IT Essentials Practice Final Exam Modules 1-9 Answers
IT Essentials (Version 8.0) – ITE 8.0 Practice Final Exam Modules 1-9 (Ch 1 – 9)
IT Essentials (Version 7.00) – IT Essentials 7.0 Practice Final 1 – 9
1. What is the function of the power supply?
- to convert AC power into a lower voltage DC power
- to convert AC power into a higher voltage DC power
- to convert DC power into a lower voltage AC power
- to convert DC power into a higher voltage AC power
2. Which two motherboard components connect to the Northbridge chipset? (Choose two.)
- NIC
- USB 2.0 devices
- USB 3.0 devices
- FireWire devices
- RAM
- video card
3. What type of connector can be used to connect an internal hard drive to the motherboard?
- USB
- SATA
- eSATA
- Thunderbolt
4. Refer to the exhibit. To what input device would the cables attach?

ITE v7.0 – IT Essentials ( Version 7.0) – IT Essentials 7.0 Practice Final Exam Answers
- keyboard/mouse combo device
- KVM switch
- video distribution center
- sound system
5. Which is the correct procedure to put out a fire with a fire extinguisher after the pin is pulled?
- Aim just above the flame, squeeze the lever, and sweep from side to side.
- Aim at the base of the flame, squeeze the lever, and sweep from side to side.
- Aim directly at the center of the flame, squeeze the lever, and sweep from side to side.
- Aim at the base of the flame, squeeze the lever, and sweep from the base to the top of the flame.
- Aim just above the flame, squeeze the lever, and sweep from the top to the base of the flame.
6. Which three safety guidelines would be recommended for a technician working inside a laser printer? (Choose three.)
- Allow the hot area of the laser printer to cool.
- Ensure that the printer has power attached and that there is a good ground.
- Keep a fire extinguisher beside the laser printer while working inside it.
- Remove jewelry and other accessories.
- Secure loose clothing.
- When removing the printer or heavy parts of the printer, be sure to bend at the waist to lift.
7. A technician is reorganizing the parts cabinet and has found some thermal paste. When would the technician use thermal paste?
- when installing SSDs
- when performing maintenance on mechanical drives
- when installing CPUs
- when troubleshooting memory problems
8. Which two types of expansion slots would be used by a wireless NIC in a computer today? (Choose two.)
- PCIe
- AGP
- PCI
- DIMM
- ISA
9. Refer to the exhibit. What is the purpose of the device that is shown?

