13.0 Introduction
13.0.1 Why Should I Take this Module?
Who is attacking our network and why? In this module you will learn about white hats, grey hats, and black hats. You will also learn about the techniques and tools used by these “hackers”. Keep reading to learn more!
13.0.2 What Will I Learn in this Module?
Module Title: Attackers and Their Tools
Module Objective: Explain how networks are attacked.
| Topic Title | Topic Objective |
|---|---|
| Who is Attacking our Network | Explain how network threats have evolved. |
| Threat Actor Tools | Describe the various types of attack tools used by Threat Actors. |
13.1 Who is Attacking Our Network?
13.1.1 Threat, Vulnerability, and Risk
We are under attack and attackers want access to our assets. Assets are anything of value to an organization, such as data and other intellectual property, servers, computers, smart phones, tablets, and more.

To better understand any discussion of network security, it is important to know the following terms:
| Term | Explanation |
|---|---|
| Threat | A potential danger to an asset such as data or the network itself. |
| Vulnerability | A weakness in a system or its design that could be exploited by a threat. |
| Attack surface | An attack surface is the total sum of the vulnerabilities in a given system that are accessible to an attacker. The attack surface describes different points where an attacker could get into a system, and where they could get data out of the system. For example, your operating system and web browser could both need security patches. They are each vulnerable to attacks and are exposed on the network or the internet. Together, they create an attack surface that the threat actor can exploit. |
| Exploit | The mechanism that is used to leverage a vulnerability to compromise an asset. Exploits may be remote or local. A remote exploit is one that works over the network without any prior access to the target system. The attacker does not need an account in the end system to exploit the vulnerability. In a local exploit, the threat actor has some type of user or administrative access to the end system. A local exploit does not necessarily mean that the attacker has physical access to the end system. |
| Risk | The likelihood that a particular threat will exploit a particular vulnerability of an asset and result in an undesirable consequence. |
Risk management is the process that balances the operational costs of providing protective measures with the gains achieved by protecting the asset. There are four common ways to manage risk, as shown in the table:
| Risk Management Strategy | Explanation |
|---|---|
| Risk acceptance | This is when the cost of risk management options outweighs the cost of the risk itself. The risk is accepted, and no action is taken. |
| Risk avoidance | This means avoiding any exposure to the risk by eliminating the activity or device that presents the risk. By eliminating an activity to avoid risk, any benefits that are possible from the activity are also lost. |
| Risk reduction | This reduces exposure to risk or reducing the impact of risk by taking action to decrease the risk. It is the most commonly used risk mitigation strategy. This strategy requires careful evaluation of the costs of loss, the mitigation strategy, and the benefits gained from the operation or activity that is at risk. |
| Risk transfer | Some or all of the risk is transferred to a willing third party such as an insurance company. |
Other commonly used network security terms include:
- Countermeasure – The actions that are taken to protect assets by mitigating a threat or reducing risk.
- Impact – The potential damage to the organization that is caused by the threat.
Note: A local exploit requires inside network access such as a user with an account on the network. A remote exploit does not require an account on the network to exploit that network’s vulnerability.
13.1.2 Hacker vs. Threat Actor
As we know, “hacker” is a common term used to describe a threat actor. However, the term “hacker” has a variety of meanings, as follows:
- A clever programmer capable of developing new programs and coding changes to existing programs to make them more efficient.
- A network professional that uses sophisticated programming skills to ensure that networks are not vulnerable to attack.
- A person who tries to gain unauthorized access to devices on the internet.
- An individual who run programs to prevent or slow network access to a large number of users, or corrupt or wipe out data on servers.
