r-- 1 analyst analyst 228844 May 20 10:54 rkhunter-1.4.6-1-any.pkg.tar.xz drwxr-xr-x 2 analyst analyst 4096 Mar 21 2018 second_drive -rw-r--r-- 1 analyst analyst 257 May 20 10:52 space.txt [analyst@secOps ~]$ [analyst@secOps ~]$ ls -l | grep host -rw-r--r-- 1 analyst analyst 9 May 20 10:51 hostfile1.txt -rw-r--r-- 1 analyst analyst 9 May 20 10:51 hostfile2.txt -rw-r--r-- 1 analyst analyst 9 May 20 10:52 hostfile3.txt [analyst@secOps ~]$ [analyst@secOps ~]$ ls -l | grep file -rw-r--r-- 1 analyst analyst 9 May 20 10:51 hostfile1.txt -rw-r--r-- 1 analyst analyst 9 May 20 10:51 hostfile2.txt -rw-r--r-- 1 analyst analyst 9 May 20 10:52 hostfile3.txt drwxr-xr-x 9 analyst analyst 4096 Jul 19 2018 lab.support.files [analyst@secOps ~]$
4.7.7 Video – Applications, Rootkits, and Piping Commands
Play the video to view a demonstration of installing and updating applications, checking for a rootkit, and using piping commands.
4.8 Linux Basics Summary
4.8.1 What Did I Learn in this Module?
Linux Basics
Linux is a fast, reliable, and small open-source operating system. It requires few hardware resources to run and is highly customizable. It is designed to be used on networks. The Linux kernel is distributed by different organizations with different tools and software packages. A customized version of Linux that is called Security Onion contains software and tools that are designed for use in network security monitoring by cybersecurity analysts. Kali Linux is another customized Linux distribution that has numerous tools that are designed for network security penetration testing.
Working in the Linux Shell
In Linux, the user communicates with the operating system through a GUI or a command-line interface (CLI), or shell. If a GUI is running, the shell is accessed through at terminal application such as xterm or gnome terminal. Linux commands are programs that perform a specific task. The man command, followed by a specific command, provides documentation for that command. It is important to know at least basic Linux commands, file and directory commands, and commands for working with text files. In Linux everything is treated is if it were a file, including the memory, disks, monitor, and directories.
Linux Servers and Clients
Servers are computers that have software installed that enables them to provide services to client computers across the network. Some services provide access to external resources such as files, email, and web pages, to clients upon request. Other services run internally and perform tasks such as log management, memory management, or disk scanning. To enable a computer to provide multiple services, ports are used. A port is a reserved network resource that “listens” for requests by clients. While the port number that is used by a service can be configured, most services listen on default “well-known” ports. Client software applications are designed to communicate with specific types of servers. Web browsers are designed to communicate with web servers by using the HTTP protocol on port 80. FTP clients communicate with FTP servers to transfer files.
Basic Server Administration
In Linux, servers are managed by using configuration files. Various settings can be modified and saved in configuration files. When a service is started, it looks at its configuration file(s) to know how it should run. There is no rule for the way configuration files are written. Configuration file formatting depends on the creator of the server software. Linux devices should be secured by using proven methods to protect the device and administrative access. This is known as hardening devices. One way to harden a device is to maintain passwords, configure enhanced login features, and implement secure remote login with SSH. It is also very important to keep the operating system up to date. Other ways to harden a device are to force periodic password changes, enforce strong passwords, and to prevent reuse of passwords. Finally, Linux clients and servers use logfiles to record the operation of the system and important events. A number of different logfiles are maintained including application logs, event logs, service logs, and system logs. Server logs record activities that are conducted by remote users who access system services. It is important to know the location of different logs in the Linux file system so that they can be accessed and monitored for problems.
The Linux File System
Linux supports a number of different file systems that vary by speed, flexibility, security, size, structure, logic, and more. Some of the file systems that are supported by Linux are ext2, ext3, ext4, NFS, and CDFS. File systems are mounted on partitions and accessed through mounting points, or directories. Windows drive letters are examples of mounting points. The mount command can be used to display details of the file systems that are currently mounted on a Linux computer. The root file system is represented by the “/” symbol. It contains all of the files in the computer by default. Linux uses file permissions to control who is permitted to have different types of access to files and directories. Permissions include read (r), write (w), and execute (x). Files and directories have permissions that are assigned for users, groups, and others. The permissions for files and folders are displayed with the ls -l command. This command also displays the links for a file. Hard links create another file with a different name that is linked to the same place in the file system. The owner of the file and the group for the file are also displayed along with the date and time of the last modification to the file. File permissions are powerful features of the Linux file system and can’t be violated. Only the root user can override file permissions. Because of the power of the root user, root access should be carefully controlled. Hard links are created with the ln command. Changes to one of the hard-linked files are also made to the original file. Symbolic links, or symlinks, are similar to hard links in that a change to the linked file is reflected in the original file. Symbolic links have several advantages over hard links.
Working with Linux GUI
The X Windows, or X11, system is a basic software framework that includes functions for creating, controlling, and configuring a windows GUI in a point-and-click interface. Different vendors use the X Windows system to create different windows manager GUIs for Linux. Examples of windows managers are Gnome and KDE. The Ubuntu Linux distribution uses Gnome 3 by default. The Gnome 3 desktop consists of the Apps Menu, Ubuntu Dock, Top Bar, Calendar and System Message tray, the Activities area, and the Status Menu.
Working on a Linux Host
In order to install applications on Linux hosts, programs called package managers are used. Packages are software applications and all of their supporting files. Package managers are extremely helpful for installing complex software applications from centralized package repositories that are accessible over the internet. Different Linux distributions use different package managers. For example, Arch Linux uses pacman, Debian uses dpkg as the base package manager and apt to communicate with dpkg. Ubuntu also uses apt. Package manager CLI commands are used to install, remove, and update software packages. Upgrade commands upgrade all currently installed packages. Package management can also be performed in a GUI. Software processes are instances of computer programs that are running. Multitasking operating systems can run many processes at the same time. Forking is a method that the kernel uses to allow a running process to copy itself. The ps command lists the running processes, top displays information about running processes dynamically, and kill is used to remove, restart, or pause running processes. While Linux is considered to be better protected against malicious software (malware) than other operating systems, it is still susceptible to Trojan horses, worms, and other types of malware. Linux is usually attacked through its services and processes. Out of date software is often vulnerable to attack. Threat actors can probe a device for open ports that are linked to out of date server processes. With this knowledge, attacks can be launched. It is important to keep the operating system and its components and applications up to date. The chkrootkit program is designed to detect rootkit malware. Rootkits are deep level malware programs that are very difficult to detect and remove. They can change the fundamental operation of the operating system itself and can be used to create unauthorized access to systems. Piping commands uses the “|” symbol to chain different commands together by using the output of one command as the input for another.
