16.0 Introduction
16.0.1 Why Should I Take this Module?
Protocols are the foundation of data communications. For this reason they have been a target of threat actors for a very long time. Cybersecurity analysts must understand how threat actors use features of common protocols in cyberattacks.
This module provides an overview of the Layer 3 IP packet fields and the Layer 4 TCP and UDP segment fields, and discusses vulnerabilities of each.
16.0.2 What Will I Learn in this Module?
Module Title: Attacking the Foundation
Module Objective: Explain how TCP/IP vulnerabilities enable network attacks.
| Topic Title | Topic Objective |
|---|---|
| IP PDU Details | Explain the IPv4 and IPv6 header structure. |
| IP Vulnerabilities | Explain how IP vulnerabilities enable network attacks. |
| TCP and UDP Vulnerabilities | Explain how TCP and UDP vulnerabilities enable network attacks. |
16.1 IP PDU Details
16.1.1 IPv4 and IPv6
IP was designed as a Layer 3 connectionless protocol. It provides the necessary functions to deliver a packet from a source host to a destination host over an interconnected system of networks. The protocol was not designed to track and manage the flow of packets. These functions, if required, are performed primarily by TCP at Layer 4.
IP makes no effort to validate whether the source IP address contained in a packet actually came from that source. For this reason, threat actors can send packets using a spoofed source IP address. In addition, threat actors can tamper with the other fields in the IP header to carry out their attacks. Therefore, it is important for security analysts to understand the different fields in both the IPv4 and IPv6 headers.
16.1.2 The IPv4 Packet Header
The fields in the IPv4 packet header are shown in the figure.
IPv4 Packet Header
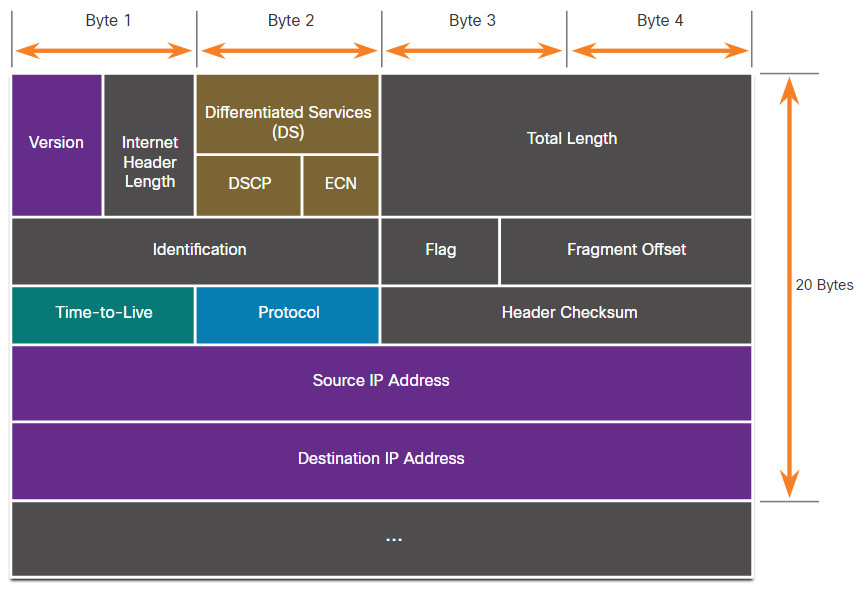
The table describes the IPv4 header fields.
| IPv4 Header Field | Description |
|---|---|
| Version |
|
| Internet Header length |
|
| Differentiated Services or DiffServ (DS) |
|
| Total length |
|
| Identification, Flag, and Fragment offset |
|
| Time-to-Live (TTL) |
|
| Protocol |
|
| Header checksum |
|
| Source IPv4 Address |
|
| Destination IPv4 Address |
|
| Options and Padding |
|
16.1.3 Video – Sample IPv4 Headers in Wireshark
Click Play in the figure to view a demonstration of examining IPv4 headers in a Wireshark capture.
16.1.4 The IPv6 Packet Header
There are eight fields in the IPv6 packet header, as shown in the figure.