- to connect multiple computers to a single keyboard and mouse
- to read data from a memory card
- to read or write data to discs
- to connect various types of external hard drives
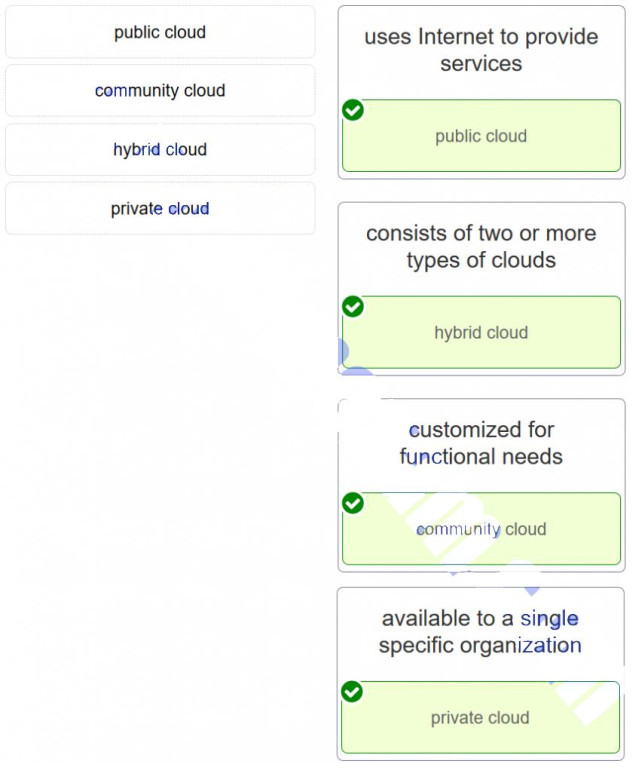
10. Refer to the exhibit. What is the motherboard component that is shown?
- front panel cable connectors
- motherboard power connector
- PATA drive connector
- SATA data and power connectors
11. Which solid-state storage technology allows a computer BIOS to be upgraded by flashing?
- SODIMM
- ROM
- SDRAM
- EEPROM
12. Which two PC settings can be configured using the BIOS setup utility? (Choose two.)
- POST
- virtualization support
- allocation of memory to applications
- enabling device drivers
- boot sequence
13. What type of device provides power to a computer and allows it to be safely shut down in the event of a power loss?
- surge suppressor
- uninterruptible power supply
- standby power supply
- power inverter
14. Why do laptop computers use CPU throttling techniques?
- to enhance the performance of the CPU
- to reduce the heat that the CPU may generate
- to ensure the CPU is running at its peak speed
- to conserve the battery life by reducing the bus speed between the CPU and RAM
15. Which two existing components must be compatible with the installation of a new upgraded CPU? (Choose two.)
- power supply
- motherboard
- hard drive
- case
- video card
16. What are three important considerations when installing a CPU on a motherboard that has just been upgraded? (Choose three.)
- Antistatic precautions are taken.
- The CPU is correctly aligned and placed in the socket.
- The CPU contacts are first cleaned with isopropyl alcohol.
- The CPU heat sink/fan assembly is correctly installed.
- The CMOS battery is removed prior to installing the CPU.
- Maximum insertion force is applied to the load lever so that the CPU is locked in place.
17. What is a possible use for virtual computing?
- to run old applications that are not compatible with current operating systems
- to allow computer hardware to be tested
- to allow computer hardware upgrades to be tested
- to allow ROM firmware upgrades to be tested
18. A customer has requested a device with a minimum of 64 GB of RAM and the requirement that large numbers of users can test software upgrades in a safe environment. What type of device should be purchased?
- CAx workstation
- VDI server
- thin client
- thick client
19. True or False?
Thin clients require a network connection to remote servers to perform data processing.
- true
- false
20. What is the correct disposal process of old computer batteries?
- They should be burned because they do not decompose.
- They can be refilled and reused.
- They should be placed in an airtight container and then thrown away in the regular garbage.
- They must be recycled because they are harmful to the environment.
- Because they will decompose harmlessly, they should be thrown away in the recycling bin.
21. Which component can be easily damaged by the direct spray of compressed air when cleaning inside the computer case?
- fan
- heat sink
- power supply
- CPU
- cable connectors
22. During the process of testing a theory of several probable causes to a problem, which should be tested first?
- the easiest and most obvious
- those the customer believes to be the most important
- the most complex and difficult to diagnose
- those chosen by random selection
23. Which two items could be used to help establish a plan of action when resolving a computer problem? (Choose two.)
- a multimeter
- a loopback plug
- the computer manual
- the computer repair history log
- BIOS diagnostics
24. What is the preferred method to remove a disc from an optical drive that fails to eject the disc?
- Insert a pin into the small hole on the front of the drive.
- Use a small screwdriver and pry the drive door open.
- Remove the top of the drive enclosure.
- Send the drive to an authorized repair depot.
25. A technician is called to an office where the computer is randomly rebooting. Which of the given components would most likely cause this issue?
- BIOS
- CMOS battery
- optical drive
- power supply
26. Which two devices are considered intermediary devices in a network? (Choose two.)
- switch
- server
- printer
- modem
- IP phone
27. What are the four layers in the TCP/IP reference model?
- application, presentation, internet, network access
- application, transport, network, data link
- application, transport, internet, network access
- application, presentation, session, transport
- physical, data link, network, transport
28. Several messages sent to the network administrator are reporting that access to a secure server using HTTPS is failing. After checking recent updates to the company firewall, the administrator learns that the firewall is blocking HTTPS. Which port should be opened to solve the problem?