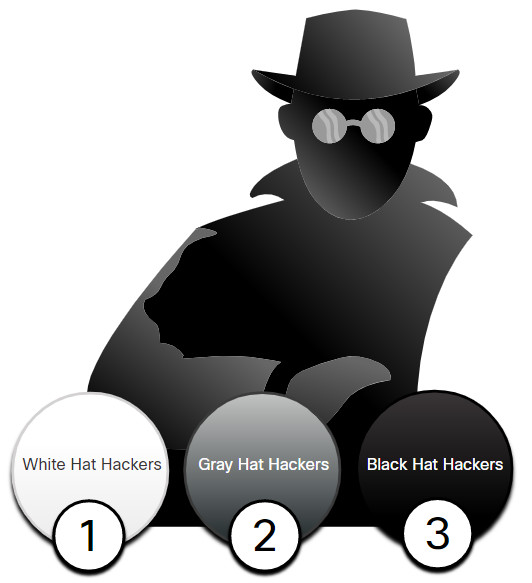
As shown in the figure, the terms white hat hacker, black hat hacker, and grey hat hacker are often used to describe hackers.
- White hat hackers are ethical hackers who use their programming skills for good, ethical, and legal purposes. They may perform network penetration tests in an attempt to compromise networks and systems by using their knowledge of computer security systems to discover network vulnerabilities. Security vulnerabilities are reported to developers and security personnel who attempt to fix the vulnerability before it can be exploited. Some organizations award prizes or bounties to white hat hackers when they provide information that helps to identify vulnerabilities.
- Grey hat hackers are individuals who commit crimes and do arguably unethical things, but not for personal gain or to cause damage. An example would be someone who compromises a network without permission and then discloses the vulnerability publicly. Grey hat hackers may disclose a vulnerability to the affected organization after having compromised their network. This allows the organization to fix the problem.
- Black hat hackers are unethical criminals who violate computer and network security for personal gain, or for malicious reasons, such as attacking networks. Black hat hackers exploit vulnerabilities to compromise computer and network systems.
Good or bad, hacking is an important aspect of network security. In this course, the term threat actor is used when referring to those individuals or groups that could be classified as gray or black hat hackers.
13.1.3 Evolution of Threat Actors
Hacking started in the 1960s with phone freaking, or phreaking, which refers to using various audio frequencies to manipulate phone systems. At that time, telephone switches used various tones, or tone dialing, to indicate different functions. Early threat actors realized that by mimicking a tone using a whistle, they could exploit the phone switches to make free long-distance calls.
In the mid-1980s, computer dial-up modems were used to connect computers to networks. Threat actors wrote “war dialing” programs which dialed each telephone number in a given area in search of computers, bulletin board systems, and fax machines. When a phone number was found, password-cracking programs were used to gain access. Since then, general threat actor profiles and motives have changed quite a bit.
There are many different types of threat actors.
13.1.4 Cybercriminals
Cybercriminals are threat actors who are motivated to make money using any means necessary. While sometimes cybercriminals work independently, they are more often financed and sponsored by criminal organizations. It is estimated that globally, cybercriminals steal billions of dollars from consumers and businesses every year.
Cybercriminals operate in an underground economy where they buy, sell, and trade exploits and tools. They also buy and sell the personal information and intellectual property that they steal from victims. Cybercriminals target small businesses and consumers, as well as large enterprises and industries.
13.1.5 Cybersecurity Tasks
Threat actors do not discriminate. They target the vulnerable end devices of home users and small-to-medium sized businesses, as well as large public and private organizations.
To make the internet and networks safer and more secure, we must all develop good cybersecurity awareness. Cybersecurity is a shared responsibility which all users must practice. For example, we must report cybercrime to the appropriate authorities, be aware of potential threats in email and the web, and guard important information from theft.
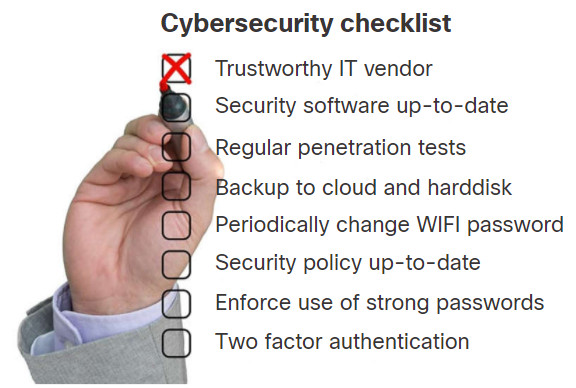
Organizations must take action and protect their assets, users, and customers. They must develop and practice cybersecurity tasks such as those listed in the figure.