IPv6 Packet Header
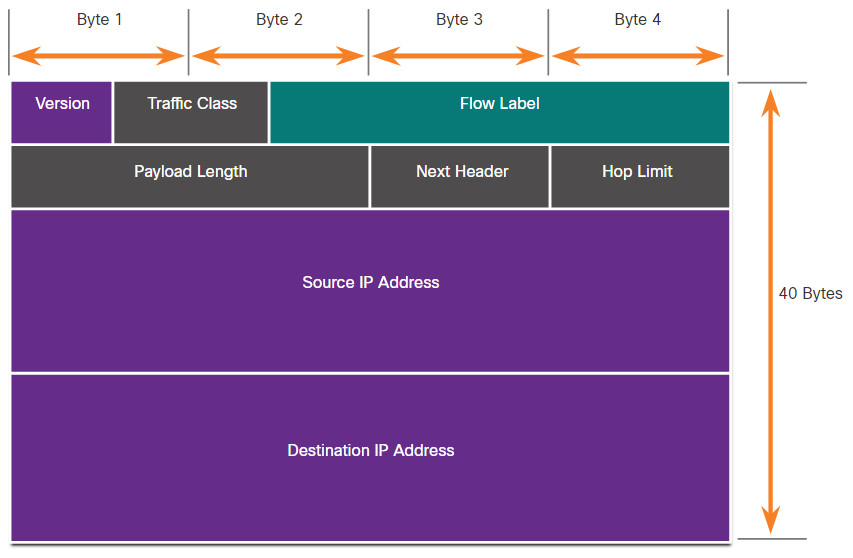
The table describes the IPv6 header fields.
| IPv6 Header Field | Description |
|---|---|
| Version |
|
| Traffic Class |
|
| Flow Label |
|
| Payload Length |
|
| Next Header |
|
| Hop Limit |
|
| Source IPv6 Address |
|
| Destination IPv6 Address |
|
An IPv6 packet may also contain extension headers (EH) that provide optional network layer information. Extension headers are optional and are placed between the IPv6 header and the payload. EHs are used for fragmentation, security, to support mobility, and more.
Unlike IPv4, routers do not fragment routed IPv6 packets.
16.1.5 Video – Sample IPv6 Headers in Wireshark
Click Play in the figure to view a demonstration of examining IPv6 headers in a Wireshark capture.
16.2 IP Vulnerabilities
16.2.1 IP Vulnerabilities
There are different types of attacks that target IP. The table lists some of the more common IP-related attacks.
| IP Attacks | Description |
|---|---|
| ICMP attacks | Threat actors use Internet Control Message Protocol (ICMP) echo packets (pings) to discover subnets and hosts on a protected network, to generate DoS flood attacks, and to alter host routing tables. |
| Denial-of-Service (DoS) attacks | Threat actors attempt to prevent legitimate users from accessing information or services. |
| Distributed Denial-of-Service (DDoS) attacks | Similar to a DoS attack, but features a simultaneous, coordinated attack from multiple source machines. |
| Address spoofing attacks | Threat actors spoof the source IP address in an attempt to perform blind spoofing or non-blind spoofing. |
| Man-in-the-middle attack (MiTM) | Threat actors position themselves between a source and destination to transparently monitor, capture, and control the communication. They could simply eavesdrop by inspecting captured packets or alter packets and forward them to their original destination. |
| Session hijacking | Threat actors gain access to the physical network, and then use an MiTM attack to hijack a session. |
16.2.2 ICMP Attacks
ICMP was developed to carry diagnostic messages and to report error conditions when routes, hosts, and ports are unavailable. ICMP messages are generated by devices when a network error or outage occurs. The ping command is a user-generated ICMP message, called an echo request, that is used to verify connectivity to a destination.
Threat actors use ICMP for reconnaissance and scanning attacks. This enables them to launch information-gathering attacks to map out a network topology, discover which hosts are active (reachable), identify the host operating system (OS fingerprinting), and determine the state of a firewall.
Threat actors also use ICMP for DoS and DDoS attacks, as shown in the ICMP flood attack in the figure.