- 22
- 53
- 80
- 143
- 443
29. A computer technician is monitoring traffic on a network where users are complaining about slow network performance. The technician is curious as to whether the new network management software is causing the slowdown. Which two port numbers would the technician be looking for in the captured packets for SNMP traffic? (Choose two.)
- 67
- 68
- 80
- 161
- 162
- 443
30. A technician has been asked to assist with the installation of smart devices in school dormitories. Which two technologies should the technician be familiar with? (Choose two.)
- VR/AR
- LTE
- IPS
- Z-Wave
- Zigbee
31. The current IP configuration of a medium size company with several subnets is done manually and is time-consuming. Because of increased network growth, a technician needs a simpler way for IP configuration of workstations. Which service or protocol would simplify the workstation IP configuration task?
- APIPA
- DHCP
- DNS
- ICMP
32. Which IPv6 address represents the most compressed form of the IPv6 address 2001:0db8:cafe:0100:0f0d:0000:0000:00AA/96
- 2001:0db8:cafe:0100:0f0d::00AA/96
- 2001:db8:cafe:1:f0d::AA/96
- 2001:db8:cafe:100:f0d::AA/96
- 2001:0db8:cafe:0100:0f0d::AA/96
32. What is the full decompressed form of the IPv6 address 2001:420:59:0:1::a/64?
- 2001:420:59:0:1:0:0:a
- 2001:0420:0059:0000:0001:0000:0000:000a
- 2001:4200:5900:0000:1000:0000:0000:a000
- 2001:4200:5900:0:1:0:0:a000
- 2001:0420:0059:0000:0001:000a
- 2001:0420:0059:0000:0001:0000:000a
33. A support desk technician is asking a customer a series of questions about a problem connecting to the network. Which step of the troubleshooting process is the technician applying?
- Identify the problem.
- Establish a theory of probable cause.
- Establish a plan of action to resolve the problem.
- Test the theory to determine cause.
34. What are three common solutions for a PC that displays an IP address starting with 169.254.x.x? (Choose three.)
- Check the DNS server setting.
- Turn on the device that is acting as a DHCP server.
- Enable the client machine to receive an IPv4 address automatically.
- Use the ipconfig /release and ipconfig /renew commands to request a new IPv4 address.
- Reboot the client machine that is using the 169.254.x.x address.
- Reenter the IPv4 address on the DHCP server.
35. A user with a laptop is trying to connect to a wireless network, but no wireless networks are showing. What is a quick way for the user to ensure that the wireless NIC is enabled?
- Enable Airplane mode.
- Use a function key.
- Hold down the Ctrl key and then press the Insert key.
- Attach the AC power cord.
36. Which laptop device would accept an SD card?
- M.2 card
- mini-PCIe adapter
- card reader
- eSATA port
37. What are two indications that a mobile device battery needs to be replaced? (Choose two.)
- The battery is leaking.
- The mobile device will not turn off properly.
- Unusual characters display on the screen.
- The battery overheats.
- The display brightness cannot be adjusted.
38. What two steps must be taken before performing a cleaning procedure on a laptop computer? (Choose two.)
- Disconnect the laptop from the electrical outlet.
- Remove all installed batteries.
- Wipe the surface of the touch pad.
- Clean the screen with a cloth.
- Insert the cleaning disk into the optical drive.
- Backup the registry.
39. A tire store needs to use carbon copy paper to print customer invoices so that both the store and the customer have a copy. What is the best printer solution?
- piezoelectric printer
- inkjet printer
- thermal printer
- impact printer
40. In what two situations is a virtual printer used? (Choose two.)
- A user sends a printed document to a remote destination through the cloud.
- A remote user sends a document to a local user who prints the document using the company laser printer.
- A corporate user prints to a centralized printer on the same floor, but on a different network.
- A document is printed to a PDF or other file type.
- A document is sent to a printer that is connected to the USB port of a co-worker on the same network.
41. What printer feature allows a computer to work while print jobs are waiting in queue to be printed?
- buffering
- duplexing
- charging
- processing
42. A user on a home network wants to share a printer from a Windows 7 computer. What must the user do in order for other Windows 7 computers in the house to obtain the proper driver?