13.1.6 Cyber Threat Indicators
Many network attacks can be prevented by sharing information about indicators of compromise (IOC). Each attack has unique identifiable attributes. Indicators of compromise are the evidence that an attack has occurred. IOCs can be features that identify malware files, IP addresses of servers that are used in attacks, filenames, and characteristic changes made to end system software, among others. IOCs help cybersecurity personnel identify what has happened in an attack and develop defenses against the attack. A summary of the IOC for a piece of malware is shown in the figure.
Malware File - "studiox-link-standalone-v20.03.8-stable.exe" sha256 6a6c28f5666b12beecd56a3d1d517e409b5d6866c03f9be44ddd9efffa90f1e0 sha1 eb019ad1c73ee69195c3fc84ebf44e95c147bef8 md5 3a104b73bb96dfed288097e9dc0a11a8 DNS requests domain log.studiox.link domain my.studiox.link domain _sips._tcp.studiox.link domain sip.studiox.link Connections ip 198.51.100.248 ip 203.0.113.82
For instance, a user receives an email claiming they have won a big prize. Clicking on the link in the email results in an attack. The IOC could include the fact the user did not enter that contest, the IP address of the sender, the email subject line, the URL to click, or an attachment to download, among others.
Indicators of attack (IOA) focus more on the motivation behind an attack and the potential means by which threat actors have, or will, compromise vulnerabilities to gain access to assets. IOAs are concerned with the strategies that are used by attackers. For this reason, rather than informing response to a single threat, IOAs can help generate a proactive security approach. This is because strategies can be reused in multiple contexts and multiple attacks. Defending against a strategy can therefore prevent future attacks that utilize the same, or similar strategy.
13.1.7 Threat Sharing and Building Cybersecurity Awareness
Governments are now actively promoting cybersecurity. For instance, the US Cybersecurity Infrastructure and Security Agency (CISA) is leading efforts to automate the sharing of cybersecurity information with public and private organizations at no cost. CISA use a system called Automated Indicator Sharing (AIS). AIS enables the sharing of attack indicators between the US government and the private sector as soon as threats are verified. CISA offers many resources that help to limit the size of the United States attack surface.
The CISA and the National Cyber Security Alliance (NCSA) promote cybersecurity to all users. For example, they have an annual campaign in every October called “National Cybersecurity Awareness Month” (NCASM). This campaign was developed to promote and raise awareness about cybersecurity.
The theme for the NCASM for 2019 was “Own IT. Secure IT. Protect IT.” This campaign encouraged all citizens to be safer and more personally accountable for using security best practices online. The campaign provides material on a wide variety of security topics including:
- Social media safety
- Updating privacy settings
- Awareness of device app security
- Keeping software up-to-date
- Safe online shopping
- Wi-Fi safety
- Protecting customer data
The European Union Agency for Cybersecurity (ENISA) delivers advice and solutions for the cybersecurity challenges of the EU member states. ENISA fills a role in Europe that is similar to the role of CISA in the US.
13.2 Threat Actor Tools
13.2.1 Introduction of Attack Tools
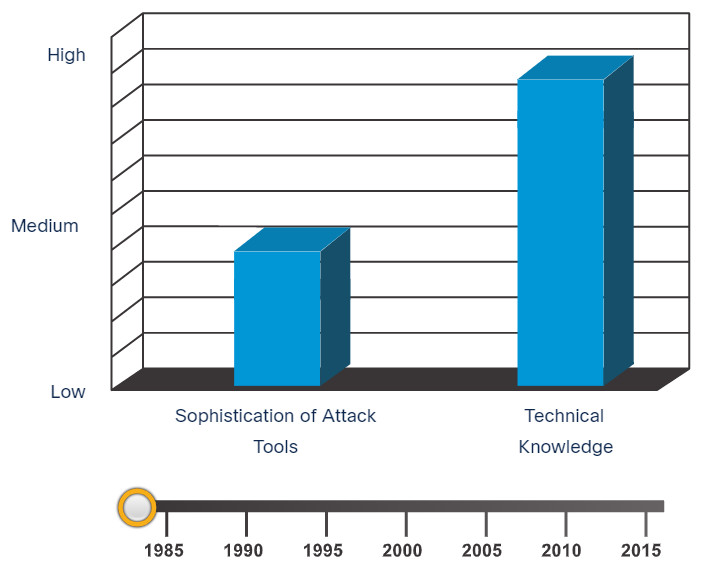
To exploit a vulnerability, a threat actor must have a technique or tool. Over the years, attack tools have become more sophisticated, and highly automated. These new tools require less technical knowledge to implement.
