14.0 Introduction
14.0.1 Why Should I Take this Module?
By now you know why our networks are attacked. In this module you will learn about common threats and attacks.
14.0.2 What Will I Learn in this Module?
Module Title: Common Threats and Attacks
Module Objective: Explain the various types of threats and attacks.
| Topic Title | Topic Objective |
|---|---|
| Malware | Describe types of malware. |
| Common Network Attacks – Reconnaissance, Access, and Social Engineering | Explain reconnaissance, access, and social engineering network attacks. |
| Network Attacks – Denial of Service, Buffer Overflows, and Evasion | Explain Denial of Service, buffer overflow, and evasion attacks. |
14.1 Malware
14.1.1 Types of Malware
End devices are especially prone to malware attacks. Therefore, the focus of this topic is on threats to end devices. Malware is short for malicious software or malicious code. It is code or software that is specifically designed to damage, disrupt, steal, or generally inflict some other “bad” or illegitimate action on data, hosts, or networks. It is important to know about malware because threat actors and online criminals frequently try to trick users into installing malware to help exploit security gaps. In addition, malware morphs so rapidly that malware-related security incidents are extremely common because antimalware software cannot be updated quickly enough to stop the new threats.
Play the animation to view examples of the three most common types of malware; virus, worm, and Trojan horse.
14.1.2 Viruses
A virus is a type of malware that spreads by inserting a copy of itself into another program. After the program is run, viruses then spread from one computer to another, infecting the computers. Most viruses require human help to spread. For example, when someone connects an infected USB drive to their PC, the virus will enter the PC. The virus may then infect a new USB drive, and spread to new PCs. Viruses can lay dormant for an extended period and then activate at a specific time and date.
A simple virus may install itself at the first line of code in an executable file. When activated, the virus might check the disk for other executables so that it can infect all the files it has not yet infected. Viruses can be harmless, such as those that display a picture on the screen, or they can be destructive, such as those that modify or delete files on the hard drive. Viruses can also be programmed to mutate to avoid detection.
Most viruses are now spread by USB memory drives, CDs, DVDs, network shares, and email. Email viruses are a common type of virus.
14.1.3 Trojan Horses
The term Trojan horse originated from Greek mythology. Greek warriors offered the people of Troy (the Trojans) a giant hollow horse as a gift. The Trojans brought the giant horse into their walled city, unaware that it contained many Greek warriors. At night, after most Trojans were asleep, the warriors burst out of the horse, opened the city gates, and allowed a sizeable force to enter and take over the city.
Trojan horse malware is software that appears to be legitimate, but it contains malicious code which exploits the privileges of the user that runs it. Often, Trojans are found attached to online games.
Users are commonly tricked into loading and executing the Trojan horse on their systems. While playing the game, the user will not notice a problem. In the background, the Trojan horse has been installed on the user’s system. The malicious code from the Trojan horse continues operating even after the game has been closed.
The Trojan horse concept is flexible. It can cause immediate damage, provide remote access to the system, or access through a back door. It can also perform actions as instructed remotely, such as “send me the password file once per week.” This tendency of malware to send data back to the cybercriminal highlights the need to monitor outbound traffic for attack indicators.
Custom-written Trojan horses, such as those with a specific target, are difficult to detect.
14.1.4 Trojan Horse Classification
Types of Trojan Horses
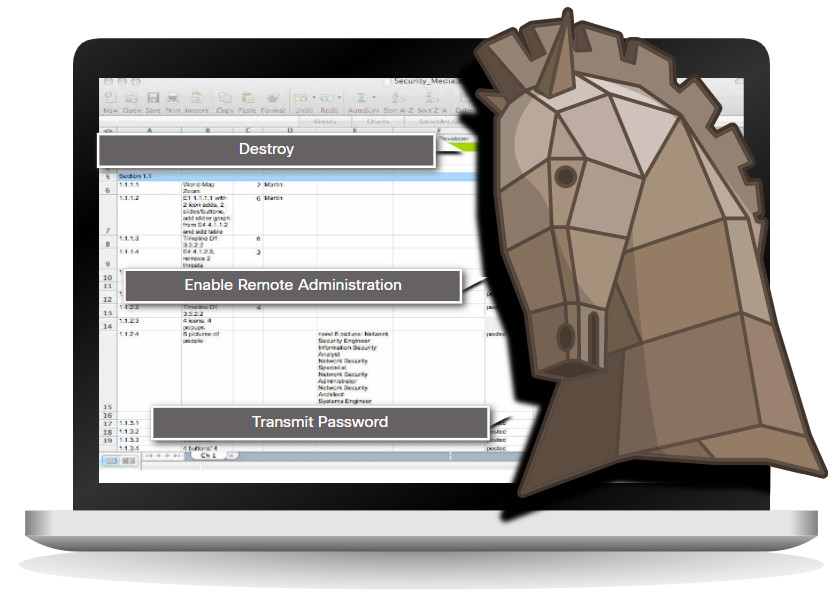
Trojan horses are usually classified according to the damage that they cause, or the manner in which they breach a system, as shown in the figure.
| Type of Trojan Horse | Description |
|---|---|
| Remote-access | Enables unauthorized remote access. |
| Data-sending | Provides the threat actor with sensitive data, such as passwords. |
| Destructive | Corrupts or deletes files. |
| Proxy | Uses the victim’s computer as the source device to launch attacks and perform other illegal activities. |
| FTP | Enables unauthorized file transfer services on end devices. |
| Security software disabler | Stops antivirus programs or firewalls from functioning. |
| Denial of Service (DoS) | Slows or halts network activity. |
| Keylogger | Actively attempts to steal confidential information, such as credit card numbers, by recording keystrokes entered into a web form. |
14.1.5 Worms
Computer worms are similar to viruses because they replicate and can cause the same type of damage. Specifically, worms replicate themselves by independently exploiting vulnerabilities in networks. Worms can slow down networks as they spread from system to system.