ICMP Flood
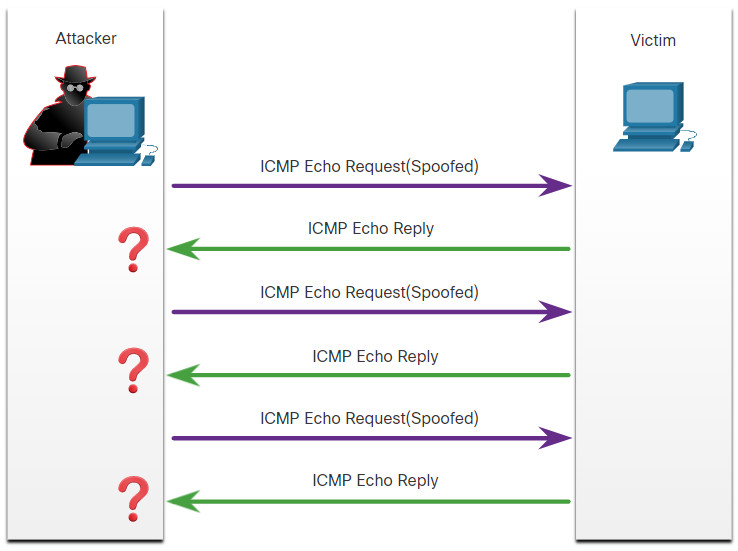
Note: ICMP for IPv4 (ICMPv4) and ICMP for IPv6 (ICMPv6) are susceptible to similar types of attacks.
The table lists common ICMP messages of interest to threat actors.
| ICMP Message | Description |
|---|---|
| ICMP echo request and echo reply | This is used to perform host verification and DoS attacks. |
| ICMP unreachable | This is used to perform network reconnaissance and scanning attacks. |
| ICMP mask reply | This is used to map an internal IP network. |
| ICMP redirects | This is used to lure a target host into sending all traffic through a compromised device and create a MiTM attack. |
| ICMP router discovery | This is used to inject bogus route entries into the routing table of a target host. |
Networks should have strict ICMP access control list (ACL) filtering on the network edge to avoid ICMP probing from the internet. Security analysts should be able to detect ICMP-related attacks by looking at captured traffic and log files. In the case of large networks, security devices, such as firewalls and intrusion detection systems (IDS), should detect such attacks and generate alerts to the security analysts.
16.2.3 Video – Amplification, Reflection, and Spoofing Attacks
Click Play in the figure to view a video about amplification, reflection, and spoofing attacks.
16.2.4 Amplification and Reflection Attacks
Threat actors often use amplification and reflection techniques to create DoS attacks. The example in the figure illustrates how an amplification and reflection technique called a Smurf attack is used to overwhelm a target host.
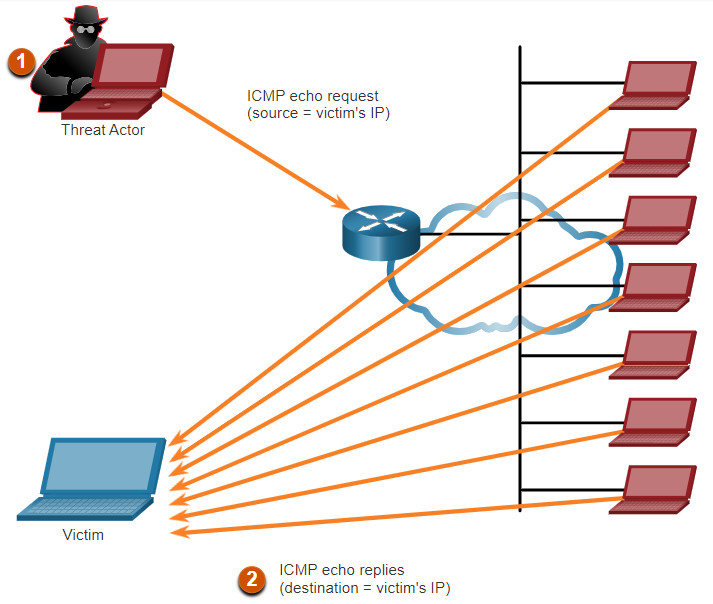
- Amplification – The threat actor forwards ICMP echo request messages to many hosts. These messages contain the source IP address of the victim.
- Reflection – These hosts all reply to the spoofed IP address of the victim to overwhelm it.
Note: Newer forms of amplification and reflection attacks such as DNS-based reflection and amplification attacks and Network Time Protocol (NTP) amplification attacks are now being used.
Threat actors also use resource exhaustion attacks. These attacks consume the resources of a target host to either to crash it or to consume the resources of a network.