In the figure, drag the white circle across the timeline to view the relationship between the sophistication of attack tools versus the technical knowledge required to use them.
Sophistication of Attack Tools vs. Technical Knowledge
13.2.2 Evolution of Security Tools
Ethical hacking involves using many different types of tools to test the network and end devices. To validate the security of a network and its systems, many network penetration testing tools have been developed. However, many of these tools can also be used by threat actors for exploitation.
Threat actors have also created various hacking tools. These tools are explicitly written for nefarious reasons. Cybersecurity personnel must also know how to use these tools when performing network penetration tests.
Explore the categories of common network penetration testing tools. Notice how some tools are used by white hats and black hats. Keep in mind that the list is not exhaustive as new tools are continually being developed.
Note: Many of these tools are UNIX or Linux based; therefore, a security professional should have a strong UNIX and Linux background.
| Categories of Tools | Description |
|---|---|
| password crackers | Passwords are the most vulnerable security threat. Password cracking tools are often referred to as password recovery tools and can be used to crack or recover the password. This is accomplished either by removing the original password, after bypassing the data encryption, or by outright discovery of the password. Password crackers repeatedly make guesses in order to crack the password and access the system. Examples of password cracking tools include John the Ripper, Ophcrack, L0phtCrack, THC Hydra, RainbowCrack, and Medusa. |
| wireless hacking tools | Wireless networks are more susceptible to network security threats. Wireless hacking tools are used to intentionally hack into a wireless network to detect security vulnerabilities. Examples of wireless hacking tools include Aircrack-ng, Kismet, InSSIDer, KisMAC, Firesheep, and NetStumbler. |
| network scanning and hacking tools | Network scanning tools are used to probe network devices, servers, and hosts for open TCP or UDP ports. Examples of scanning tools include Nmap, SuperScan, Angry IP Scanner, and NetScanTools. |
| packet crafting tools | Packet crafting tools are used to probe and test a firewall’s robustness using specially crafted forged packets. Examples of such tools include Hping, Scapy, Socat, Yersinia, Netcat, Nping, and Nemesis. |
| packet sniffers | Packet sniffers tools are used to capture and analyze packets within traditional Ethernet LANs or WLANs. Tools include Wireshark, Tcpdump, Ettercap, Dsniff, EtherApe, Paros, Fiddler, Ratproxy, and SSLstrip. |
| rootkit detectors | A rootkit detector is a directory and file integrity checker used by white hats to detect installed root kits. Example tools include AIDE, Netfilter, and PF: OpenBSD Packet Filter. |
| fuzzers to search vulnerabilities | Fuzzers are tools used by threat actors when attempting to discover a computer system’s security vulnerabilities. Examples of fuzzers include Skipfish, Wapiti, and W3af. |
| forensic tools | White hat hackers use forensic tools to sniff out any trace of evidence existing in a particular computer system. Example of tools include Sleuth Kit, Helix, Maltego, and Encase. |
| debuggers | Debugger tools are used by black hats to reverse engineer binary files when writing exploits. They are also used by white hats when analyzing malware. Debugging tools include GDB, WinDbg, IDA Pro, and Immunity Debugger. |
| hacking operating systems | Hacking operating systems are specially designed operating systems preloaded with tools and technologies optimized for hacking. Examples of specially designed hacking operating systems include Kali Linux, SELinux, Knoppix, Parrot OS, and BackBox Linux. |
| encryption tools | These tools safeguard the contents of an organization’s data when it is stored or transmitted. Encryption tools use algorithm schemes to encode the data to prevent unauthorized access to the data. Examples of these tools include VeraCrypt, CipherShed, Open SSH, OpenSSL, OpenVPN, and Stunnel. |
| vulnerability exploitation tools | These tools identify whether a remote host is vulnerable to a security attack. Examples of vulnerability exploitation tools include Metasploit, Core Impact, Sqlmap, Social Engineer Tool Kit, and Netsparker. |
| vulnerability scanners | These tools scan a network or system to identify open ports. They can also be used to scan for known vulnerabilities and scan VMs, BYOD devices, and client databases. Examples of these tools include Nipper, Securia PSI, Core Impact, Nessus, SAINT, and Open VAS. |
13.2.3 Categories of Attacks
Threat actors can use the previously mentioned tools or a combination of tools to create various attacks. The table displays common types of attacks. However, the list of attacks is not exhaustive as new ways to attack networks are continually being discovered.