Whereas a virus requires a host program to run, worms can run by themselves. Other than the initial infection, they no longer require user participation. After a host is infected, the worm is able to spread very quickly over the network.
Worms are responsible for some of the most devastating attacks on the internet. In 2001, the Code Red worm had initially infected 658 servers. Within 19 hours, the worm had infected over 300,000 servers.
The initial infection of the SQL Slammer worm is known as the worm that ate the internet. SQL Slammer was a denial of service (DoS) attack that exploited a buffer overflow bug in Microsoft’s SQL Server. At its peak, the number of infected servers doubled in size every 8.5 seconds. This is why it was able to infect 250,000+ hosts within 30 minutes. When it was released on the weekend of January 25, 2003, it disrupted the internet, financial institutions, ATM cash machines, and more. Ironically, a patch for this vulnerability had been released 6 months earlier. The infected servers did not have the updated patch applied. This was a wake-up call for many organizations to implement a security policy requiring that updates and patches be applied in a timely fashion.
Worms share similar characteristics. They all exploit an enabling vulnerability, have a way to propagate themselves, and they all contain a payload.
14.1.6 Worm Components
Despite the mitigation techniques that have emerged over the years, worms have continued to evolve and pose a persistent threat. Worms have become more sophisticated over time, but they still tend to be based on exploiting weaknesses in software applications.
Common Worm Pattern
Most worm attacks consist of three components, as listed in the animation above.
- Enabling vulnerability – A worm installs itself using an exploit mechanism, such as an email attachment, an executable file, or a Trojan horse, on a vulnerable system.
- Propagation mechanism – After gaining access to a device, the worm replicates itself and locates new targets.
- Payload – Any malicious code that results in some action is a payload. Most often this is used to create a backdoor that allows a threat actor access to the infected host or to create a DoS attack.
Worms are self-contained programs that attack a system to exploit a known vulnerability. Upon successful exploitation, the worm copies itself from the attacking host to the newly exploited system and the cycle begins again. Their propagation mechanisms are commonly deployed in a way that is difficult to detect.
The propagation technique used by the Code Red worm is shown in the figure.
Code Red Worm Propagation
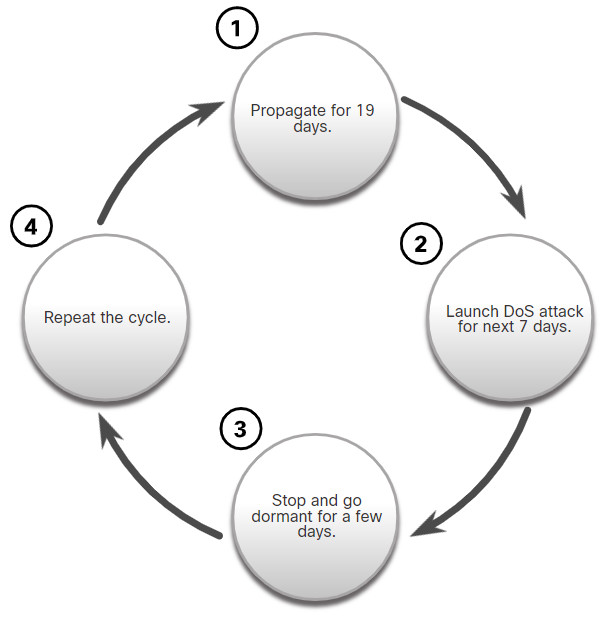
Note: Worms never really stop spreading on the internet. After they are released, worms continue to propagate until all possible sources of infection are properly patched.
14.1.7 Ransomware
Threat actors have used viruses, worms, and Trojan horses to carry their payloads and for other malicious reasons. However, malware continues to evolve.
Currently, the most dominating malware is ransomware. Ransomware is malware that denies access to the infected computer system or its data. The cybercriminals then demand payment to release the computer system.
Ransomware has evolved to become the most profitable malware type in history. In the first half of 2016, ransomware campaigns targeting both individual and enterprise users became more widespread and potent.
There are dozens of ransomware variants. Ransomware frequently uses an encryption algorithm to encrypt system files and data. The majority of known ransomware encryption algorithms cannot be easily decrypted, leaving victims with little option but to pay the asking price. Payments are typically paid in Bitcoin because users of bitcoin can remain anonymous. Bitcoin is an open-source, digital currency that nobody owns or controls.
Email and malicious advertising, also known as malvertising, are vectors for ransomware campaigns. Social engineering is also used, as when cybercriminals who identify themselves as security technicians call homes and persuade users to connect to a website that downloads the ransomware to the user’s computer..
14.1.8 Other Malware
These are some examples of the varieties of modern malware:
| Type of Malware | Description |
|---|---|
| Spyware | Used to gather information about a user and send the information to another entity without the user’s consent. Spyware can be a system monitor, Trojan horse, Adware, tracking cookies, and key loggers. |
| Adware | Displays annoying pop-ups to generate revenue for its author. The malware may analyze user interests by tracking the websites visited. It can then send pop-up advertising pertinent to those sites. |
| Scareware | Includes scam software which uses social engineering to shock or induce anxiety by creating the perception of a threat. It is generally directed at an unsuspecting user and attempts to persuade the user to infect a computer by taking action to address the bogus threat. |
| Phishing | Attempts to convince people to divulge sensitive information. Examples include receiving an email from their bank asking users to divulge their account and PIN numbers. |
| Rootkits | Installed on a compromised system. After it is installed, it continues to hide its intrusion and provide privileged access to the threat actor. |
This list will continue to grow as the internet evolves. New malware will always be developed. A major goal of cybersecurity operations is to learn about new malware and how to promptly mitigate it.
