IT Essentials 8.0 Module 12.5.1.2 Mobile, Linux and macOS Operating Systems-Quiz Answers
1. Which feature of an Android or iOS mobile device helps prevent malicious programs from infecting the device?
- The phone carrier prevents the mobile device app from accessing some smartphone features and programs.
- The passcode restricts the mobile device app from access to other programs.
- Mobile device apps are run in a sandbox that isolates them from other resources.
- The remote lock feature prevents malicious programs from infecting the device.
2. What are two types of cloud-enabled services for mobile devices? (Choose two.)
- locator apps
- remote backup
- passcode configuration
- screen calibration
- screen app locking
3. True of False? Android and OS X are based on the Unix operating system.
- true
- false
4. A person with an Android mobile device holds down the power button and the volume down button until the device turns off. The person then turns the device back on. What was this person doing to the device?
- a normal power off
- a factory reset
- a full backup to the iCloud
- a standard reset of the device
- an operating system update
5. What two preventive maintenance tasks should be scheduled to occur automatically? (Choose two.)
- executing a backup
- scanning the signature files
- updating the operating system software
- resetting devices by applying the factory reset feature
- checking the disks for bad sectors
6. What are two features of the Android operating system? (Choose two.)
- Android is open source and allows anyone to contribute to its development and evolution.
- Android has been implemented on devices such as cameras, smart TVs, and e-book readers.
- All available Android applications have been tested and approved by Google to run on the open source operating system.
- Each implementation of Android requires a royalty to be paid to Google.
- Android applications can only be downloaded from Google Play.
7. Which two terms describe unlocking Android and iOS mobile devices to allow users full access to the file system and full access to the kernel module? (Choose two.)
- patching
- rooting
- remote wipe
- sandboxing
- jailbreaking
8. A user presses the Recent Apps icon on an Android-based smartphone to see a list of recently used apps. What should the user do to remove an app from the list?
- Swipe the app up.
- Double tap on the app.
- Swipe the app down.
- Swipe the app to either side.
9. Which two location-specific services can the GPS feature on a mobile device offer? (Choose two.)
- playing local songs
- delivering local advertising
- displaying local weather information
- planning a route between two locations
- displaying a map of a destination city while driving
10. Which three methods can be used to unlock a smartphone? (Choose three.)
- NFC
- passcode
- encryption
- swipe pattern
- QR code scan
- biometric information
11. A user has an iOS device. What will happen if the user forgets the passcode to unlock the device?
- The user must call Apple to reset the passcode.
- The user can visit the Apple website to initiate a passcode reset request.
- The user must perform a full restore from a backup saved in iTunes or iCloud.
- The user can use the Find My iPhone service on the website www.icloud.com to reset the passcode.
12. A system administrator is using the crontab command to edit an entry on a Linux server. Which service is the administrator configuring?
- editing a shell script to run when the server starts
- installing the new BIOS update when it is available
- scheduling a task to run at a specific time and date
- deleting caches and cookies after the web browser closes
13. A company is creating a new website to be hosted on a Linux server. The system administrator creates the group “webteam” and assigns team members to it. The administrator then creates the directory “webpages” for storing files. Later that day, one of the team members reports of being unable to create files in the “webpages” directory or subdirectories. The administrator uses the ls -l command to view the file permissions. The result displayed is drwxr-xr– . What should the administrator do to allow team members to add and edit files?
- Add the user to the webteam group.
- Issue the command chmod 775 –R webteam .
- Issue the command chmod 775 –R webpages .
- Make the user the owner of the directory and subdirectories.
14. Which two tasks can be done with the iOS device Home button? (Choose two.)
- wake the device
- respond to an alert
- display the navigation icons
- return to the home screen
- place apps into folders
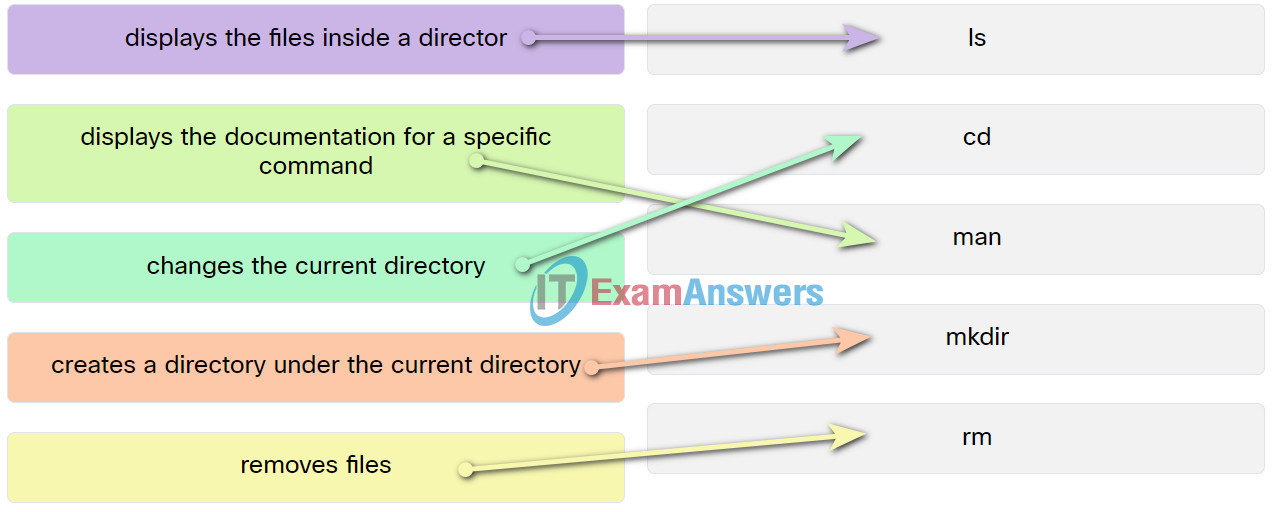
15. Match the Linux CLI commands to their function. (Not all options are used.)
12.5.1.2 Mobile, Linux and macOS Operating Systems-Quiz