16.2.5 Address Spoofing Attacks
IP address spoofing attacks occur when a threat actor creates packets with false source IP address information to either hide the identity of the sender, or to pose as another legitimate user. The threat actor can then gain access to otherwise inaccessible data or circumvent security configurations. Spoofing is usually incorporated into another attack such as a Smurf attack.
Spoofing attacks can be non-blind or blind:
- Non-blind spoofing – The threat actor can see the traffic that is being sent between the host and the target. The threat actor uses non-blind spoofing to inspect the reply packet from the target victim. Non-blind spoofing determines the state of a firewall and sequence-number prediction. It can also hijack an authorized session.
- Blind spoofing – The threat actor cannot see the traffic that is being sent between the host and the target. Blind spoofing is used in DoS attacks.
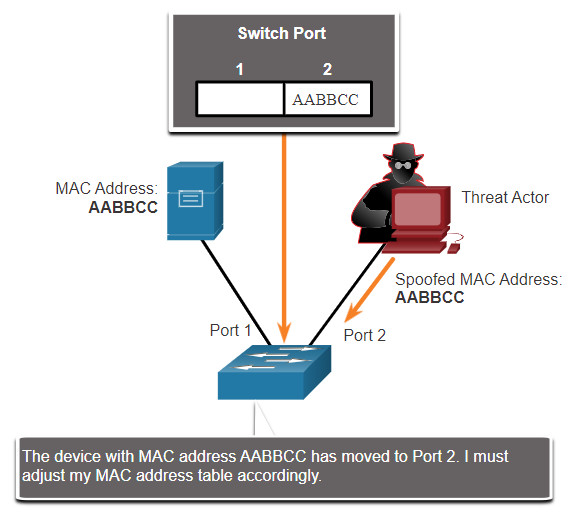
MAC address spoofing attacks are used when threat actors have access to the internal network. Threat actors alter the MAC address of their host to match another known MAC address of a target host, as shown in the figure. The attacking host then sends a frame throughout the network with the newly-configured MAC address. When the switch receives the frame, it examines the source MAC address.
Threat Actor Spoofs a Server’s MAC Address
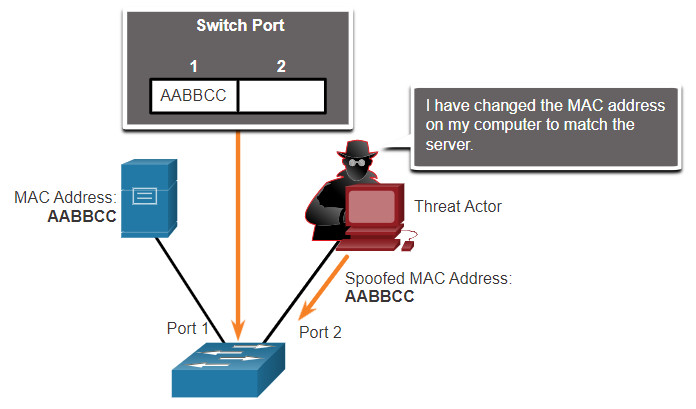
The switch overwrites the current CAM table entry and assigns the MAC address to the new port, as shown in the figure. It then forwards frames destined for the target host to the attacking host.
Switch Updates CAM Table with Spoofed Address
Application or service spoofing is another spoofing example. A threat actor can connect a rogue DHCP server to create an MiTM condition.
16.3 TCP and UDP Vulnerabilities
16.3.1 TCP Segment Header
While some attacks target IP, this topic discusses attacks that target TCP and UDP.
TCP segment information appears immediately after the IP header. The fields of the TCP segment and the flags for the Control Bits field are displayed in the figure.