14.1.9 Common Malware Behaviors
Cybercriminals continually modify malware code to change how it spreads and infects computers. However, most produce similar symptoms that can be detected through network and device log monitoring.
Computers infected with malware often exhibit one or more of the following symptoms:
- Appearance of strange files, programs, or desktop icons
- Antivirus and firewall programs are turning off or reconfiguring settings
- Computer screen is freezing or system is crashing
- Emails are spontaneously being sent without your knowledge to your contact list
- Files have been modified or deleted
- Increased CPU and/or memory usage
- Problems connecting to networks
- Slow computer or web browser speeds
- Unknown processes or services running
- Unknown TCP or UDP ports open
- Connections are made to hosts on the Internet without user action
- Strange computer behavior
Note: Malware behavior is not limited to the above list.
14.1.11 Lab – Anatomy of Malware
In this lab, you will research and analyze some recent malware.
14.1.11 Lab – Anatomy of Malware
14.2 Common Network Attacks – Reconnaissance, Access, and Social Engineering
14.2.1 Types of Network Attacks
Malware is a means to get a payload delivered. When it is delivered and installed, the payload can be used to cause a variety of network-related attacks from the inside. Threat actors can also attack the network from outside.
Why do threat actors attack networks? There are many motives including money, greed, revenge, or political, religious, or sociological beliefs. Network security professionals must understand the types of attacks used to counter these threats to ensure the security of the LAN.
To mitigate attacks, it is useful to first categorize the various types of attacks. By categorizing network attacks, it is possible to address types of attacks rather than individual attacks.
Although, there is no standardized way of categorizing network attacks, the method used in this course classifies attacks in three major categories.
- Reconnaissance Attacks
- Access Attacks
- DoS Attacks
14.2.2 Reconnaissance Attacks
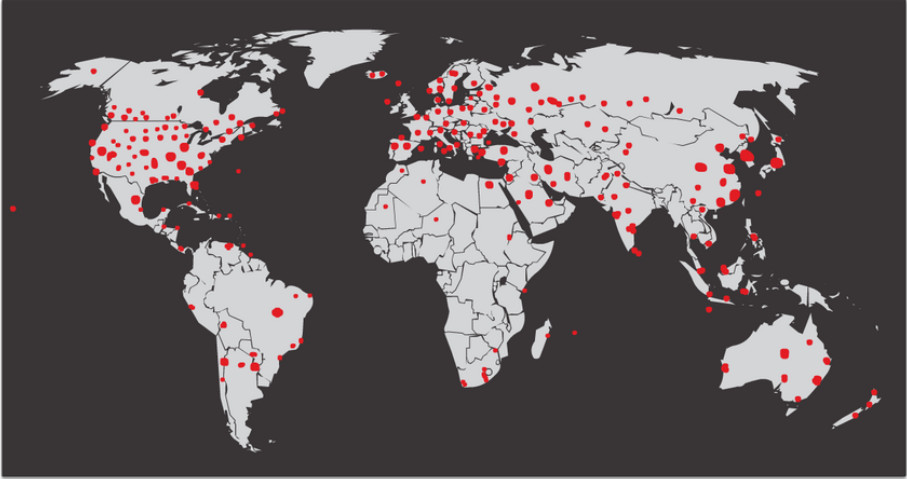
Reconnaissance is information gathering. It is analogous to a thief surveying a neighborhood by going door-to-door pretending to sell something. What the thief is actually doing is looking for vulnerable homes to break into, such as unoccupied residences, residences with easy-to-open doors or windows, and those residences without security systems or security cameras.
Threat actors use reconnaissance (or recon) attacks to do unauthorized discovery and mapping of systems, services, or vulnerabilities. Recon attacks precede access attacks or DoS attacks.
Some of the techniques used by malicious threat actors to conduct reconnaissance attacks are described in the table.
| Technique | Description |
|---|---|
| Perform an information query of a target | The threat actor is looking for initial information about a target. Various tools can be used, including the Google search, organizations website, whois, and more. |
| Initiate a ping sweep of the target network | The information query usually reveals the target’s network address. The threat actor can now initiate a ping sweep to determine which IP addresses are active. |
| Initiate a port scan of active IP addresses | This is used to determine which ports or services are available. Examples of port scanners include Nmap, SuperScan, Angry IP Scanner, and NetScanTools. |
| Run vulnerability scanners | This is to query the identified ports to determine the type and version of the application and operating system that is running on the host. Examples of tools include Nipper, Secuna PSI, Core Impact, Nessus v6, SAINT, and Open VAS. |
| Run exploitation tools | The threat actor now attempts to discover vulnerable services that can be exploited. A variety of vulnerability exploitation tools exist including Metasploit, Core Impact, Sqlmap, Social Engineer Toolkit, and Netsparker. |
Click each button to view the progress of a reconnaissance attack from information query, to ping sweep, to port scan.
14.2.3 Video – Reconnaissance Attacks
14.2.4 Access Attacks
Access attacks exploit known vulnerabilities in authentication services, FTP services, and web services. The purpose of this type of attack is to gain entry to web accounts, confidential databases, and other sensitive information.