- The user must browse the Internet, then download and install the proper driver.
- The person doing the sharing must use the Additional Drivers button in order to designate how many device drivers are allowed to be downloaded.
- Nothing. Windows automatically provides the driver.
- The person doing the sharing must use the Additional Drivers button in order to designate the driver to be used by the other Windows 7 computers.
43. For cleaning a laser printer, what should be used to pick up excess particles of toner?
- a HEPA-capable vacuum
- a lint-free cloth
- isopropyl alcohol
- a damp cloth
44. What is the difference between cloud computing and a data center?
- A data center provides access to shared computing resources, wheras a cloud is a private on-premise facility that stores and processes local data.
- Cloud computing solutions are network resources and services provided to the clients through the use of services from data centers.
- The data center makes use of more devices to process data.
- Data centers require cloud computing but cloud computing does not require data centers.
45. Which technology provides a solution for PC virtualization?
- hypervisor
- server clustering
- Terminal Services
- RAID
46. What is an example of cloud computing?
- a continuous interaction between people, processes, data, and things
- a service that offers on-demand access to shared resources
- a network infrastructure that spans a large geographic area
- an architectural style of the World Wide Web
47. Which Cloud computing service would be best for a new organization that cannot afford physical servers and networking equipment and must purchase network services on-demand?
- PaaS
- SaaS
- ITaaS
- IaaS
48. Match the cloud model with the description.
IT Essentials (Version 7.00) – IT Essentials 7.0 Practice Final 1 – 9
49. A customer comes into a computer parts and service store. The customer is looking for a device to allow users to tap and pay for their purchases. What device should the store owner recommend to accomplish the required task?
- NFC device
- keyboard
- flatbed scanner
- barcode scanner
50. A customer comes into a computer parts and service store. The customer is looking for a device to allow secure access to the main doors of the company by swiping an ID card. What device should the store owner recommend to accomplish the required task?
- magstripe reader
- keyboard
- NFC device
- flatbed scanner
51. A customer comes into a computer parts and service store. The customer is looking for a device to scan some old family photos into a laptop. What device should the store owner recommend to accomplish the required task?
- flatbed scanner
- keyboard
- NFC device
- barcode scanner
52. A customer comes into a computer parts and service store. The customer is looking for a device to display a promotional presentation to a large audience at a conference. What device should the store owner recommend to accomplish the required task?
- projector
- keyboard
- NFC device
- flatbed scanner
53. A customer comes into a computer parts and service store. The customer is looking for a device to simplify inventory ordering and control in the customer retail store. What device should the store owner recommend to accomplish the required task?
- barcode scanner
- stylus
- AR headset
- KVM switch
54. A customer comes into a computer parts and service store. The customer is looking for a device to train pilots how to land and take off in a computer simulation environment. What device should the store owner recommend to accomplish the required task?
- joystick or gamepad
- KVM switch
- stylus
- barcode scanner
55. A customer comes into a computer parts and service store. The customer is looking for a device to share a keyboard and mouse between two computers. What device should the store owner recommend to accomplish the required task?
- KVM switch
- stylus
- AR headset
- barcode scanner
56. A customer comes into a computer parts and service store. The customer is looking for a device to verify the identity of the receiver when a purchased product is delivered by courier to the door of a customer. What device should the store owner recommend to accomplish the required task?
- signature pad
- stylus
- AR headset
- KVM switch
57. A customer comes into a computer parts and service store. The customer is looking for a device to provide secure access to the central server room using a retinal scan. What device should the store owner recommend to accomplish the required task?
- biometric scanner
- stylus
- AR headset
- KVM switch
58. A customer comes into a computer parts and service store. The customer is looking for a device to help a person with accessibility issues input instructions into a laptop by using a pen. What device should the store owner recommend to accomplish the required task?
- stylus
- KVM switch
- AR headset
- barcode scanner
59. A consultant has been asked to help decide on the best power protection for some equipment in a company that trades electricity and energy nation-wide. The company has multiple cubicles where the energy traders work. Each cubicle has a computer, an IP phone, and eight monitors. All devices need power and the ability to protect the equipment from power spikes. Which protection device would be best to use for each computer station?