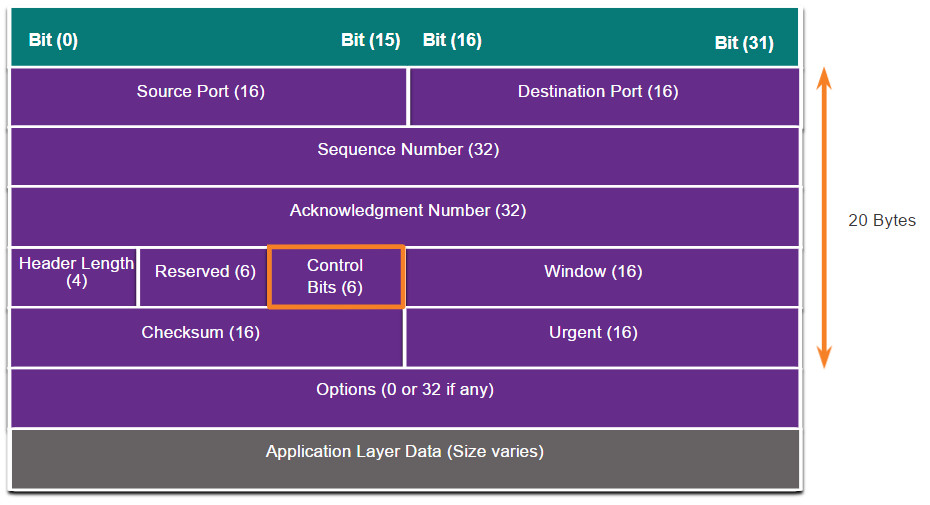
The following are the six control bits of the TCP segment:
- URG – Urgent pointer field significant
- ACK – Acknowledgment field significant
- PSH – Push function
- RST- Reset the connection
- SYN – Synchronize sequence numbers
- FIN – No more data from sender
16.3.2 TCP Services
TCP provides these services:
- Reliable delivery – TCP incorporates acknowledgments to guarantee delivery, instead of relying on upper-layer protocols to detect and resolve errors. If a timely acknowledgment is not received, the sender retransmits the data. Requiring acknowledgments of received data can cause substantial delays. Examples of application layer protocols that make use of TCP reliability include HTTP, SSL/TLS, FTP, DNS zone transfers, and others.
- Flow control – TCP implements flow control to address this issue. Rather than acknowledge one segment at a time, multiple segments can be acknowledged with a single acknowledgment segment.
- Stateful communication – TCP stateful communication between two parties occurs during the TCP three-way handshake. Before data can be transferred using TCP, a three-way handshake opens the TCP connection, as shown in the figure. If both sides agree to the TCP connection, data can be sent and received by both parties using TCP.
TCP Three-Way Handshake
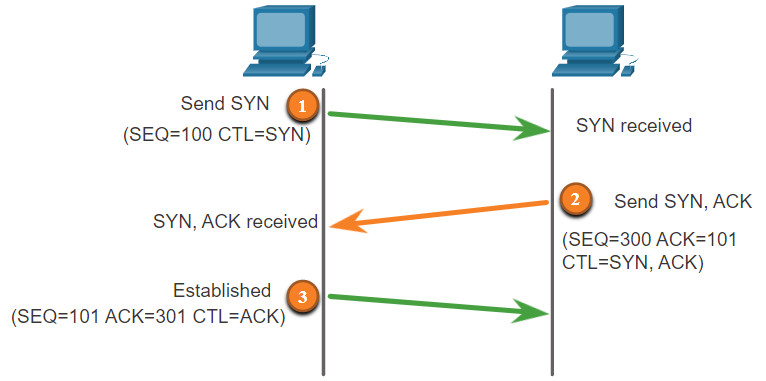
A TCP connection is established in three steps:
- The initiating client requests a client-to-server communication session with the server.
- The server acknowledges the client-to-server communication session and requests a server-to-client communication session.
- The initiating client acknowledges the server-to-client communication session.
16.3.3 TCP Attacks
Network applications use TCP or UDP ports. Threat actors conduct port scans of target devices to discover which services they offer.
TCP SYN Flood Attack
The TCP SYN Flood attack exploits the TCP three-way handshake. The figure shows a threat actor continually sending TCP SYN session request packets with a randomly spoofed source IP address to a target. The target device replies with a TCP SYN-ACK packet to the spoofed IP address and waits for a TCP ACK packet. Those responses never arrive. Eventually the target host is overwhelmed with half-open TCP connections, and TCP services are denied to legitimate users.