Threat actors use access attacks on network devices and computers to retrieve data, gain access, or to escalate access privileges to administrator status.
Password Attacks
In a password attack, the threat actor attempts to discover critical system passwords using various methods. Password attacks are very common and can be launched using a variety of password cracking tools.
Spoofing Attacks
In spoofing attacks, the threat actor device attempts to pose as another device by falsifying data. Common spoofing attacks include IP spoofing, MAC spoofing, and DHCP spoofing. These spoofing attacks will be discussed in more detail later in this module
Other Access attacks include:
- Trust exploitations
- Port redirections
- Man-in-the-middle attacks
- Buffer overflow attacks
Click each button to view an illustration and explanation of these access attacks.
14.2.5 Video – Access and Social Engineering Attacks
Watch the video to see a demonstration of some types of access and social engineering attacks.
14.2.6 Social Engineering Attacks
Social engineering is an access attack that attempts to manipulate individuals into performing actions or divulging confidential information. Some social engineering techniques are performed in-person while others may use the telephone or internet.
Social engineers often rely on people’s willingness to be helpful. They also prey on people’s weaknesses. For example, a threat actor could call an authorized employee with an urgent problem that requires immediate network access. The threat actor could appeal to the employee’s vanity, invoke authority using name-dropping techniques, or appeal to the employee’s greed.
Information about social engineering techniques is shown in the table.
| Social Engineering Attack | Description |
|---|---|
| Pretexting | A threat actor pretends to need personal or financial data to confirm the identity of the recipient. |
| Phishing | A threat actor sends fraudulent email which is disguised as being from a legitimate, trusted source to trick the recipient into installing malware on their device, or to share personal or financial information. |
| Spear phishing | A threat actor creates a targeted phishing attack tailored for a specific individual or organization. |
| Spam | Also known as junk mail, this is unsolicited email which often contains harmful links, malware, or deceptive content. |
| Something for Something | Sometimes called “Quid pro quo”, this is when a threat actor requests personal information from a party in exchange for something such as a gift. |
| Baiting | A threat actor leaves a malware infected flash drive in a public location. A victim finds the drive and unsuspectingly inserts it into their laptop, unintentionally installing malware. |
| Impersonation | In this type of attack, a threat actor pretends to be someone else to gain the trust of a victim. |
| Tailgating | This is where a threat actor quickly follows an authorized person into a secure location to gain access to a secure area. |
| Shoulder surfing | This is where a threat actor inconspicuously looks over someone’s shoulder to steal their passwords or other information. |
| Dumpster diving | This is where a threat actor rummages through trash bins to discover confidential documents. |
The Social Engineer Toolkit (SET) was designed to help white hat hackers and other network security professionals create social engineering attacks to test their own networks. It is a set of menu-based tools that help launch social engineering attacks. The SET is for educational purposes only. It is freely available on the internet.
Enterprises must educate their users about the risks of social engineering, and develop strategies to validate identities over the phone, via email, or in person.
The figure shows recommended practices that should be followed by all users.
Recommended Social Engineering Protection Practices

14.2.7 Strengthening the Weakest Link
Cybersecurity is only as strong as its weakest link. Since computers and other internet-connected devices have become an essential part of our lives, they no longer seem new or different. People have become very casual in their use of these devices and rarely think about network security. The weakest link in cybersecurity can be the personnel within an organization, and social engineering a major security threat. Because of this, one of the most effective security measures that an organization can take is to train its personnel and create a “security-aware culture.”
14.2.8 Lab – Social Engineering
In this lab, you will research examples of social engineering and identify ways to recognize and prevent it.
14.2.8 Lab – Social Engineering
14.3 Network Attacks – Denial of Service, Buffer Overflows, and Evasion
14.3.1 Video – Denial of Service Attacks
Watch the video to learn about denial of service attacks.
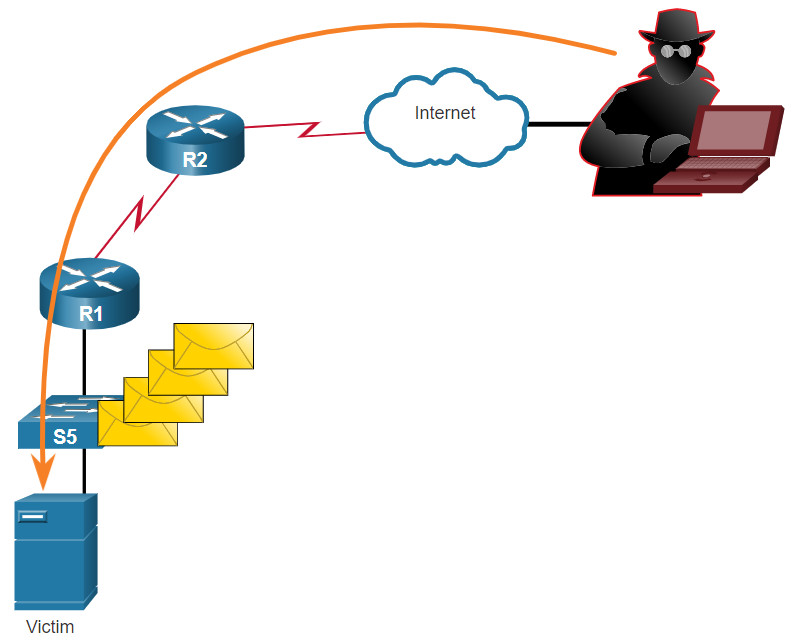
14.3.2 DoS and DDoS Attacks
A Denial of Service (DoS) attack creates some sort of interruption of network services to users, devices, or applications. There are two major types of DoS attacks:
- Overwhelming Quantity of Traffic – The threat actor sends an enormous quantity of data at a rate that the network, host, or application cannot handle. This causes transmission and response times to slow down. It can also crash a device or service.