- a surge protector
- a capacitor
- a phone line filter
- a redundant power supply
60. A consultant has been asked to help decide on the best power protection for some equipment in a company that provides payroll services to small businesses. The company has staff that require a PC, laser printer, and IP phone from 8 a.m. to 5 p.m. Monday through Friday. The power protection device needs to be able to provide protection for an overvoltage situation. Which protection device would be best to use for each computer station?
- a surge protector
- a capacitor
- a phone line filter
- a redundant power supply
61. A consultant has been asked to help decide on the best power protection for some equipment in a company that specializes in PC technical support for senior citizens. The company is a 24/7 operation. Each technician is assigned to a computer that has an IP phone with a headset and two monitors. All devices need power and the ability to protect the equipment from power spikes. Which protection device would be best to use for each computer station?
- a surge protector
- a 24-pin power connector
- a capacitor
- a redundant power supply
62. A consultant has been asked to help decide on the best power protection for some equipment in a company that trades electricity and energy nation-wide. The company has multiple cubicles where the energy traders work. Each cubicle has a computer, an IP phone, and eight monitors. All devices need consistent quality power, the ability to use the equipment 24/7, and the ability to save information about the current transaction if the power goes out. Which protection device would be best to use for each computer station?
- a UPS
- an anti-static wrist band
- a capacitor
- a redundant power supply
63. A consultant has been asked to help decide on the best power protection for some equipment in a company that provides payroll services to small businesses. The company has staff that require a PC, laser printer, and IP phone from 8 a.m. to 5 p.m. Monday through Friday. The power protection device needs to be able to provide conditioned power at all times the ability to save payroll information if the power goes out. Which protection device would be best to use for each computer station?
- a UPS
- an anti-static wrist band
- a capacitor
- a redundant power supply
64. A consultant has been asked to help decide on the best power protection for some equipment in a company that specializes in PC technical support for senior citizens. The company is a 24/7 operation. Each technician is assigned to a computer that has an IP phone with a headset and two monitors. All devices need quality power, the ability to finish the current call if the power goes out, and constant battery charging. Which protection device would be best to use for each computer station?
- a UPS
- a lightning arrestor
- a 24-pin power connector
- a capacitor
65. A user is building a new computer system. Why would the user select a DDR3?
- to install a memory module
- to diminish any electrostatic charge
- to configure a gaming console
- to attach an external HD
66. A user is building a new computer system. Why would the user select external screws?
- to install a power supply into a PC tower case
- to attach an external HD
- to attach a VR headset
- to install an EEPROM
67. A user is building a new computer system. Why would the user select a part that has a 3.5 inch (8.89 cms) form factor?
- to install an internal HDD
- to configure a gaming console
- to attach a VR headset
- to install an EEPROM
68. A user is building a new computer system. Why would the user select an HDMI cable?
- to attach a digital monitor
- to configure a gaming console
- to attach a VR headset
- to install an EEPROM
69. A user is building a new computer system. Why would the user select a DVI cable?
- to attach a digital monitor
- to replace the CPU cooling system
- to attach a VR headset
- to install an EEPROM
70. A user is building a new computer system. Why would the user select a media reader?
- to copy files from an SD card
- to attach a laser printer
- to install an EEPROM
- to replace a heatsink
71. A user is building a new computer system. Why would the user select an RJ-45 connector?
- to connect a device to a wired network
- to attach a laser printer
- to install an EEPROM
- to replace a heatsink
72. How many bits are used to represent the host address of a computer with the IP address of 192.168.1.25 and a subnet mask of 255.255.255.0?
- 8
- 32
- 128
- 4
73. How many bits are used to represent the network address of a host with an IP address of 192.168.150.16 and a subnet mask of 255.255.0.0?