TCP SYN Flood Attack
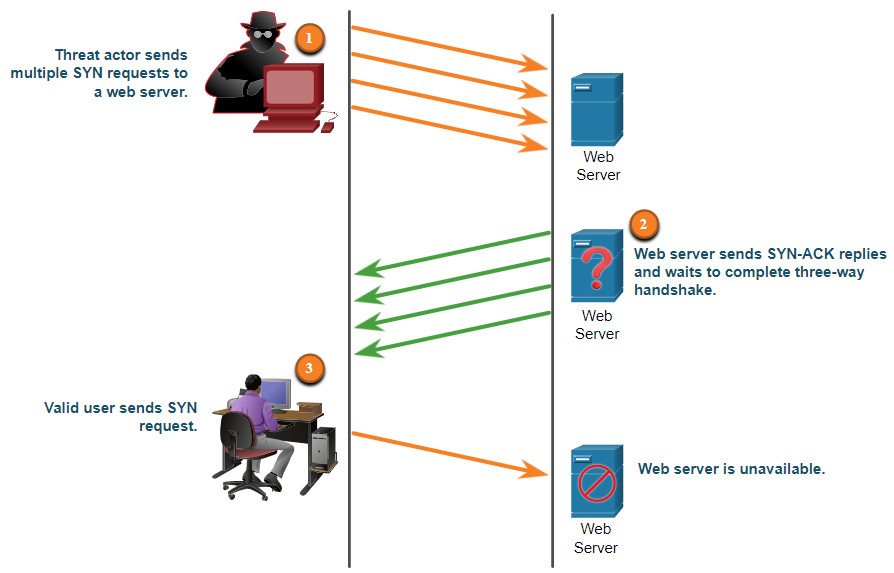
- The threat actor sends multiple SYN requests to a web server.
- The web server replies with SYN-ACKs for each SYN request and waits to complete the three-way handshake. The threat actor does not respond to the SYN-ACKs.
- A valid user cannot access the web server because the web server has too many half-opened TCP connections.
TCP Reset Attack
A TCP reset attack can be used to terminate TCP communications between two hosts. The figure displays how TCP uses a four-way exchange to close the TCP connection using a pair of FIN and ACK segments from each TCP endpoint. A TCP connection terminates when it receives an RST bit. This is an abrupt way to tear down the TCP connection and inform the receiving host to immediately stop using the TCP connection. A threat actor could do a TCP reset attack and send a spoofed packet containing a TCP RST to one or both endpoints.
Terminating a TCP Connection
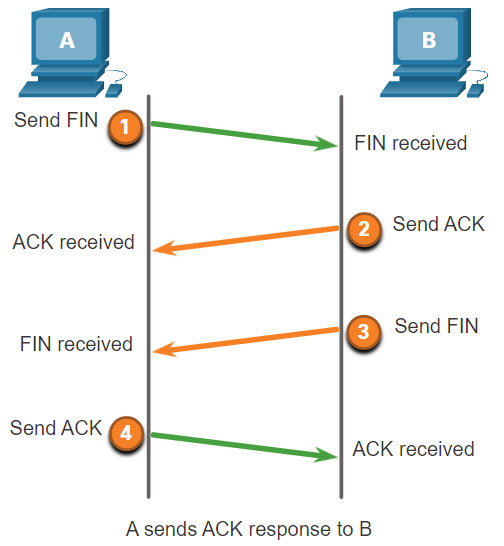
Terminating a TCP session uses the following four-way exchange process:
- When the client has no more data to send in the stream, it sends a segment with the FIN flag set.
- The server sends an ACK to acknowledge the receipt of the FIN to terminate the session from client to server.
- The server sends a FIN to the client to terminate the server-to-client session.
- The client responds with an ACK to acknowledge the FIN from the server.
TCP Session Hijacking
TCP session hijacking is another TCP vulnerability. Although difficult to conduct, a threat actor takes over an already-authenticated host as it communicates with the target. The threat actor must spoof the IP address of one host, predict the next sequence number, and send an ACK to the other host. If successful, the threat actor could send, but not receive, data from the target device.
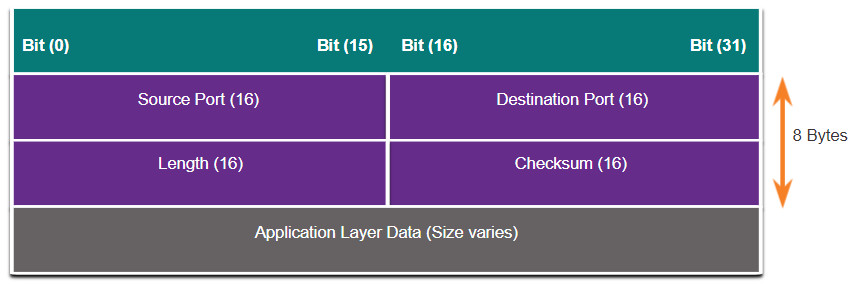
16.3.4 UDP Segment Header and Operation
UDP is commonly used by DNS, DHCP, TFTP, NFS, and SNMP. It is also used with real-time applications such as media streaming or VoIP. UDP is a connectionless transport layer protocol. It has much lower overhead than TCP because it is not connection-oriented and does not offer the sophisticated retransmission, sequencing, and flow control mechanisms that provide reliability. The UDP segment structure, shown in the figure, is much smaller than TCP’s segment structure.