- Maliciously Formatted Packets – The threat actor sends a maliciously formatted packet to a host or application and the receiver is unable to handle it. This causes the receiving device to run very slowly or crash.
Click each button for an illustration and explanation of DoS and DDoS attacks.
14.3.3 Components of DDoS Attacks
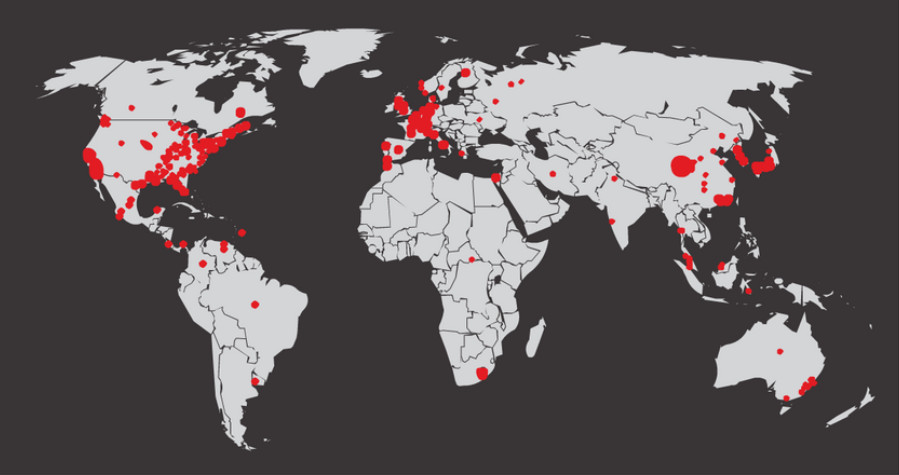
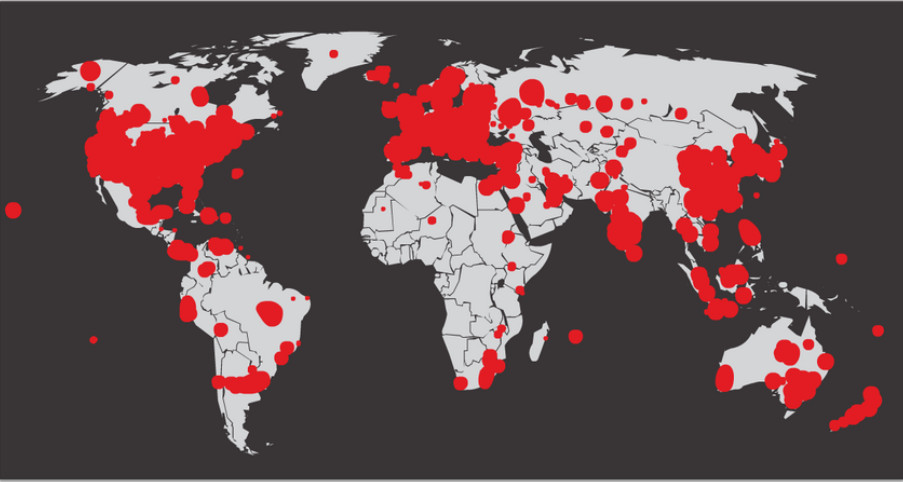
If threat actors can compromise many hosts, they can perform a Distributed DoS Attack (DDoS). DDoS attacks are similar in intent to DoS attacks, except that a DDoS attack increases in magnitude because it originates from multiple, coordinated sources, as shown in the figure. A DDoS attack can use hundreds or thousands of sources, as in IoT-based DDoS attacks.
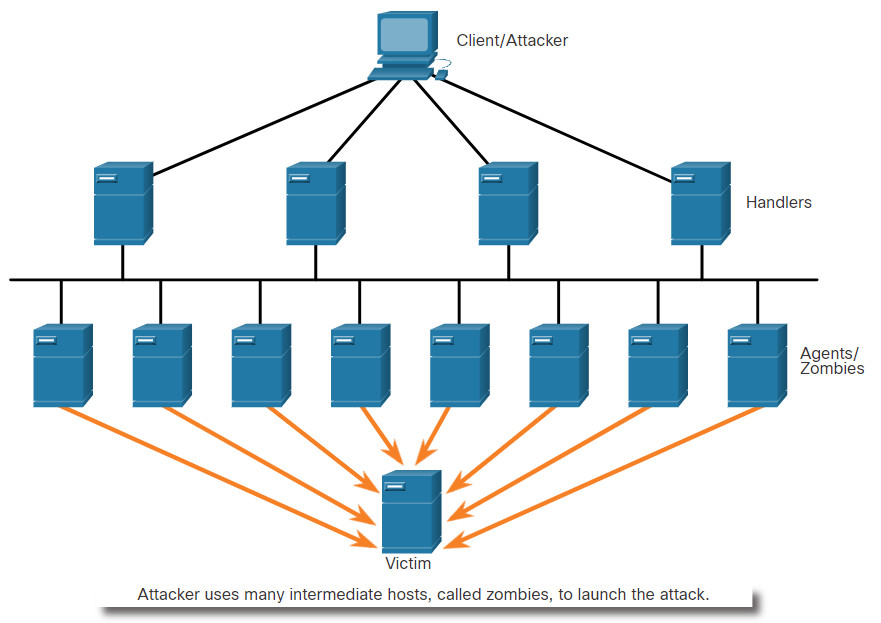
The following terms are used to describe components of a DDoS attack:
| Component | Description |
|---|---|
| zombies | This refers to a group of compromised hosts (i.e., agents). These hosts run malicious code referred to as robots (i.e., bots). The zombie malware continually attempts to self-propagate like a worm. |
| bots | Bots are malware that is designed to infect a host and communicate with a handler system. Bots can also log keystrokes, gather passwords, capture and analyze packets, and more. |
| botnet | This refers to a group of zombies that have been infected using self-propagating malware (i.e., bots) and are controlled by handlers. |
| handlers | This refers to a master command-and-control (CnC or C2) server controlling groups of zombies. The originator of a botnet can use Internet Relay Chat (IRC) or a web server on the C2 server to remotely control the zombies. |
| botmaster | This is the threat actor who is in control of the botnet and handlers. |
Note: There is an underground economy where botnets can be bought (and sold) for a nominal fee. This can provide threat actors with botnets of infected hosts ready to launch a DDoS attack against the target of choice.