- 16
- 32
- 128
- 4
74. How many bits are used to represent a MAC address?
- 48
- 128
- 8
- 64
75. How many bits are used to represent an IPv4 address?
- 32
- 48
- 128
- 132
76. How many bits are used to represent an IPv6 address?
- 128
- 48
- 32
- 12
77. How many bits are used to represent the OUI part of the MAC address of a NIC card?
- 24
- 8
- 128
- 42
78. A computer user logs a problem stating that the computer is emitting a loud clicking noise. Which device should the technician check first?
- hard drive
- CPU
- RAM
- CPU fan
79. While a technician is installing a printer, the technician hears a loud clicking noise. Which device should the technician check first?
- hard drive
- RAM
- CPU
- motherboard
80. While working in a computer training room, the technician notices that one computer emits a loud clicking noise. Which device should the technician check first?
- hard drive
- sound card
- CPU fan
- motherboard
81. Every time a user turns on the computer in the morning, the user hears a loud clicking noise. Which device should the technician check first?
- hard drive
- internal speaker
- CPU fan
- motherboard
82. When a co-worker steps into another office, the co-worker notices that the computer is making a loud clicking noise and asks about it. The technician is contacted to investigate. Which device should the technician check first?
- hard drive
- monitor
- CPU
- CPU fan
83. When a user turns on a workstation, the screen displays an “Invalid Boot Disk” error. The user calls the help desk. Which device should the technician check first?
- hard drive
- power supply
- sound card
- internal speaker
84. A technician is working on a laptop and an app is not loading. What is a possible solution for this situation?
- Perform a reset.
- Ensure that only one app is open at a time.
- Check the display settings.
- Check the screen refresh rate.
85. A technician is working on a laptop and an app is not responding. What is a possible solution for this situation?
- Perform a reset.
- Recharge the battery.
- Check the screen refresh rate.
- Replace the digitizer.
86. A technician is working on a laptop and an error message about decryption appears when opening an email. What is a possible solution for this situation?
- Install an appropriate certificate.
- Check the display settings.
- Check the screen refresh rate.
- Replace the digitizer.
87. A technician is working on a laptop and a key on the keyboard is not responding as it should. What is a possible solution for this situation?
- Clean with compressed air.
- Update all security apps.
- Recharge the battery.
- Verify that the Num Lock key is not depressed.
88. A technician is working on a laptop and the GPS is not functioning. What is a probable cause for this situation?
- A service is disabled.
- Bluetooth is activated.
- The display setting is incorrect.
- The battery is low.
89. What is the purpose of a network load balancer?
- to route data between different networks
- to prevent network timeouts and slow server responses
- to ensure that each server is deployed in a different network
- to manage network DNS and DHCP services
90. What is the purpose of an OLT in a fiber network?
- This is the splitter in the street cabinet that has connections for each customer being supplied in the area.
- It brings the fiber to the curb.
- It brings the fiber to the customer building.
- This is located inside the customer premises and interconnects the external optical network to the internal router.
91. A school is installing a new shared printer but the printer is not showing up on the list of available printers. What should the technician do to resolve the issue?
- Manually add the printer IP address.
- Reset the page counter.
- Install a USB hub.
- Connect the printer using wireless.
- Update the BIOS.
92. A Windows 10 computer has several printers configured in the Control Panel Devices and Printers window. Which printer will the computer choose to be the first option for printing?
- a manual selection, which is always needed
- the software-based printer that is used to create XPS files
- the printer that is set as the default printer
- the software-based printer that is used to create PDF files
93. What is the purpose of the Server Message Block (SMB) protocol on Windows networks?
- file sharing
- web browsing
- desktop management
- email services
94. A user on a home network wants to share a printer from a Windows 10 computer. What must the user do in order for other Windows 10 computers in the house to obtain the proper driver?
- The person doing the sharing must use the Additional Drivers button in order to designate how many device drivers are allowed to be downloaded.
- Nothing. Windows automatically provides the driver.
- The person doing the sharing must use the Additional Drivers button in order to designate the driver to be used by the other Windows 10 computers.
- The user must browse the Internet, then download and install the proper driver.