It is important to understand that threat actors use a variety of security tools to carry out these attacks.
| Category of Attack | Description |
|---|---|
| eavesdropping attack | An eavesdropping attack is when a threat actor captures and listens to network traffic. This attack is also referred to as sniffing or snooping. |
| data modification attack | Data modification attacks occur when a threat actor has captured enterprise traffic and has altered the data in the packets without the knowledge of the sender or receiver. |
| IP address spoofing attack | An IP address spoofing attack is when a threat actor constructs an IP packet that appears to originate from a valid address inside the corporate intranet. |
| password-based attacks | Password-based attacks occur when a threat actor obtains the credentials for a valid user account. Threat actors then use that account to obtain lists of other users and network information. They could also change server and network configurations, and modify, reroute, or delete data. |
| denial-of-service (DoS) attack | A DoS attack prevents normal use of a computer or network by valid users. After gaining access to a network, a DoS attack can crash applications or network services. A DoS attack can also flood a computer or the entire network with traffic until a shutdown occurs because of the overload. A DoS attack can also block traffic, which results in a loss of access to network resources by authorized users. |
| man-in-the-middle attack (MiTM) | A MiTM attack occurs when threat actors have positioned themselves between a source and destination. They can now actively monitor, capture, and control the communication transparently. |
| compromised key attack | A compromised-key attack occurs when a threat actor obtains a secret key. This is referred to as a compromised key. A compromised key can be used to gain access to a secured communication without the sender or receiver being aware of the attack. |
| sniffer attack | A sniffer is an application or device that can read, monitor, and capture network data exchanges and read network packets. If the packets are not encrypted, a sniffer provides a full view of the data inside the packet. Even encapsulated (tunneled) packets can be broken open and read unless they are encrypted and the threat actor does not have access to the key. |
13.3 Attackers and Their Tools Summary
13.3.1 What Did I Learn in this Module?
Who is Attacking Our Network?
Understanding network security requires you to understand the following terms: threat, vulnerability, attack surface, exploit, and risk. Risk management is the process that balances the operational costs of providing protective measures with the gains achieved by protecting the asset. Four common ways to manage risk are risk acceptance, risk avoidance, risk reduction, and risk transfer. Hacker is a term used to describe a threat actor. White hat hackers are ethical hackers using their skills for good, ethical, and legal purposes. Grey hat hackers are individuals who commit crimes and do unethical things, but not for personal gain or to cause damage. Black hat hackers are criminals who violate computer and network security for personal gain, or for malicious reasons, such as attacking networks. Threat actors include script kiddies, vulnerability brokers, hacktivists, cybercriminals, and state-sponsored hackers. Many network attacks can be prevented by sharing information about indicators of compromise (IOC). Many governments are promoting cybersecurity. CISA and NCSA are examples of such organizations.
Introduction of Attack Tools
Threat actors use a technique or tool. Attack tools have become more sophisticated, and highly automated. Many of the tools are Linux or UNIX based and a knowledge of these are useful to a cybersecurity professional. Tools include password crackers, wireless hacking tools, network security scanning and hacking tools, packet crafting tools, packet crafting tools, packet sniffers, rootkit detectors, fuzzers to search vulnerabilities, forensic tools, debuggers, hacking operating systems, encryption tools, vulnerability exploitation tools, and vulnerability scanners. Categories of attacks include eavesdropping attacks, data modification attacks, IP address spoofing attacks, password-based attacks, denial-of-service attacks, man-in the-middle attacks, compromised key attacks, and sniffer attacks.