14.3.4 Video – Mirai Botnet
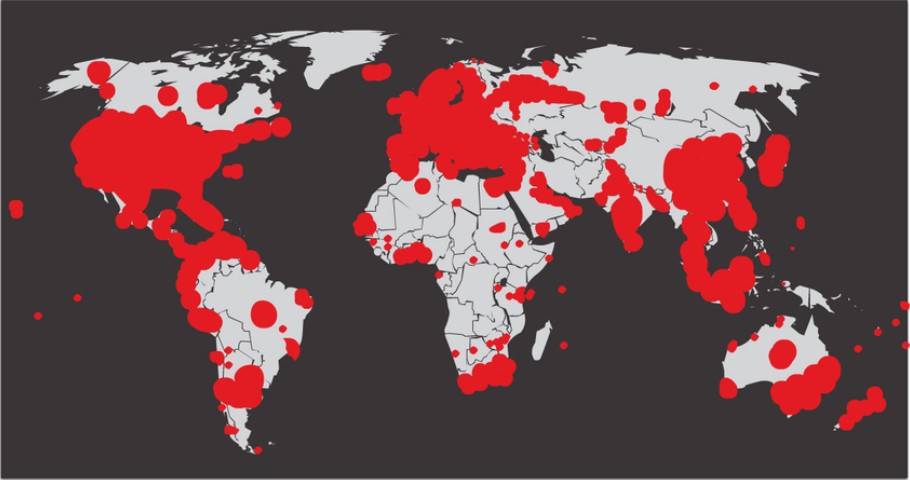
Mirai is malware that targeted IoT devices that are configured with default login information. Closed-circuit television (CCTV) cameras made up the majority of Mirai’s targets. Using a brute force dictionary attack, Mirai ran through a list of default usernames and passwords that were widely known on the internet.
- root/default
- root/1111
- root/54321
- admin/admin1234
- admin1/password
- guest/12345
- tech/tech
- support/support
After gaining successful access, Mirai targeted the Linux-based BusyBox utilities that run on these devices. These utilities were used to turn the devices into bots that could be remotely controlled as part of a botnet. The botnet was then used as part of a distributed denial of service (DDoS) attack. In September 2016, a Mirai botnet of over 152,000 CCTVs and digital video recorders (DVRs) was responsible for the largest DDoS attack known until that time. With peak traffic of over 1 Tb/s, it took down the hosting services of a France-based web hosting company.
In October 2016 the services of Dyn, a domain name service (DNS) provider, were attacked, causing internet outages for millions of users in the United States and Europe.
Play the video to view a demonstration of how a botnet-based DDoS attack makes services unavailable.
Note: In December 2017, three American threat actors pleaded guilty to conspiring to “conduct DDoS attacks against websites and web hosting companies located in the United States and abroad.” The three felons face up to 10 years in prison and $250,000 in fines.
14.3.5 Buffer Overflow Attack
The goal of a threat actor when using a buffer overflow DoS attack is to find a system memory-related flaw on a server and exploit it. Exploiting the buffer memory by overwhelming it with unexpected values usually renders the system inoperable, creating a DoS attack.
For example, a threat actor enters input that is larger than expected by the application running on a server. The application accepts the large amount of input and stores it in memory. The result is that it may consume the associated memory buffer and potentially overwrite adjacent memory, eventually corrupting the system and causing it to crash.
An early example of using malformed packets was the Ping of Death. In this legacy attack, the threat actor sent a ping of death, which was an echo request in an IP packet larger than the maximum packet size of 65,535 bytes. The receiving host would not be able to handle a packet of that size and it would crash.
Buffer overflow attacks are continually evolving. For instance, a remote denial of service attack vulnerability was recently discovered in Microsoft Windows 10. Specifically, a threat actor created malicious code to access out-of-scope memory. When this code is accessed by the Windows AHCACHE.SYS process, it attempts to trigger a system crash, denying service to the user. Search the Internet on “TALOS-2016-0191 blog” to go to the Cisco Talos threat intelligence website and read a description of such an attack.
Note: It is estimated that one third of malicious attacks are the result of buffer overflows.
14.3.6 Evasion Methods
Threat actors learned long ago that “to hide is to thrive”. This means their malware and attack methods are most effective when they are undetected. For this reason, many attacks use stealthy evasion techniques to disguise an attack payload. Their goal is to prevent detection by evading network and host defenses.