95. What are two probable causes of a VoIP implementation experiencing dropouts, echoes, or glitches? (Choose two.)
- high cable voltage
- high latency
- high bandwidth
- high cable impedance
- high jitter
96. The SDN controller controls which layers in the SDN framework?
- the network access and transport layers
- the application and transport layers
- the application and infrastructure layers
- the internet and network access layers

is this preparation for final exam on blackboard or cisco
hi is this only preperation for final or is this also final test?
hi Hi, yes, but not all of them from 96 are included
Doesn’t have this
What is the purpose of a network load balancer?
to route data between different networks
to prevent network timeouts and slow server responses
to ensure that each server is deployed in a different network
to manage network DNS and DHCP services
Navigation Bar
added, thank you!
doesnt have
What is the purpose of an OLT in a fiber network?
What type of connector can be used to connect an internal hard drive to the motherboard?
Which laptop device would accept an SD card?
Hi, can you provide the answer choices for this question?
What is the purpose of an OLT in a fiber network?
What is the purpose of an OLT in a fiber network?
This is the splitter in the street cabinet that has connections for each customer being supplied in the area.
It brings the fiber to the curb.
It brings the fiber to the customer building.
This is located inside the customer premises and interconnects the external optical network to the internal router.
Navigation Bar
Thank you for sharing.
A school is installing a new shared printer but the printer is not showing up on the list of available printers. What should the technician do to resolve the issue?
I added. Thank you.
A user is building a new computer system. Why would the user select a DDR4?
to install a memory module
1.A technician is working on a laptop and the GPS is not functioning. What is a probable cause for this situation?
Thanks for your sharing!
72. How many bits are used to represent the host address of a computer with the IP address of 192.168.1.25 and a subnet mask of 255.255.255.0?
The answer is wrong! Right answer is 32.
IPv4 has 8 bayts, but it is 32 bits ( 8 * 4 = 32 ).
(87)
Ans-
Clean with compressed air
1Once a technician understands a customer complaint, it is common to ask closed-ended questions. Which question is a close-ended one?
Is this the first time the error occurred?
What happened after the error occurred?
What happened before the error occurred?
What error messages were displayed when the error occurred?
Navigation Bar
Is this similar to the Testout edition of the Final Exam?
two questions are wrong
– A technician uses the shrink volume feature of the disk management utility and splits the partition. What must the technician do next in order to make use of the new space?
answer: Partition the unallocated space
– Where can a technician enable ACPI mode on a laptop?
answer: BIOS
A technician uses the shrink volume feature of the disk management utility and splits the partition. What must the technician do next in order to make use of the new space?
The correct answer is: Partition the unallocated space.
Where can a technician enable ACPI mode on a laptop?
The correct answer is: BIOS
Correction: Question 59’s answer is wrong- bottom two answers should be swapped around.
This Question:
A technician is asked to set up one hard drive that will support two operating systems and will store data files in three separate drive locations. Which partition settings will support these requirements?
1 primary, 3 active, 1 extended, 2 logical
** Your Correct Answer 2 logical, 2 active, 3 extended
2 primary, 1 active, 1 extended, 3 logical
3 primary, 1 active, 2 extended
Feedback to me from Cisco:
A technician is asked to set up one hard drive that will support two operating systems and will store data files in three separate drive locations. Which partition settings will support these requirements?
Your Response: 2 logical, 2 active, 3 extended
1 primary, 3 active, 1 extended, 2 logical
Correct Response: 2 primary, 1 active, 1 extended, 3 logical
3 primary, 1 active, 2 extended
The primary partition that is marked active must carry the boot files for both the operating systems.In this case the data can be stored in the three logical drives created in the extended partition, leaving one extra primary drive for additional storage.
Two other questions I missed where your answer does not agree with how I was scored:
A technician uses the shrink volume feature of the disk management utility and splits the partition. What must the technician do next in order to make use of the new space?
Correct Response: Partition the unallocated space.
Convert the unallocated space into a dynamic disk.
Delete all partitions and reinitialize the disk.
Your Response: Format the existing partition.
Where can a technician enable ACPI mode on a laptop?
Correct Response: BIOS
Task Manager
Personalization
Your Response: Device Manager