Note: UDP actually divides data into datagrams. However, the generic term “segment” is commonly used
Although UDP is normally called unreliable, in contrast to TCP’s reliability, this does not mean that applications that use UDP are always unreliable, nor does it mean that UDP is an inferior protocol. It means that these functions are not provided by the transport layer protocol and must be implemented elsewhere if required.
The low overhead of UDP makes it very desirable for protocols that make simple request and reply transactions. For example, using TCP for DHCP would introduce unnecessary network traffic. If no response is received, the device resends the request.
16.3.5 UDP Attacks
UDP is not protected by any encryption. You can add encryption to UDP, but it is not available by default. The lack of encryption means that anyone can see the traffic, change it, and send it on to its destination. Changing the data in the traffic will alter the 16-bit checksum, but the checksum is optional and is not always used. When the checksum is used, the threat actor can create a new checksum based on the new data payload, and then record it in the header as a new checksum. The destination device will find that the checksum matches the data without knowing that the data has been altered. This type of attack is not widely used.
UDP Flood Attacks
You are more likely to see a UDP flood attack. In a UDP flood attack, all the resources on a network are consumed. The threat actor must use a tool like UDP Unicorn or Low Orbit Ion Cannon. These tools send a flood of UDP packets, often from a spoofed host, to a server on the subnet. The program will sweep through all the known ports trying to find closed ports. This will cause the server to reply with an ICMP port unreachable message. Because there are many closed ports on the server, this creates a lot of traffic on the segment, which uses up most of the bandwidth. The result is very similar to a DoS attack.
16.4 Attacking the Foundation Summary
16.4.1 What Did I Learn in this Module?
IP PDU Details
IP was designed as a Layer 3 connectionless protocol. The IPv4 header consists of several fields while the IPv6 header contains fewer fields. It is important for security analysts to understand the different fields in both the IPv4 and IPv6 headers.
IP Vulnerabilities
There are different types of attacks that target IP. Common IP-related attacks include:
- ICMP attacks
- Denial-of-Service (DoS) attacks
- Distributed Denial-of-Service (DoS) attacks
- Address spoofing attacks
- Man-in-the-middle attack (MiTM)
- Session hijacking
ICMP was developed to carry diagnostic messages and to report error conditions when routes, hosts, and ports are unavailable. Threat actors use ICMP for reconnaissance and scanning attacks. Threat actors also use ICMP for DoS and DDoS attacks. Threat actors often use amplification and reflection techniques to create DoS attacks. Threat actors also use resource exhaustion attacks to consume the resources of a target host to either crash it or to consume the resources of a network. IP address spoofing attacks occur when a threat actor creates packets with false source IP address information to either hide the identity of the sender, or to pose as another legitimate user. Address spoofing attacks can be non-blind spoofing to hijack a session, or blind spoofing to create a DoS attack. MAC address spoofing attacks are used when threat actors have access to the internal network.
TCP and UDP Vulnerabilities
TCP segment and UDP datagram information appear immediately after the IP header. It is important to understand Layer 4 headers and their functions in data communication. TCP provides reliable delivery, flow control, and stateful communication. TCP stateful communication between two parties occurs during the TCP three-way handshake. Threat actors can conduct a variety of TCP related attacks:
- TCP port scans
- TCP SYN Flood attack
- TCP Reset Attack
- TCP Session Hijacking attack
The UDP segment (i.e., datagram) is much smaller than the TCP segment, which makes it very desirable for use by protocols that make simple request and reply transactions such as DNS, DHCP, SNMP, and others. Threat actors can conduct UDP flood attacks which sweep through all the known UDP ports on a server trying to find closed ports. This can create a DoS situation.