Some of the evasion methods used by threat actors include:
| Evasion Method | Description |
|---|---|
| Encryption and tunneling | This evasion technique uses tunneling to hide, or encryption to scramble, malware files. This makes it difficult for many security detection techniques to detect and identify the malware. Tunneling can mean hiding stolen data inside of legitimate packets. |
| Resource exhaustion | This evasion technique makes the target host too busy to properly use security detection techniques. |
| Traffic fragmentation | This evasion technique splits a malicious payload into smaller packets to bypass network security detection. After the fragmented packets bypass the security detection system, the malware is reassembled and may begin sending sensitive data out of the network. |
| Protocol-level misinterpretation | This evasion technique occurs when network defenses do not properly handle features of a PDU like a checksum or TTL value. This can trick a firewall into ignoring packets that it should check. |
| Traffic substitution | In this evasion technique, the threat actor attempts to trick an IPS by obfuscating the data in the payload. This is done by encoding it in a different format. For example, the threat actor could use encoded traffic in Unicode instead of ASCII. The IPS does not recognize the true meaning of the data, but the target end system can read the data. |
| Traffic insertion | Similar to traffic substitution, but the threat actor inserts extra bytes of data in a malicious sequence of data. The IPS rules miss the malicious data, accepting the full sequence of data. |
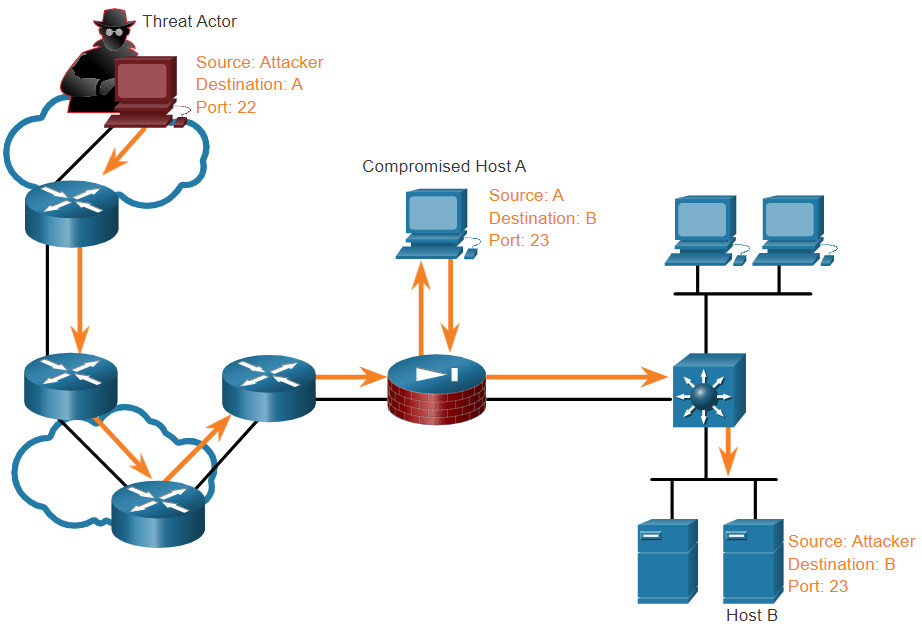
| Pivoting | This technique assumes the threat actor has compromised an inside host and wants to expand their access further into the compromised network. An example is a threat actor who has gained access to the administrator password on a compromised host and is attempting to login to another host using the same credentials. |
| Rootkits | A rootkit is a complex attacker tool used by experienced threat actors. It integrates with the lowest levels of the operating system. When a program attempts to list files, processes, or network connections, the rootkit presents a sanitized version of the output, eliminating any incriminating output. The goal of the rootkit is to completely hide the activities of the attacker on the local system. |
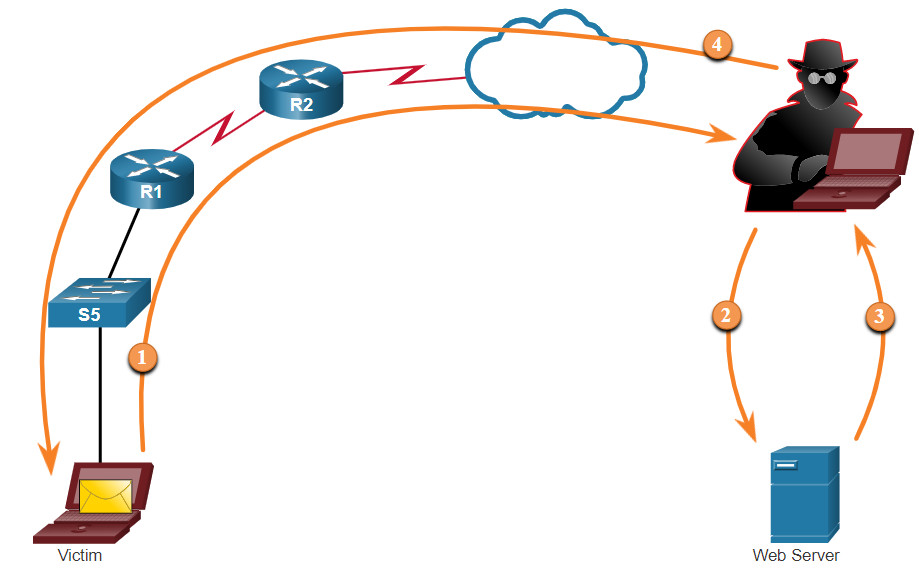
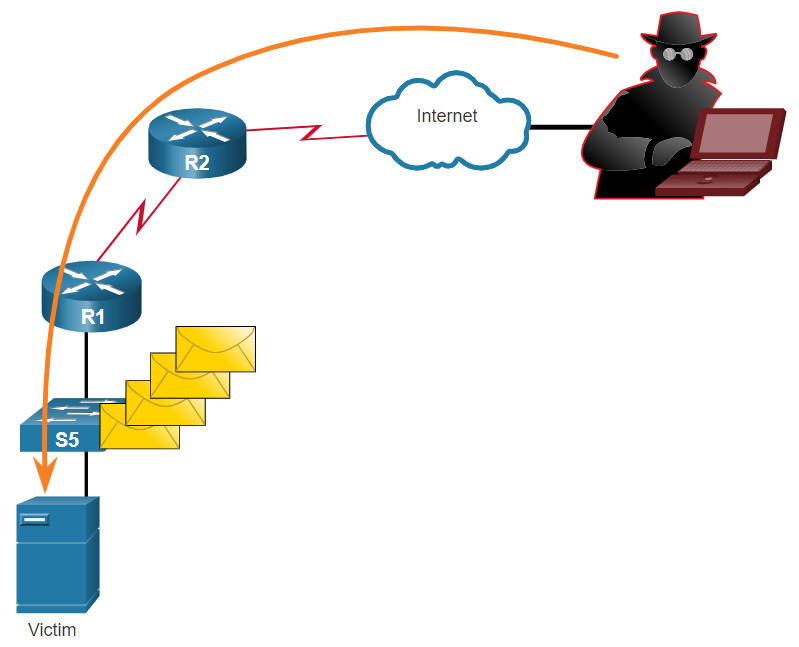
| Proxies | Network traffic can be redirected through intermediate systems in order to hide the ultimate destination for stolen data. In this way, known command-and-control not be blocked by an enterprise because the proxy destination appears benign. Additionally, if data is being stolen, the destination for the stolen data can be distributed among many proxies, thus not drawing attention to the fact that a single unknown destination is serving as the destination for large amounts of network traffic. |
New attack methods are constantly being developed. Network security personnel must be aware of the latest attack methods in order to detect them.
14.4 Common Threats and Attacks Summary
14.4.1 What Did I Learn in this Module?
Malware
Malware is short for malicious software or malicious code. Threat actors frequently try to trick users into installing malware to help exploit end device vulnerabilities. Often antimalware software cannot be updated quickly enough to stop new threats. Three common types are virus, worm, and Trojan horse. A virus is a type of malware that spreads by inserting a copy of itself into another program. Most viruses are spread through USB memory drives, CDs, DVDs, network shares, and email. Trojan horse malware is software that appears to be legitimate, but it contains malicious code that exploits the privileges of the user that runs it. Often, Trojans are found on online games. Trojan horses are usually classified according to the damage they cause. Types of Trojan horses include remote-access, data-sending, destructive, proxy, FTP, security software disabler, DoS, and keylogger. Worms are similar to viruses because they replicate and can cause the same type of damage. Viruses require a host program to run. Worms can run themselves. Most worm attacks consist of three components: enabling vulnerability, propagation mechanism, and payload. Currently, ransomware is the most dominant malware. It denies access to the infected system or its data. The cybercriminals then demand payment to release the computer system. Other malware examples include spyware, adware, scareware, phishing, and rootkits.
Common Network Attacks – Reconnaissance, Access, and Social Engineering
Threat actors can also attack the network from outside. To mitigate attacks, it is useful to categorize the various types of attacks. The three major categories are reconnaissance, access, and DoS attacks. Reconnaissance is information gathering. Threat actors do unauthorized discovery and mapping of systems, services, or vulnerabilities. Recon attacks precede access or DoS attacks. Some of the techniques used include the following: performing an information query of a target, initiating a ping sweep of the target network, initiating a port scan of active IP addresses, running vulnerability scanners, and running exploitation tools. Access attacks exploit known vulnerabilities in authentication services, FTP services, and web services. These attacks include password attacks, spoofing attacks, trust exploitation attacks, port redirections, man-in-the-middle attacks, and buffer overflow attacks. Social engineering is an access attack that attempts to manipulate individuals into performing unsafe actions or divulging confidential information. These attacks include pretexting, phishing, spear phishing, spam, something for something, baiting, impersonation, tailgating, shoulder surfing, and dumpster diving.
Network Attacks – Denial of Service, Buffer Overflows, and Evasion
DoS attacks create some sort of interruption of network services to users, devices, or applications. There are two major types: overwhelming quantity of traffic, and maliciously formatted packets. DDoS attacks are similar in intent to DoS attacks, except that the DDoS attack increases in magnitude because it originates from multiple, coordinated sources. The following terms are used to describe DDoS attacks: zombies, bots, botnet, handlers, and botmaster. Mirai is malware that targets IoT devices configured with default login information. Mirai uses a brute force dictionary attack. After successful access, Mirai targets the Linux-based BusyBox utilities that are designed for these devices. The goal of a threat actor when using a buffer overflow DoS attack is to find a system memory-related flaw on a server and exploit it. Exploiting the buffer memory by overwhelming it with unexpected values usually renders the system inoperable, creating a DoS attack. Many attacks use stealthy evasion techniques to disguise an attack payload. Evasion methods include encrypting and tunneling, resource exhaustion, traffic fragmentation, protocol-level misinterpretation, traffic substitution, traffic insertion, pivoting, rootkits, and proxies.